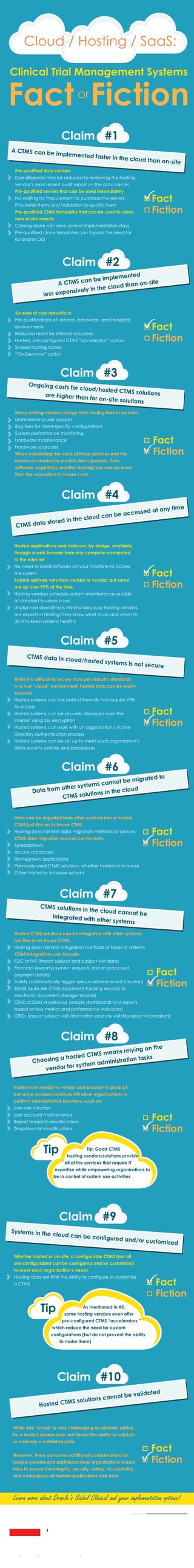
Cloud Clinical Trial Management Systems: Fact or Fiction
•
0 likes•486 views
How much do you know about running your clinical trial management system (CTMS) in the cloud? How does it compare to implementing a CTMS on-premises? View this infographic to learn more!
Report
Share
Report
Share
Download to read offline
Recommended
Cloud based clinical trial management system

A new Cloud based CTMS could challenge the traditional model and has the potential to transform and become the next generation of CTMS technology. Cloud computing is a major paradigm shift in how business applications of the future will be developed and delivered. The customers of a Cloud based CTMS will share, consume, and access platform resources as a service, and pay for only those resources that they use.
The Cloud, Cold Chain, and Compliance

A presentation on the Cold Chain, Cloud Computing, and Validation from the DicksonOne Product Manager, Matt McNamara, presented at the Cold Chain Conference in Dubai. Matt walks you through the different advantages to using cloud computing in the cold chain, and how new technology currently complies with regulatory agencies such as the FDA. Questions? Send us an email at content@dicksondata.com, and for more content on temperature, visit our blog at www.blog.dicksondata.com. Enjoy!
Endpoint Protection as a Service (EPaaS)

Slide presentasi Pak Samuel H. Winata dari McAfee dalam seminar "Accelerating Cloud Computing Adoption".
09ntc Server Virtualization Session Slides

Slides from the 2009 Nonprofit Technology Conference Session on Server Virtualization. These slides introduce the main concepts and suggest approaches for small, medium and large business scenarios. the latter set of slides are by matt eshelman of CITIDC, who presented with me.
Disaster Recovery Cook Book

Disaster Recovery Cookbook - Secret recipes for hybrid-cloud success.
Digital era make organizations must depend on system to operate, but sometime organizations facing the downtime and data loss which are expensive threats.
In this webinar you will learn how to selecting the right solution to protect, move, and recover mission-critical application with near 0% data loss in cost-effective model.
Cloud Based Disaster Recovery (DRaaS)

Slide presentasi Pak Iwan Cahya Widarta dari Datacomm Cloud Business dalam seminar "Accelerating Cloud Computing Adoption".
Azure SQL DB V12 at your service by Pieter Vanhove

Microsoft Azure SQL Database came in the picture when nobody was talking about cloud computing. Since that time, Azure SQL Database has known many versions but was rather limited in functionality. Backing up your database was not possible, the size of your database was limited, heap tables were not allowed…
Last November, Microsoft reached another milestone by introducing near-complete SQL Server engine compatibility and more premium performance. So, let’s get ready for this new release! I will to take you on a tour around the new Microsoft Azure SQL Database world. You will get an overview of the fundamentals of Microsoft Azure SQL Database administration – What’s new in the latest Update V12 – Azure SQL Database Auditing – Dynamic Data Masking – Row Level Security and many more. After attending this session you will have a good idea which features can be helpful to move your production database to Microsoft Azure SQL Database.
Recommended
Cloud based clinical trial management system

A new Cloud based CTMS could challenge the traditional model and has the potential to transform and become the next generation of CTMS technology. Cloud computing is a major paradigm shift in how business applications of the future will be developed and delivered. The customers of a Cloud based CTMS will share, consume, and access platform resources as a service, and pay for only those resources that they use.
The Cloud, Cold Chain, and Compliance

A presentation on the Cold Chain, Cloud Computing, and Validation from the DicksonOne Product Manager, Matt McNamara, presented at the Cold Chain Conference in Dubai. Matt walks you through the different advantages to using cloud computing in the cold chain, and how new technology currently complies with regulatory agencies such as the FDA. Questions? Send us an email at content@dicksondata.com, and for more content on temperature, visit our blog at www.blog.dicksondata.com. Enjoy!
Endpoint Protection as a Service (EPaaS)

Slide presentasi Pak Samuel H. Winata dari McAfee dalam seminar "Accelerating Cloud Computing Adoption".
09ntc Server Virtualization Session Slides

Slides from the 2009 Nonprofit Technology Conference Session on Server Virtualization. These slides introduce the main concepts and suggest approaches for small, medium and large business scenarios. the latter set of slides are by matt eshelman of CITIDC, who presented with me.
Disaster Recovery Cook Book

