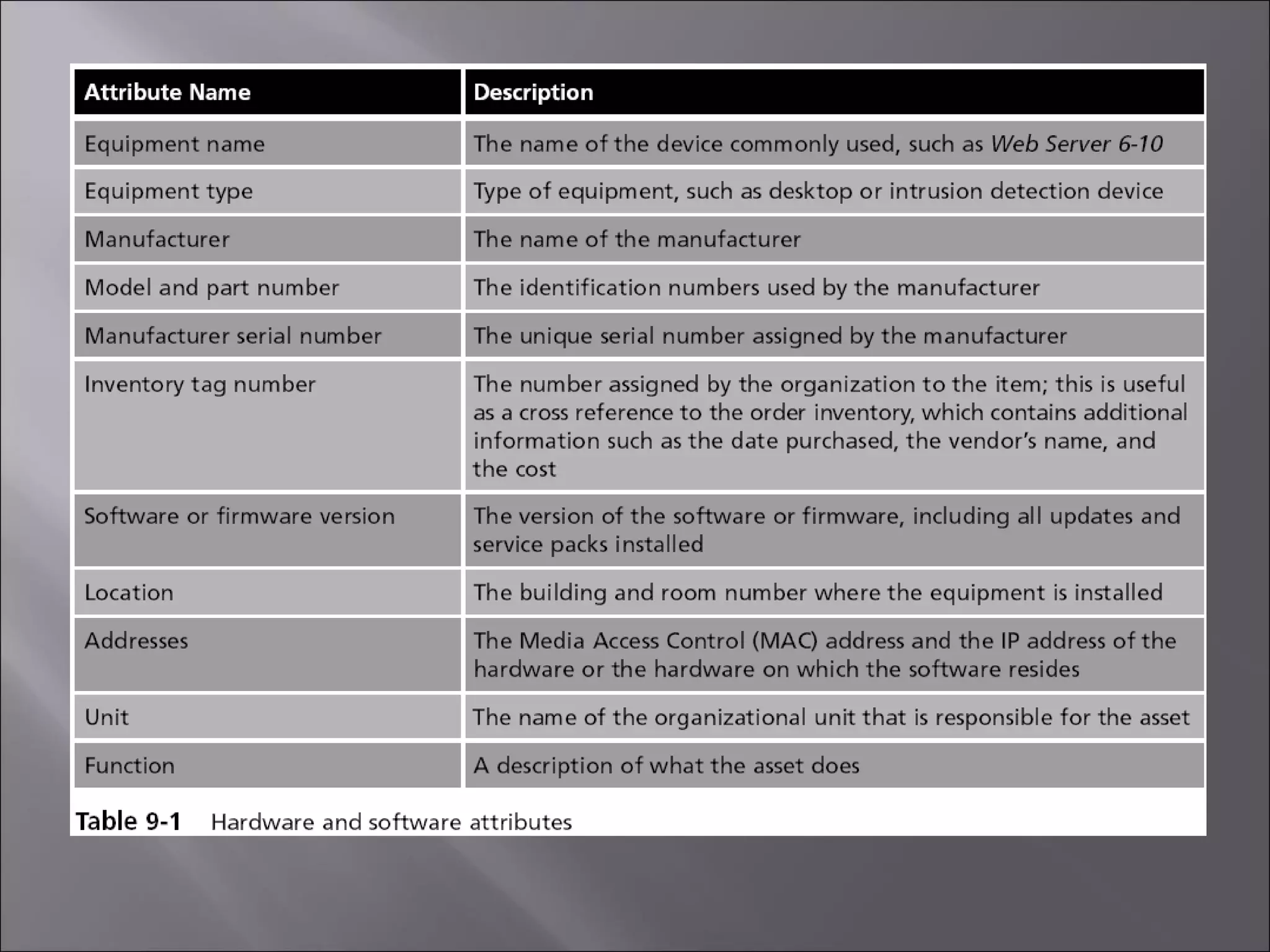
