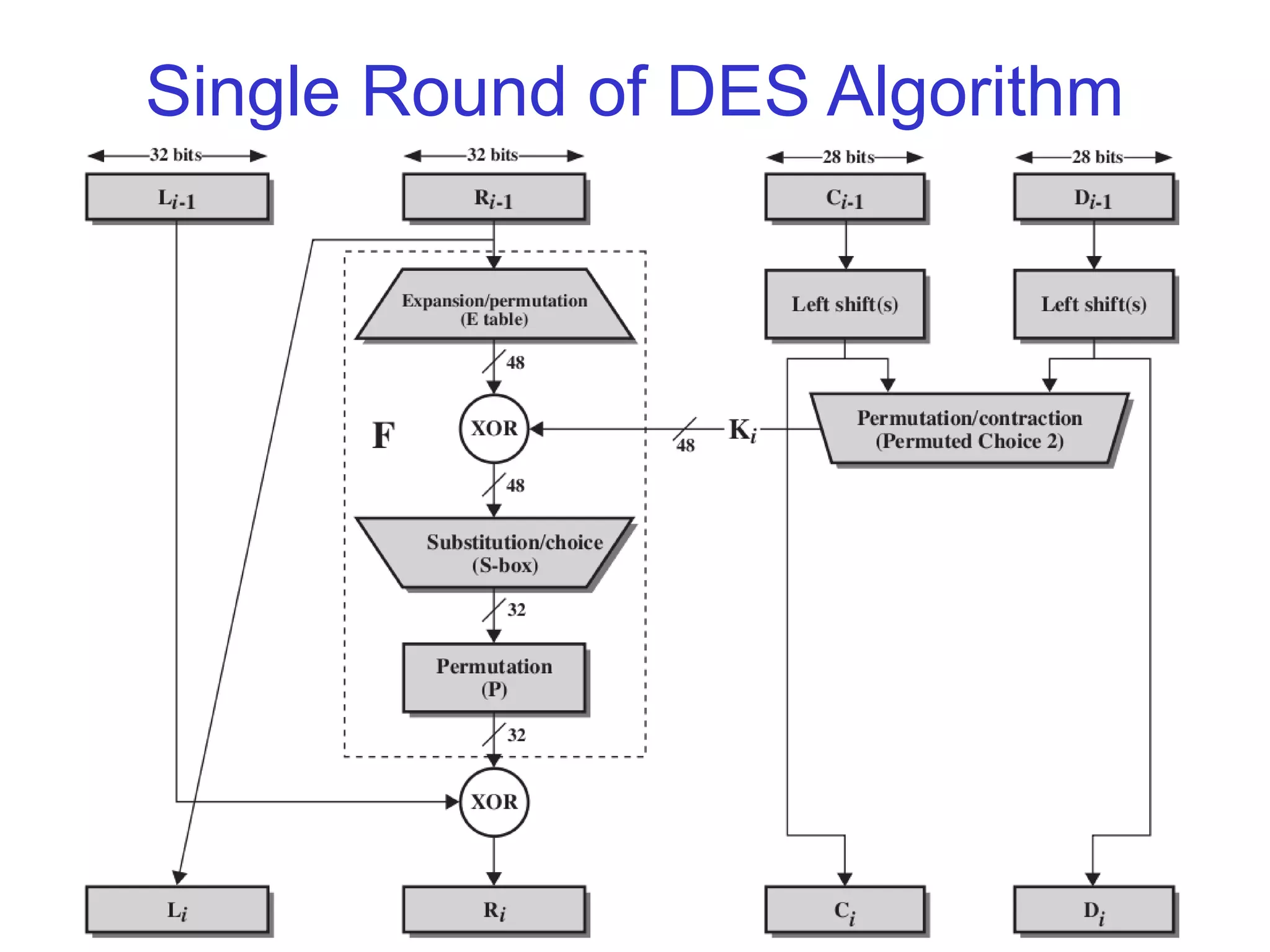
Block ciphers encrypt data in fixed-size blocks and can be categorized as stream or block ciphers. The document describes block cipher principles including the Feistel cipher structure, ideal block ciphers, and the practical block cipher Data Encryption Standard (DES). It provides details on the DES algorithm, key schedule, substitution boxes, diffusion and confusion properties, and modern cryptanalysis techniques such as differential and linear cryptanalysis. The DES standard utilizes a 56-bit key and has been superseded by algorithms with stronger 128-bit keys due to advances in computing power allowing brute force attacks on its 56-bit key.






















































![56
Searching for a DES key
Year Source Implemented? (Estimated)
Cost in US$
(Estimated)
Search time
1977 Diffie
Hellman
No 20 million 20 hours
1993 Wiener No 10.5 million
1.5 million
600 000
21 minutes
3.5 hours
35 hours
1997 Internet Yes Unknown 140 days
1998 Electronic
Frontier
Foundation
[www.eff.org]
Yes 210 000 56 hours](https://image.slidesharecdn.com/des-140619083232-phpapp02/75/Des-56-2048.jpg)






