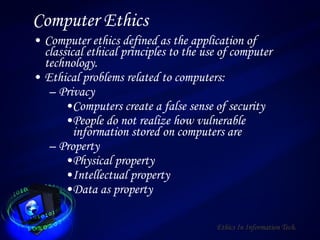
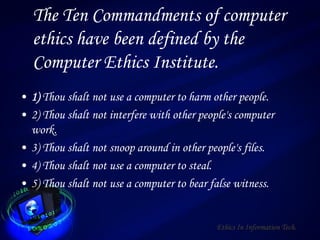
The document discusses various topics relating to ethics and information technology including definitions of ethics, computer ethics, and issues like privacy, property, and access. It also covers computer viruses, types of computer crimes, hacking, software piracy, and ethical dilemmas. Computer viruses are defined as programs designed to spread and interfere with computers. Types of computer crimes include those targeting information, medium of attack, tools used, and motives like economic or psychological gain. Hacking and software piracy are also defined and their advantages and disadvantages discussed. Ethical dilemmas concern areas like privacy, information accuracy, access, and intellectual property rights.