Disaster Recovery Cookbook - Secret recipes for hybrid-cloud success.
Digital era make organizations must depend on system to operate, but sometime organizations facing the downtime and data loss which are expensive threats.
In this webinar you will learn how to selecting the right solution to protect, move, and recover mission-critical application with near 0% data loss in cost-effective model.
Cloud Based Disaster Recovery (DRaaS)

Slide presentasi Pak Iwan Cahya Widarta dari Datacomm Cloud Business dalam seminar "Accelerating Cloud Computing Adoption".
Azure SQL DB V12 at your service by Pieter Vanhove

Microsoft Azure SQL Database came in the picture when nobody was talking about cloud computing. Since that time, Azure SQL Database has known many versions but was rather limited in functionality. Backing up your database was not possible, the size of your database was limited, heap tables were not allowed…
Last November, Microsoft reached another milestone by introducing near-complete SQL Server engine compatibility and more premium performance. So, let’s get ready for this new release! I will to take you on a tour around the new Microsoft Azure SQL Database world. You will get an overview of the fundamentals of Microsoft Azure SQL Database administration – What’s new in the latest Update V12 – Azure SQL Database Auditing – Dynamic Data Masking – Row Level Security and many more. After attending this session you will have a good idea which features can be helpful to move your production database to Microsoft Azure SQL Database.
Data Center Automation - Cisco ASAP Data Center

Cisco ASAP Data Center www.cisco.com/go/asap
Go to www.esgjrconsultinginc.com to learn more about Software/Network Engineering Solutins.
CMMS Hosted vs On-Premise Installation

The choice between CMMS hosted or an on-premise installation can be a difficult decision to make. Learn more about these two options and determine what option is best for you.
3 Types of Cloud Computing

Cloud computing may be a confusing subject because of the number of different businesses offering what they call “cloud computing,” but it's not as complicated as it sounds. There are three types of cloud computing infrastructures, each with its own benefits.
The New Rules For IT Security - SME's

With cyber-security breaches and hacks more common than ever before we've compiled the key IT-security rules that will help you to protect your business against the most likely threats. While this deck is predominately aimed at SMEs the rules apply broadly to businesses of any size.
5 Applications of Cloud Computing

Cloud computing environments offer benefits to business and IT departments that aren't easily gained through the use of traditional IT infrastructures. Here are five of the most common applications for cloud computing right now.
Corporate Laptop Backup and Recovery

Slides for webinar hosted by Druva and Curtis Preston on enterprise laptop bakcup and recovery.
Cloudciti Enterprise File Share (EFS)

Slide presentasi Pak Zulkarnaen Arsi dari Datacomm Cloud Business dalam seminar "Accelerating Cloud Computing Adoption".
Proact backup and storage vs ransomware 2021

How modern backup and storage systems can help ransomware situation
VMware: Enabling Software-Defined Storage Using Virtual SAN (Business Decisio...

Business decision maker for service provider
RapidScale CloudMail

RapidScale is an industry-leading company in the delivery, design, and support of Microsoft Exchange. Our Service Level Agreement on CloudMail is 100% uptime and all support is U.S. based as we take pride in providing world-class service.
Microsoft Exchange introduces built-in integrated email archiving, retention, and discovery capabilities that save costs and simplify the process of preserving business communications. RapidScale’s Hosted Exchange solution delivers on the capabilities demanded by mobile workforces. Access your business email, calendar and contacts on your desktop, laptop, smartphone, and Web browser so it can always go where you go. With Exchange, you will remain in control of your solution by tailoring it to your specific needs and ensuring that your communications are always available.
Microsoft Exchange 2010 combines built in anti-spam and encryption technologies with an advanced anti-virus infrastructure for efficient management of a wide range of security threats. You will see a high standard of physical and digital security for your data as it receives reliable monitoring and support from our team.
We guarantee 24x7x365 uptime and provide 100% US-based support to our clients. Our Cloud Engineers and Sr. Cloud Consultants are all internal employees and are dedicated to providing you with first-class support. You will have a dedicated Sr. Cloud Consultant to oversee your account specifically and assist with the transition.
Outlook Web App in Microsoft Exchange helps users be more efficient and productive across platforms and locations by giving them access to email, voice mail, instant messaging, SMS text messages, and more inside all popular browsers. Reduce complexity for your users and instead, offer secure access for multiple approved applications.
Our pay-as-you go plan is affordable and will help to remove the budgeting burden as well as hardware acquisition costs. Benefit from the latest version of Microsoft Exchange, and receive the latest software and security updates. With CloudMail, you will save short- and long-term costs while receiving superior support. This is how RapidScale’s CloudMail differs from its competitors.
While email is critical to your business, managing your Exchange server in-house can be expensive, time consuming, and full of hassles. Working with an external service provider can help you eliminate those headaches and take advantage of the full functionality of your Microsoft Hosted Exchange server.
Our CloudMail product set is built on our high performance fully redundant physical hardware platform just like the rest of our products sets. Uniformity between hardware and data centers ensures consistency across the board, eliminating the possibility of asymmetrical performance and simplifying diagnostics. For storage, we run NetApp controllers and storage shelves, Cisco UCS blade chassis for compute, and Cisco Nexus routers for core routing.
Cisco Powered DRaaS eBook

