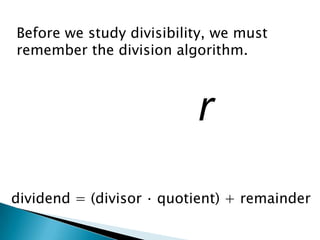
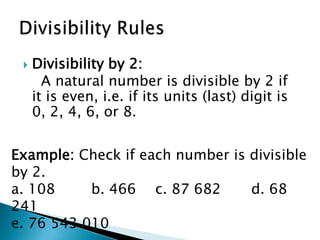
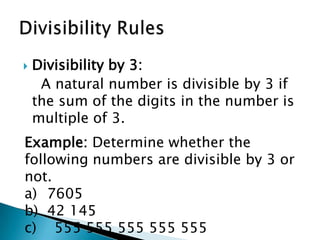
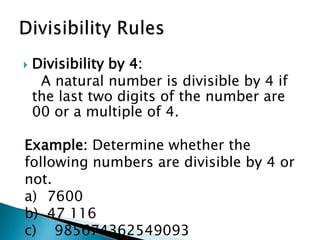
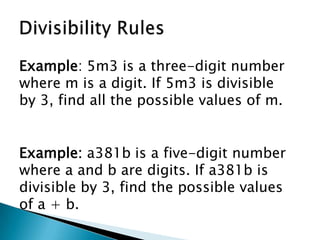
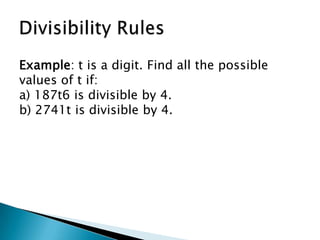
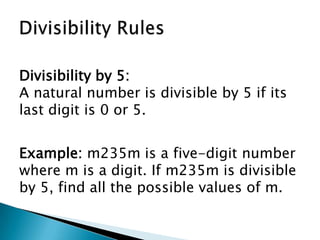
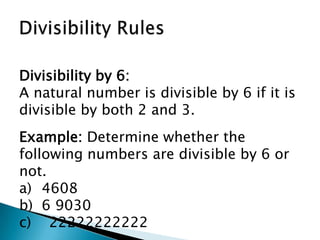
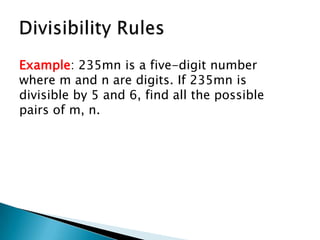
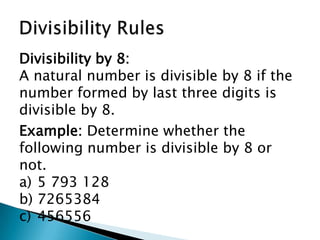
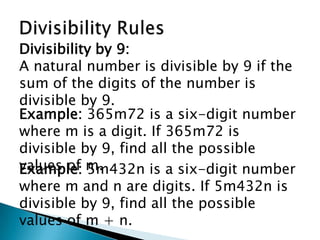
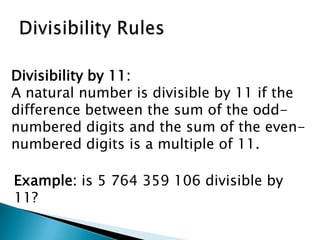
The document discusses divisibility rules for natural numbers. It begins by introducing the division algorithm and defining divisibility. It then provides divisibility rules and examples for numbers being divisible by 2, 3, 4, 5, 6, 8, 9, 10, and 11. Specific rules include a number being divisible by 2 if the last digit is even, divisible by 3 if the sum of the digits is divisible by 3, and divisible by 4 if the last two digits are a multiple of 4.