The document discusses various methods for downloading and storing digital information, including:
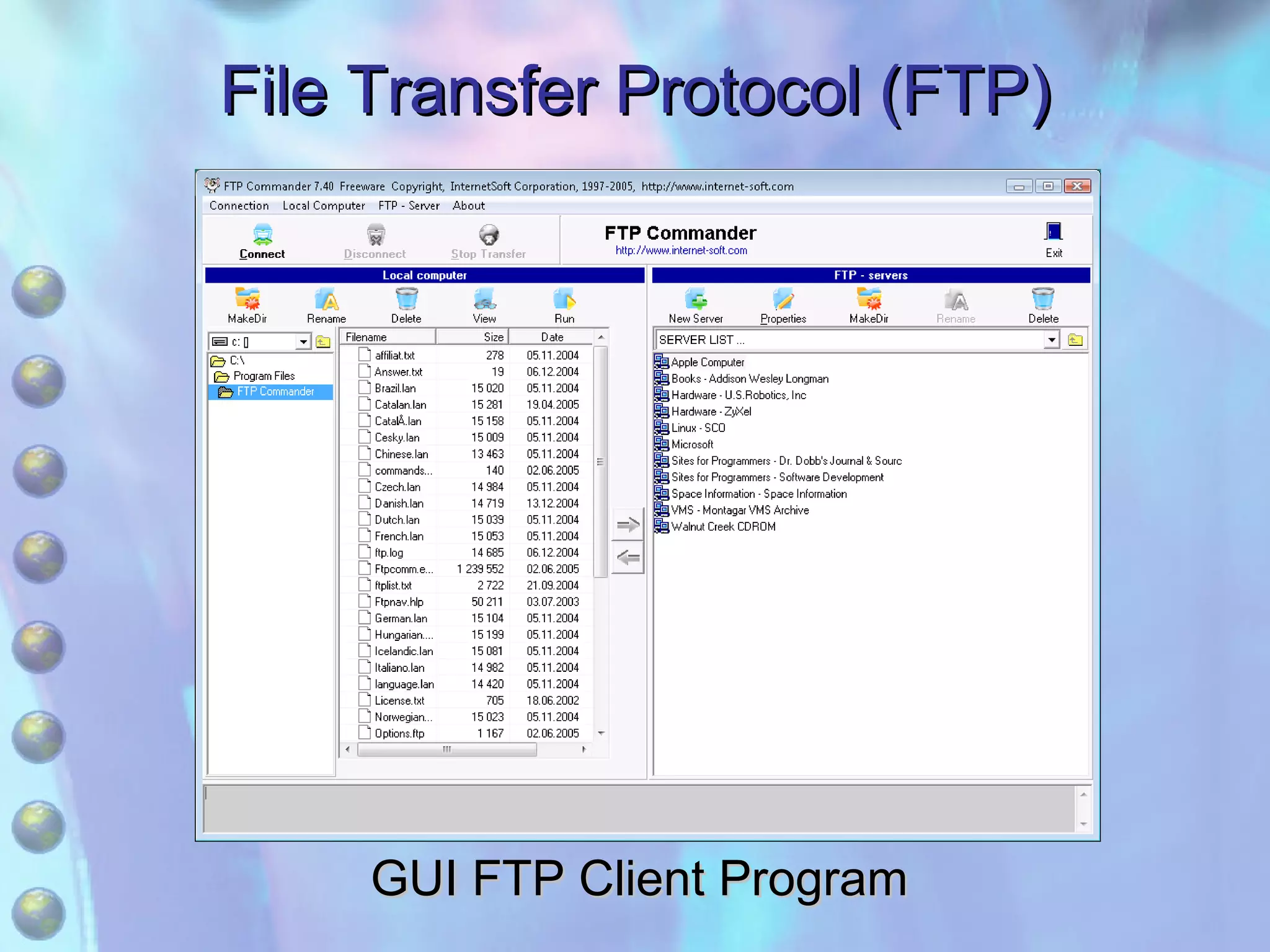
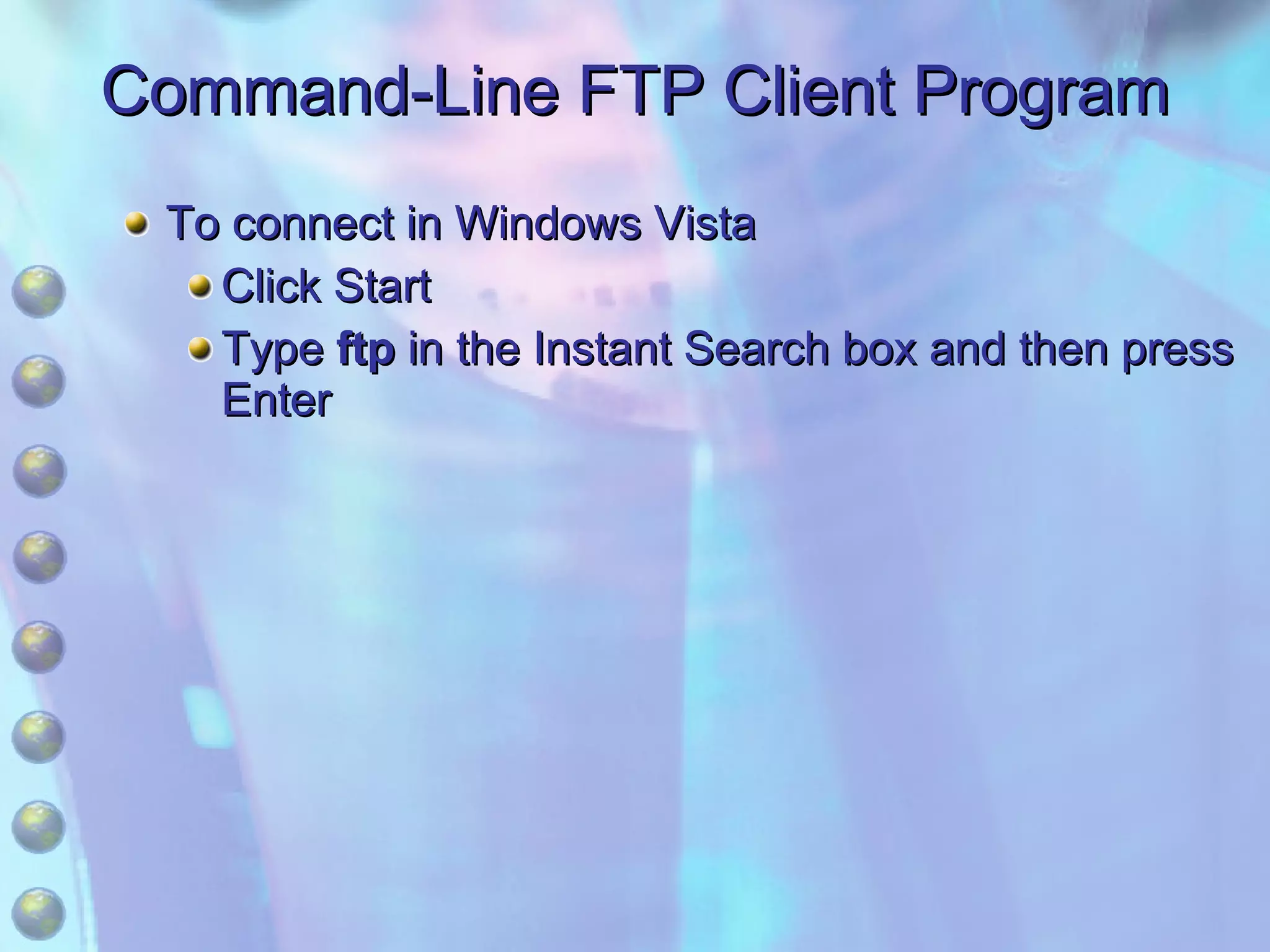
