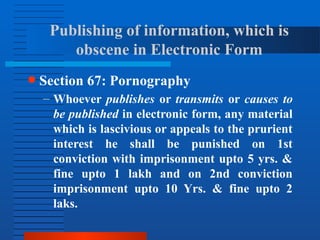
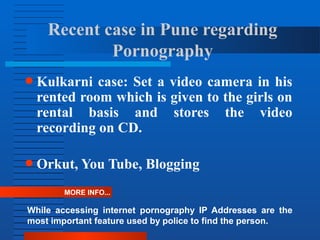
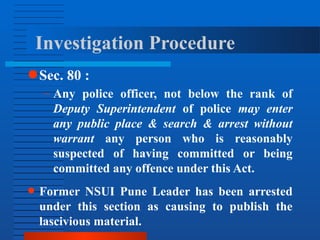
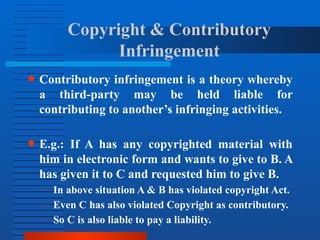
Cyber law governs the use of computers, the internet, and digital technology. It defines illegal access to computer systems and digital content as well as crimes like hacking and distributing obscene materials online. The Information Technology Act of 2000 is the primary law regulating cyber activity in India and outlines offenses and penalties. For example, unauthorized access to a computer system or downloading copyrighted content without permission can result in fines of up to 1 crore rupees. The act also prohibits hacking, publishing obscene materials electronically, and contributory infringement of copyright.