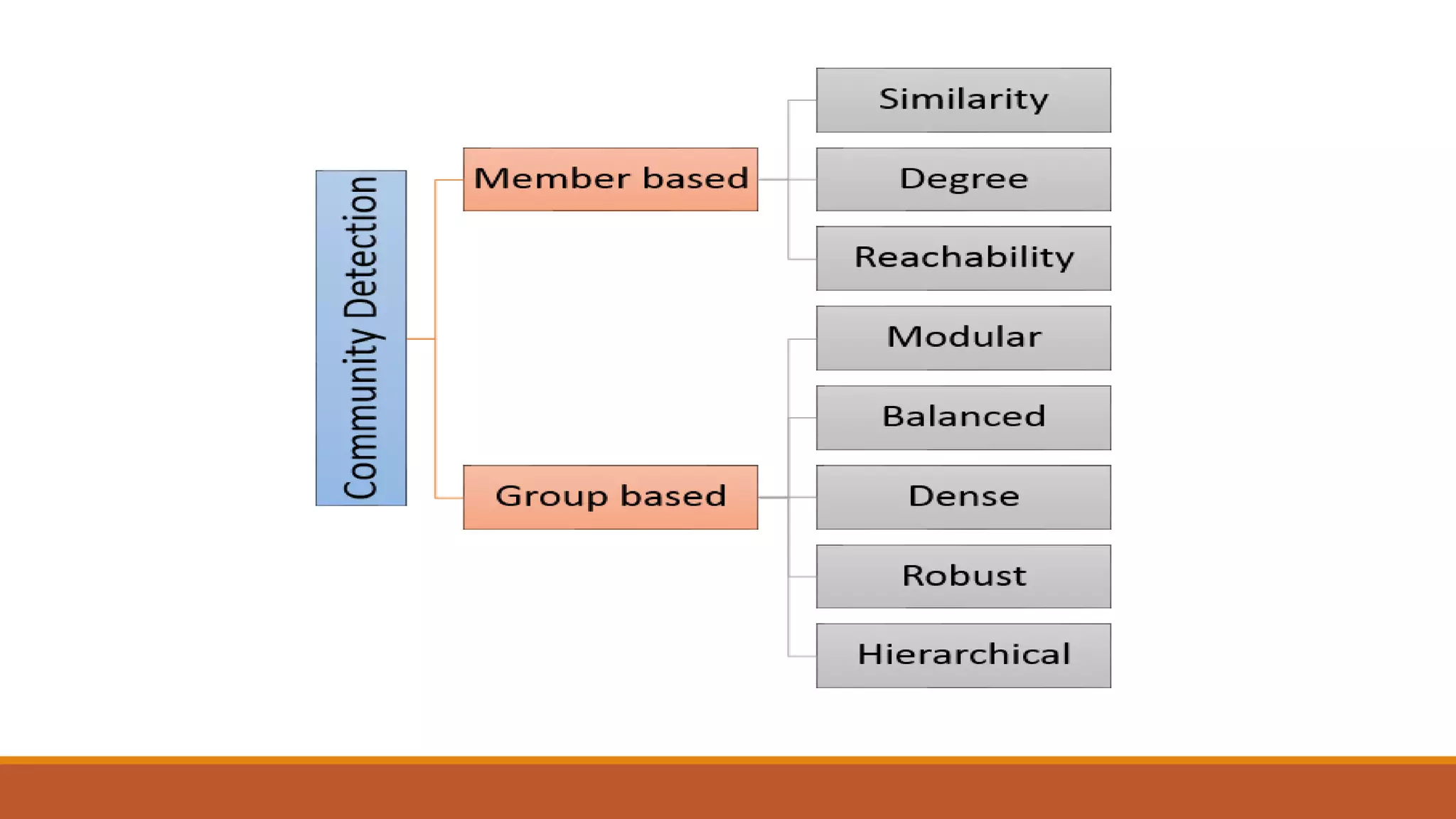
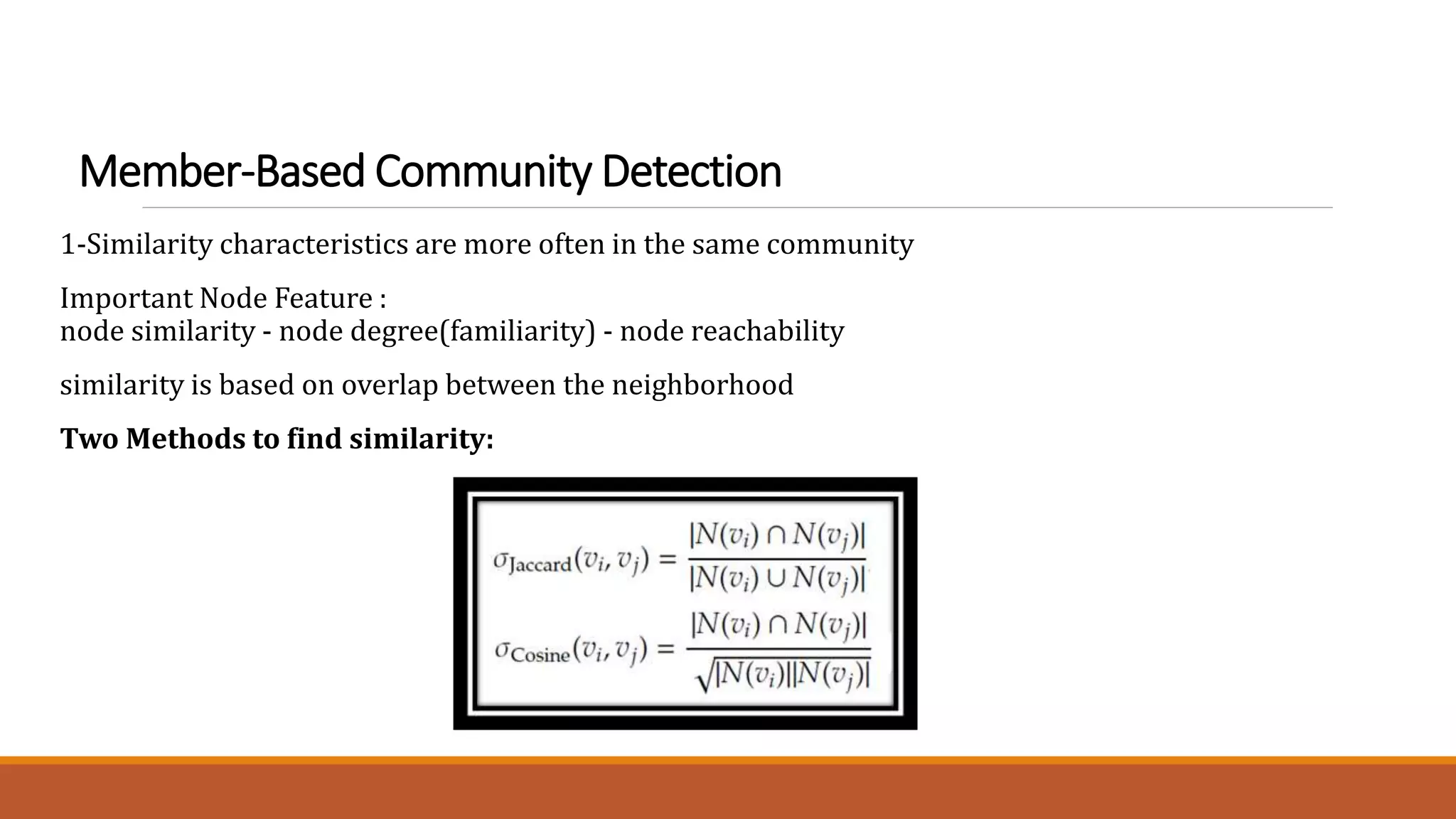
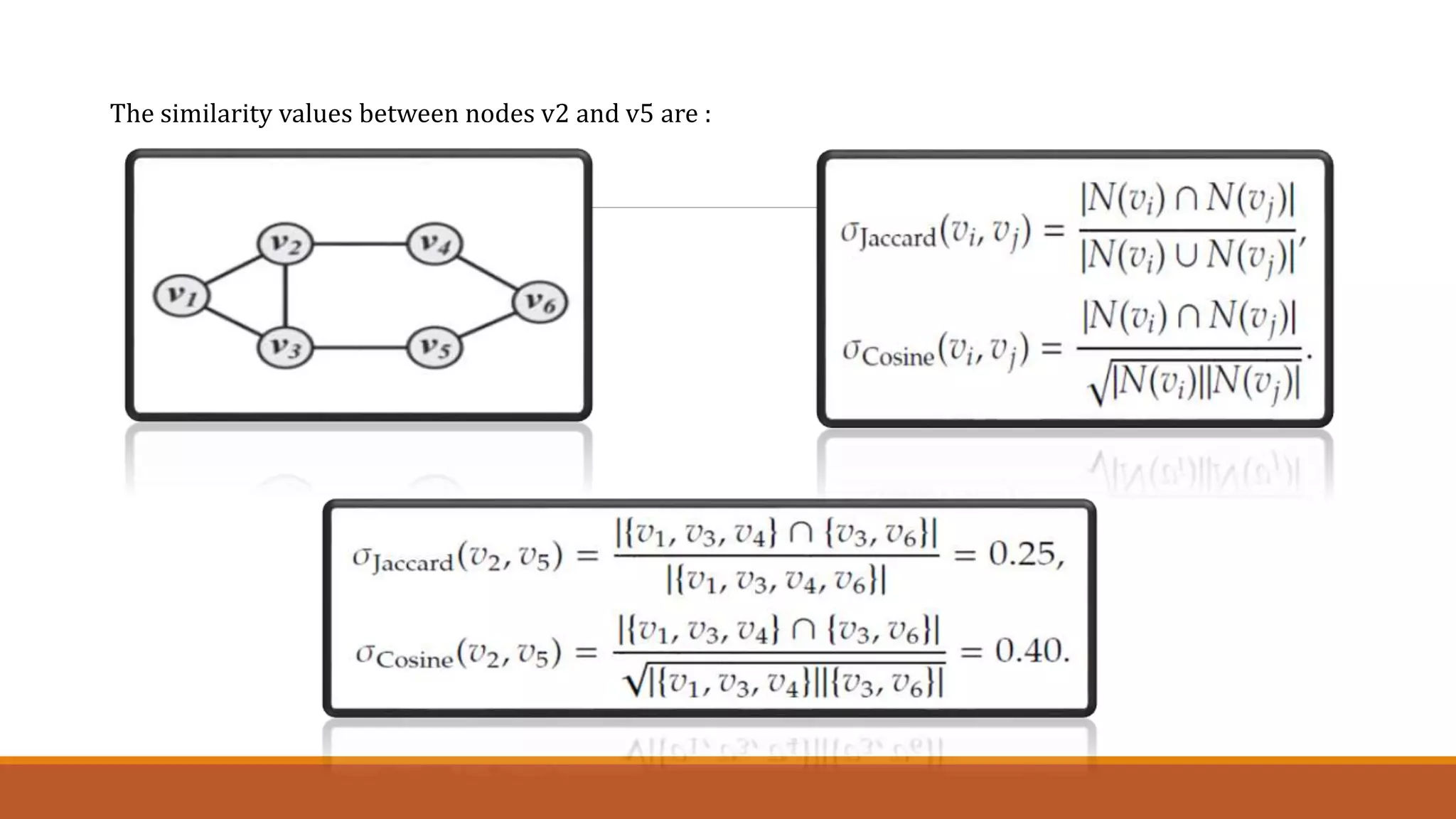
