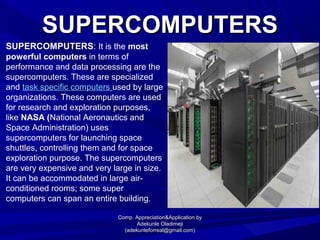
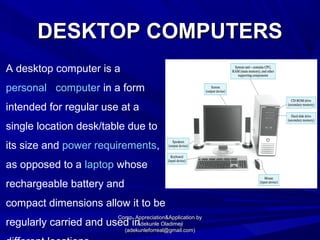
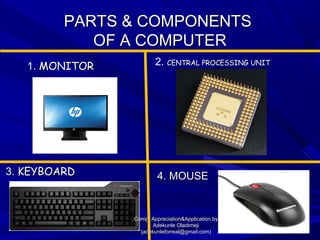
The document discusses different types of computers and their uses. It defines a computer as an electronic device that can store, retrieve, and process data. It then describes several types of computers including supercomputers, mainframes, mini computers, desktops, laptops, and tablets. Each computer type has different processing power, data storage capabilities, and typical uses. The document also covers computer components, software types, and basic functions like word processing, spreadsheets and presentations.