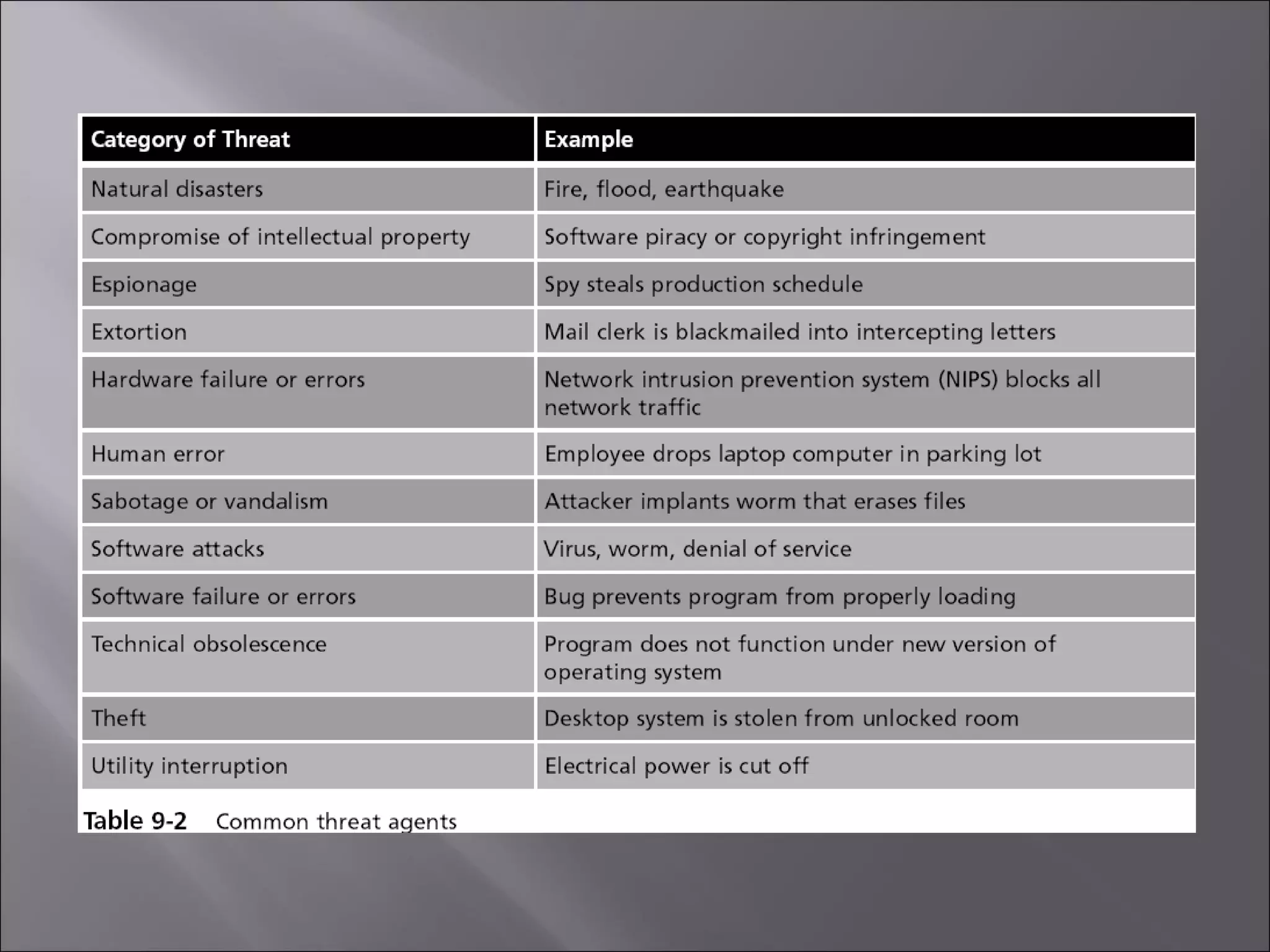