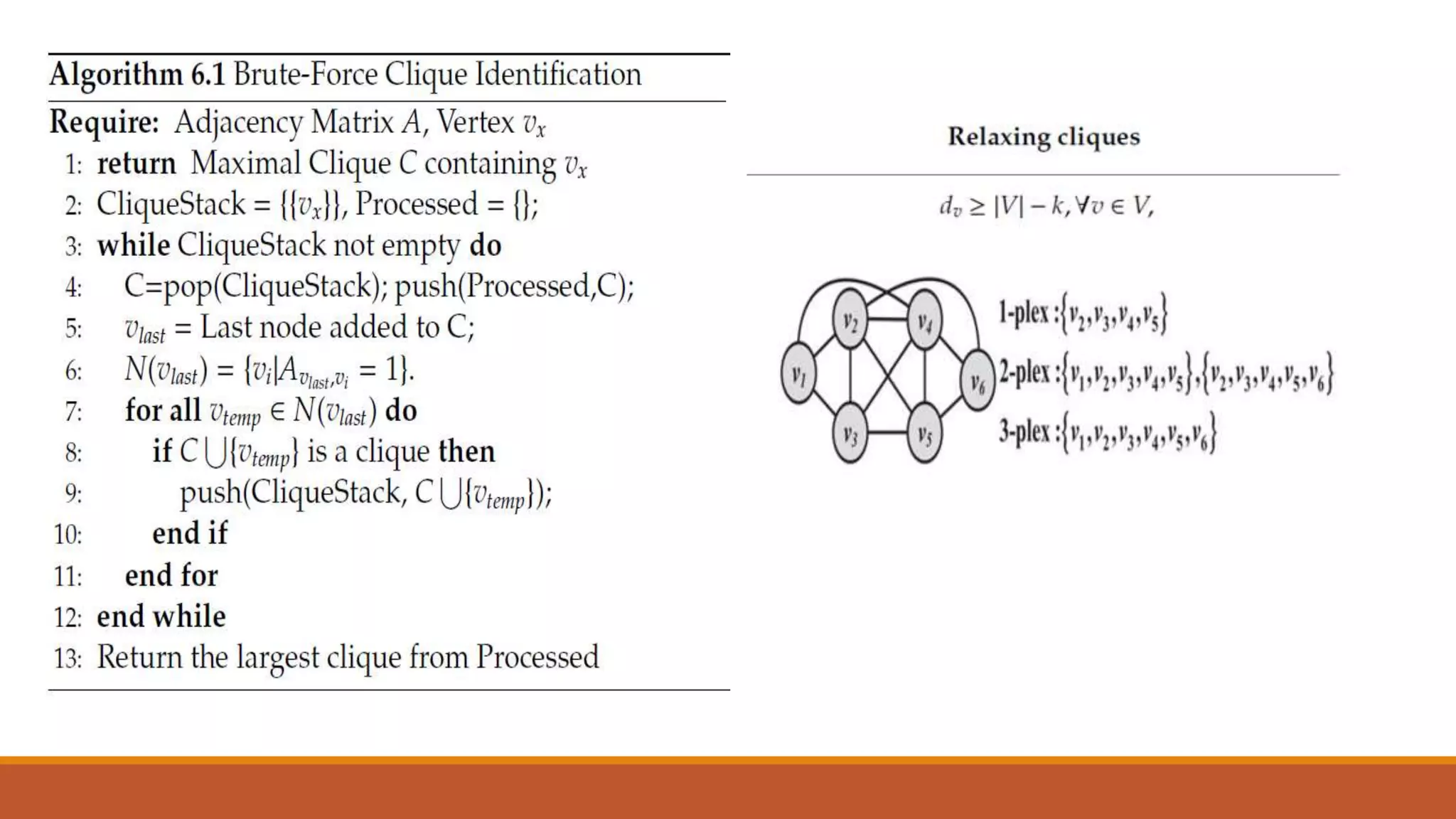
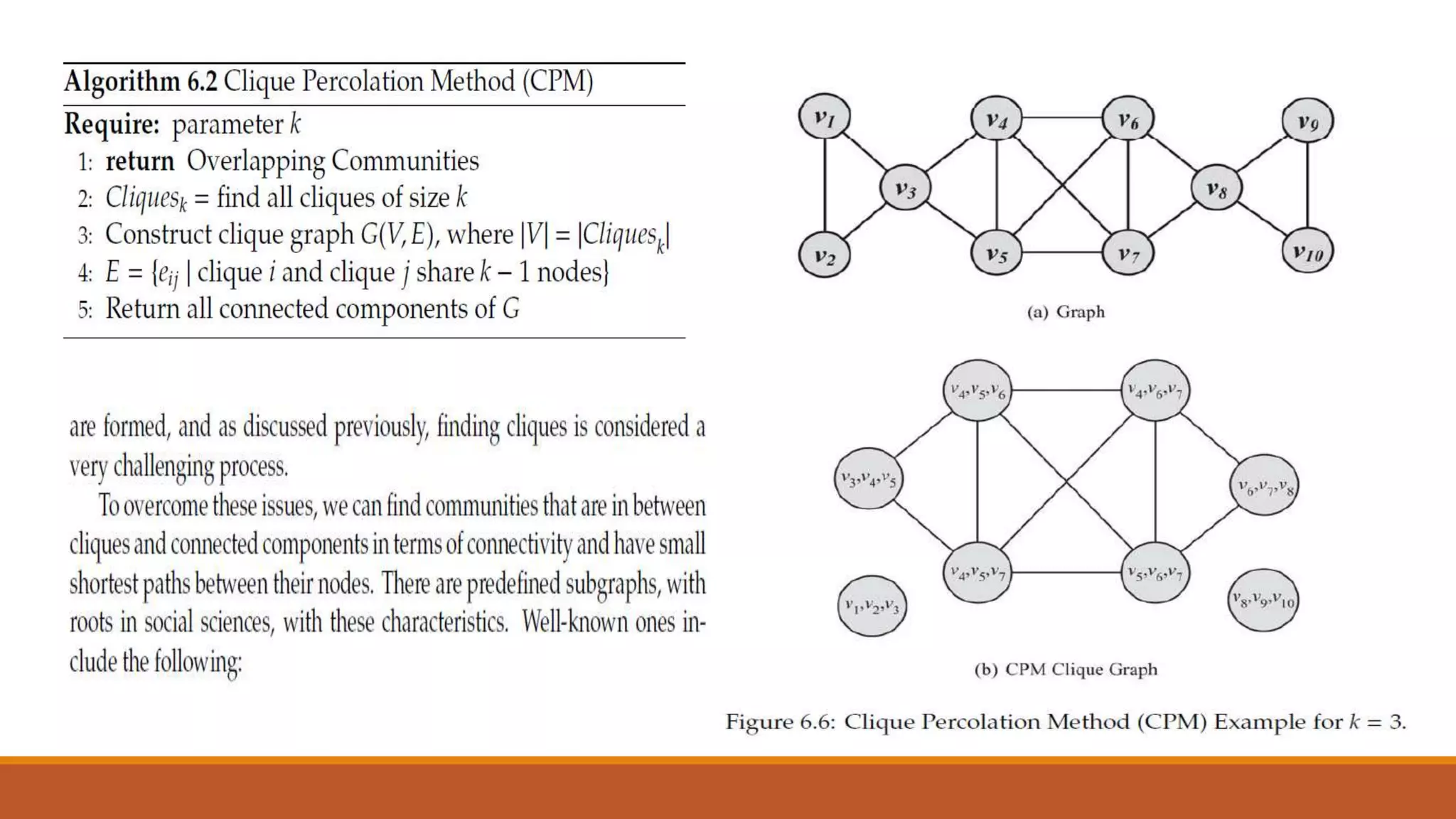
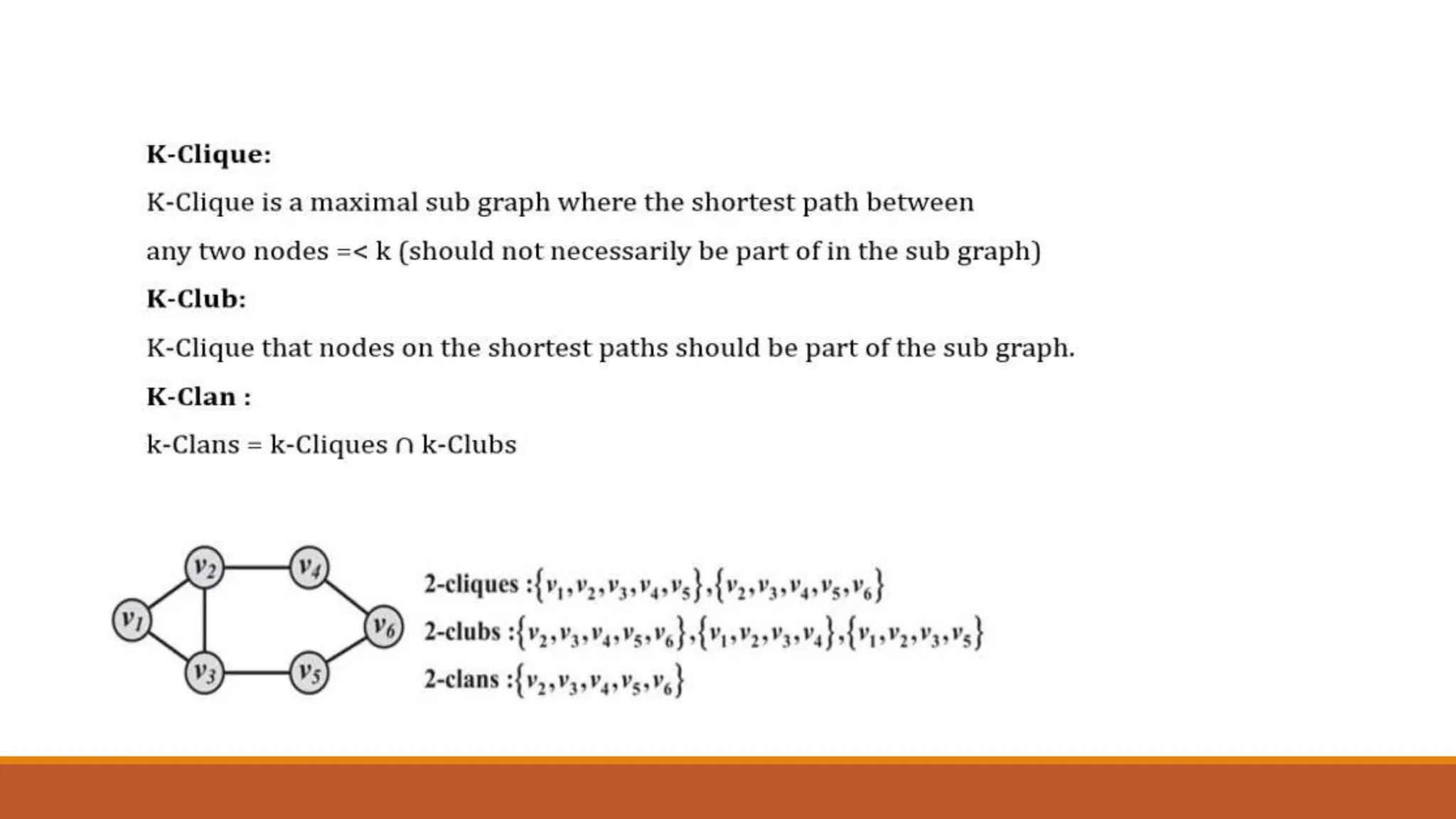
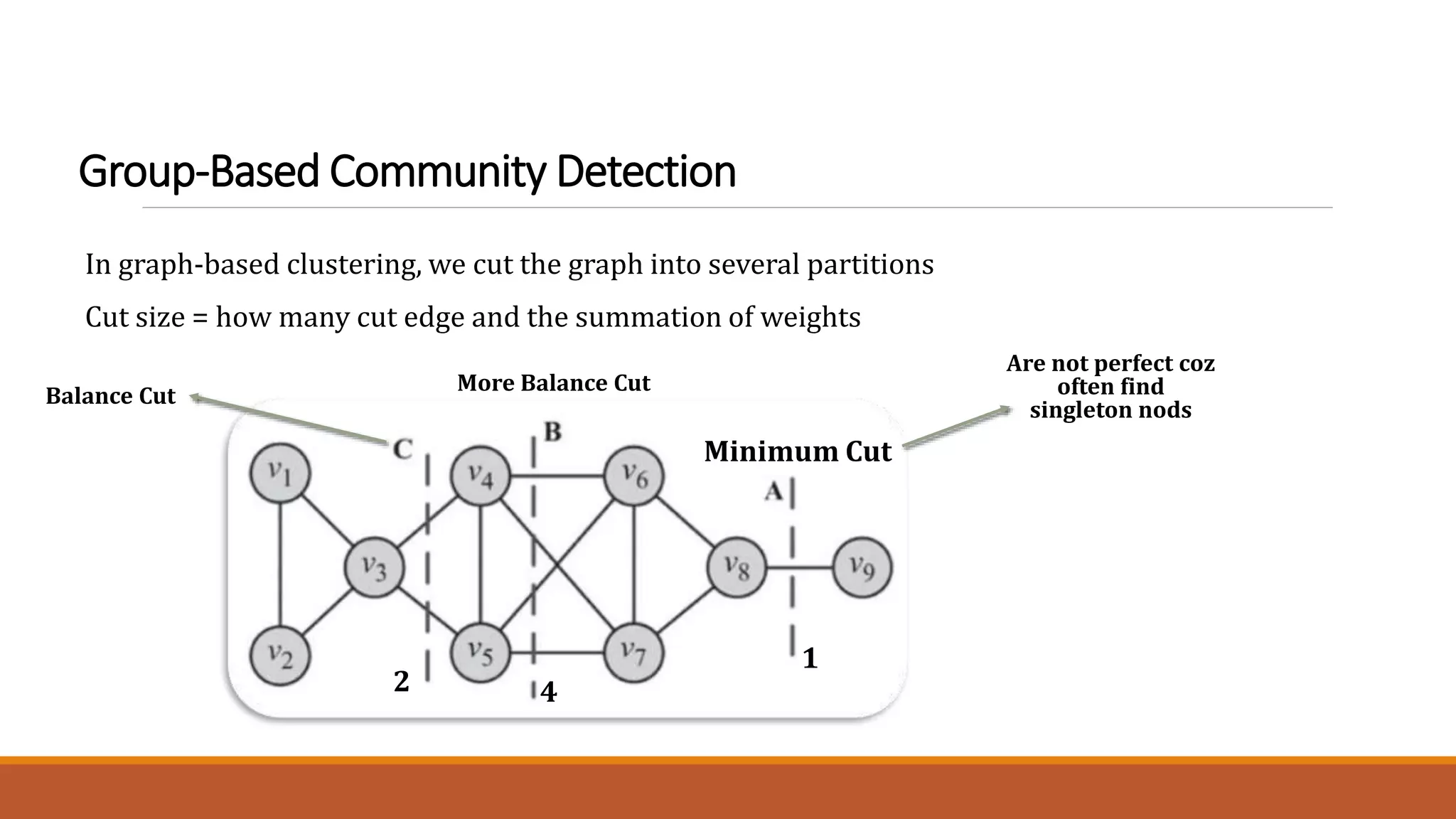
