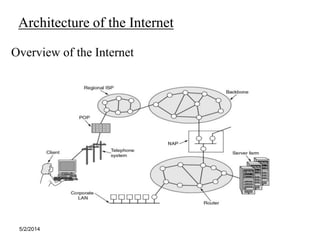
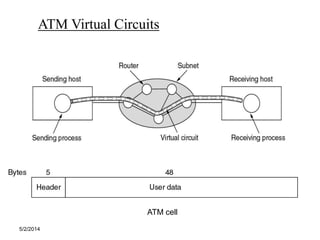
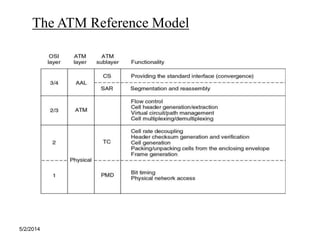
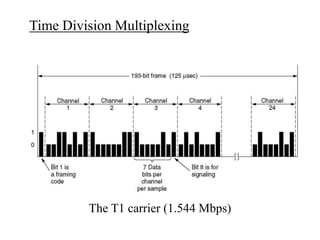
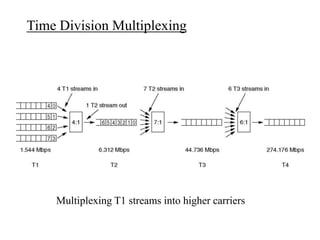
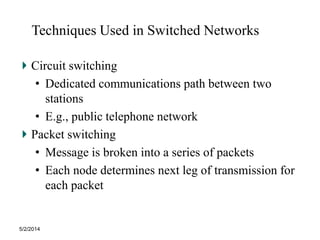
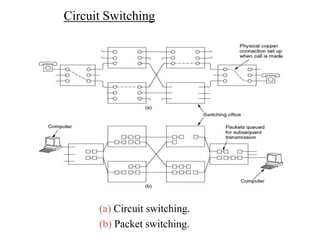
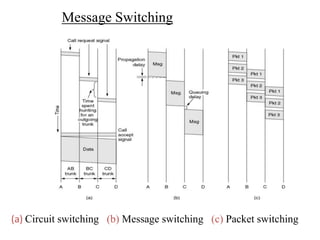
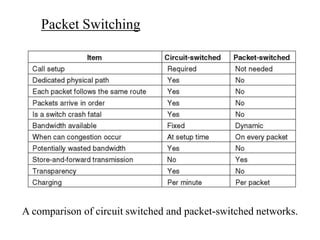
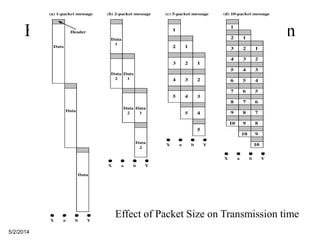
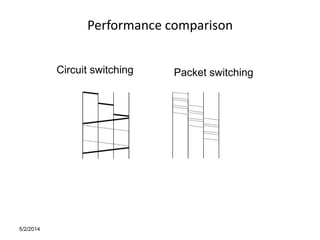
The document discusses the characteristics and differences between wide area networks (WANs) and local area networks (LANs), including their data rates, ownership, and interconnection of devices. It also covers various network technologies such as circuit switching, packet switching, and ATM, along with performance criteria like reliability and security. Additionally, it highlights techniques used in switched networks and the impact of packet size on transmission times.