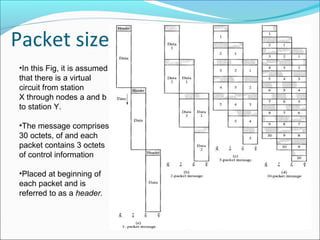
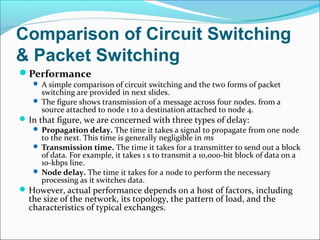
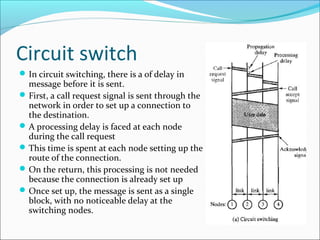
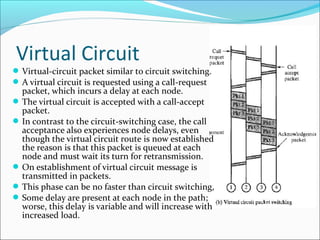
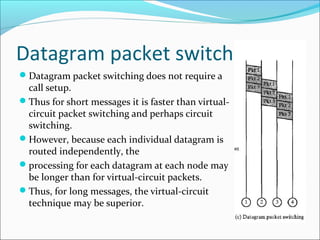
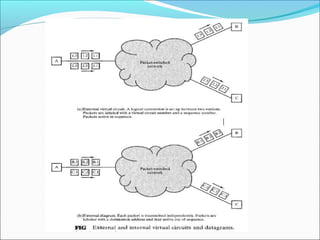
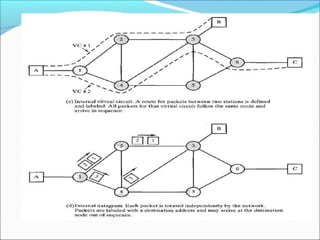
The document discusses the evolution from circuit-switching to packet-switching networks in telecommunications, highlighting inefficiencies in circuit-switching when handling data traffic. It explains packet-switching's advantages such as better line efficiency, dynamic sharing of resources, and the capability to handle different data rates between interconnected devices. Two primary packet-switching approaches, datagram and virtual circuits, are compared, detailing their operational mechanisms, reliability, and use cases depending on network design objectives.