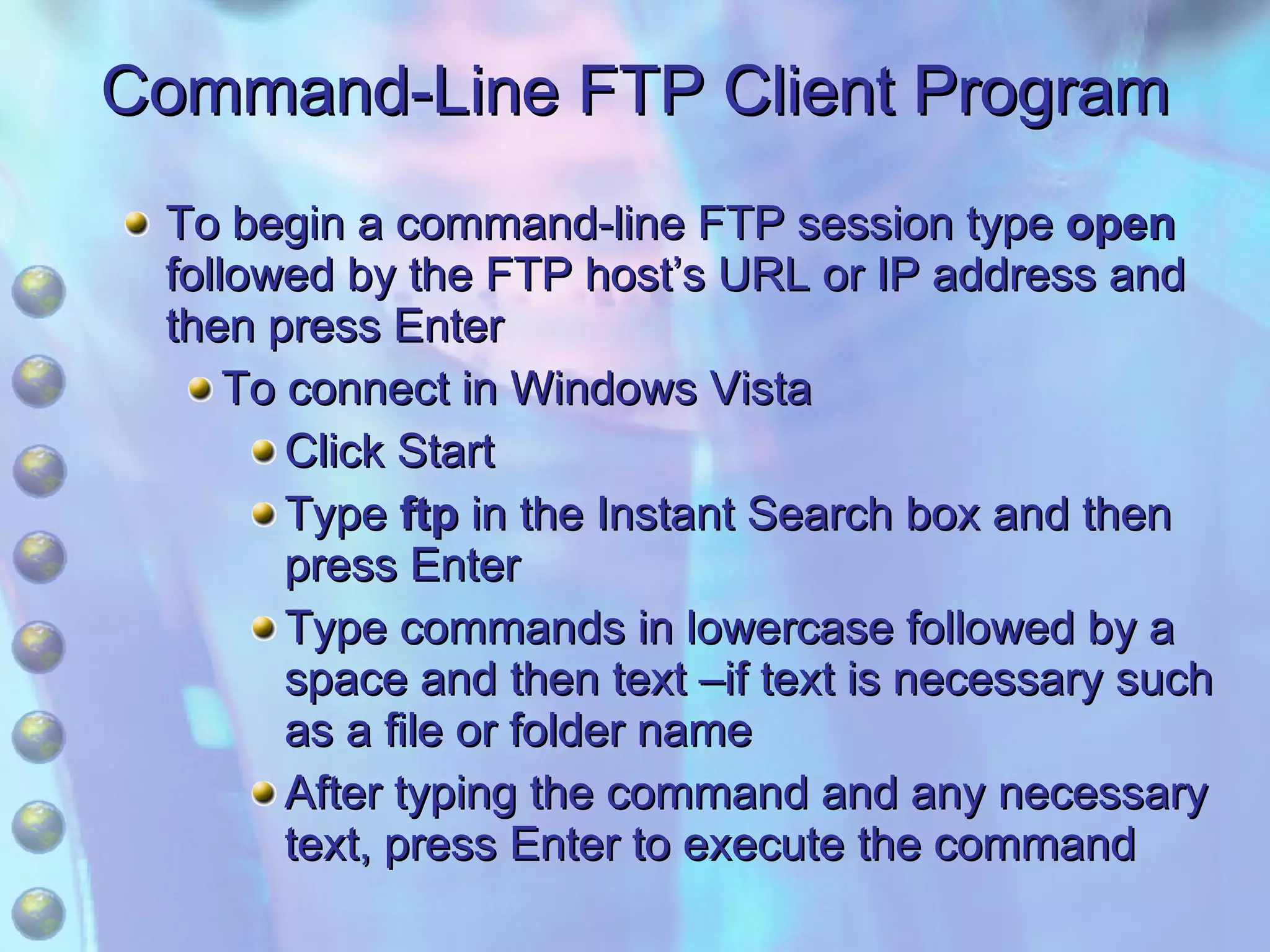
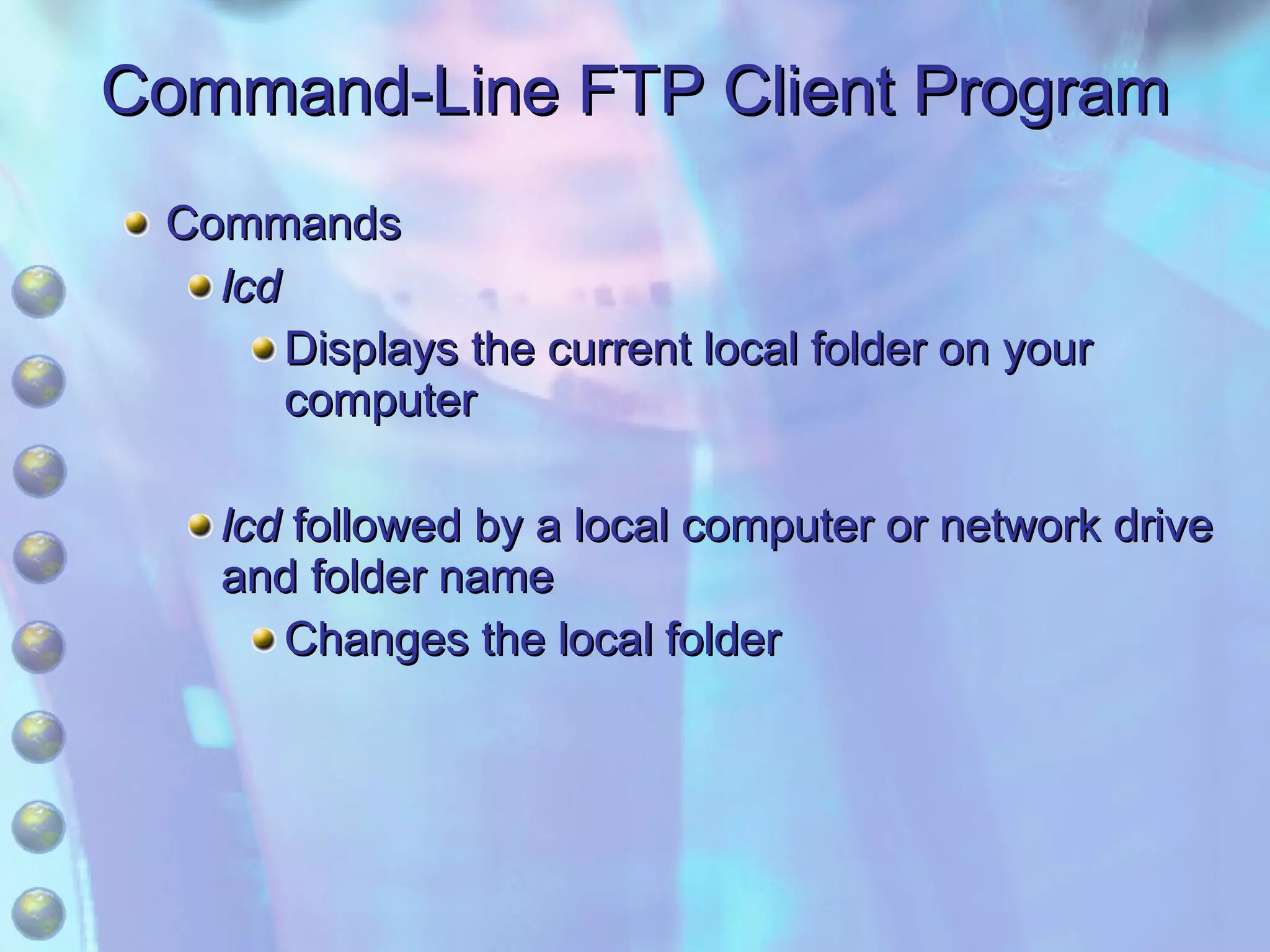
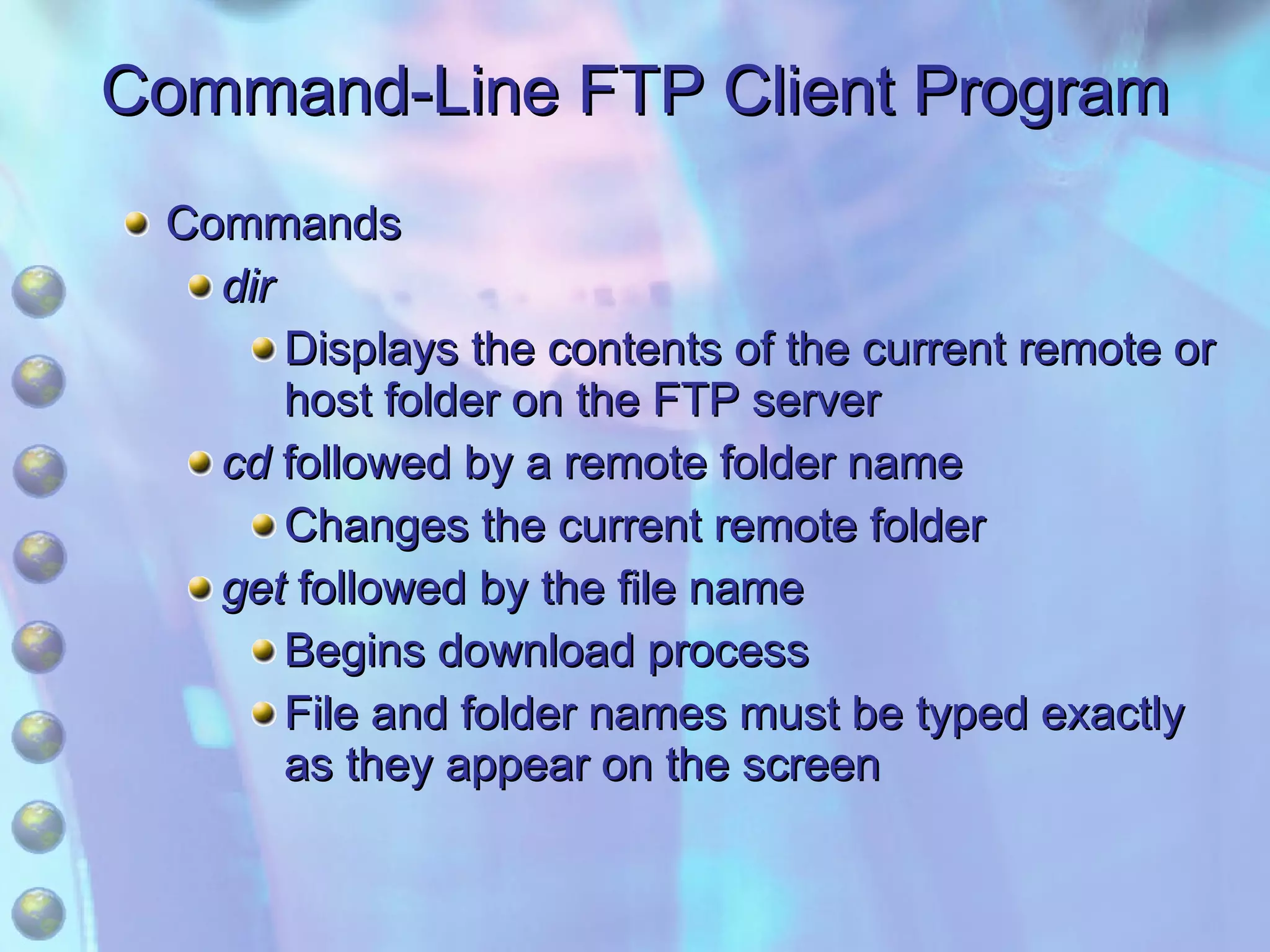
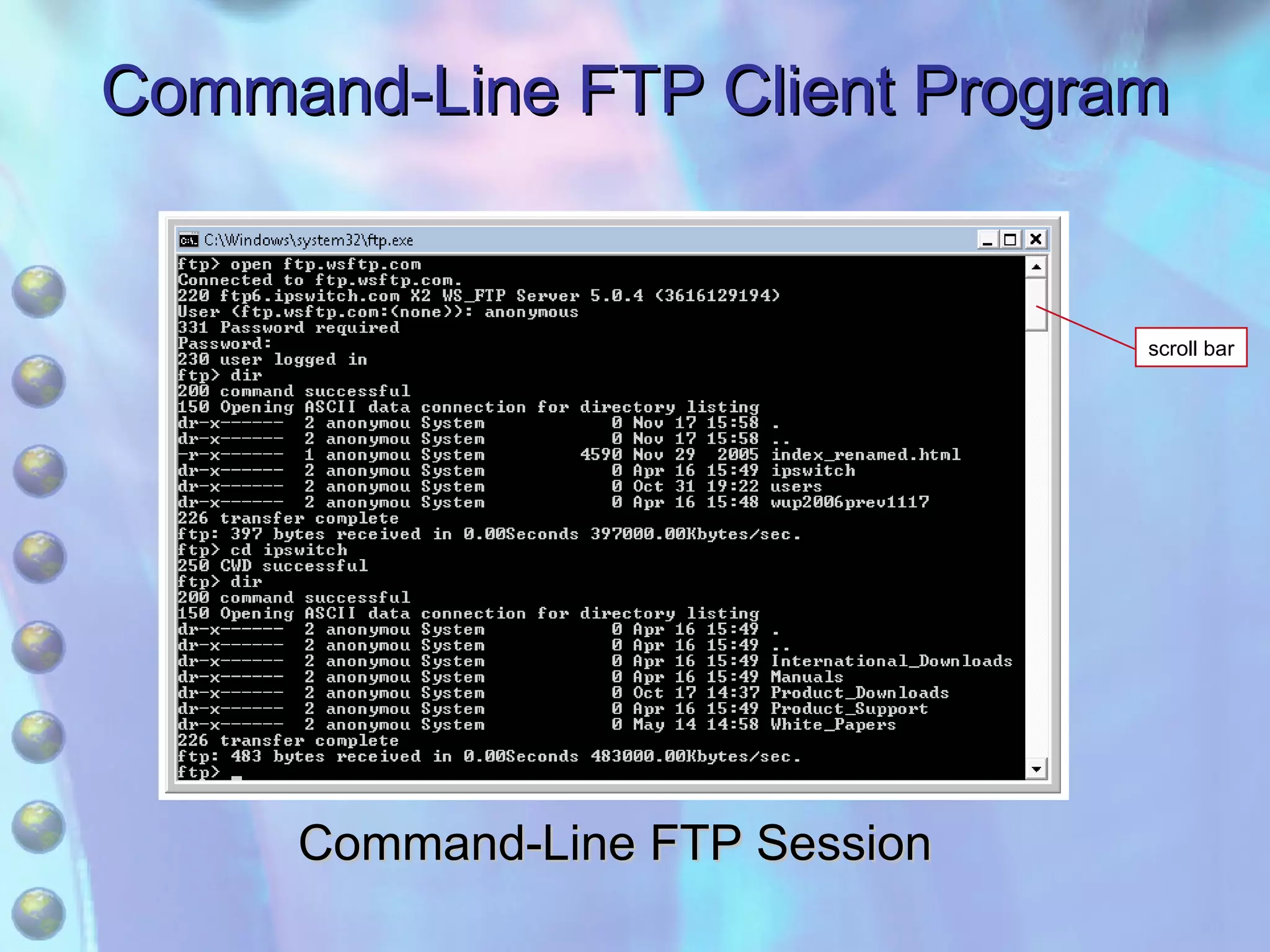
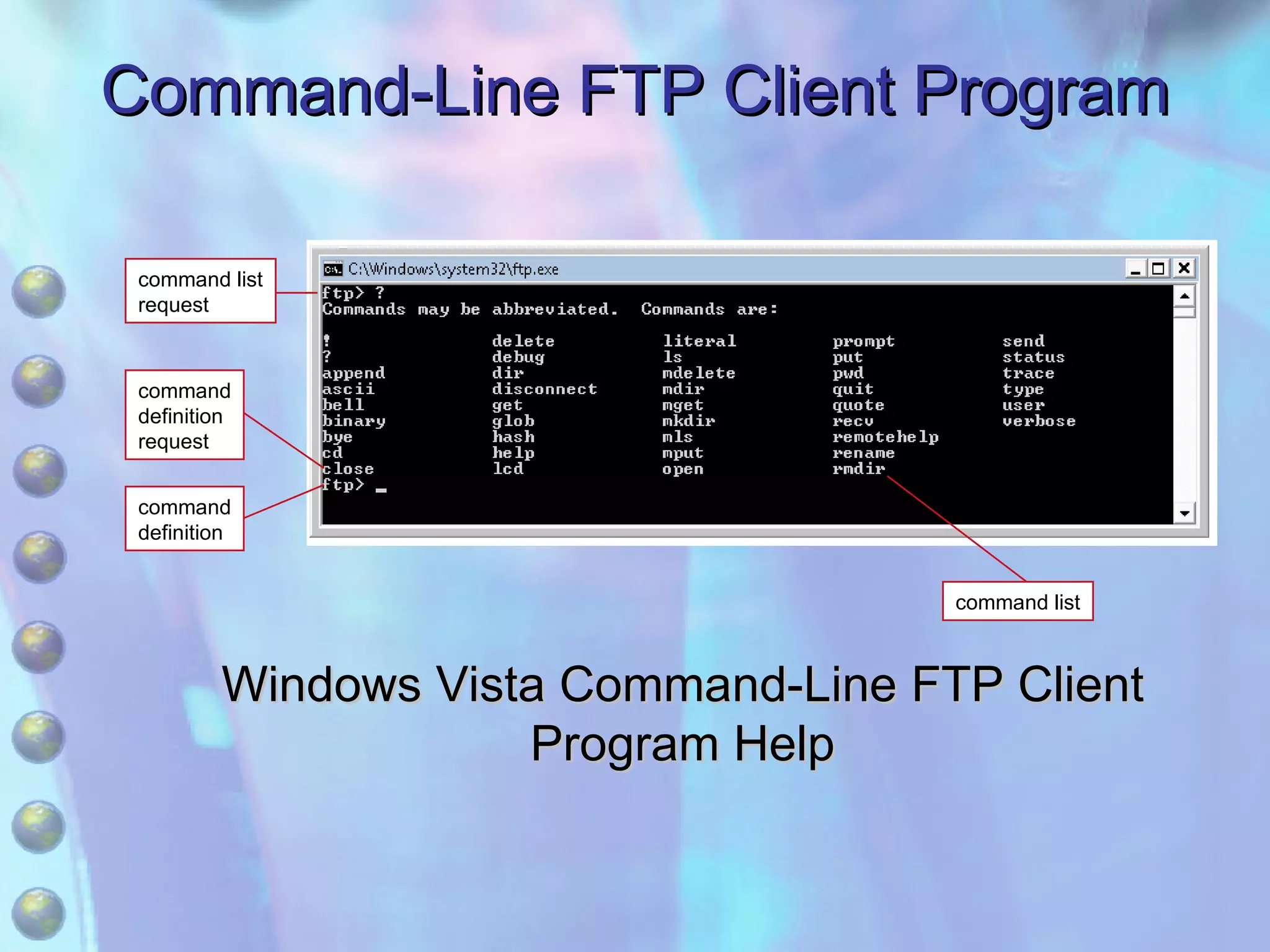