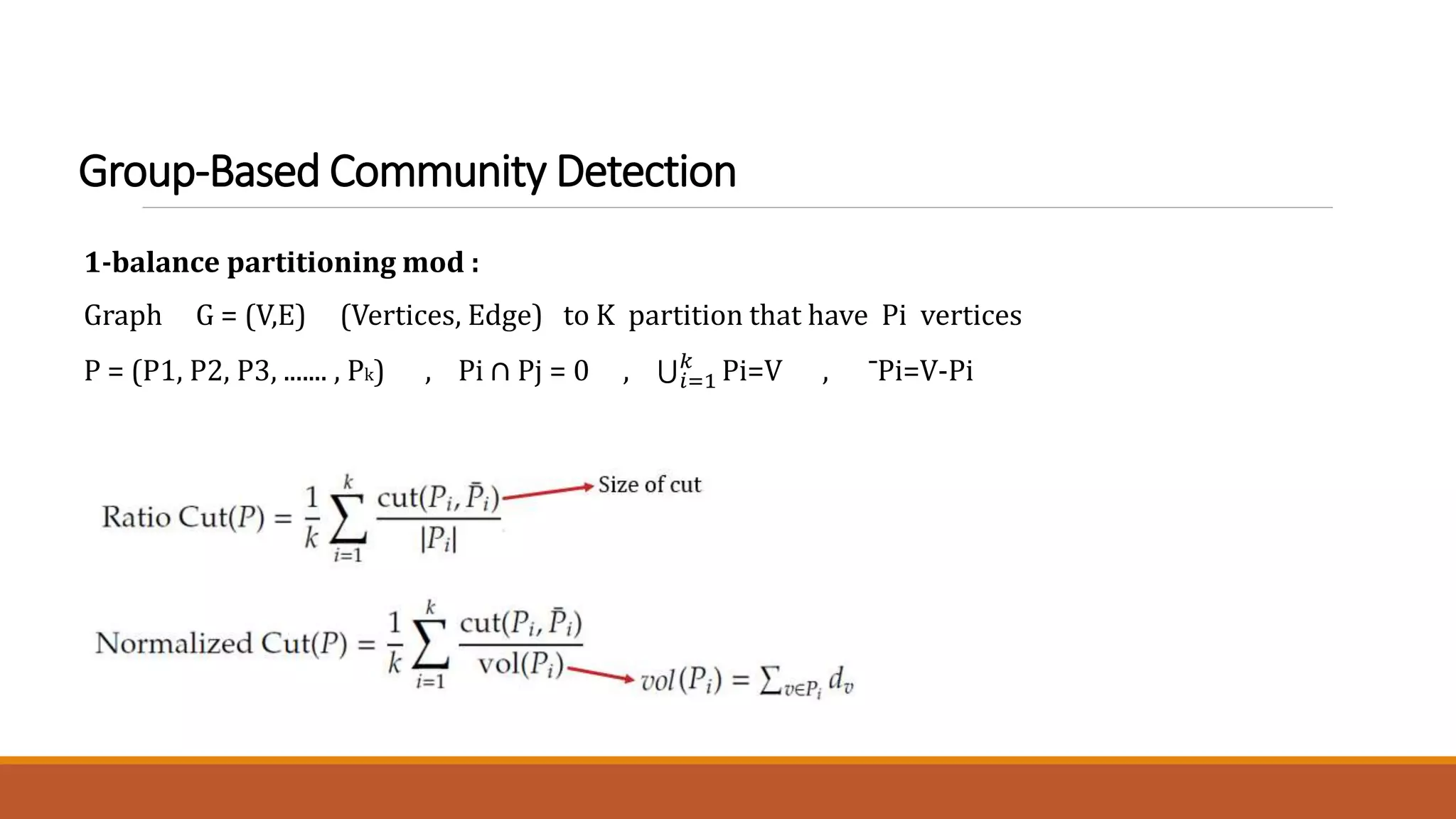
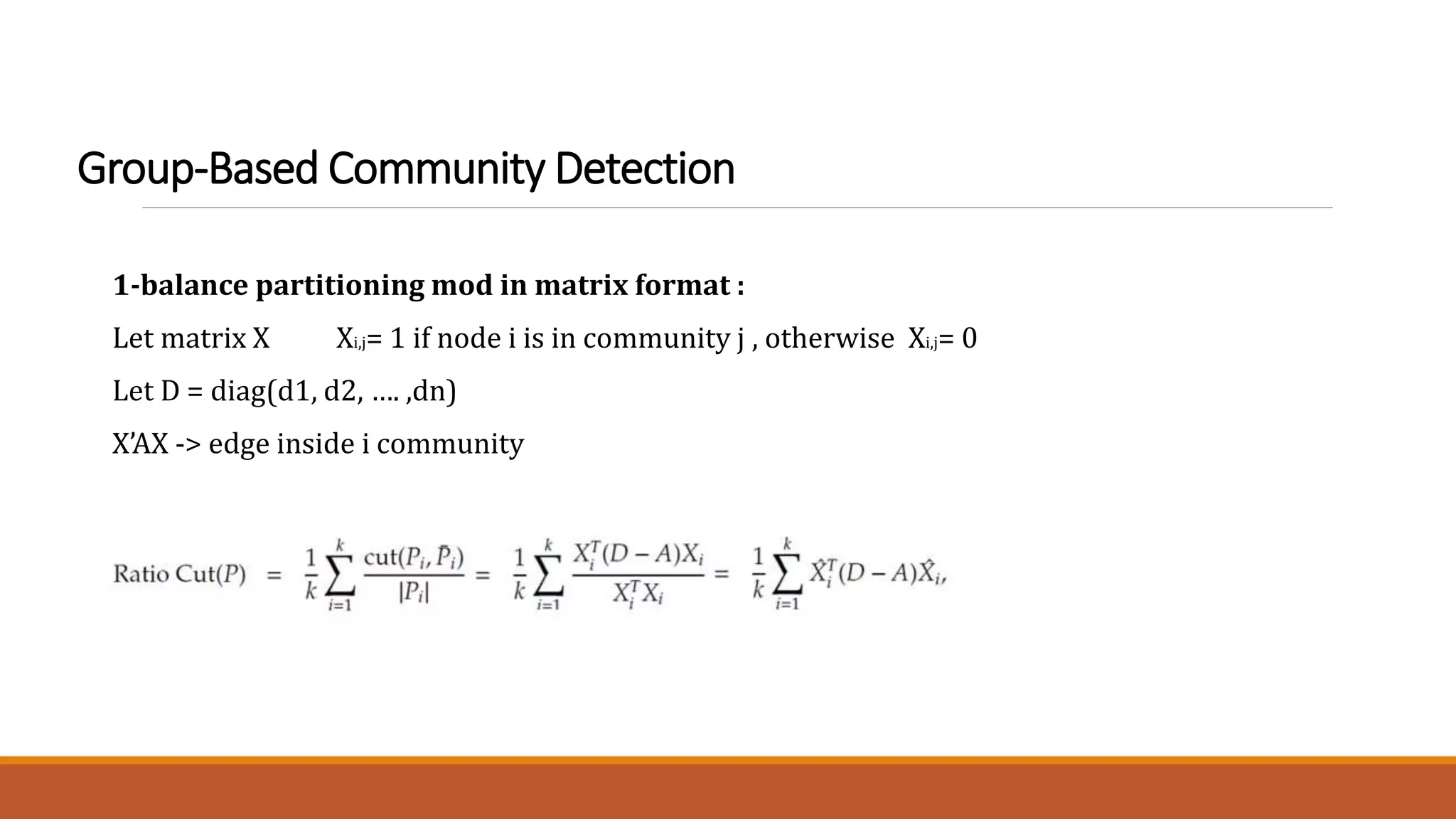
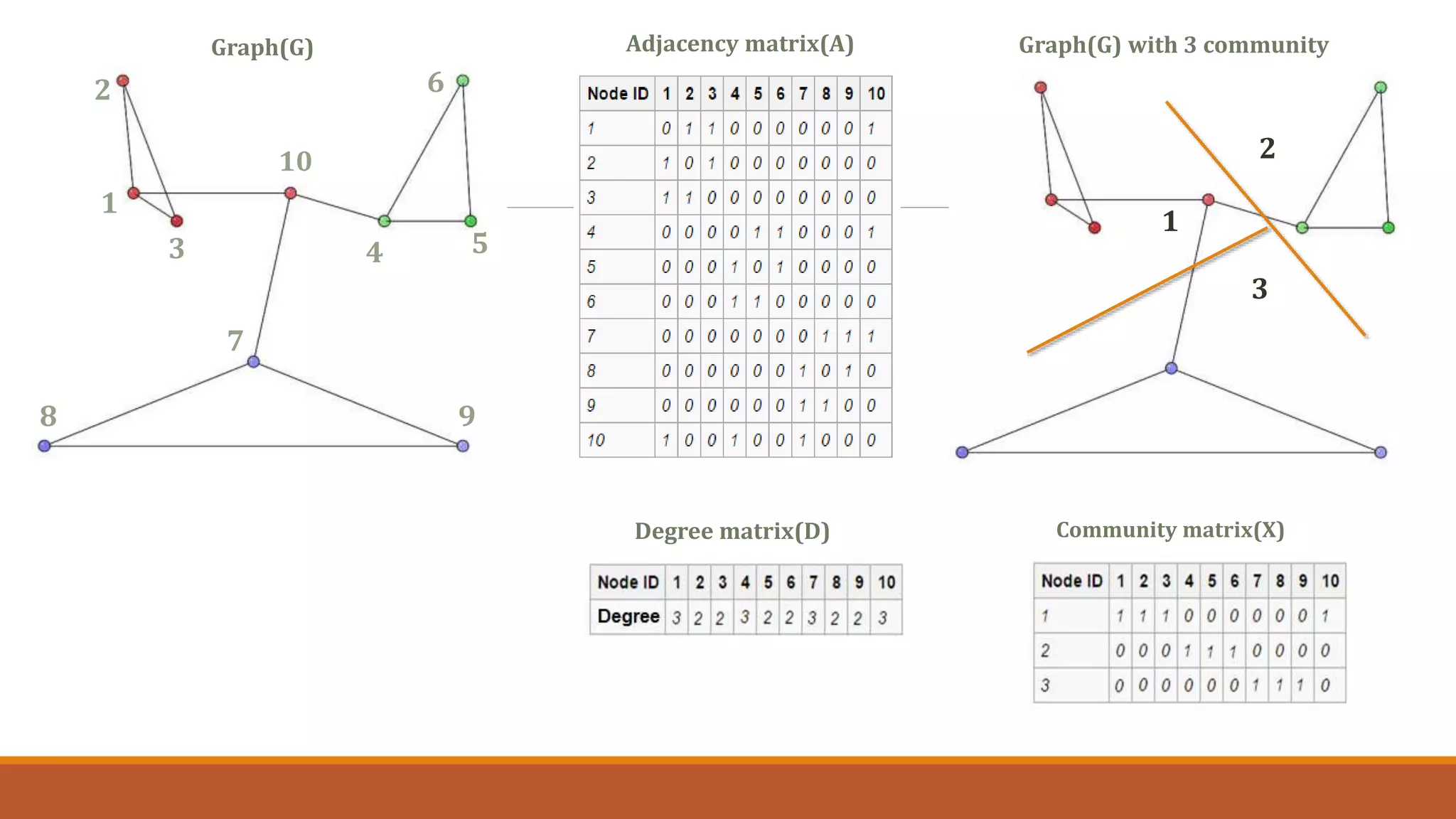
