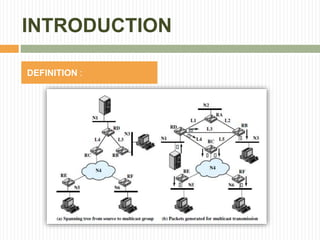
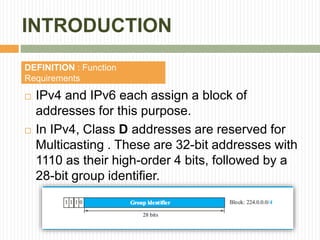
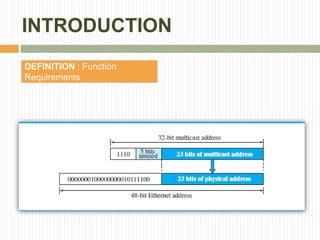
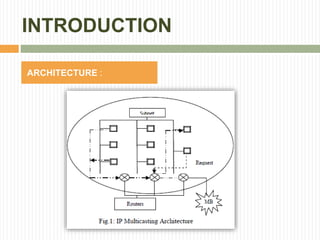
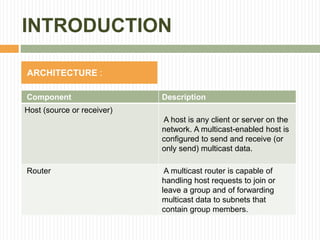
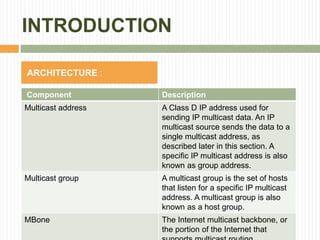
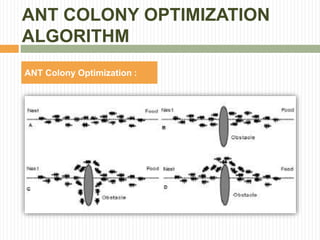
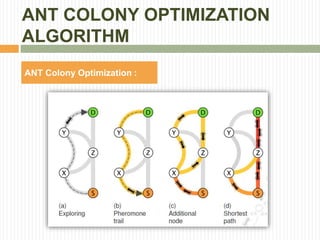
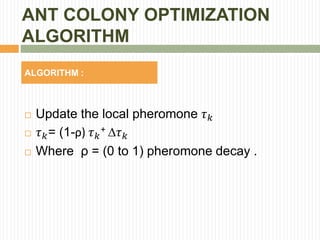
The document discusses a proposed ant colony optimization (ACO) algorithm for solving the Quality of Service (QoS) multicast routing problem in IP multicasting. It explains the nature of multicasting compared to unicast and broadcast, detailing both technical requirements and the functioning of multicast systems. Additionally, it introduces the principles behind ACO, likening its process to the behavior of real ants in finding optimal paths and laying down pheromones.



![ANT COLONY OPTIMIZATION
ALGORITHM
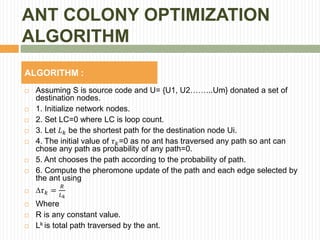
ALGORITHM :
Compute the probability 𝑃𝑘 of each edge.
𝑃𝑘 =
[𝜏] 𝛼
∗ [𝑛]
𝛽
𝑗∈𝑛[𝜏] 𝛼
∗ [𝑛]
𝛽
𝑛 𝑘= 1
𝑒 𝑘
Where k ϵ N
α,β are meta values.
𝑛 𝑘 heuristic value.
𝑒 𝑘 edge value.
9. Set LC=LC+1.](https://image.slidesharecdn.com/solvingqosmulticastroutingproblemusingacoalgorithm-150907050735-lva1-app6891/85/Solving-QoS-multicast-routing-problem-using-aco-algorithm-45-320.jpg)