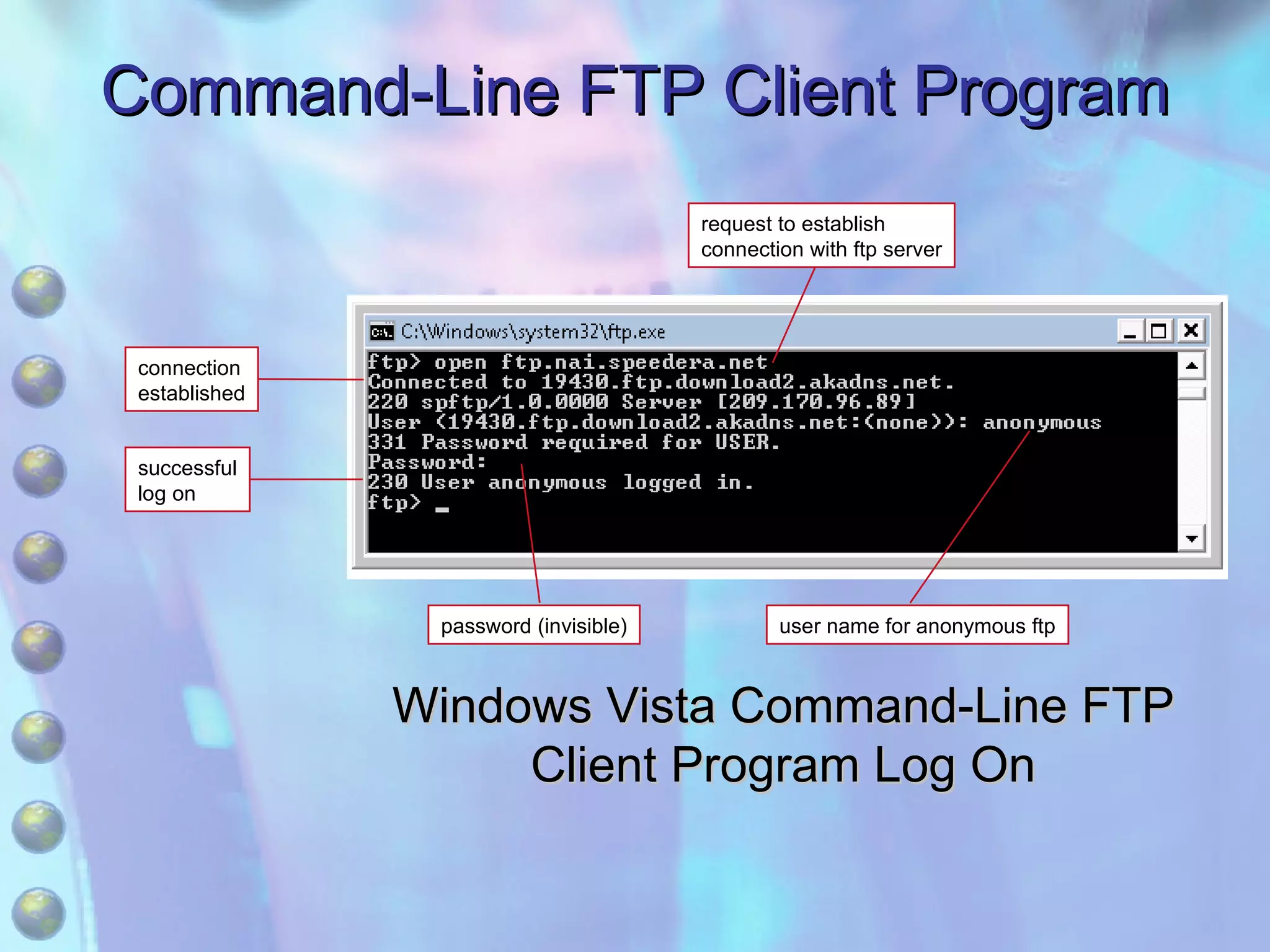
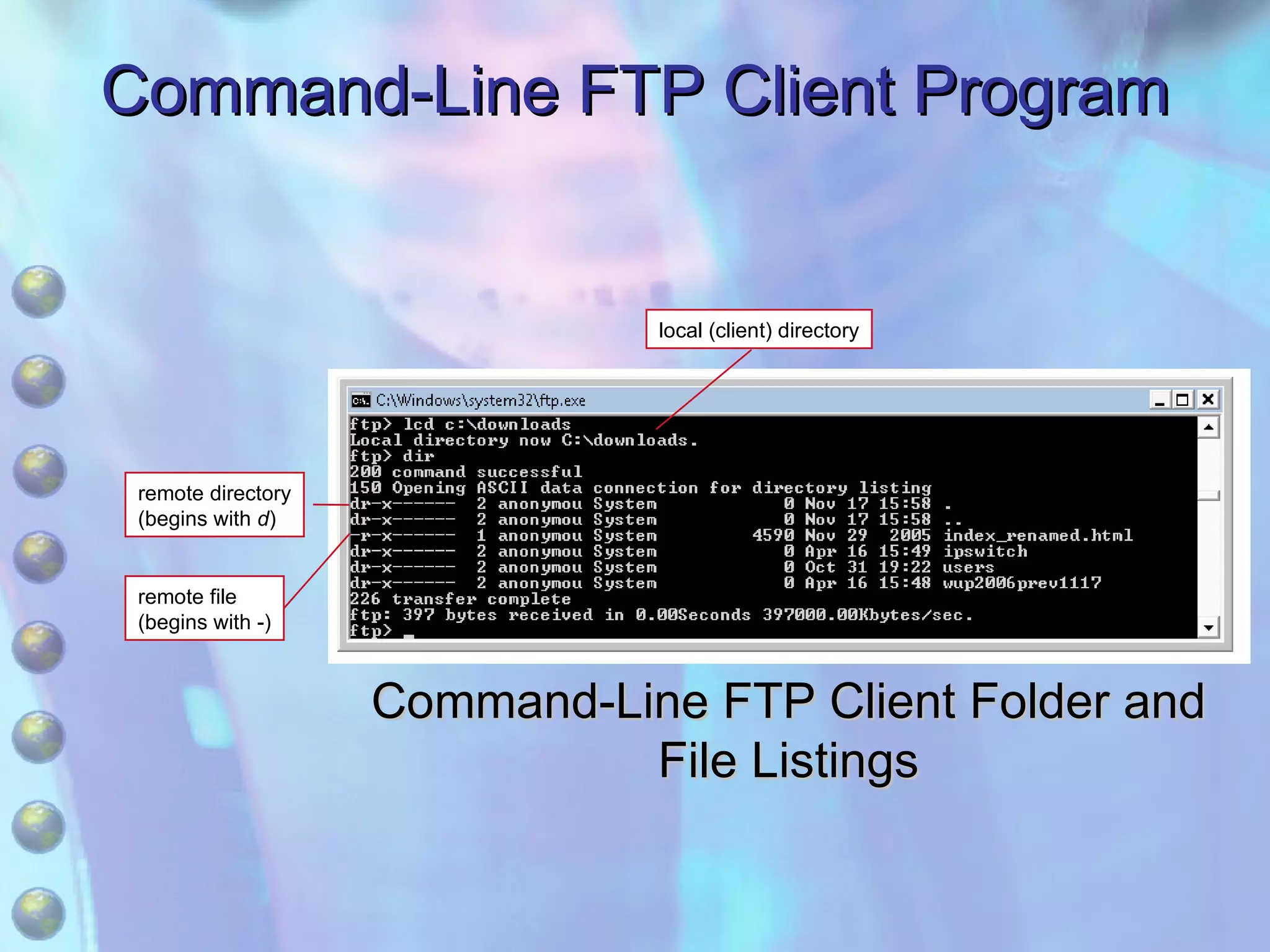
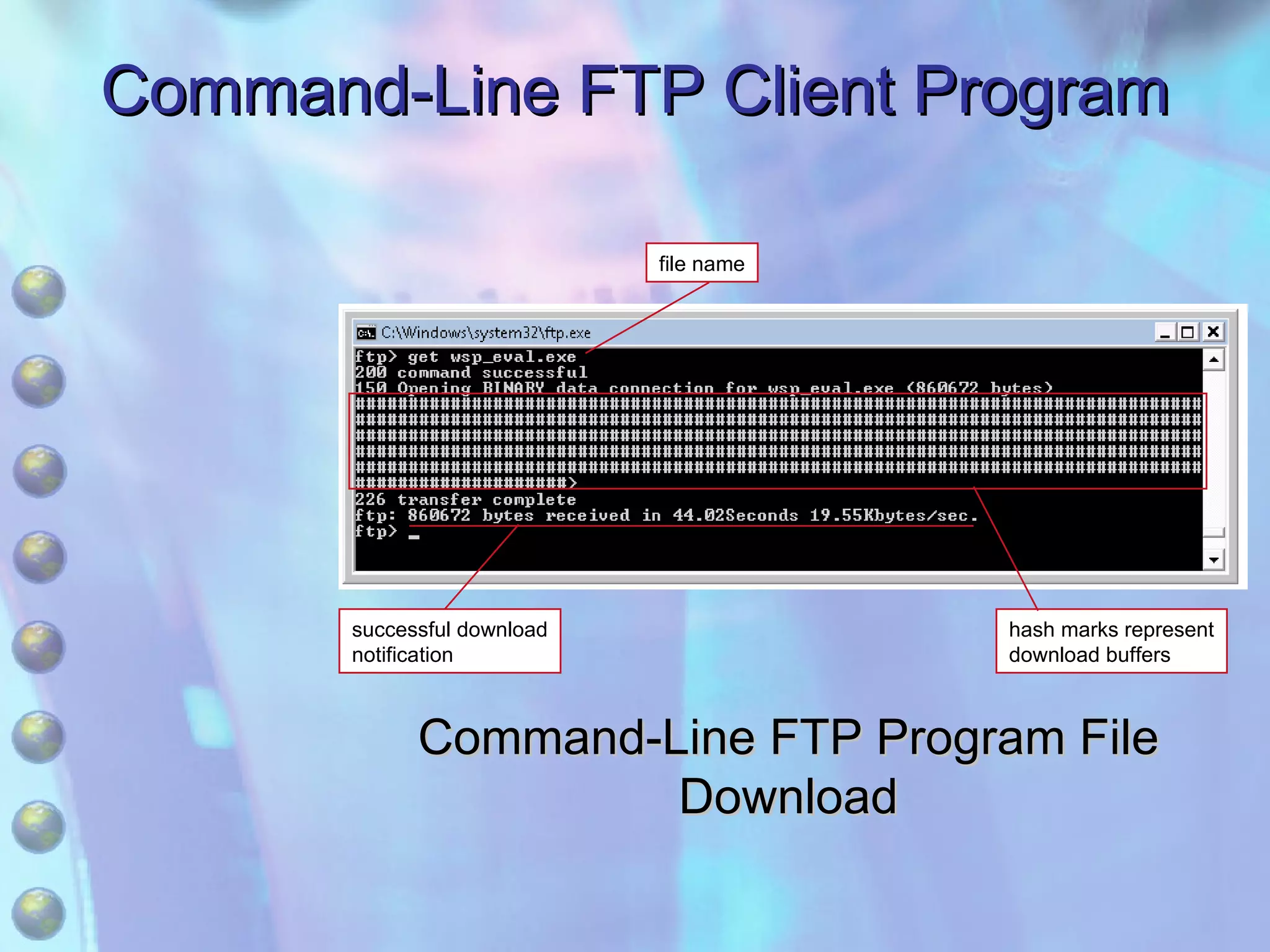
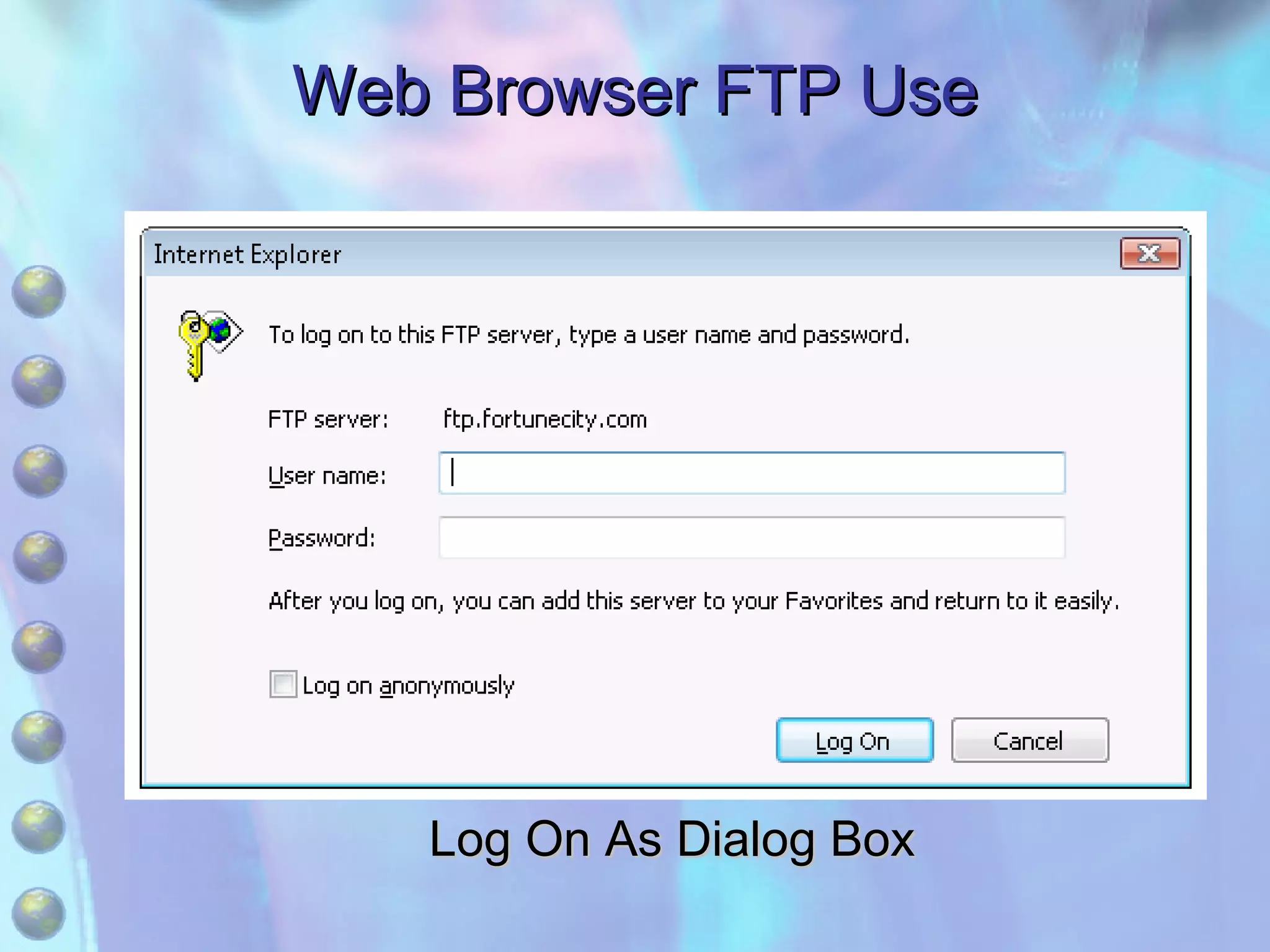
