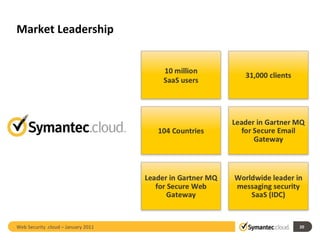
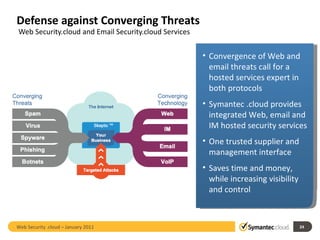
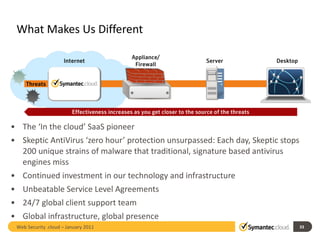
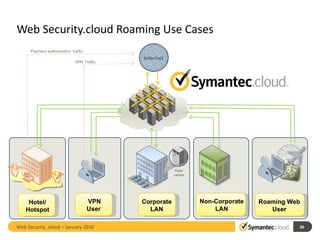
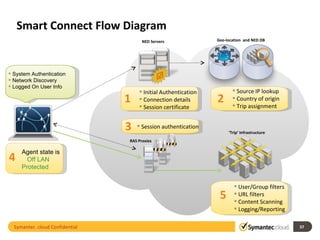
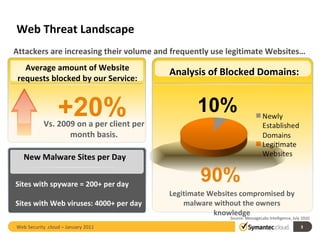
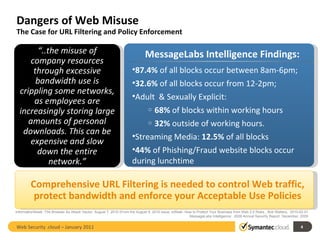
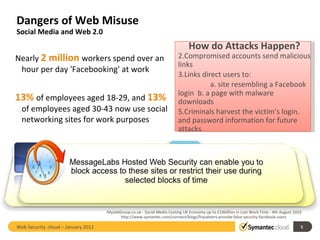
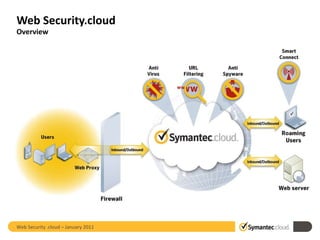
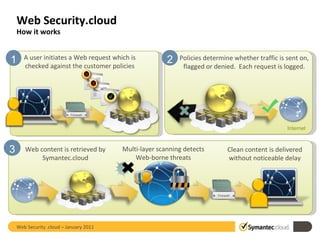
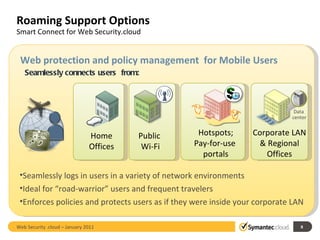
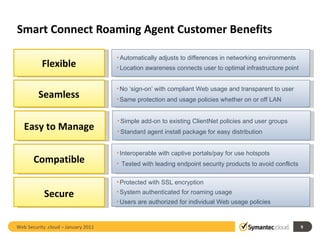
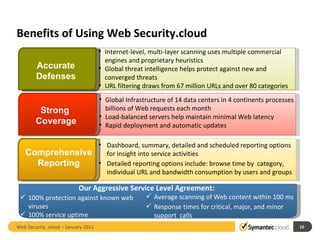
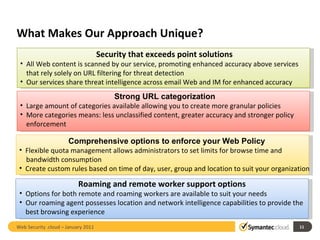
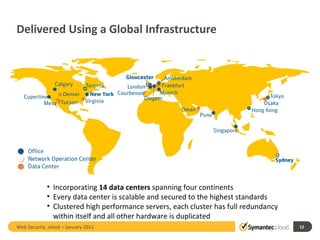
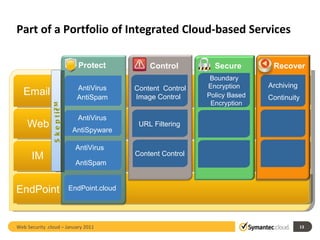
Web Security.cloud is a cloud-based web security service that provides comprehensive protection from web threats. It uses multi-layer scanning to detect malware and enforce acceptable use policies across 14 global data centers with minimal latency. The service offers reporting, mobile access, and a robust SLA to back its security, availability, and performance.

![Chris Russell [email_address] +61 (0) 2 9086 8285 Web Security .cloud – January 2011](https://image.slidesharecdn.com/websecuritycloud-13037756775104-phpapp02/85/Web-Security-and-Network-Security-16-320.jpg)