Use this comprehensive eBook to learn all about Cisco Powered Disaster Recovery-as-a-Service.
Compliance policies and procedures followed in data centers

compliance for data center, Compliance policies and procedures followed in data centers, policies and procedures in data center, standards in data center, data center standard policies
From Disaster to Recovery: Preparing Your IT for the Unexpected

Did you know that 22% of data center outages are caused by human error? Or that 10% are caused by weather incidents?
The impact of an unexpected outage for just a few hours or even days could be catastrophic to your business.
How would you like to minimize or even eliminate these business interruptions, and more?
Join us to discover:
• Useful and simple measures to use that can help you keep the lights on
• How to quickly recover when the worst-case scenario occurs
• How to achieve zero downtime and high availability
More Related Content
What's hot
Data Center Automation - Cisco ASAP Data Center

Cisco ASAP Data Center www.cisco.com/go/asap
Go to www.esgjrconsultinginc.com to learn more about Software/Network Engineering Solutins.
CMMS Hosted vs On-Premise Installation

The choice between CMMS hosted or an on-premise installation can be a difficult decision to make. Learn more about these two options and determine what option is best for you.
3 Types of Cloud Computing

Cloud computing may be a confusing subject because of the number of different businesses offering what they call “cloud computing,” but it's not as complicated as it sounds. There are three types of cloud computing infrastructures, each with its own benefits.
The New Rules For IT Security - SME's

With cyber-security breaches and hacks more common than ever before we've compiled the key IT-security rules that will help you to protect your business against the most likely threats. While this deck is predominately aimed at SMEs the rules apply broadly to businesses of any size.
5 Applications of Cloud Computing

Cloud computing environments offer benefits to business and IT departments that aren't easily gained through the use of traditional IT infrastructures. Here are five of the most common applications for cloud computing right now.
Corporate Laptop Backup and Recovery

Slides for webinar hosted by Druva and Curtis Preston on enterprise laptop bakcup and recovery.
Cloudciti Enterprise File Share (EFS)

Slide presentasi Pak Zulkarnaen Arsi dari Datacomm Cloud Business dalam seminar "Accelerating Cloud Computing Adoption".
Proact backup and storage vs ransomware 2021

How modern backup and storage systems can help ransomware situation
VMware: Enabling Software-Defined Storage Using Virtual SAN (Business Decisio...

Business decision maker for service provider
RapidScale CloudMail

RapidScale is an industry-leading company in the delivery, design, and support of Microsoft Exchange. Our Service Level Agreement on CloudMail is 100% uptime and all support is U.S. based as we take pride in providing world-class service.
Microsoft Exchange introduces built-in integrated email archiving, retention, and discovery capabilities that save costs and simplify the process of preserving business communications. RapidScale’s Hosted Exchange solution delivers on the capabilities demanded by mobile workforces. Access your business email, calendar and contacts on your desktop, laptop, smartphone, and Web browser so it can always go where you go. With Exchange, you will remain in control of your solution by tailoring it to your specific needs and ensuring that your communications are always available.
Microsoft Exchange 2010 combines built in anti-spam and encryption technologies with an advanced anti-virus infrastructure for efficient management of a wide range of security threats. You will see a high standard of physical and digital security for your data as it receives reliable monitoring and support from our team.
We guarantee 24x7x365 uptime and provide 100% US-based support to our clients. Our Cloud Engineers and Sr. Cloud Consultants are all internal employees and are dedicated to providing you with first-class support. You will have a dedicated Sr. Cloud Consultant to oversee your account specifically and assist with the transition.
Outlook Web App in Microsoft Exchange helps users be more efficient and productive across platforms and locations by giving them access to email, voice mail, instant messaging, SMS text messages, and more inside all popular browsers. Reduce complexity for your users and instead, offer secure access for multiple approved applications.
Our pay-as-you go plan is affordable and will help to remove the budgeting burden as well as hardware acquisition costs. Benefit from the latest version of Microsoft Exchange, and receive the latest software and security updates. With CloudMail, you will save short- and long-term costs while receiving superior support. This is how RapidScale’s CloudMail differs from its competitors.
While email is critical to your business, managing your Exchange server in-house can be expensive, time consuming, and full of hassles. Working with an external service provider can help you eliminate those headaches and take advantage of the full functionality of your Microsoft Hosted Exchange server.
Our CloudMail product set is built on our high performance fully redundant physical hardware platform just like the rest of our products sets. Uniformity between hardware and data centers ensures consistency across the board, eliminating the possibility of asymmetrical performance and simplifying diagnostics. For storage, we run NetApp controllers and storage shelves, Cisco UCS blade chassis for compute, and Cisco Nexus routers for core routing.
Cisco Powered DRaaS eBook

Use this comprehensive eBook to learn all about Cisco Powered Disaster Recovery-as-a-Service.
Compliance policies and procedures followed in data centers

compliance for data center, Compliance policies and procedures followed in data centers, policies and procedures in data center, standards in data center, data center standard policies
From Disaster to Recovery: Preparing Your IT for the Unexpected

Did you know that 22% of data center outages are caused by human error? Or that 10% are caused by weather incidents?
The impact of an unexpected outage for just a few hours or even days could be catastrophic to your business.
How would you like to minimize or even eliminate these business interruptions, and more?
Join us to discover:
• Useful and simple measures to use that can help you keep the lights on
• How to quickly recover when the worst-case scenario occurs
• How to achieve zero downtime and high availability
What's hot (20)
VMware: Enabling Software-Defined Storage Using Virtual SAN (Business Decisio...