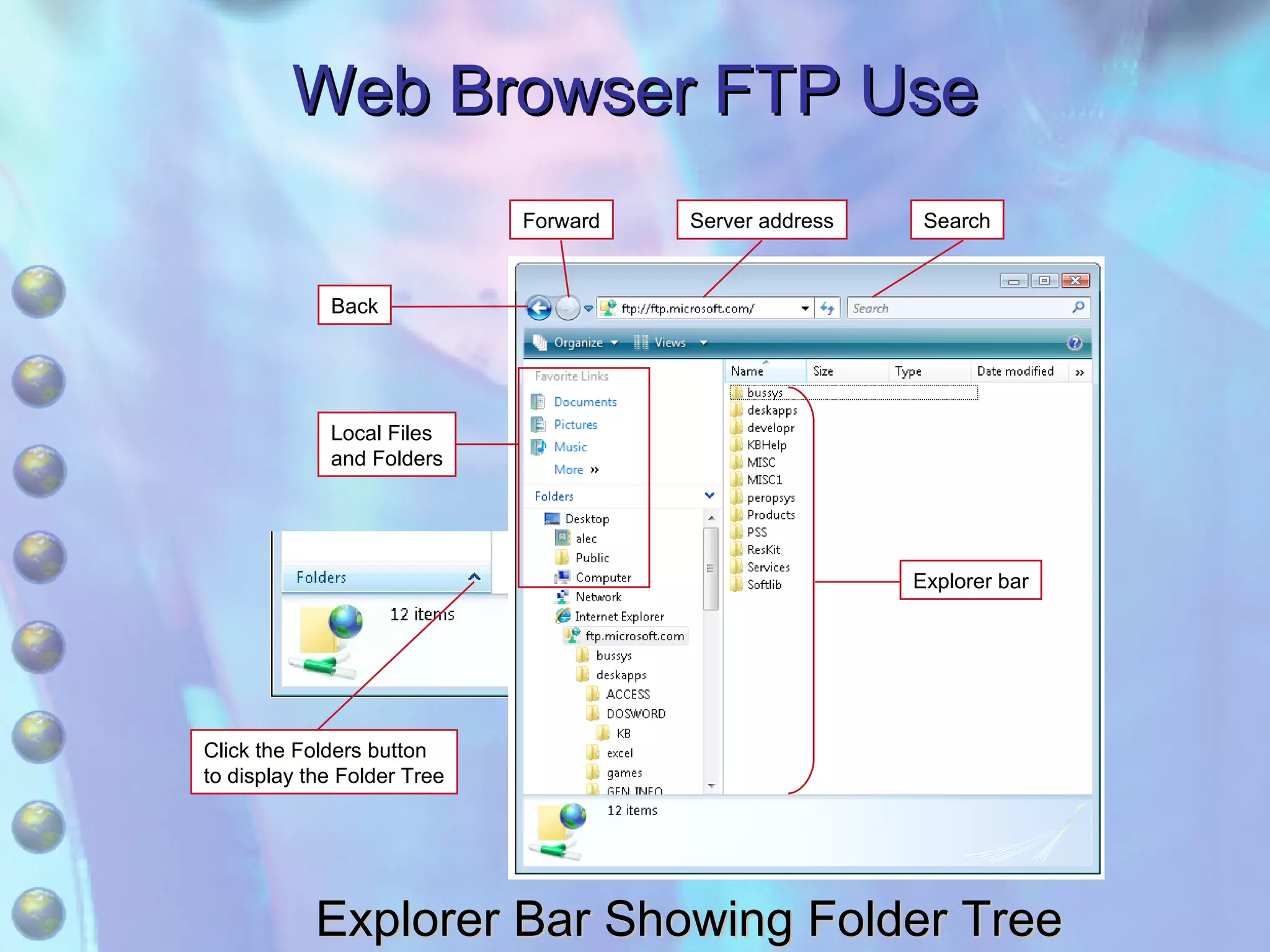
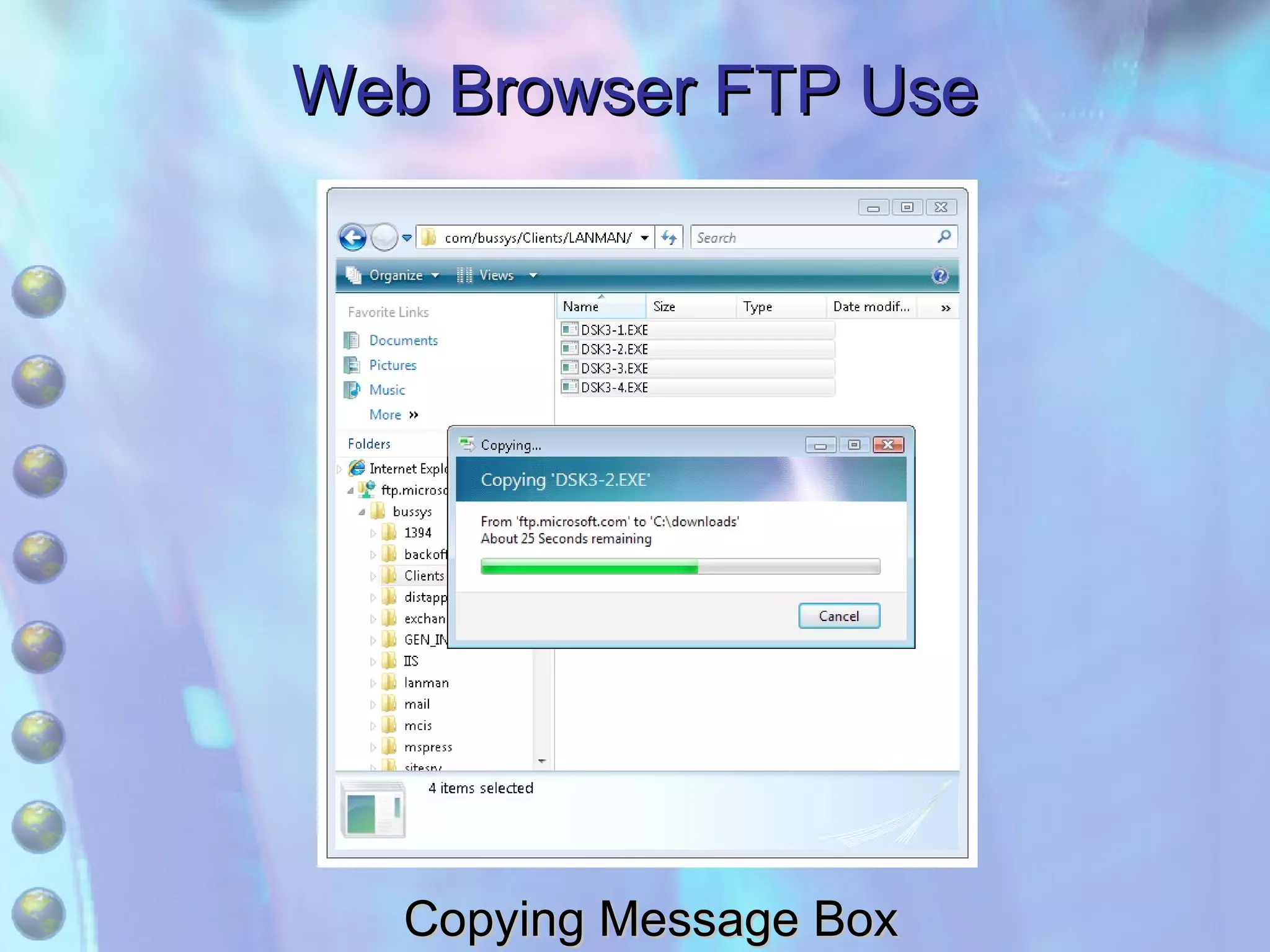
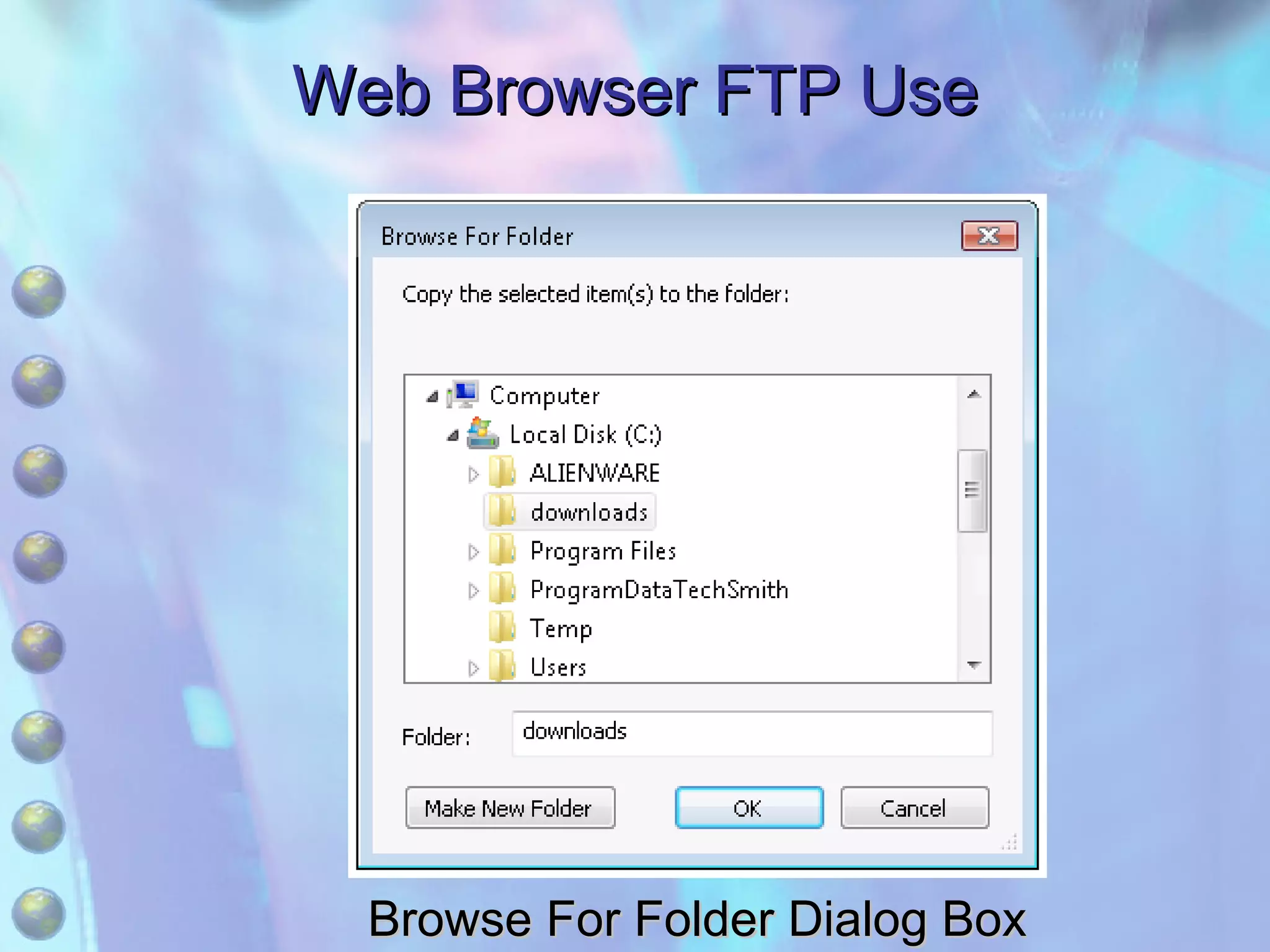
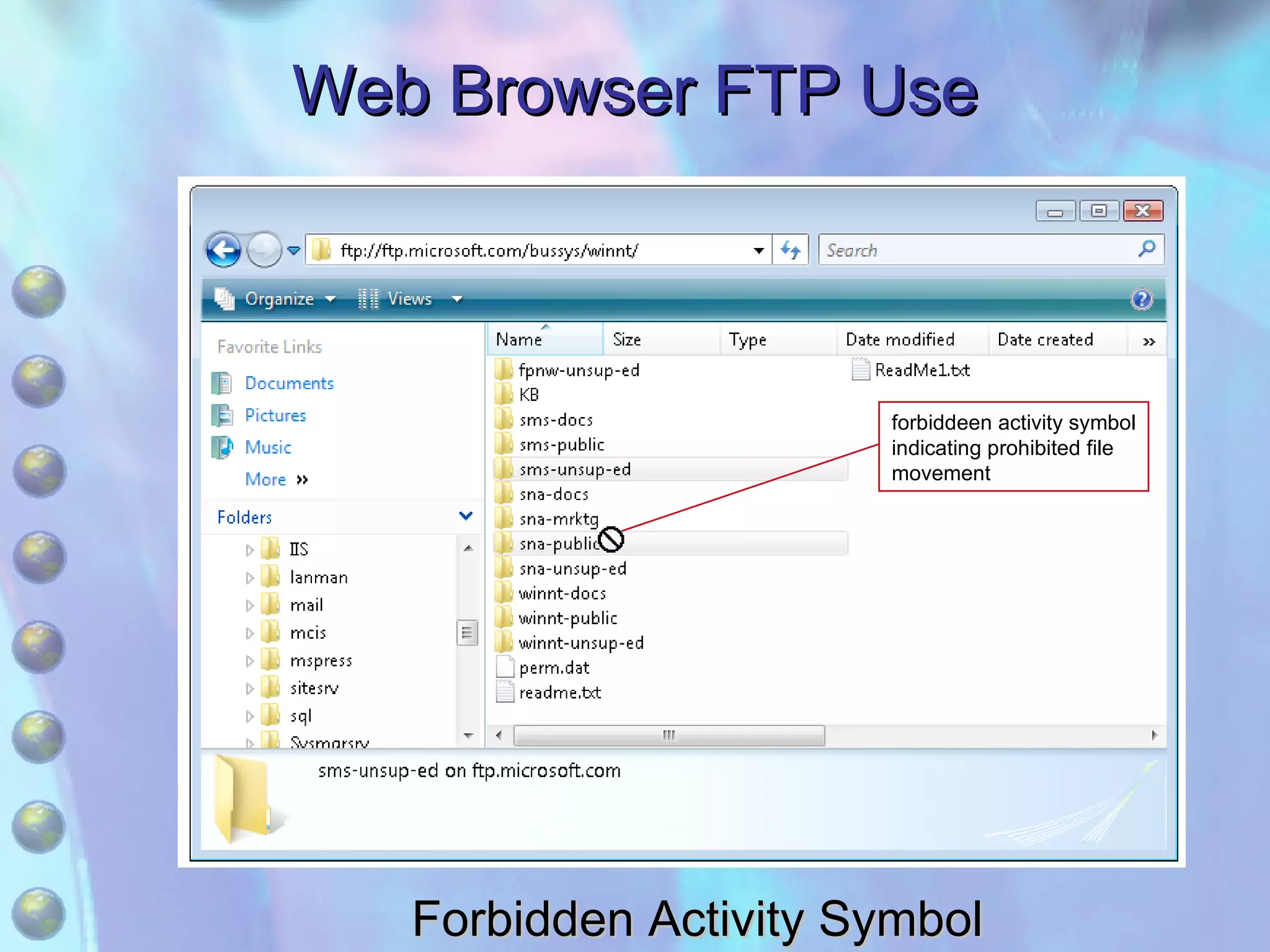
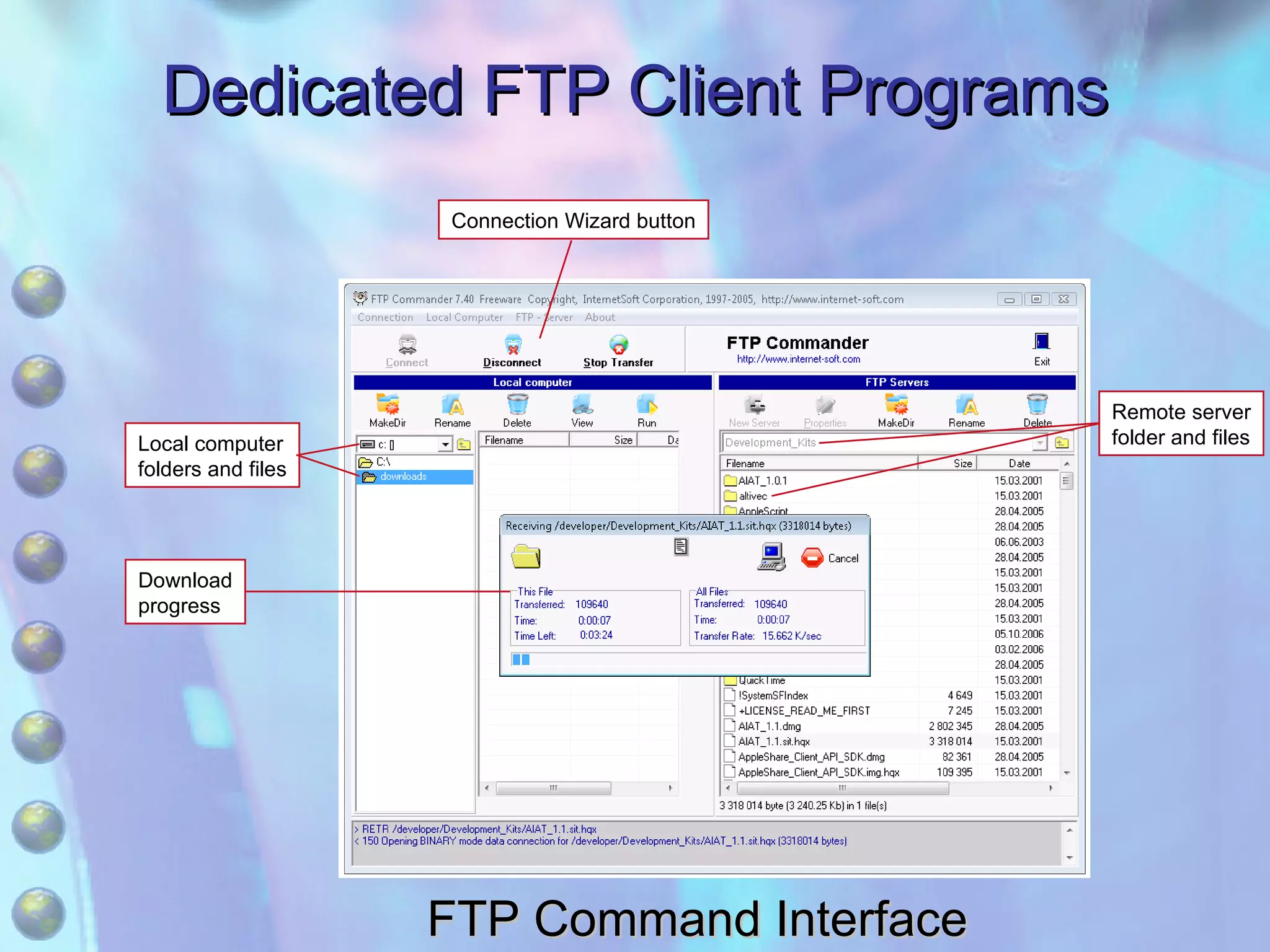
1) File Transfer Protocol (FTP) which allows transferring files between networked computers using FTP client programs with either a command line or graphical user interface.
