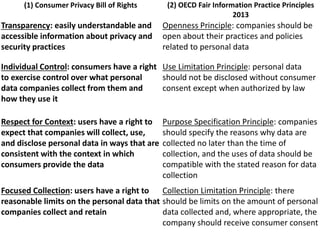
The document discusses the evolving landscape of privacy and data ethics in the context of advancing technology, emphasizing themes like seamless data integration in daily life and the ethical challenges posed by big data. It highlights the public's growing concerns about privacy, the shifting nature of consent, and the need for transparency and accountability in data handling. Additionally, it outlines principles for consumer privacy rights and calls for new frameworks to protect individuals' data amidst increasing digital interconnectedness.