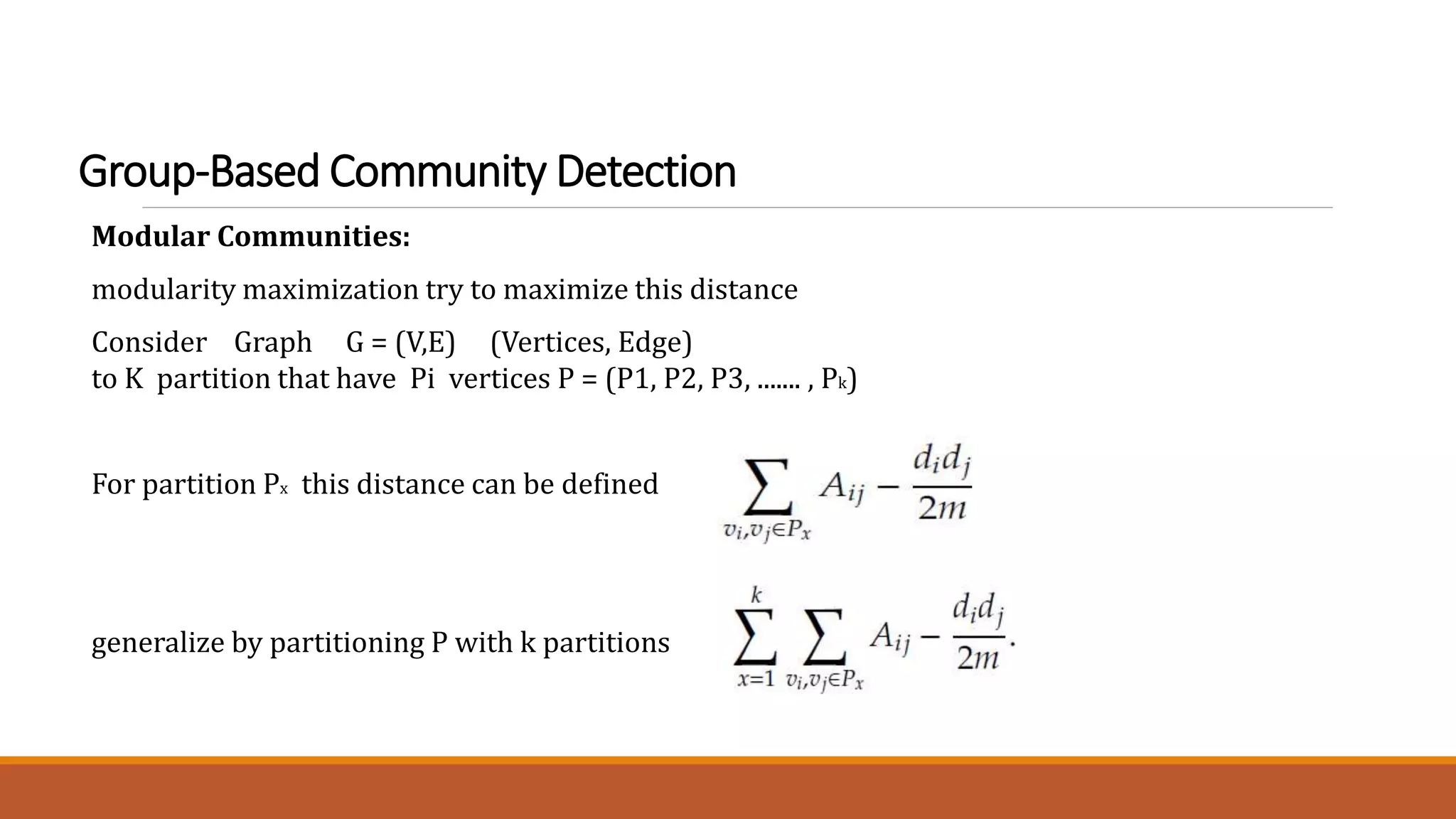
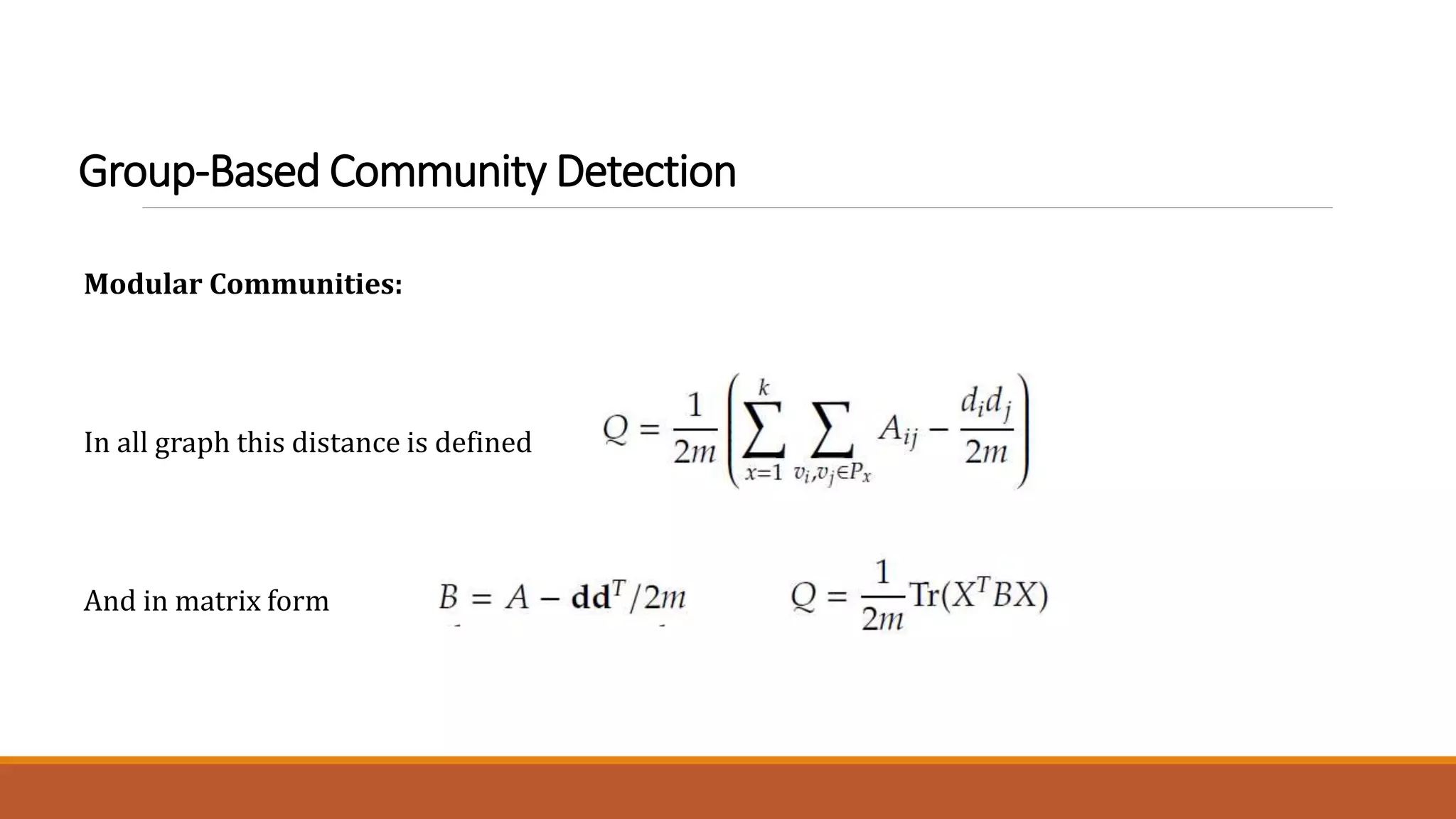
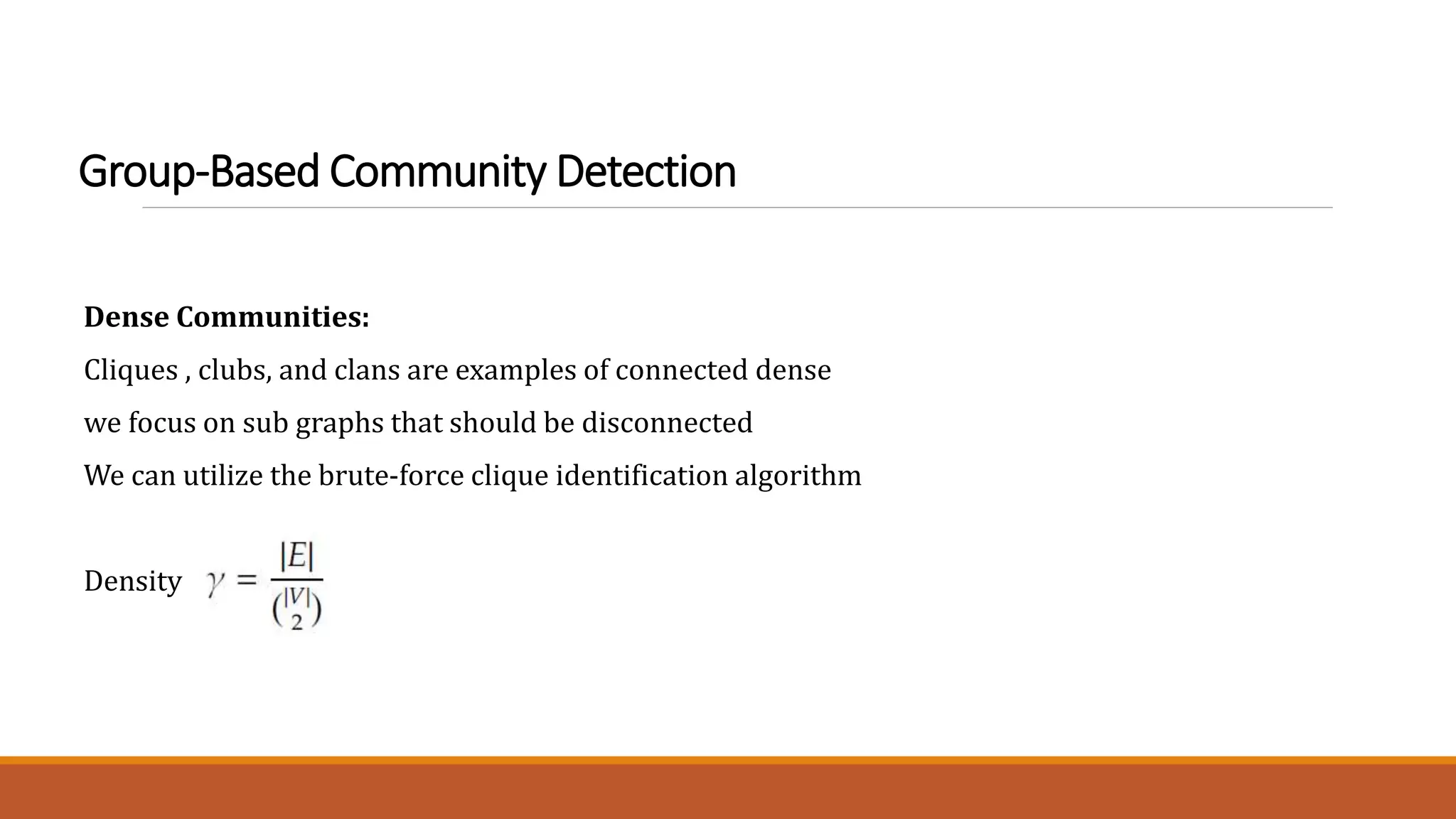
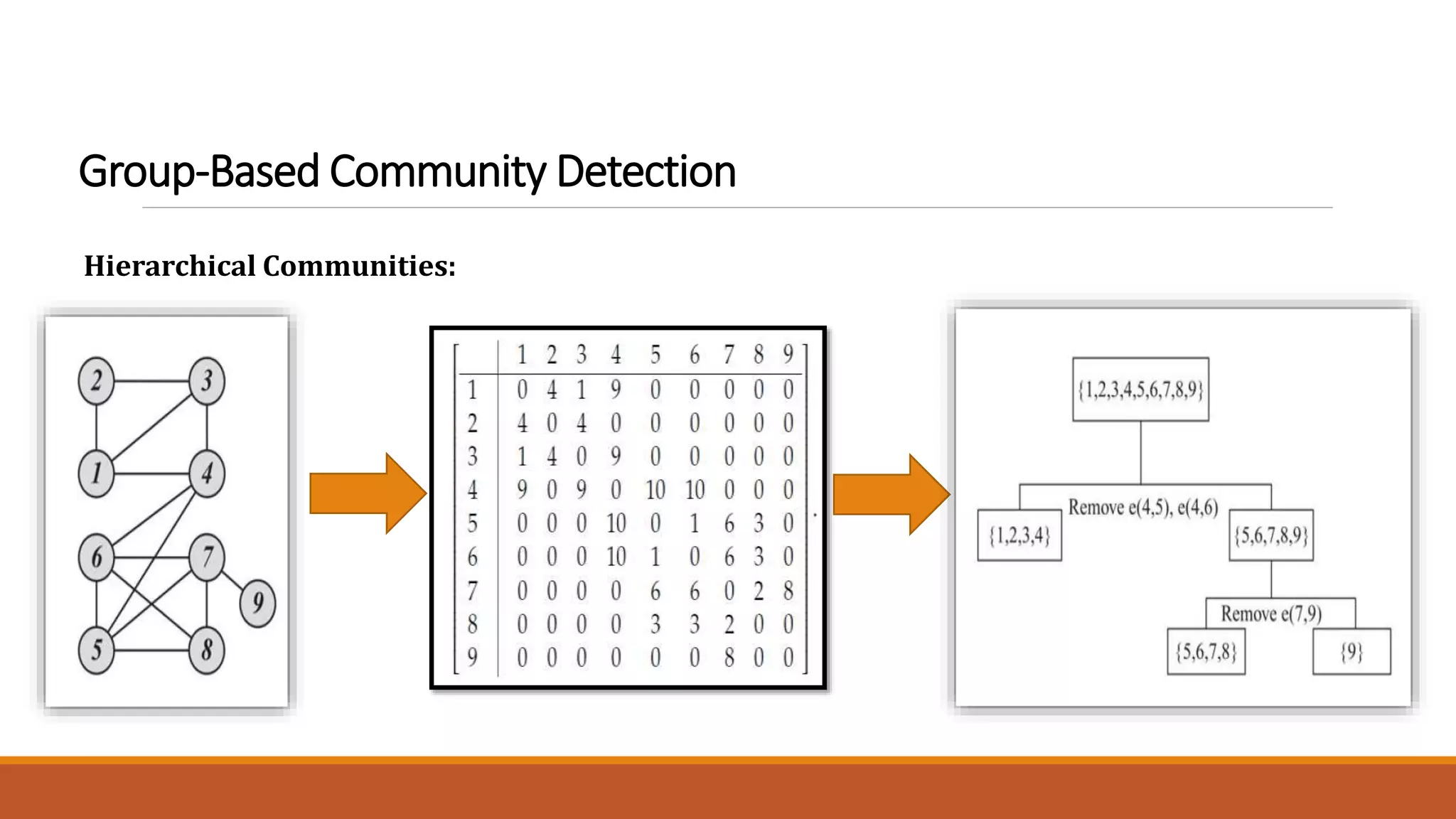
The document discusses various community detection algorithms, emphasizing member-based and group-based methods to identify communities and their structures within graphs. It highlights key concepts such as node similarity, clique identification, balance partitioning, and modularity maximization, along with the hierarchical community detection approach using the Girvan-Newman algorithm. The aim is to find robust and modular communities that withstand the removal of edges or nodes while assessing their connectivity and structure effectively.