VMware: Enabling Software-Defined Storage Using Virtual SAN (Business Decisio...
Compliance policies and procedures followed in data centers

Compliance policies and procedures followed in data centers
From Disaster to Recovery: Preparing Your IT for the Unexpected

From Disaster to Recovery: Preparing Your IT for the Unexpected
Viewers also liked
Getting the Most out of Siebel CTMS with APIs

If your organization is using Siebel CTMS, you're already ahead of the game. However, you can further enhance the user experience and functionality by utilizing existing third-party APIs with Siebel CTMS. An API, also known as application programming interface, offers the ability to leverage various third-party web applications within a particular solution.
Examples of how you can enhance Siebel CTMS with APIs:
-Exchange rates
-Company Twitter feed
-Google Maps for clinical sites
-LinkedIn profiles for investigators
-Company news and stock quotes
-Google Analytics for CTMS users
Perficient’s Param Singh, director of clinical trial management solutions, discussed several APIs that you can use to boost productivity and increase employee engagement. The webinar included a live demonstration of a Google Analytics integration with Siebel CTMS.
Integrating Siebel CTMS with Medidata Rave and Veeva Vault

Alliance Foundation Trials (AFT), a research organization that develops and conducts cancer clinical trials, selected Perficient’s Siebel Clinical accelerator, ASCEND, as its clinical trial management system (CTMS). Since the initial implementation they have added integrations with Medidata Rave, a unified electronic data capture (EDC) and clinical data management system (CDMS), and Veeva Vault eTMF, an electronic trial master file system.
Why did AFT choose ASCEND? Why did they prioritize the integration with Rave? What challenges led them to integrate with Veeva? How useful are the integrations proving to be? What are their future plans for their CTMS?
Param Singh, director of clinical operations solutions at Perficient, hosted a one-hour “fireside chat” with Jennifer Gaskin, operations director at AFT, in which Param asked all of these questions, and more.
Create and Simplify Flexible Order Management with IBM OMS

Successful order management projects are unique in their ability to create brand loyalty by demonstrating a unified commerce approach, spanning pre- and post-sales. Intelligent fulfillment is also essential to organizations selling complex configurable offerings, due to assembly and fulfillment workflows that may span multiple facilities and planning systems.
Perficient’s OMS Rapid Deployment Asset is a pre-configured solution that can be implemented quickly to demonstrate tangible results. The OMS RDA delivers pre-defined functionality, cuts implementation time, and provides flexible, process-based order management from multiple channels while enabling customized fulfillment based upon user-defined business requirements.
In our webinar, we discussed the key benefits of the OMS Rapid Deployment Asset:
-Rapid implementation using pre-defined accelerators
-Simplified connectivity with an IBM ESB that enables various enterprise applications to seamlessly communicate
-Pre-built artifacts for solution design, detail design, and test cases
-Quick delivery of the end-to-end solution to showcase value to your organization
Viewers also liked (7)
Making the Move to an Enterprise Clinical Trial Management System

Making the Move to an Enterprise Clinical Trial Management System
Integrating Siebel CTMS with Medidata Rave and Veeva Vault

Integrating Siebel CTMS with Medidata Rave and Veeva Vault
Create and Simplify Flexible Order Management with IBM OMS

Create and Simplify Flexible Order Management with IBM OMS
Similar to Cloud Clinical Trial Management Systems: Fact or Fiction
Cloud vs On-prem Data Warehouse.pdf

Make informed decisions for Data Management strategy by exploring the benefits and considerations of cloud-based and on-prem data warehousing solutions.
Pros And Cons Of Cloud-Based Security Solutions.pptx

Computer, network, and, more generally, data security have a growing subfield in Cloud Computing security, often known as cloud-based security. It, too, protects separate groups within a population by encrypting data in a structured hierarchy. There are significant risks and impediments to using cloud services, even though there are solid reasons for their use.
Cloud services and it security

This presentation explains the approach of a global utility company to identify the measures and controls available within a cloud service offering.
Cloud based dlms cosem metering head end

This webinar introduces the concept of Cloud-based HES (Head End System) for DLMS COSEM metering for Energy Data Management, AMI, Smart Grid and Smart Cities. With the meter data being crucial for all energy analytics and integration with multiple applications and systems becomes critical, Cloud-based HES provides a cost-effective, secure and scalable alternative for meter data acquisition
Pros and Cons of Cloud-Based and On-Premise CMMS Software

Are you looking for your organization's perfect Computerized Maintenance Management System (CMMS) software? Before deciding, it's essential to understand the pros and cons of cloud-based and on-premise solutions. Our comprehensive document explores the benefits and drawbacks of each option, providing valuable insights to help you make an informed choice. Whether you're seeking scalability, data security, cost-effectiveness, or customization, this document shares the essential information you need. Download it now and empower your maintenance management with the right CMMS software solution.
Can You Trust Cloud Security In Public Cloud?