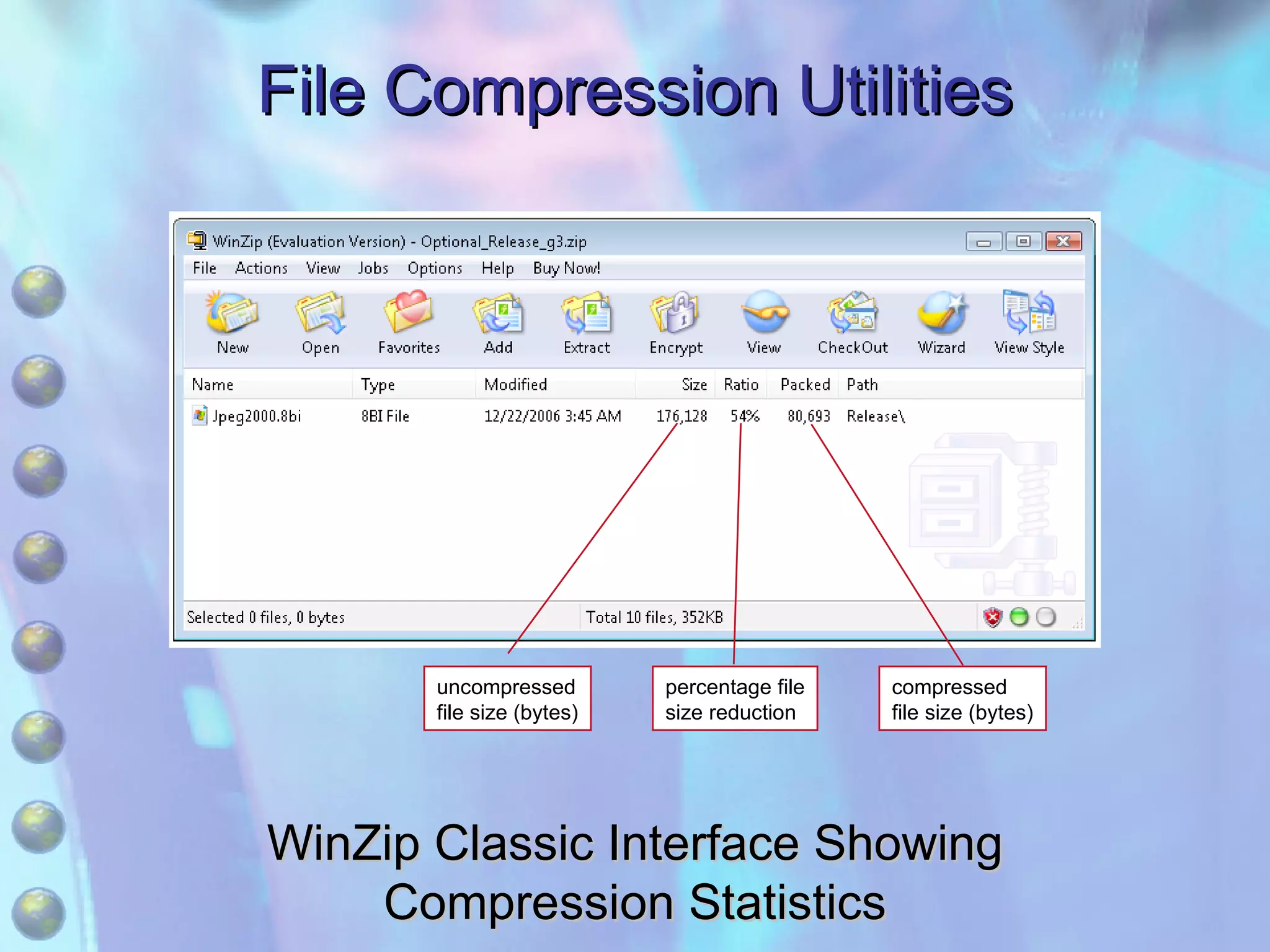
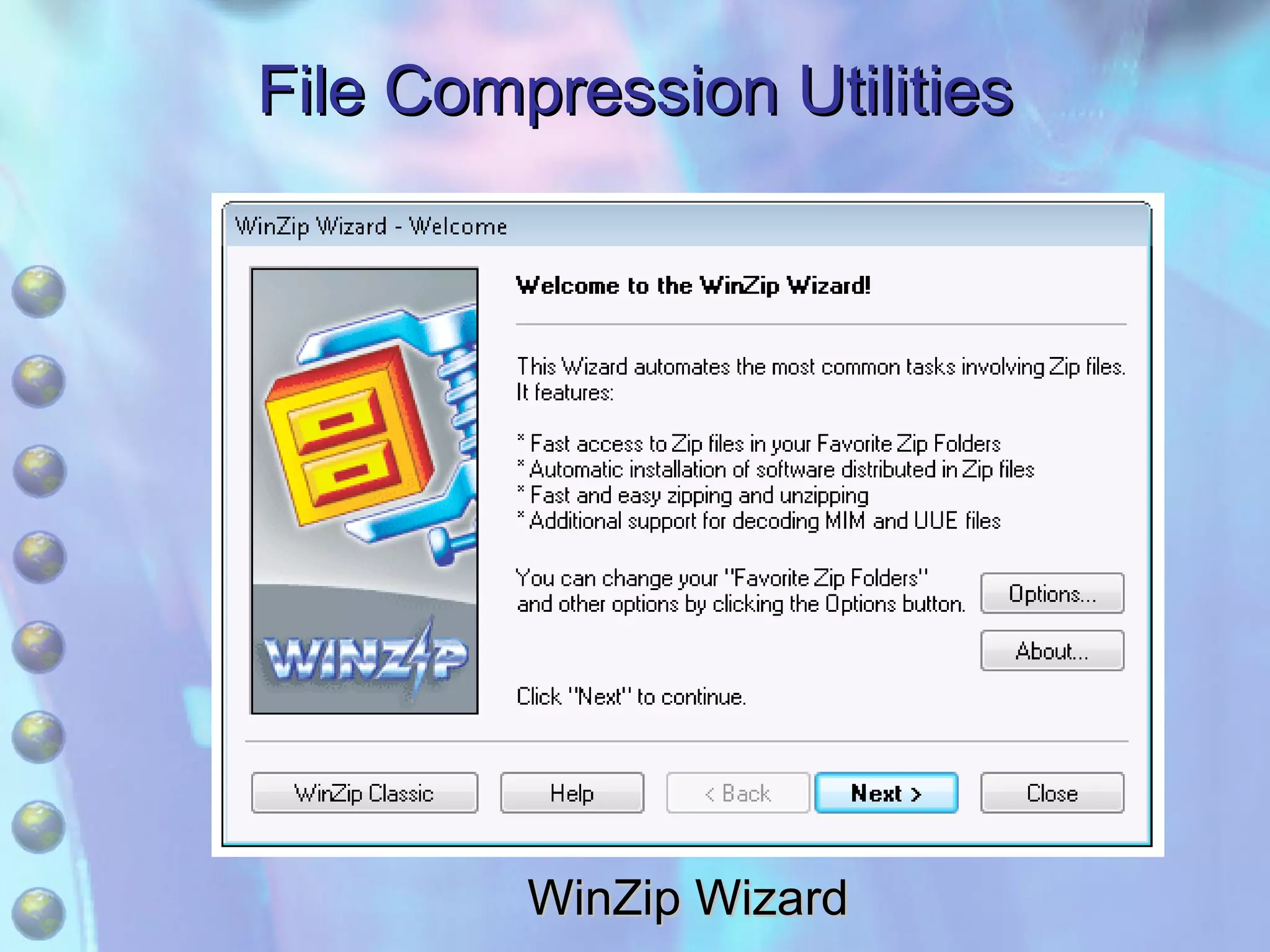
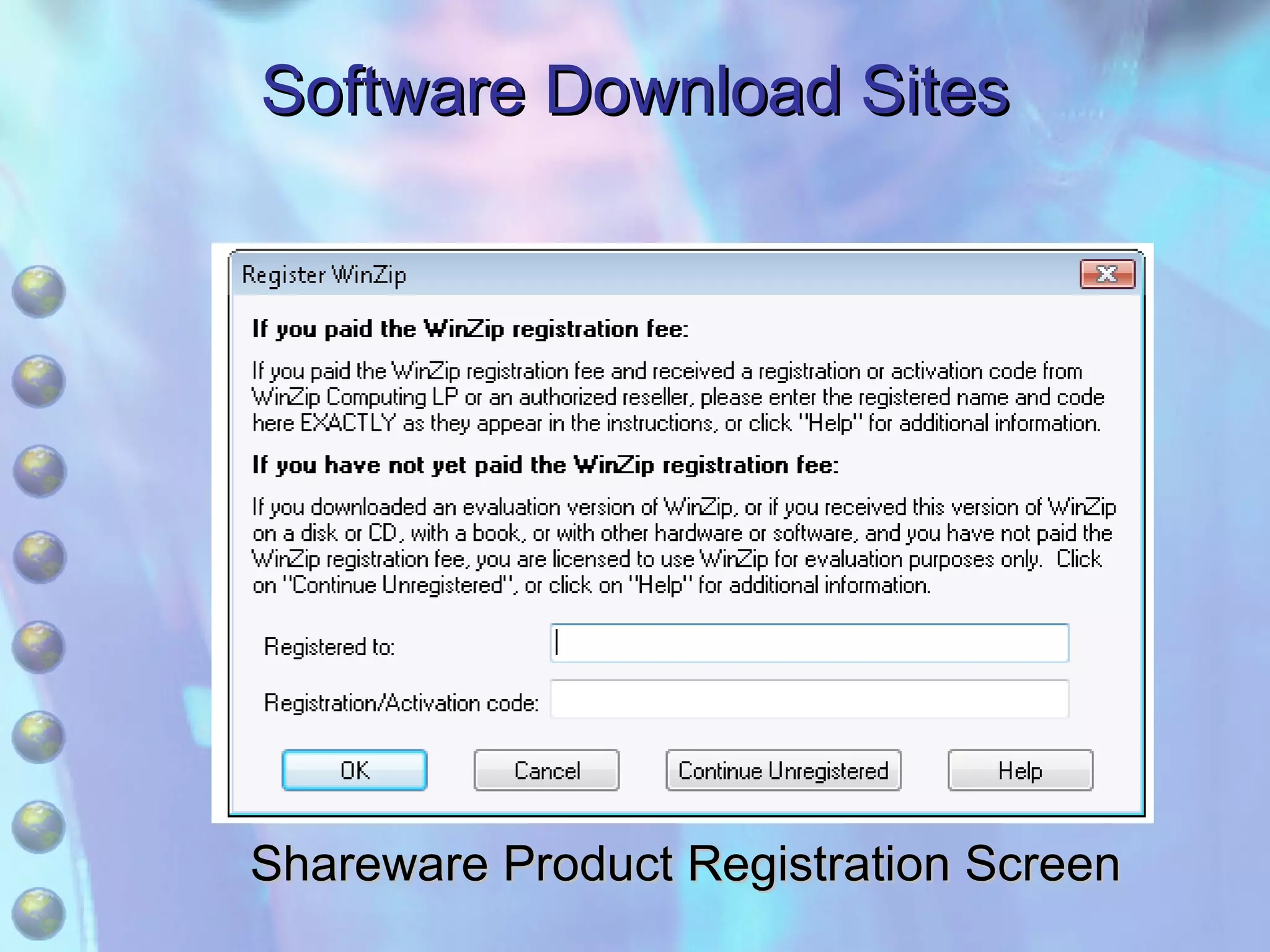
2) File compression utilities like WinZip which use algorithms to compact file sizes for more efficient storage and transfer, without losing data.
