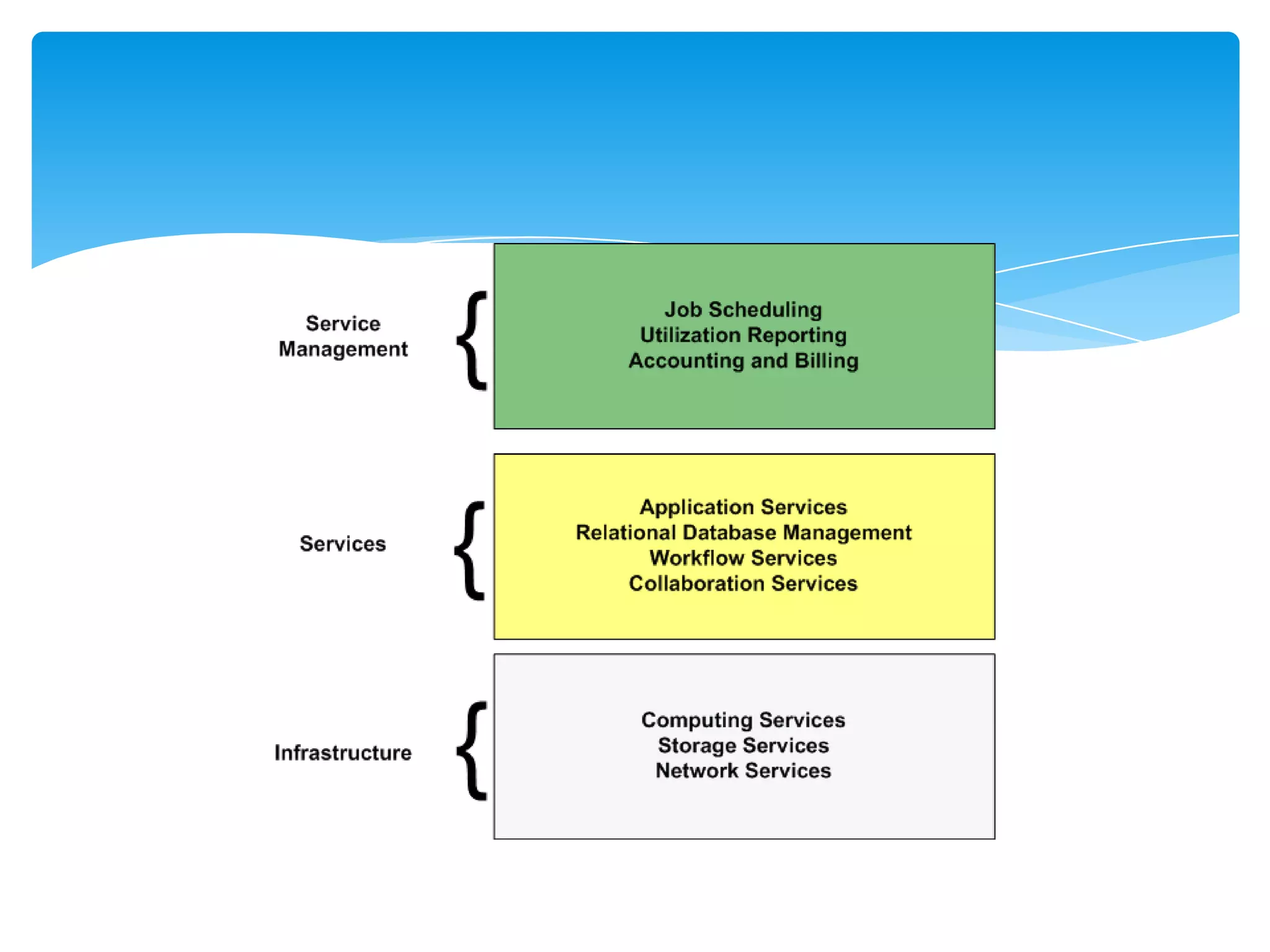
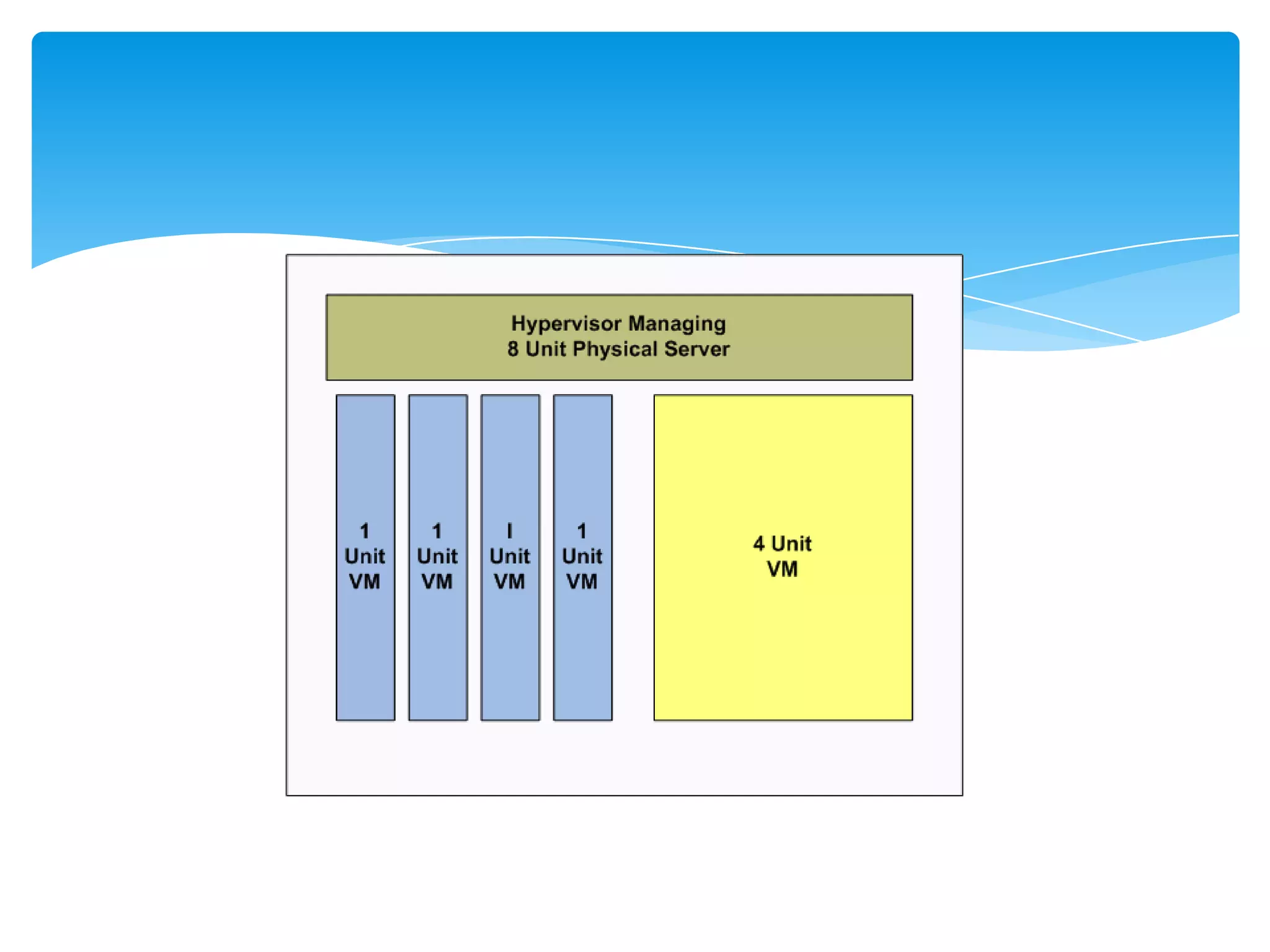
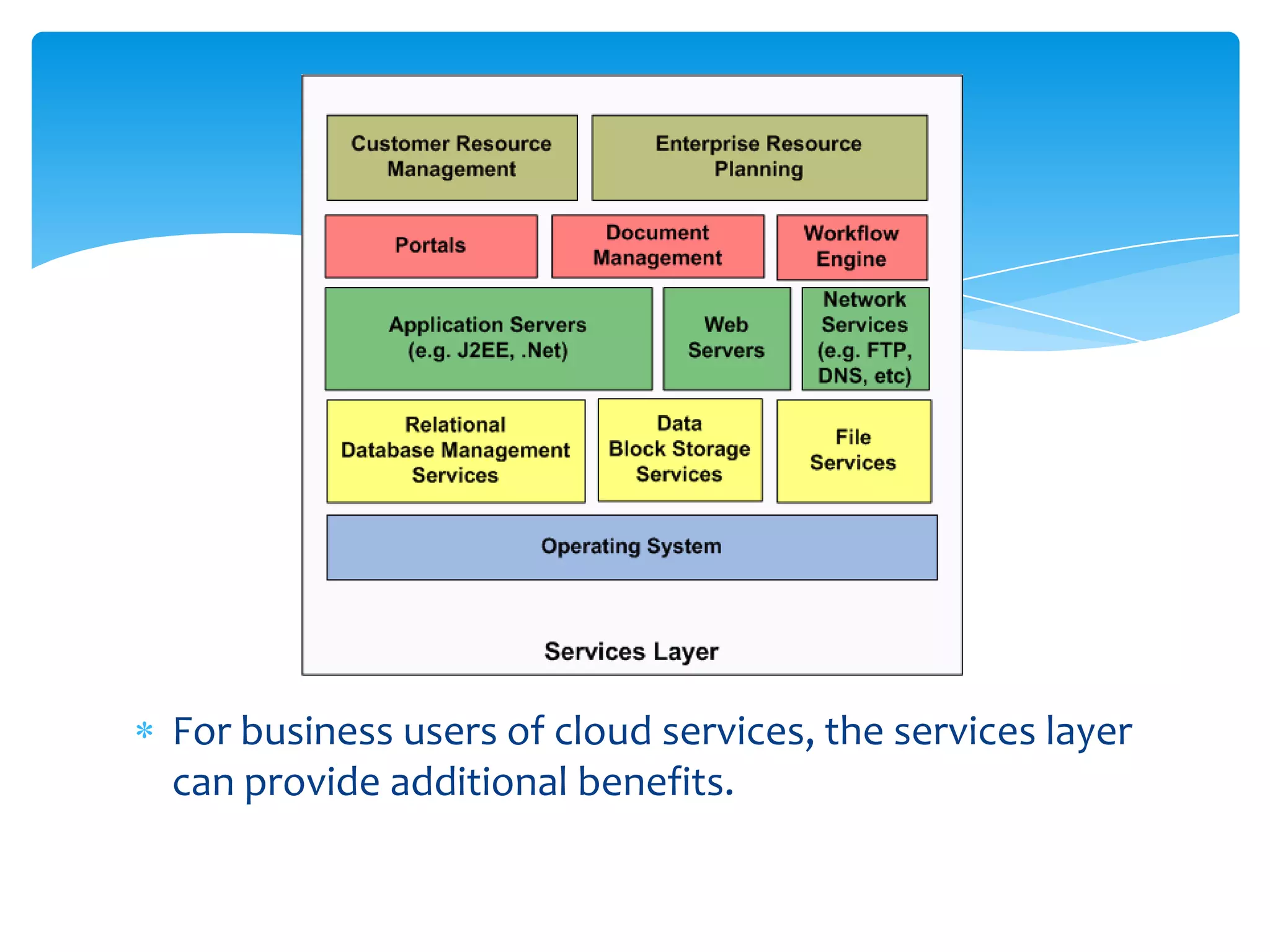
Cloud architectures can be thought of in layers, with each layer providing services to the next. There are three main layers: virtualization of resources, services layer, and server management processes. Virtualization abstracts hardware and provides flexibility. The services layer provides OS and application services. Management processes support service delivery through image management, deployment, scheduling, reporting, etc. When providing compute and storage services, considerations include hardware selection, virtualization, failover/redundancy, and reporting. Network services require capacity planning, redundancy, and reporting.