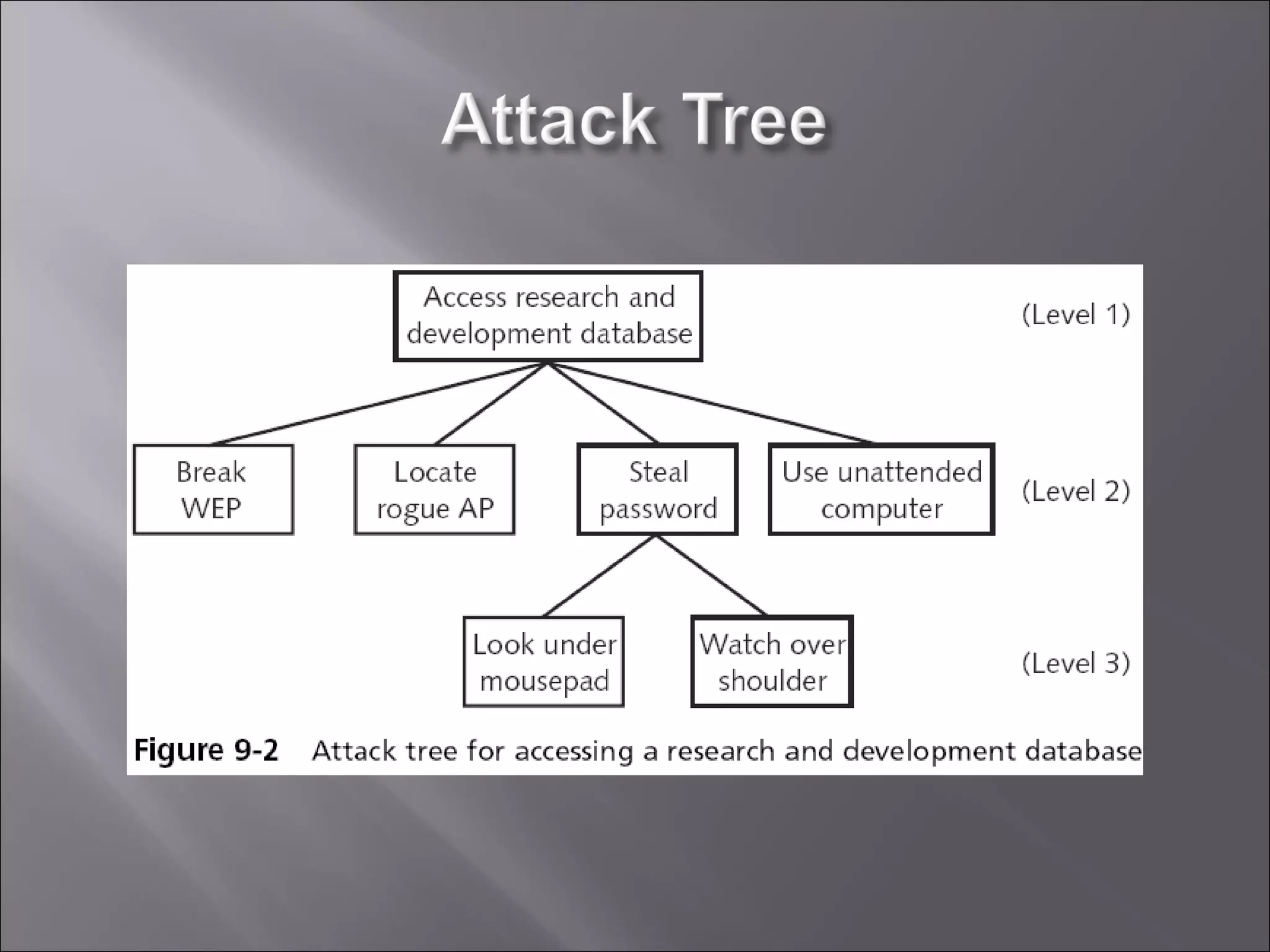