SMBs are fast at adapting to innovation and change, cloud computing has grabbed the spotlight for safer business with data security solutions. Know how today's business can reap and adopt cloud security features for public cloud.
Part 2: Cloudera’s Operational Database: Unlocking New Benefits in the Cloud

3 Things to Learn About:
*On-premises versus the cloud
*Design & benefits of real-time operational data in the cloud
*Best practices and architectural considerations
Google cloud computing

The concept of “cloud computing” has been around since the beginning of the internet. Join Brian Pichman as he goes beyond storing files in the cloud and gets you started with the powerful Google Cloud service. The webinar will demonstrate how to get started with $300 in Google Credits to learn and play. Libraries can use Google Cloud to build websites, host applications, offload processes to save money/resources, or even migrate your environment to theirs. You do not need to be in IT to participate; as we will cover the basics of Cloud Computing and Google Cloud. You will need a Google Account prior to joining the webinar.
Cloud Computing

Cloud computing is the on-demand availability of computer system resources, especially data storage and computing power, without direct active management by the user. The term is generally used to describe data centers available to many users over the Internet.
Trust and Cloud computing, removing the need for the consumer to trust their ...

Presentation given at Society of Saudi Students Seminar, 28th April 2017
Cloud security risks

The transition to cloud services provides many advantages to the organization, including scalability, flexibility, efficiency, reducing cost and enjoying an enterprise grade level of security that meets the highest standards. However, cloud services also entail various risks that the organization must recognize and mitigate before the transition to the cloud.
Cloud security risks

The transition to cloud services contain many advantages to the organization such as, scalability, flexibility, efficiency, reducing cost and enjoying an enterprise grade level of security that meets the highest standards. However, cloud services also entail various risks that the organization must recognize and mitigate before the transition to the cloud.
Similar to Cloud Clinical Trial Management Systems: Fact or Fiction (20)
Cloud-based vs. On-site CTMS - Which is Right for Your Organization?

Cloud-based vs. On-site CTMS - Which is Right for Your Organization?
Pros And Cons Of Cloud-Based Security Solutions.pptx

Pros And Cons Of Cloud-Based Security Solutions.pptx
Pros and Cons of Cloud-Based and On-Premise CMMS Software

Pros and Cons of Cloud-Based and On-Premise CMMS Software
Part 2: Cloudera’s Operational Database: Unlocking New Benefits in the Cloud

Part 2: Cloudera’s Operational Database: Unlocking New Benefits in the Cloud
Trust and Cloud computing, removing the need for the consumer to trust their ...

Trust and Cloud computing, removing the need for the consumer to trust their ...
More from Perficient
The Perils of Clinical Trial Budgeting

This infographic discusses ClearTrial, Oracle's clinical trial budgeting software.
2013 OHSUG - Use Cases for using the Program Type View in Oracle Life Science...

Use Cases for using the Program Type View in Oracle Life Sciences Data Hub (LSH)
2013 OHSUG - The Ins and Outs of CTMS Data Migration

The Ins and Outs of Clinical Trial Management Software Data Migration
2013 OHSUG - Siebel Clinical Integration with Other Systems

Siebel CTMS Integration with Clinical and Safety Systems
2013 OHSUG - Sharing CTMS Data between Sponsors and Contract Research Organiz...

Sharing CTMS Data between Sponsors and CROs
2013 OHSUG - Oracle Clinical and RDC Training for Data Management and Clinica...

2013 OHSUG - Oracle Clinical and Oracle Remote Data Capture Training for Data Management and Clinical Teams
2013 OHSUG - Merging Multiple Drug Safety and Pharmacovigilance Databases int...

Merging Multiple Drug Safety and Pharmacovigilance Databases into One Global Oracle Argus Safety System
2013 OHSUG - Integration of Argus and Other Products Using the E2B Interchange

Integration of Argus and Other Products Using the E2B Interchange
2013 OHSUG - Use Cases for Using the Program Type View in Oracle Life Science...

Use Cases for Using the Program Type View in Oracle Life Sciences Data Hub (LSH)
2013 OHSUG - Facilitating Pharmacovigilance Globalization with Process Reengi...

Facilitating Pharmacovigilance Globalization with Process Reengineering
More from Perficient (20)
Freedom and Flexibility with Siebel Clinical (CTMS) Open UI

Freedom and Flexibility with Siebel Clinical (CTMS) Open UI
Managing Global Studies with Oracle's Siebel Clinical Trial Management System...

Managing Global Studies with Oracle's Siebel Clinical Trial Management System...
How to Rapidly Configure Oracle Life Sciences Data Hub (LSH) to Support the M...

How to Rapidly Configure Oracle Life Sciences Data Hub (LSH) to Support the M...
Using Oracle Health Sciences Data Management Workbench to Optimize the Manage...

Using Oracle Health Sciences Data Management Workbench to Optimize the Manage...
Integrating Oracle Argus Safety with other Clinical Systems Using Argus Inter...

Integrating Oracle Argus Safety with other Clinical Systems Using Argus Inter...
How St. Jude Medical Manages Oracle Clinical Studies Using Accel-Copy

How St. Jude Medical Manages Oracle Clinical Studies Using Accel-Copy
Evaluating and Investigating Drug Safety Signals with Public Databases

Evaluating and Investigating Drug Safety Signals with Public Databases
Plug & Play: Benefits of Out-of-the-Box Clinical Development Analytics (CDA) ...

