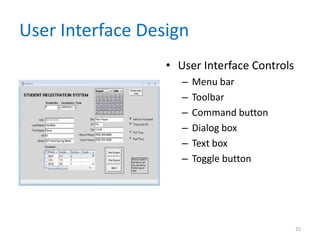
This chapter discusses output and user interface design. It covers types of output like reports, screen design, and user interface elements. The chapter emphasizes user-centered design principles to understand users and make interfaces intuitive. Guidelines are provided for output design, reports, and reducing input errors through validation and limiting data entry fields. The overall goal is to design interfaces and outputs that meet user needs.