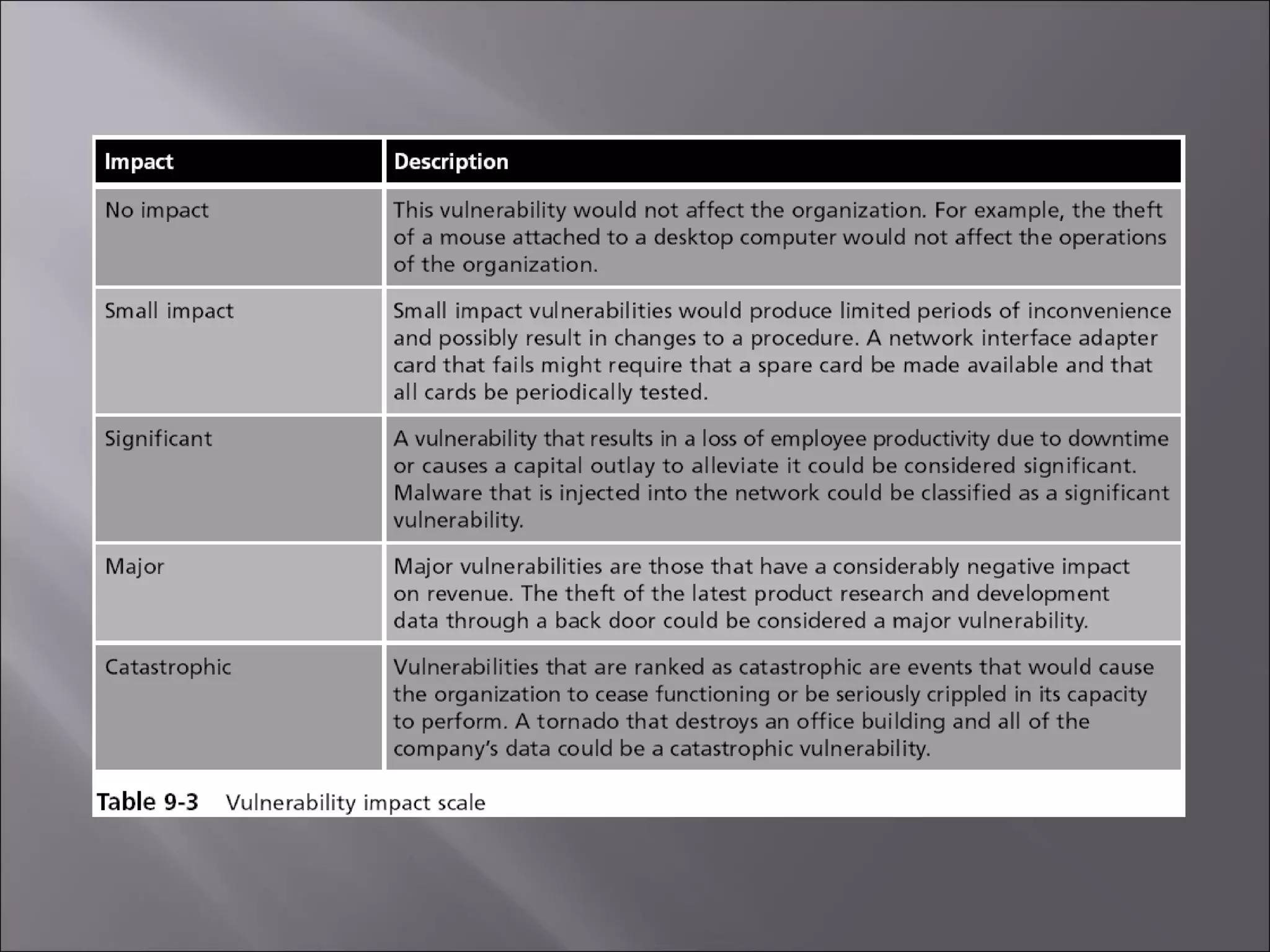