Plug & Play: Benefits of Out-of-the-Box Clinical Development Analytics (CDA) ...
2013 OHSUG - Use Cases for using the Program Type View in Oracle Life Science...

2013 OHSUG - Use Cases for using the Program Type View in Oracle Life Science...
2013 OHSUG - The Ins and Outs of CTMS Data Migration

2013 OHSUG - The Ins and Outs of CTMS Data Migration
2013 OHSUG - Siebel Clinical Integration with Other Systems

2013 OHSUG - Siebel Clinical Integration with Other Systems
2013 OHSUG - Sharing CTMS Data between Sponsors and Contract Research Organiz...

2013 OHSUG - Sharing CTMS Data between Sponsors and Contract Research Organiz...
2013 OHSUG - Oracle Clinical and RDC Training for Data Management and Clinica...

2013 OHSUG - Oracle Clinical and RDC Training for Data Management and Clinica...
2013 OHSUG - Merging Multiple Drug Safety and Pharmacovigilance Databases int...

2013 OHSUG - Merging Multiple Drug Safety and Pharmacovigilance Databases int...
2013 OHSUG - Integration of Argus and Other Products Using the E2B Interchange

2013 OHSUG - Integration of Argus and Other Products Using the E2B Interchange
2013 OHSUG - Use Cases for Using the Program Type View in Oracle Life Science...

2013 OHSUG - Use Cases for Using the Program Type View in Oracle Life Science...
2013 OHSUG - Facilitating Pharmacovigilance Globalization with Process Reengi...

2013 OHSUG - Facilitating Pharmacovigilance Globalization with Process Reengi...
2013 OHSUG - Clinical Data Warehouse Implementation

2013 OHSUG - Clinical Data Warehouse Implementation
Recently uploaded
UiPath Test Automation using UiPath Test Suite series, part 3

Welcome to UiPath Test Automation using UiPath Test Suite series part 3. In this session, we will cover desktop automation along with UI automation.
Topics covered:
UI automation Introduction,
UI automation Sample
Desktop automation flow
Pradeep Chinnala, Senior Consultant Automation Developer @WonderBotz and UiPath MVP
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

Do you want to learn how to model and simulate an electrical network from scratch in under an hour?
Then welcome to this PowSyBl workshop, hosted by Rte, the French Transmission System Operator (TSO)!
During the webinar, you will discover the PowSyBl ecosystem as well as handle and study an electrical network through an interactive Python notebook.
PowSyBl is an open source project hosted by LF Energy, which offers a comprehensive set of features for electrical grid modelling and simulation. Among other advanced features, PowSyBl provides:
- A fully editable and extendable library for grid component modelling;
- Visualization tools to display your network;
- Grid simulation tools, such as power flows, security analyses (with or without remedial actions) and sensitivity analyses;
The framework is mostly written in Java, with a Python binding so that Python developers can access PowSyBl functionalities as well.
What you will learn during the webinar:
- For beginners: discover PowSyBl's functionalities through a quick general presentation and the notebook, without needing any expert coding skills;
- For advanced developers: master the skills to efficiently apply PowSyBl functionalities to your real-world scenarios.
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head of Product, Amazon Games
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

The IoT and OT threat landscape report has been prepared by the Threat Research Team at Sectrio using data from Sectrio, cyber threat intelligence farming facilities spread across over 85 cities around the world. In addition, Sectrio also runs AI-based advanced threat and payload engagement facilities that serve as sinks to attract and engage sophisticated threat actors, and newer malware including new variants and latent threats that are at an earlier stage of development.
The latest edition of the OT/ICS and IoT security Threat Landscape Report 2024 also covers:
State of global ICS asset and network exposure
Sectoral targets and attacks as well as the cost of ransom
Global APT activity, AI usage, actor and tactic profiles, and implications
Rise in volumes of AI-powered cyberattacks
Major cyber events in 2024
Malware and malicious payload trends
Cyberattack types and targets
Vulnerability exploit attempts on CVEs
Attacks on counties – USA
Expansion of bot farms – how, where, and why
In-depth analysis of the cyber threat landscape across North America, South America, Europe, APAC, and the Middle East
Why are attacks on smart factories rising?
Cyber risk predictions
Axis of attacks – Europe
Systemic attacks in the Middle East
Download the full report from here:
https://sectrio.com/resources/ot-threat-landscape-reports/sectrio-releases-ot-ics-and-iot-security-threat-landscape-report-2024/
Elizabeth Buie - Older adults: Are we really designing for our future selves?

