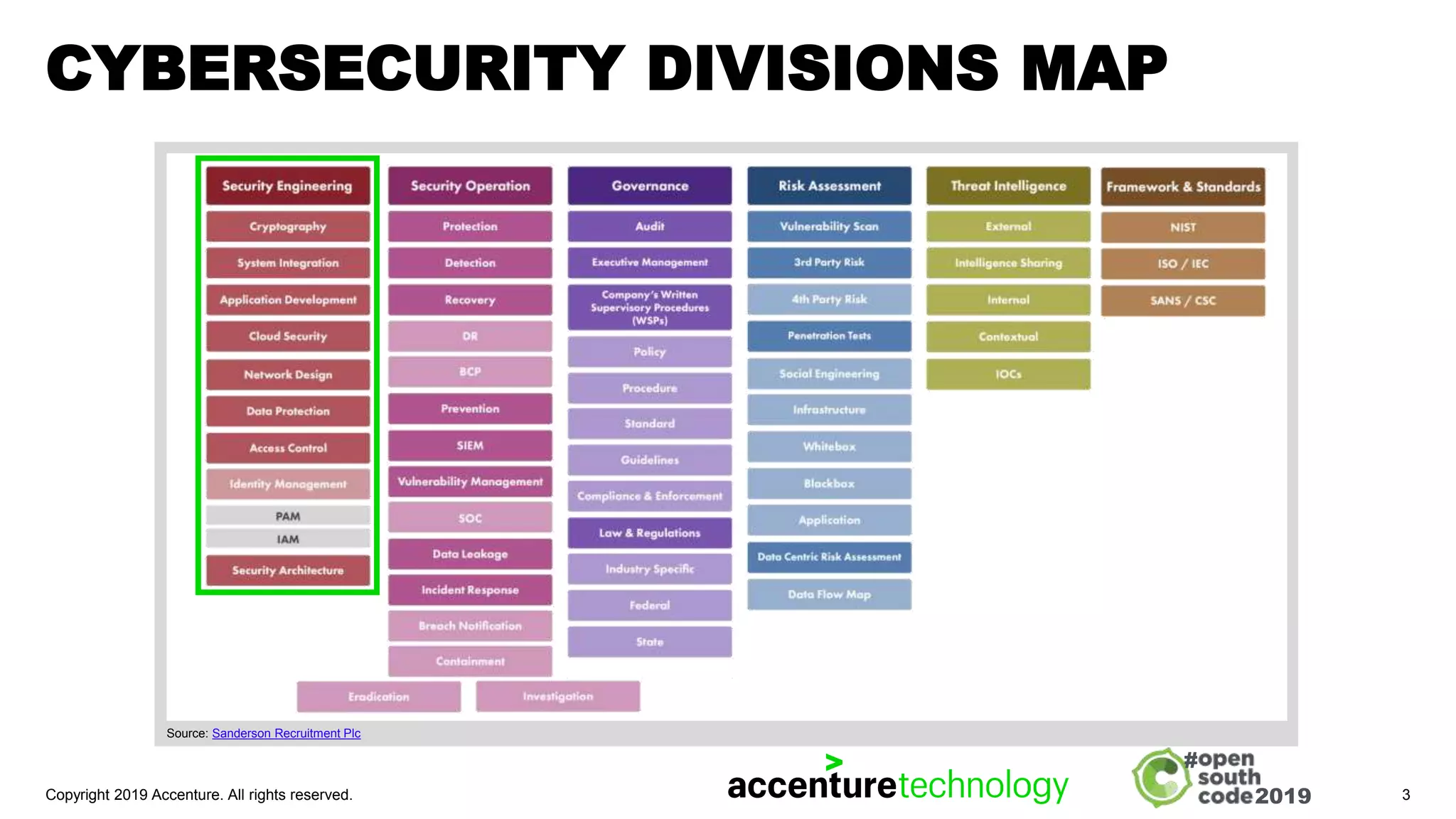
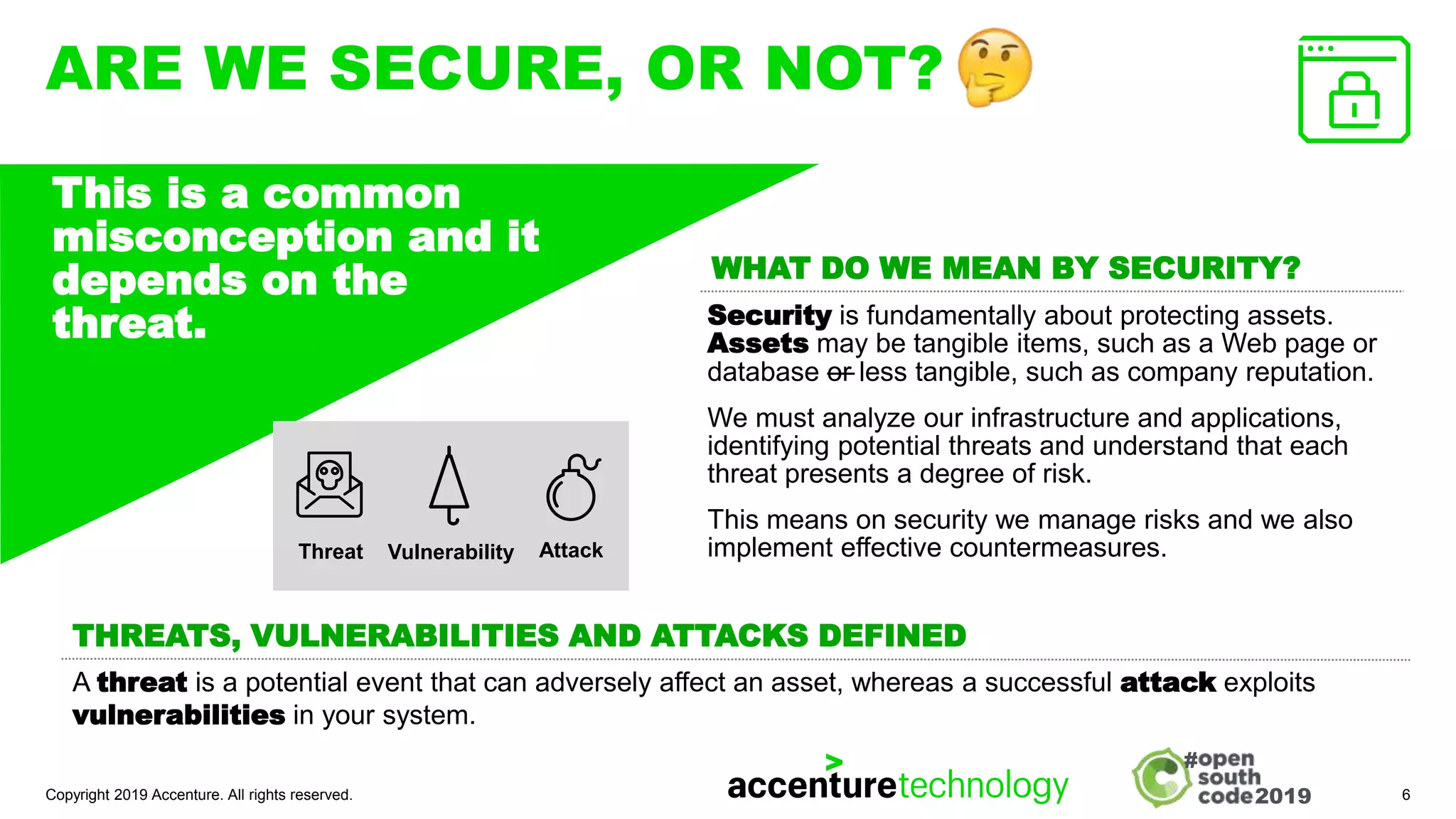
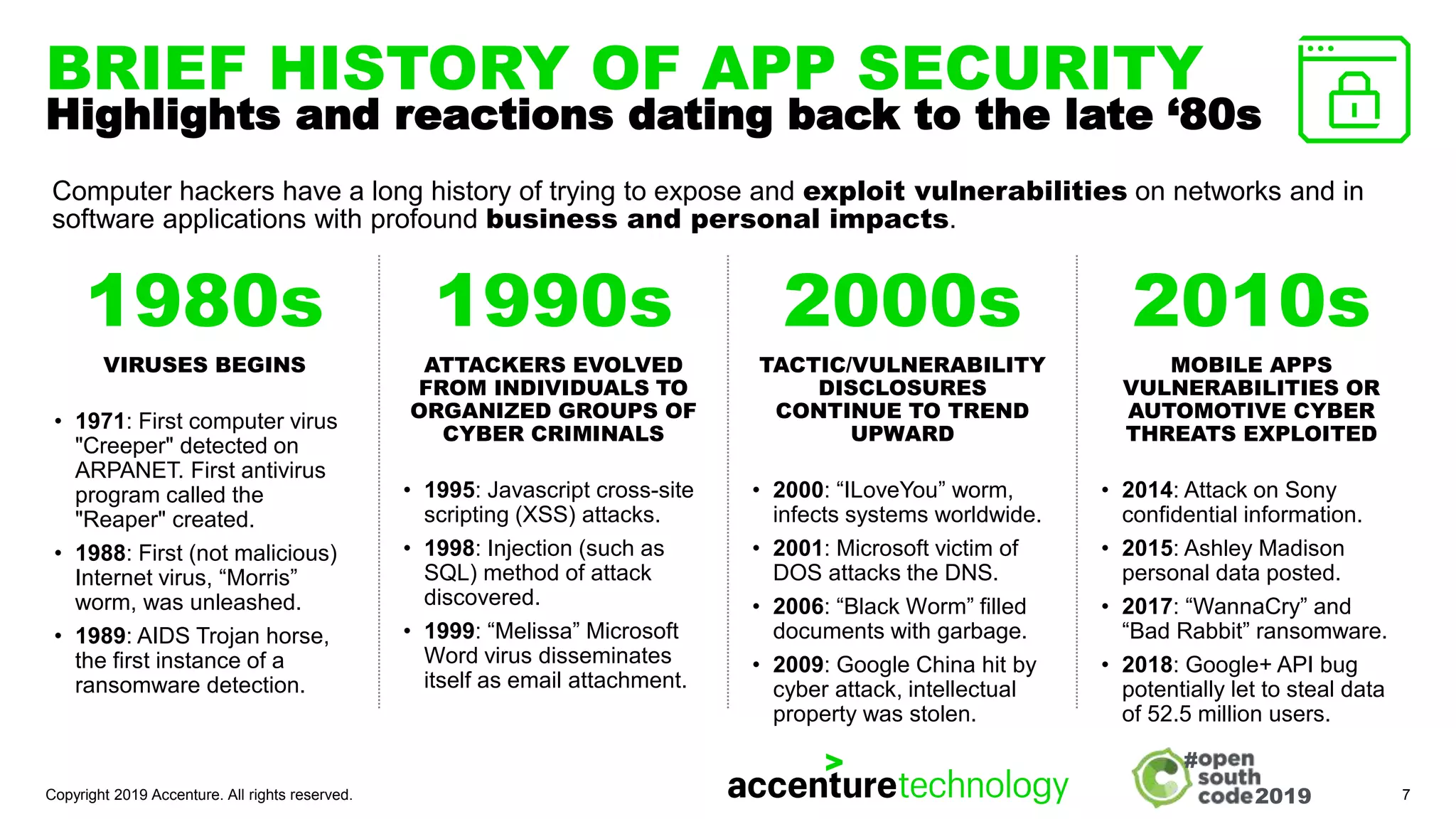