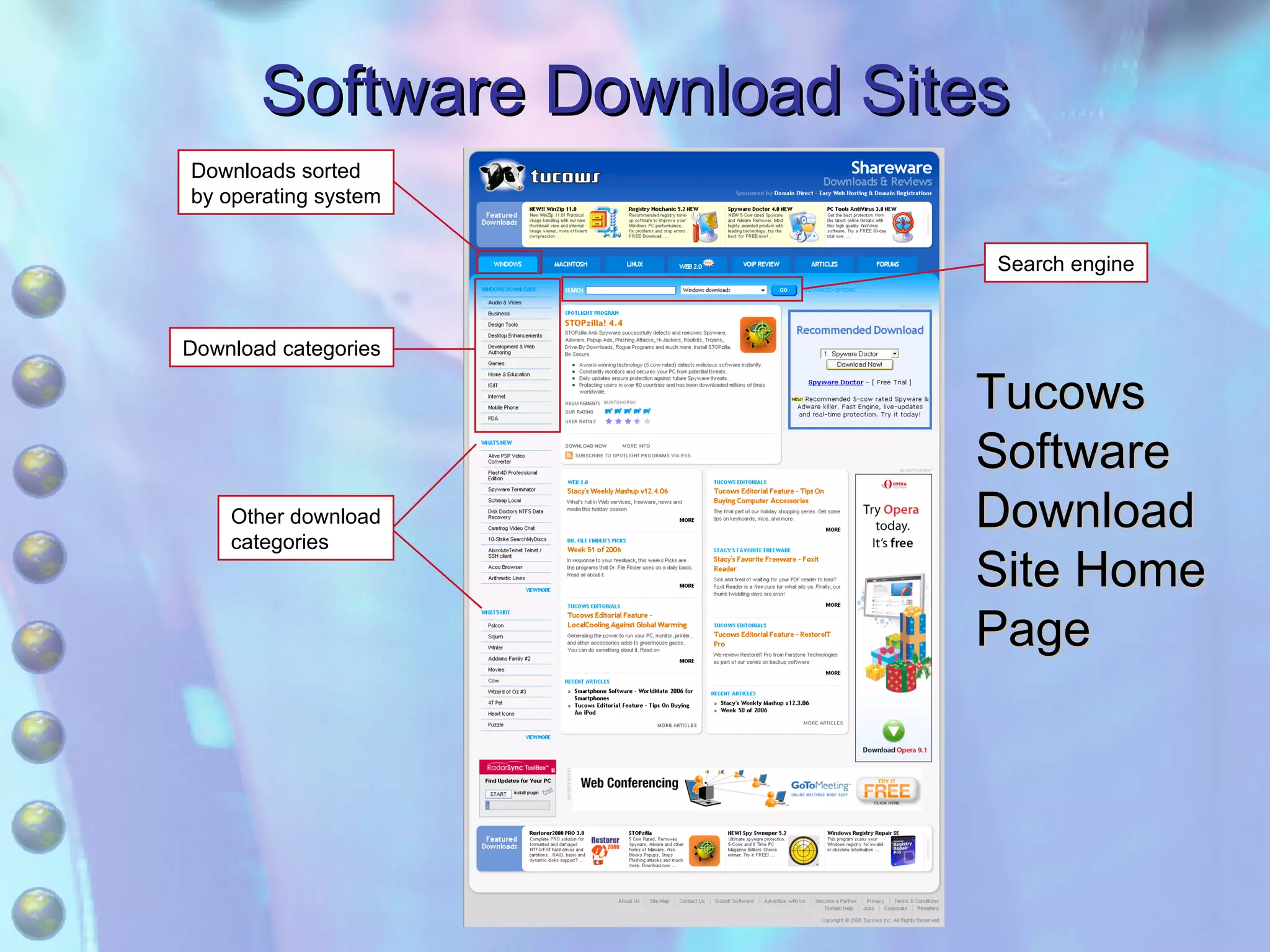
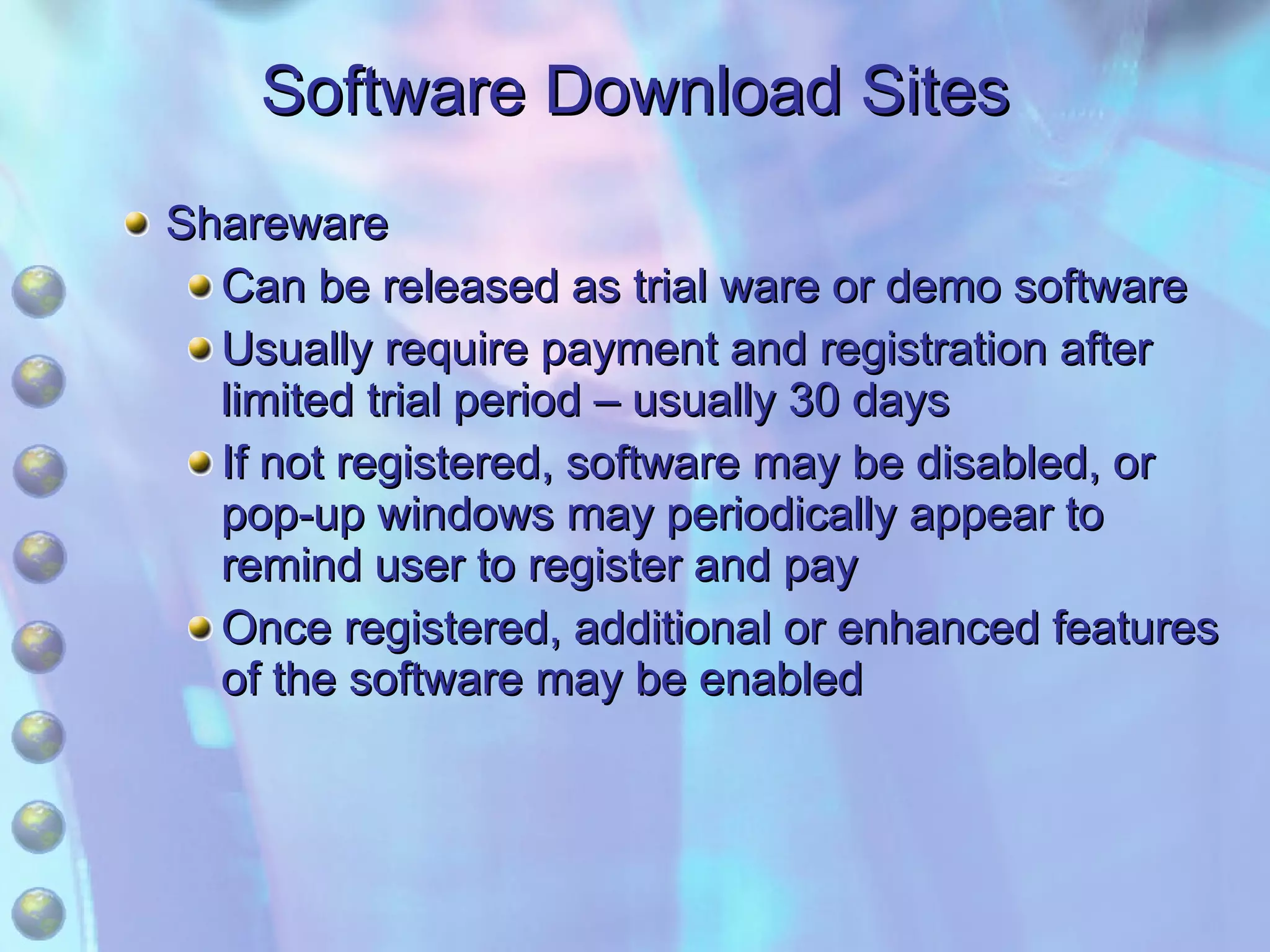
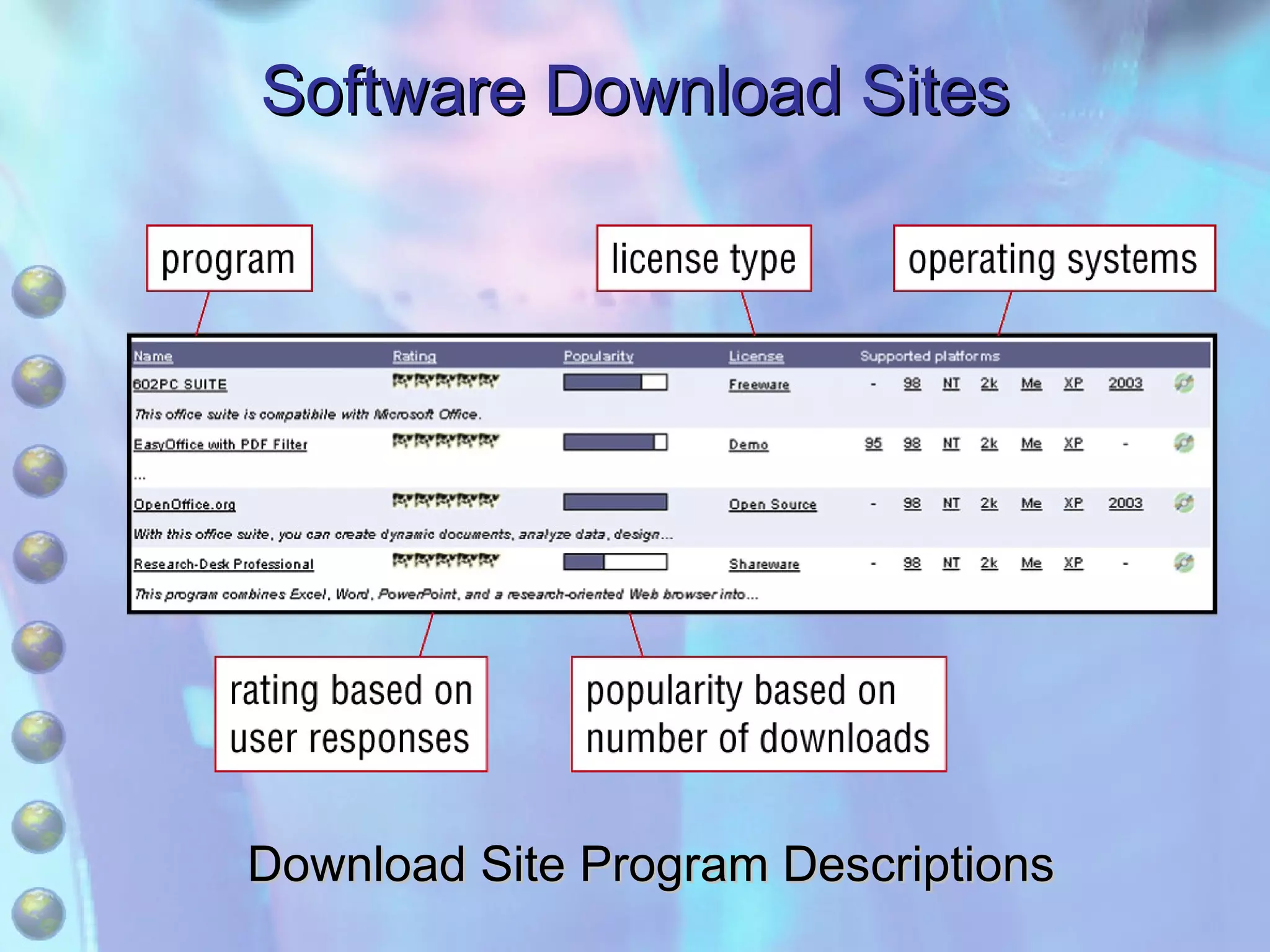
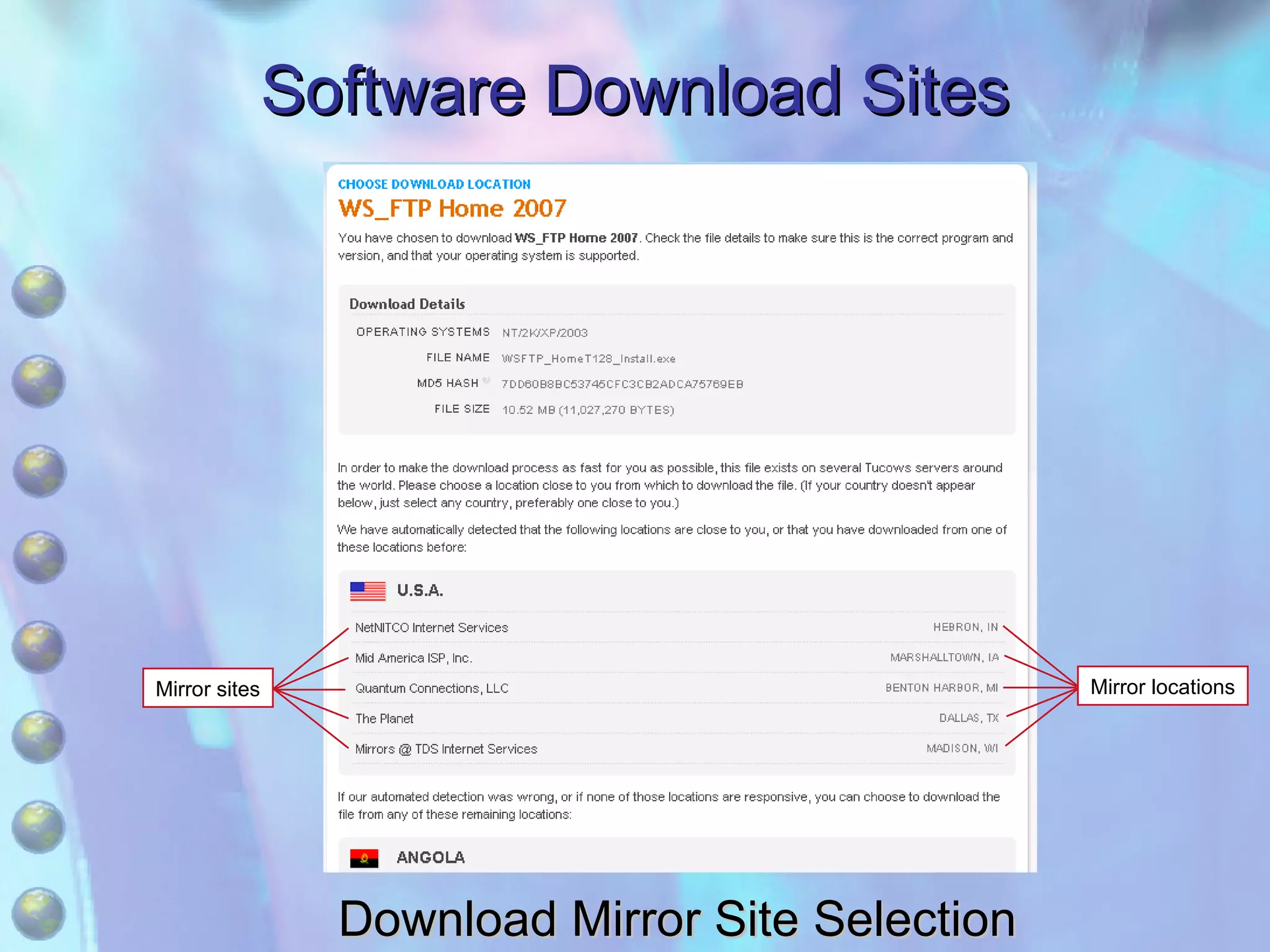
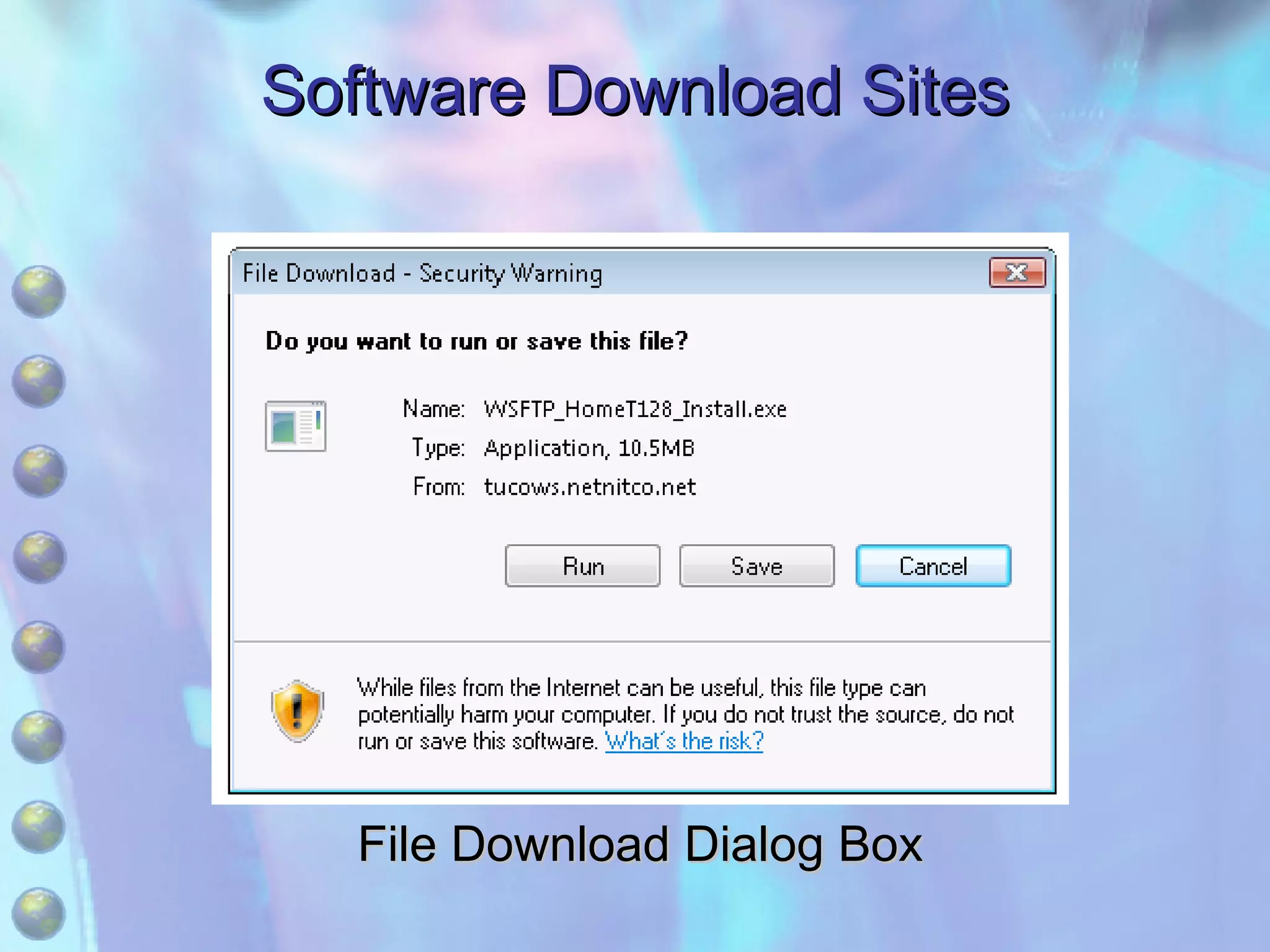
3) Software download sites that provide freeware and shareware programs that can be downloaded, with freeware being free but