Elizabeth Buie - Older adults: Are we really designing for our future selves?
Elevating Tactical DDD Patterns Through Object Calisthenics

After immersing yourself in the blue book and its red counterpart, attending DDD-focused conferences, and applying tactical patterns, you're left with a crucial question: How do I ensure my design is effective? Tactical patterns within Domain-Driven Design (DDD) serve as guiding principles for creating clear and manageable domain models. However, achieving success with these patterns requires additional guidance. Interestingly, we've observed that a set of constraints initially designed for training purposes remarkably aligns with effective pattern implementation, offering a more ‘mechanical’ approach. Let's explore together how Object Calisthenics can elevate the design of your tactical DDD patterns, offering concrete help for those venturing into DDD for the first time!
Epistemic Interaction - tuning interfaces to provide information for AI support

Paper presented at SYNERGY workshop at AVI 2024, Genoa, Italy. 3rd June 2024
https://alandix.com/academic/papers/synergy2024-epistemic/
As machine learning integrates deeper into human-computer interactions, the concept of epistemic interaction emerges, aiming to refine these interactions to enhance system adaptability. This approach encourages minor, intentional adjustments in user behaviour to enrich the data available for system learning. This paper introduces epistemic interaction within the context of human-system communication, illustrating how deliberate interaction design can improve system understanding and adaptation. Through concrete examples, we demonstrate the potential of epistemic interaction to significantly advance human-computer interaction by leveraging intuitive human communication strategies to inform system design and functionality, offering a novel pathway for enriching user-system engagements.
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Presented by Suzanne Phillips and Alex Marcotte
Welocme to ViralQR, your best QR code generator.

Welcome to ViralQR, your best QR code generator available on the market!
At ViralQR, we design static and dynamic QR codes. Our mission is to make business operations easier and customer engagement more powerful through the use of QR technology. Be it a small-scale business or a huge enterprise, our easy-to-use platform provides multiple choices that can be tailored according to your company's branding and marketing strategies.
Our Vision
We are here to make the process of creating QR codes easy and smooth, thus enhancing customer interaction and making business more fluid. We very strongly believe in the ability of QR codes to change the world for businesses in their interaction with customers and are set on making that technology accessible and usable far and wide.
Our Achievements
Ever since its inception, we have successfully served many clients by offering QR codes in their marketing, service delivery, and collection of feedback across various industries. Our platform has been recognized for its ease of use and amazing features, which helped a business to make QR codes.
Our Services
At ViralQR, here is a comprehensive suite of services that caters to your very needs:
Static QR Codes: Create free static QR codes. These QR codes are able to store significant information such as URLs, vCards, plain text, emails and SMS, Wi-Fi credentials, and Bitcoin addresses.
Dynamic QR codes: These also have all the advanced features but are subscription-based. They can directly link to PDF files, images, micro-landing pages, social accounts, review forms, business pages, and applications. In addition, they can be branded with CTAs, frames, patterns, colors, and logos to enhance your branding.
Pricing and Packages
Additionally, there is a 14-day free offer to ViralQR, which is an exceptional opportunity for new users to take a feel of this platform. One can easily subscribe from there and experience the full dynamic of using QR codes. The subscription plans are not only meant for business; they are priced very flexibly so that literally every business could afford to benefit from our service.
Why choose us?
ViralQR will provide services for marketing, advertising, catering, retail, and the like. The QR codes can be posted on fliers, packaging, merchandise, and banners, as well as to substitute for cash and cards in a restaurant or coffee shop. With QR codes integrated into your business, improve customer engagement and streamline operations.
Comprehensive Analytics
Subscribers of ViralQR receive detailed analytics and tracking tools in light of having a view of the core values of QR code performance. Our analytics dashboard shows aggregate views and unique views, as well as detailed information about each impression, including time, device, browser, and estimated location by city and country.
So, thank you for choosing ViralQR; we have an offer of nothing but the best in terms of QR code services to meet business diversity!
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar
Key Trends Shaping the Future of Infrastructure.pdf

Keynote at DIGIT West Expo, Glasgow on 29 May 2024.
Cheryl Hung, ochery.com
Sr Director, Infrastructure Ecosystem, Arm.
The key trends across hardware, cloud and open-source; exploring how these areas are likely to mature and develop over the short and long-term, and then considering how organisations can position themselves to adapt and thrive.
PHP Frameworks: I want to break free (IPC Berlin 2024)

In this presentation, we examine the challenges and limitations of relying too heavily on PHP frameworks in web development. We discuss the history of PHP and its frameworks to understand how this dependence has evolved. The focus will be on providing concrete tips and strategies to reduce reliance on these frameworks, based on real-world examples and practical considerations. The goal is to equip developers with the skills and knowledge to create more flexible and future-proof web applications. We'll explore the importance of maintaining autonomy in a rapidly changing tech landscape and how to make informed decisions in PHP development.
This talk is aimed at encouraging a more independent approach to using PHP frameworks, moving towards a more flexible and future-proof approach to PHP development.
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

The publishing industry has been selling digital audiobooks and ebooks for over a decade and has found its groove. What’s changed? What has stayed the same? Where do we go from here? Join a group of leading sales peers from across the industry for a conversation about the lessons learned since the popularization of digital books, best practices, digital book supply chain management, and more.
Link to video recording: https://bnctechforum.ca/sessions/selling-digital-books-in-2024-insights-from-industry-leaders/
Presented by BookNet Canada on May 28, 2024, with support from the Department of Canadian Heritage.
Recently uploaded (20)
UiPath Test Automation using UiPath Test Suite series, part 3

UiPath Test Automation using UiPath Test Suite series, part 3
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...
State of ICS and IoT Cyber Threat Landscape Report 2024 preview

State of ICS and IoT Cyber Threat Landscape Report 2024 preview
Elizabeth Buie - Older adults: Are we really designing for our future selves?