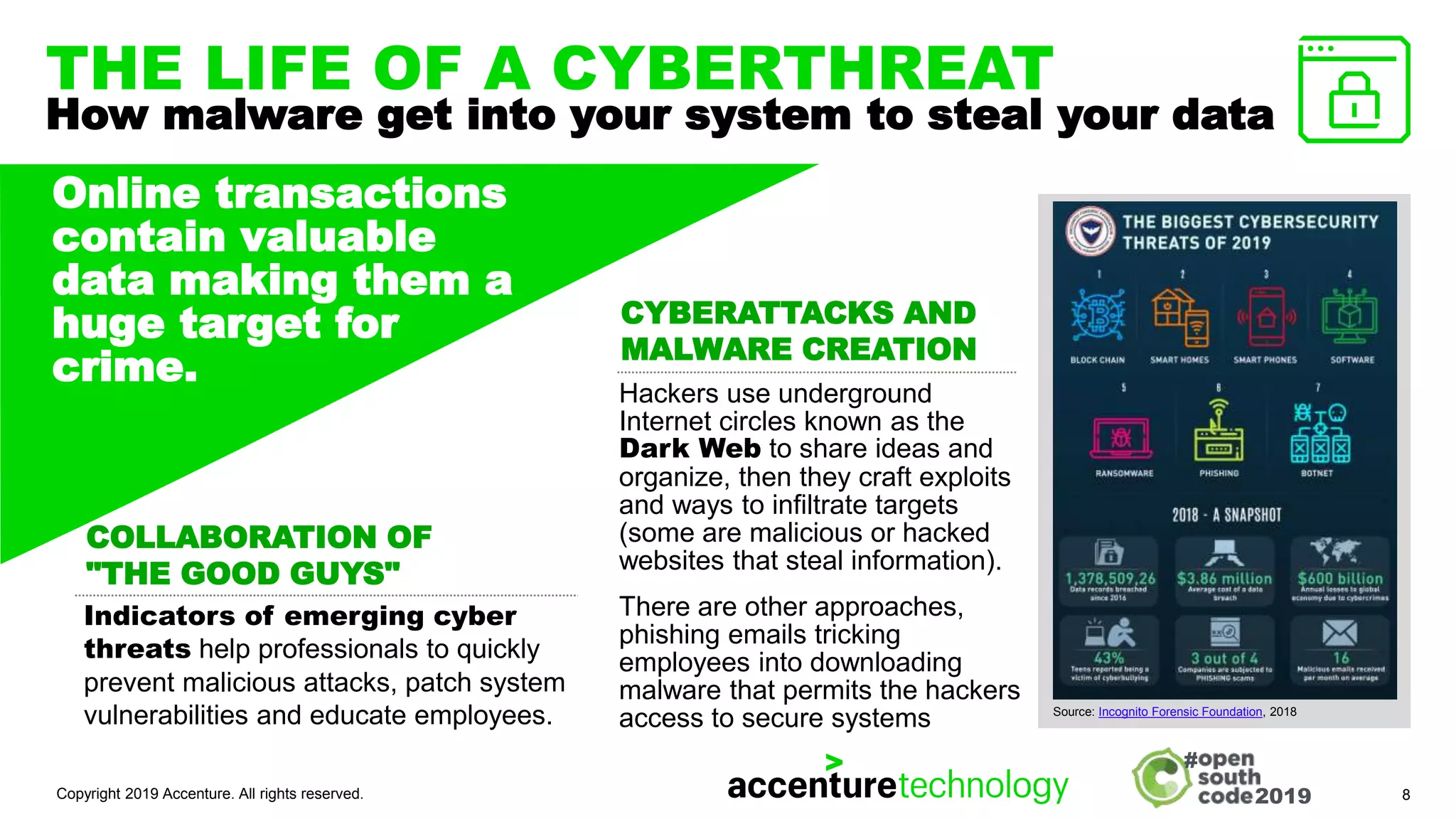
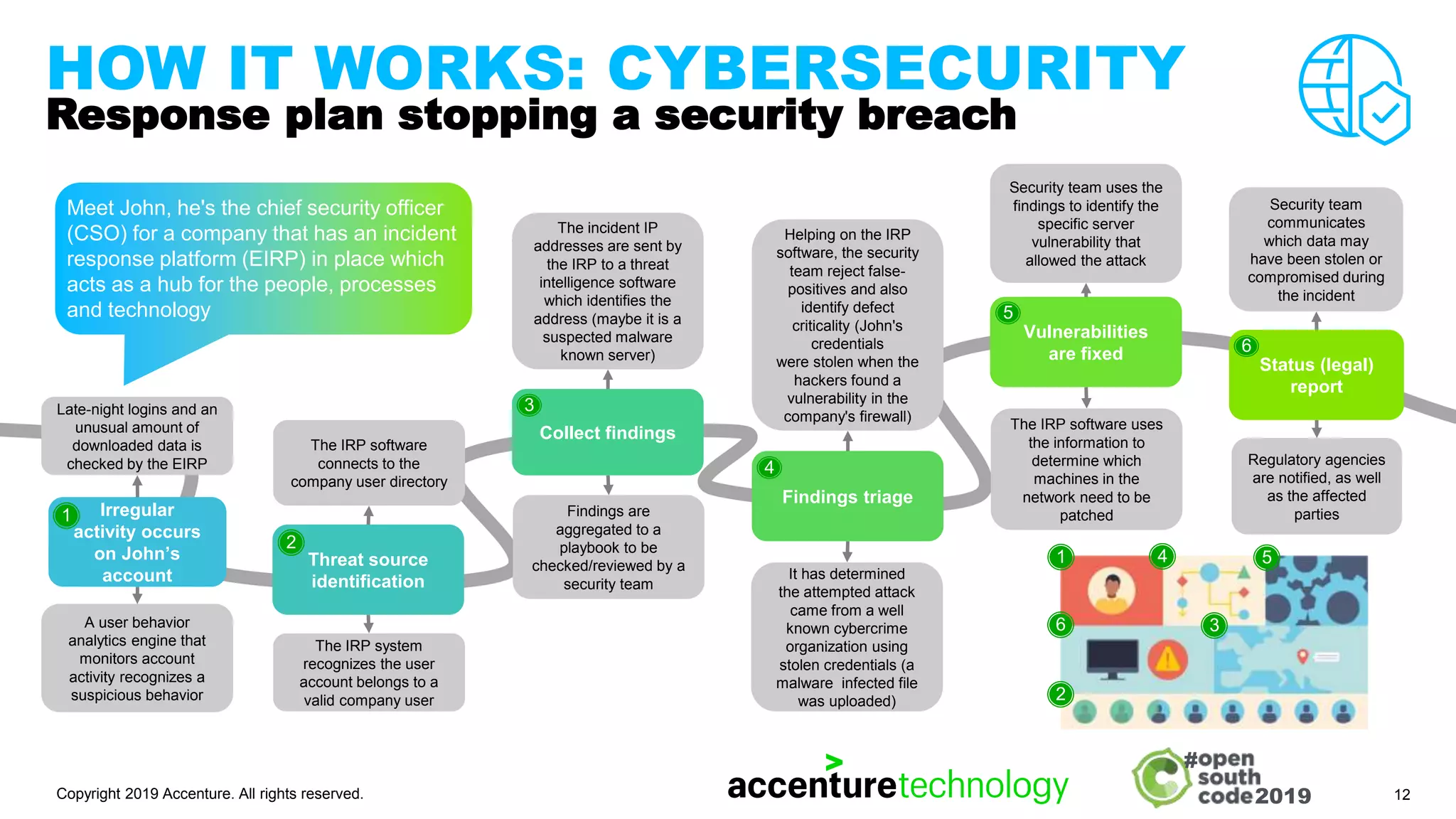
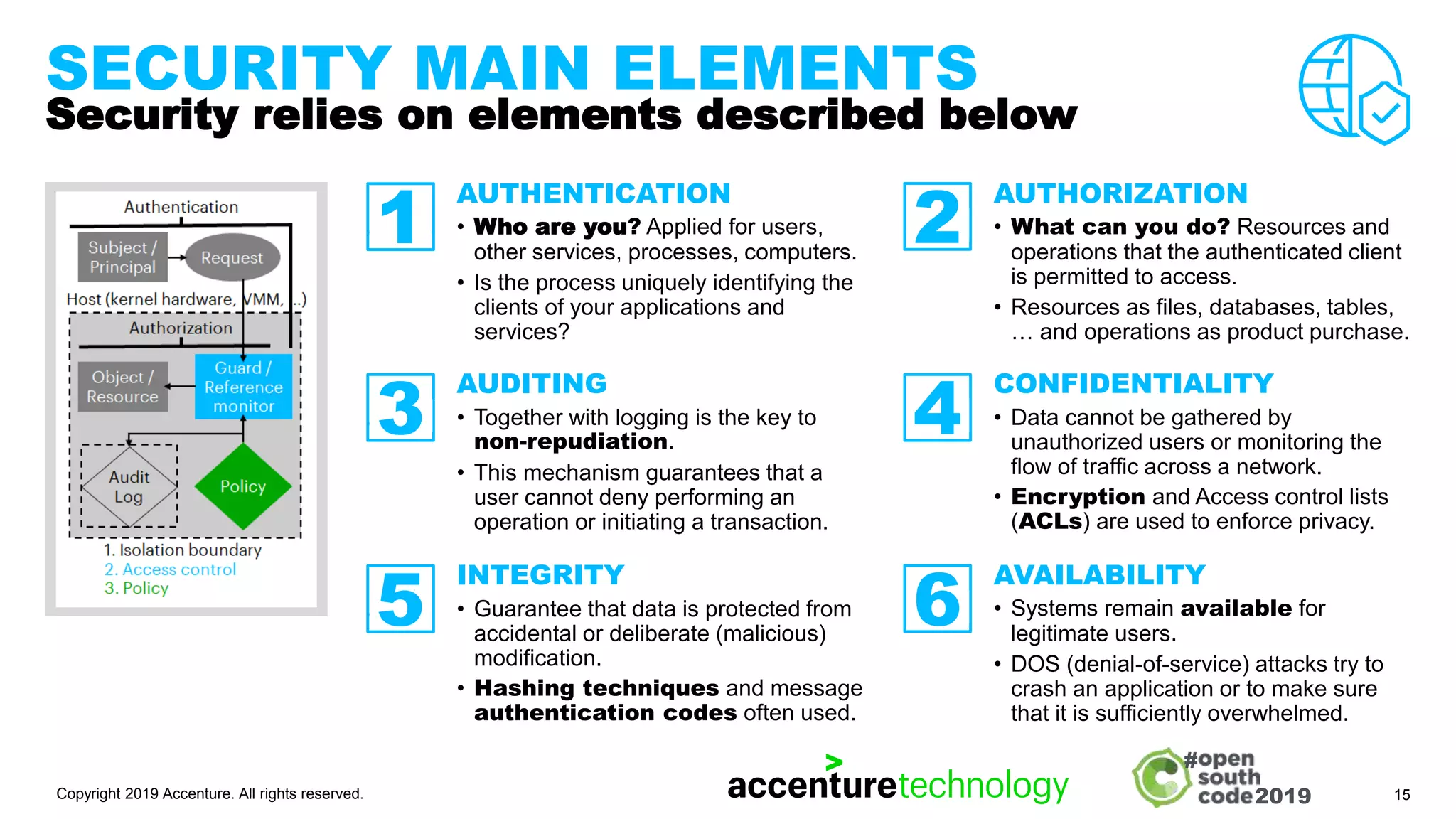