possibly less polished, and shareware requiring payment after trial usage.
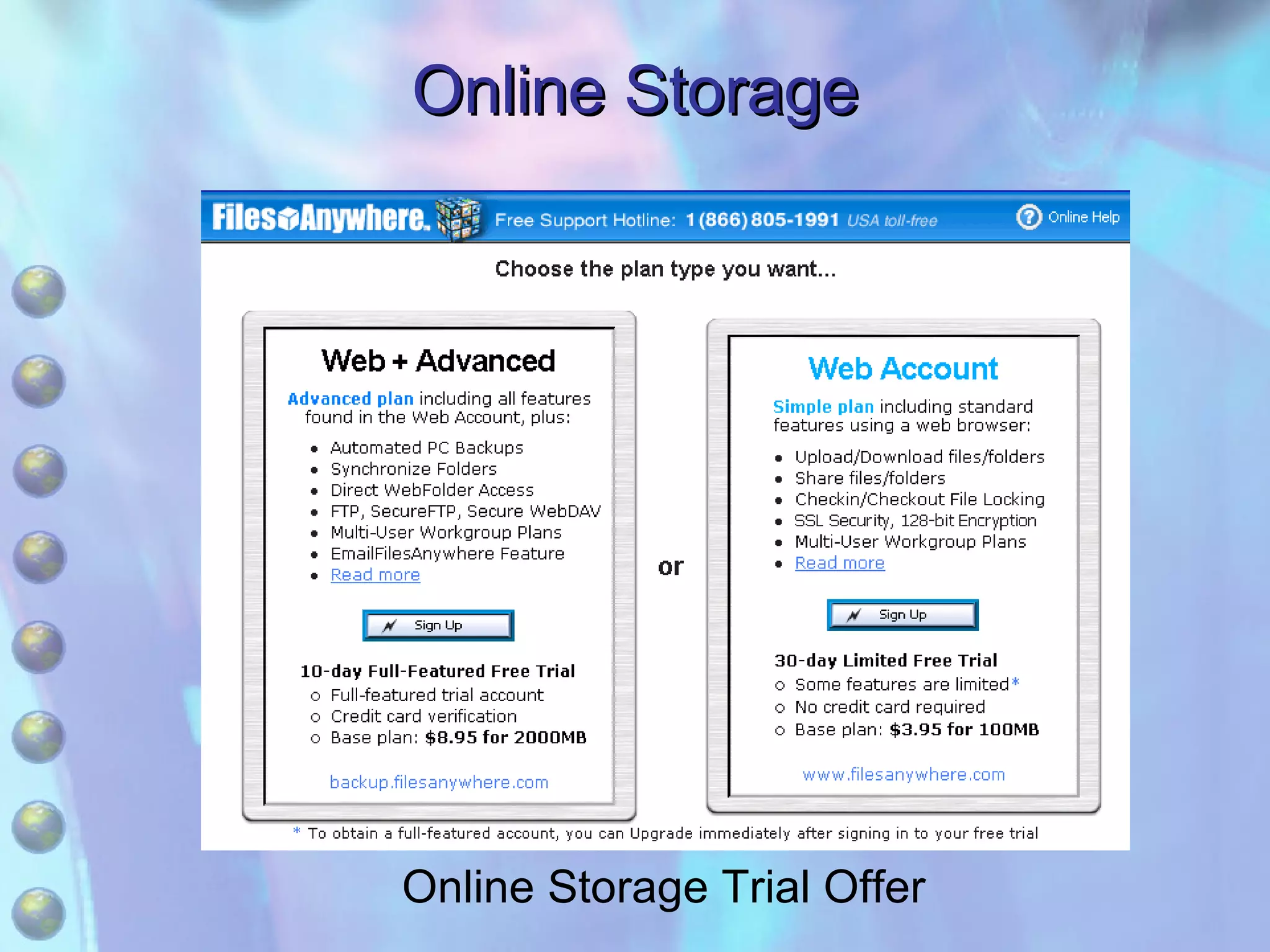
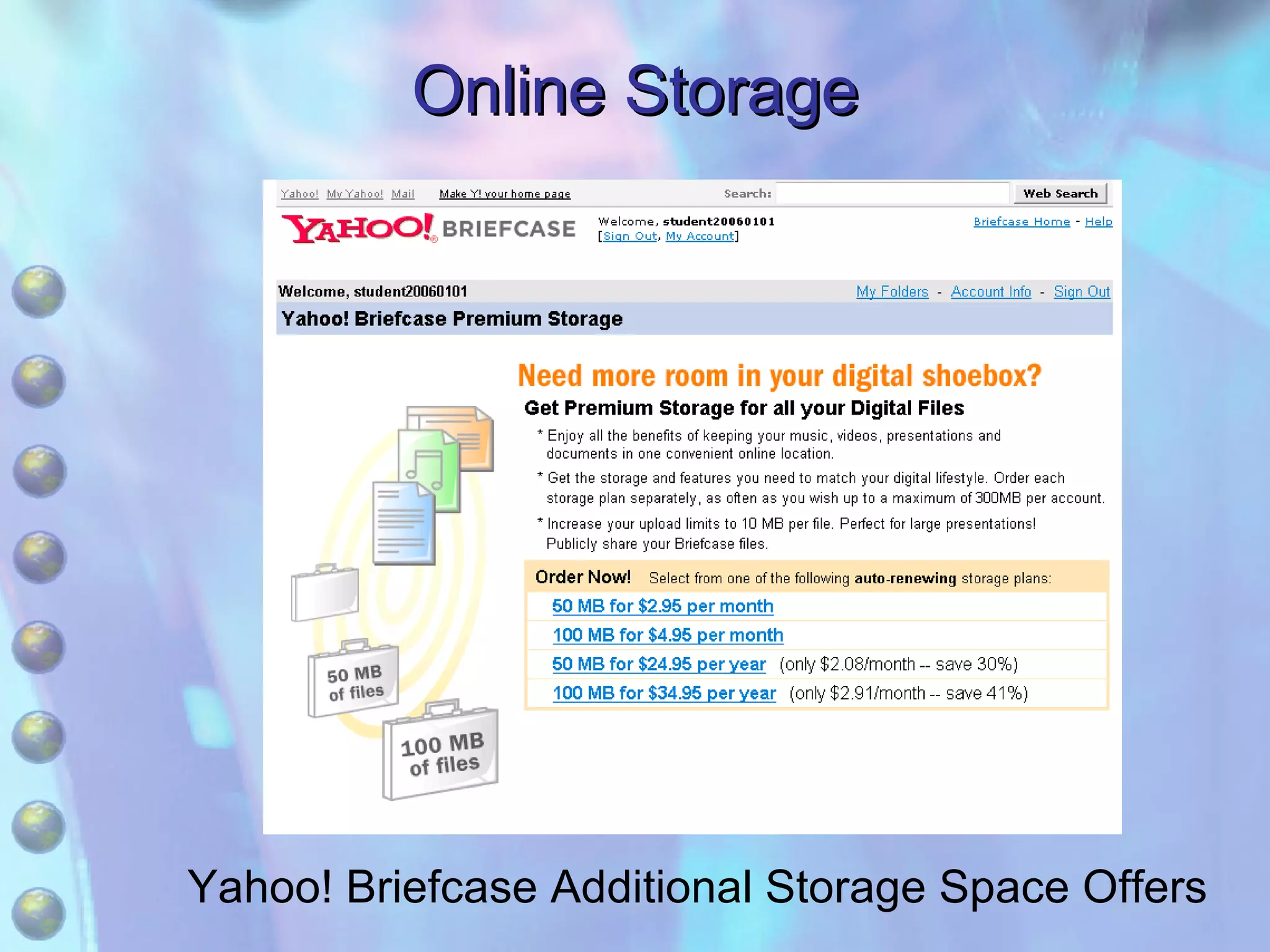
4) Online storage services which offer remote storage space that can be accessed online through the provider's website, allowing backup of personal files and sharing of documents.