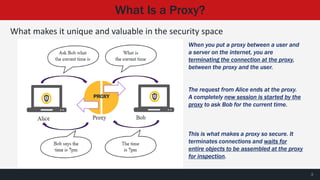
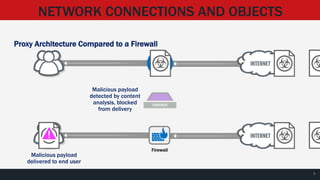
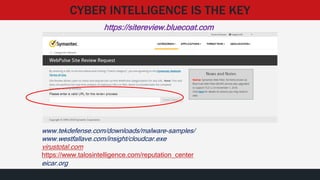
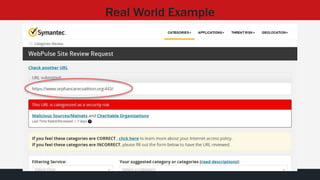
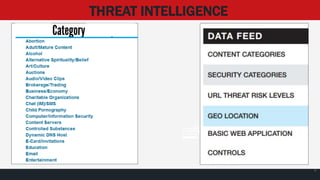
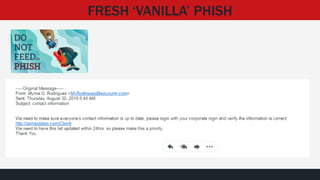
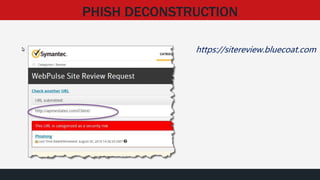
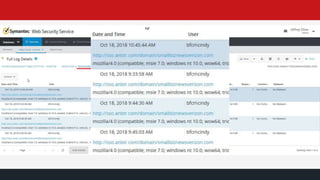
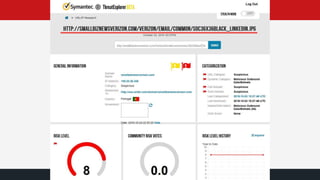
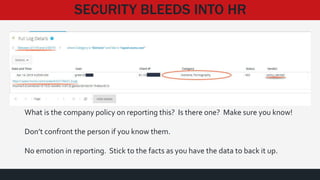
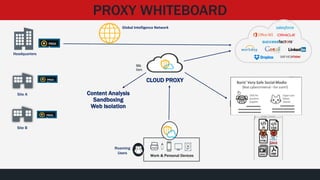
The document provides an overview of cloud proxy technology and cyber security. It discusses how proxies work by terminating connections between users and servers and inspecting transmitted objects. The document then shares several "real world" examples of how proxies can detect and prevent phishing attempts, malware infections, and other cyber threats by analyzing URLs, file downloads, and network traffic patterns. It emphasizes the importance of threat intelligence and how proxies use global intelligence networks to identify and block malicious activity in real-time.
![SESSION AGENDA
• Proxy Fundamentals [Quick overview as a foundation]
• Cyber Security ‘Real’ Forensics Stories
• Proxy Architecture in the Modern Business Environment
• Q & A](https://image.slidesharecdn.com/hackerhaltedoct2019-191031172637/85/Cloud-Proxy-Technology-Hacker-Halted-2019-Jeff-Silver-2-320.jpg)