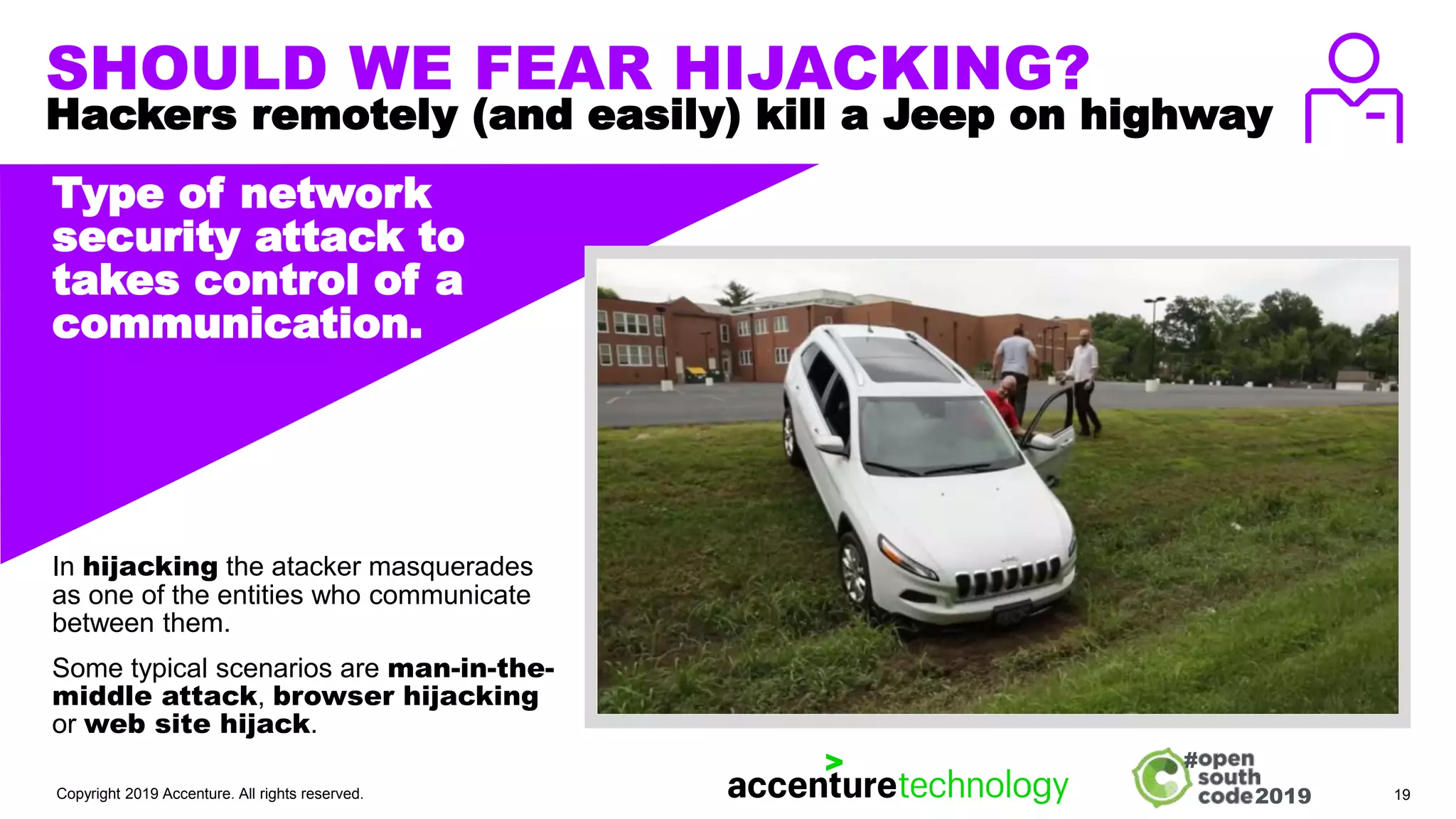
The document outlines fundamental concepts of application security, emphasizing the need to manage risks, identify threats, and implement effective countermeasures. It provides a historical perspective on cyber threats, profiling various vulnerabilities and their impacts, as well as highlighting the importance of a robust cybersecurity framework. Key principles for securing applications are discussed, along with various hacking scenarios, underscoring the evolving nature of cyber threats and the necessity for continuous awareness and adaptation.