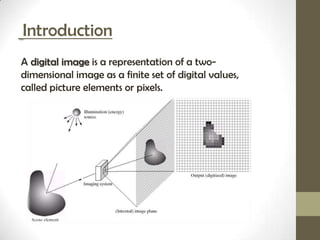
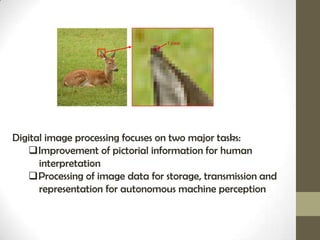
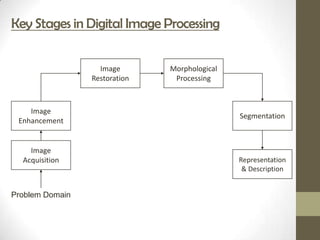
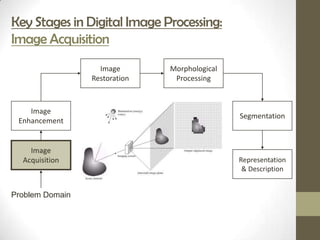
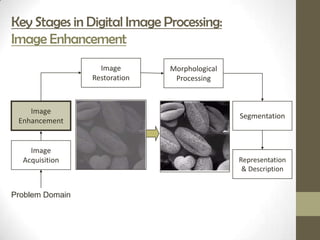
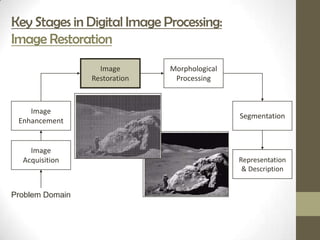
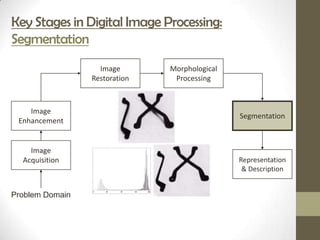
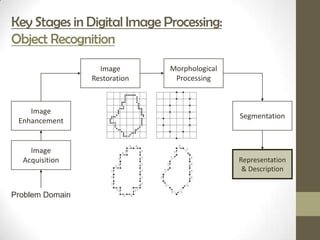
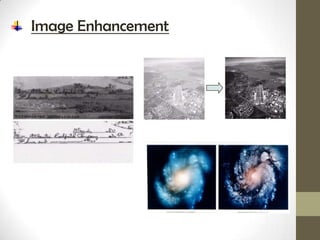
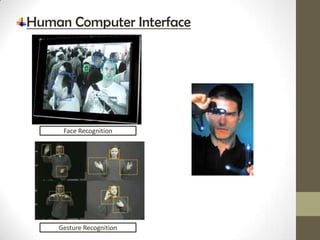
Digital image processing focuses on improving images for human interpretation and machine perception. It involves key stages like acquisition, enhancement, restoration, morphological processing, segmentation, and representation. Applications include medical imaging, industrial inspection, law enforcement, and human-computer interfaces. While digital images allow for faster and more efficient processing than analog images, limitations include reduced quality if enlarged beyond a certain file size.