Elizabeth Buie - Older adults: Are we really designing for our future selves?
Elevating Tactical DDD Patterns Through Object Calisthenics

Elevating Tactical DDD Patterns Through Object Calisthenics
FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf

FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf
Epistemic Interaction - tuning interfaces to provide information for AI support

Epistemic Interaction - tuning interfaces to provide information for AI support
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
Assure Contact Center Experiences for Your Customers With ThousandEyes

Assure Contact Center Experiences for Your Customers With ThousandEyes
Free Complete Python - A step towards Data Science

Free Complete Python - A step towards Data Science
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Assuring Contact Center Experiences for Your Customers With ThousandEyes
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf
Key Trends Shaping the Future of Infrastructure.pdf

Key Trends Shaping the Future of Infrastructure.pdf
PHP Frameworks: I want to break free (IPC Berlin 2024)

PHP Frameworks: I want to break free (IPC Berlin 2024)
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

Transcript: Selling digital books in 2024: Insights from industry leaders - T...
Cloud Clinical Trial Management Systems: Fact or Fiction
- 1. Tip Learn more about Oracle’s Siebel Clinical and your implementation options! Clinical Trial Management Systems Fact Fiction A CTMS can be implemented faster in the cloud than on-site Claim #1 Pre-qualified data centers Due diligence may be reduced to reviewing the hosting vendor’s most recent audit report on the data center Pre-qualified servers that can be used immediately No waiting for Procurement to purchase the servers, IT to install them, and Validation to qualify them Pre-qualified CTMS templates that can be used to clone new environments Cloning alone can save several implementation days Pre-qualified clone templates can bypass the need for IQ and/or OQ Fact Fiction Sources of cost reductions: Pre-qualifications of vendors, hardware, and template environments Reduced need for internal resources Hosted, pre-configured CTMS “accelerator” option Shared hosting option “On-Demand” option Cloud / Hosting / SaaS: Factor Fiction A CTMS can be implemented less expensively in the cloud than on-site Claim #2 Ongoing costs for cloud/hosted CTMS solutionsare higher than for on-site solutions Claim #3 Many hosting vendors design their hosting fees to include: Unlimited end-user support Bug fixes for client-specific configurations System performance monitoring Hardware maintenance Hardware upgrades When calculating the costs of these services and the resources needed to provide them (people, time, software, expertise), monthly hosting fees can be lower than the equivalent in-house costs Fact Fiction Hosted applications and data are, by design, available through a web browser from any computer connected to the Internet No need to install software on your machine to access the system System uptimes vary from vendor to vendor, but some are up over 99% of the time Hosting vendors schedule system maintenance outside of standard business hours Unplanned downtime is minimal because hosting vendors are experts in hosting; they know what to do and when to do it to keep systems healthy CTMS data stored in the cloud can be accessed at any time Claim #4 Fact Fiction CTMS data in cloud/hosted systems is not secure Claim #5 While it is difficult to secure data per industry standards in a true “cloud” environment, hosted data can be easily secured Hosted systems can live behind firewalls that require VPN to access Hosted systems can be securely deployed over the Internet using SSL encryption Hosted systems can work with an organization’s Active Directory authentication process Hosted systems can be set up to meet each organization’s data security policies and procedures Fact Fiction Data can be migrated from other systems into a hosted CTMS just like an in-house CTMS Hosting does not limit data migration methods or sources CTMS data migration sources can include: Spreadsheets Access databases Homegrown applications Previously-used CTMS solutions, whether hosted or in-house Other hosted or in-house systems Data from other systems cannot be migrated to CTMS solutions in the cloud Claim #6 Fact Fiction CTMS solutions in the cloud cannot beintegrated with other systems Claim #7 Hosted CTMS solutions can be integrated with other systems just like an in-house CTMS Hosting does not limit integration methods or types of systems CTMS integrations can include: EDC or IVR (import subject and subject visit data) Financial (export payment requests, import processed payment details) Safety (automatically trigger serious adverse event creation) EDMS (auto-link CTMS document tracking records to electronic document storage records) Clinical Data Warehouse (create dashboards and reports based on key metrics and performance indicators) CROs (Import subject visit information and site visit/trip report information) Fact Fiction Varies from vendor to vendor and product to product, but some vendors/solutions still allow organizations to perform administrative functions, such as: User role creation User account maintenance Report template modifications Dropdown list modifications Choosing a hosted CTMS means relying on the vendor for system administration tasks Claim #8 Fact Fiction Systems in the cloud can be configured and/or customized Claim #9 Whether hosted or on-site, a configurable CTMS (not all are configurable) can be configured and/or customized to meet each organization’s needs Hosting does not limit the ability to configure or customize a CTMS Fact Fiction While true “cloud” is very challenging to validate, opting for a hosted system does not hinder the ability to validate or maintain a validated state However, there are some additional considerations for hosted systems and additional steps organizations should take to ensure the integrity, security, safety, accessibility, and compliance of hosted applications and data Hosted CTMS solutions cannot be validated Claim #10 As mentioned in #2, some hosting vendors even offer pre-configured CTMS “accelerators,” which reduce the need for custom configurations (but do not prevent the ability to make them) Tip Tip: Good CTMS hosting vendors/solutions provide all of the services that require IT expertise while empowering organizations to be in control of system use activities Fact Fiction
