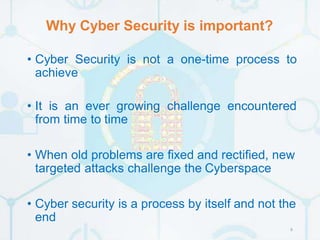
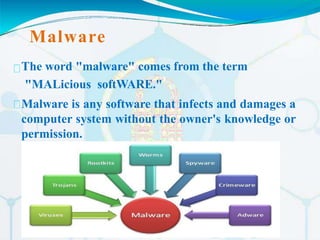
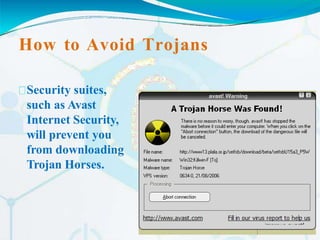
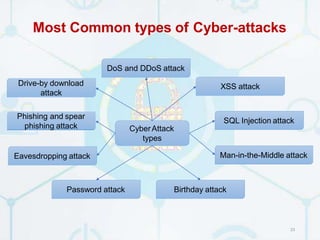
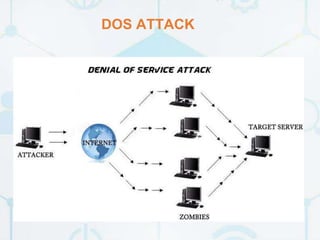
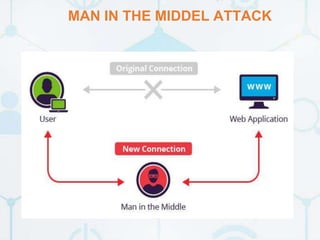
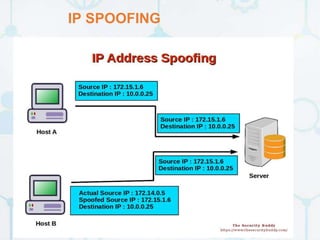
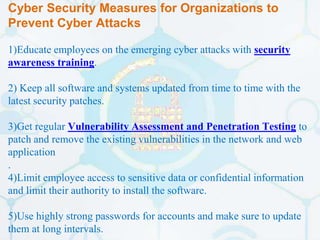
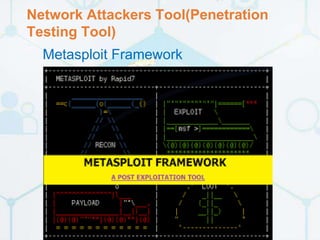
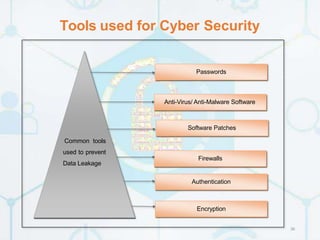
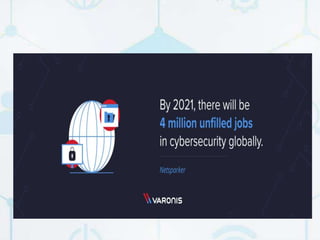
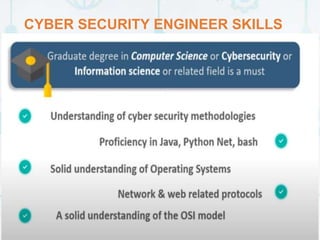
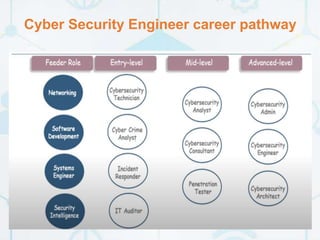
Cyber security is important to protect electronic data and online services from criminal or unauthorized use. There are various security problems in the cyber field like cyber attacks, viruses, hackers, malware, and trojan horses. Some major cyber attacks in India include the Cosmos Bank attack, Aadhaar software hack, ATM system hack, and personal data breaches at companies like JustDial. To prevent cyber attacks, organizations should educate employees, keep software updated, perform security testing, and limit employee access to sensitive data. Careers in cyber security include roles like cyber security engineers, penetration testers, and security analysts.