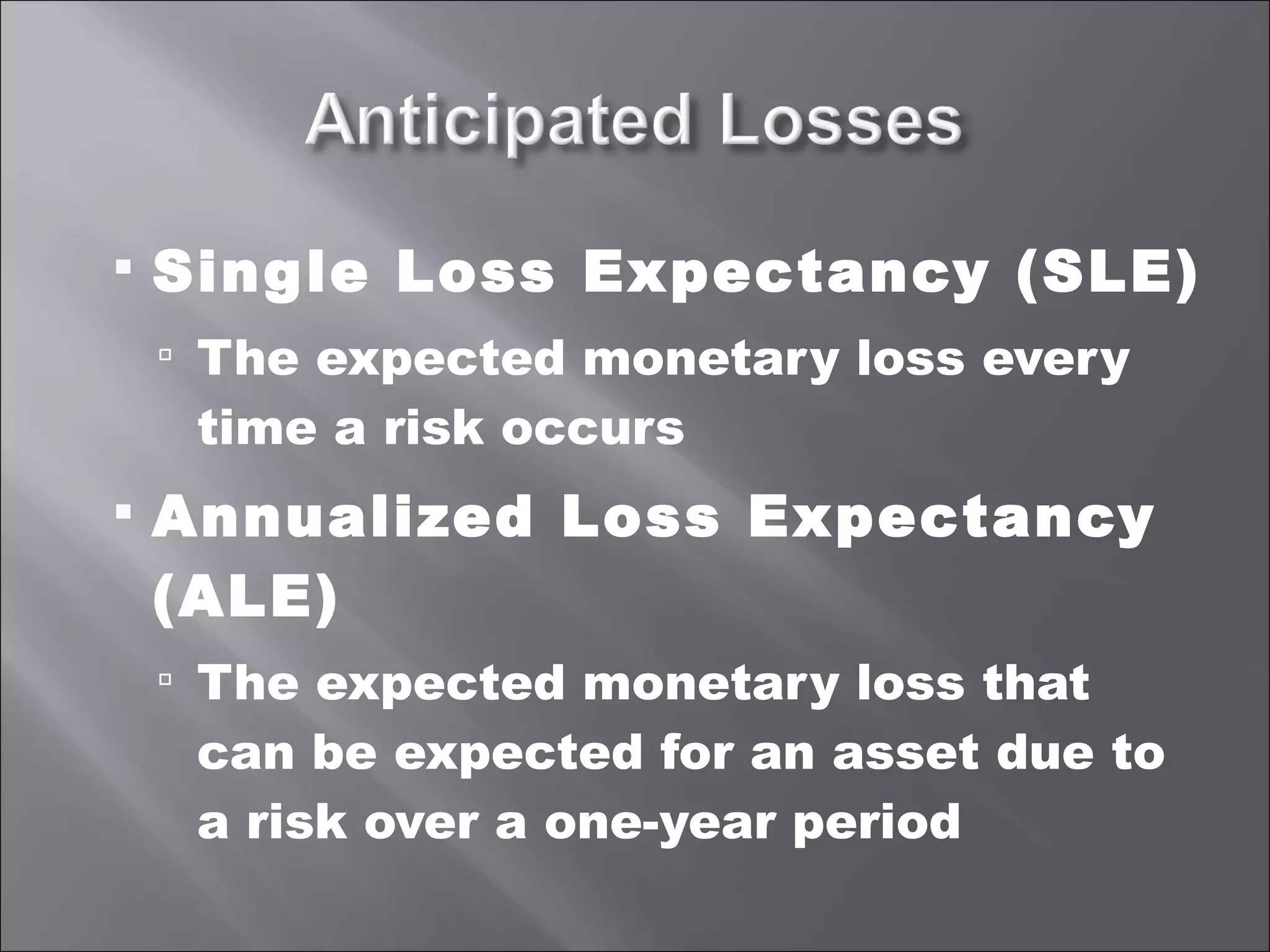
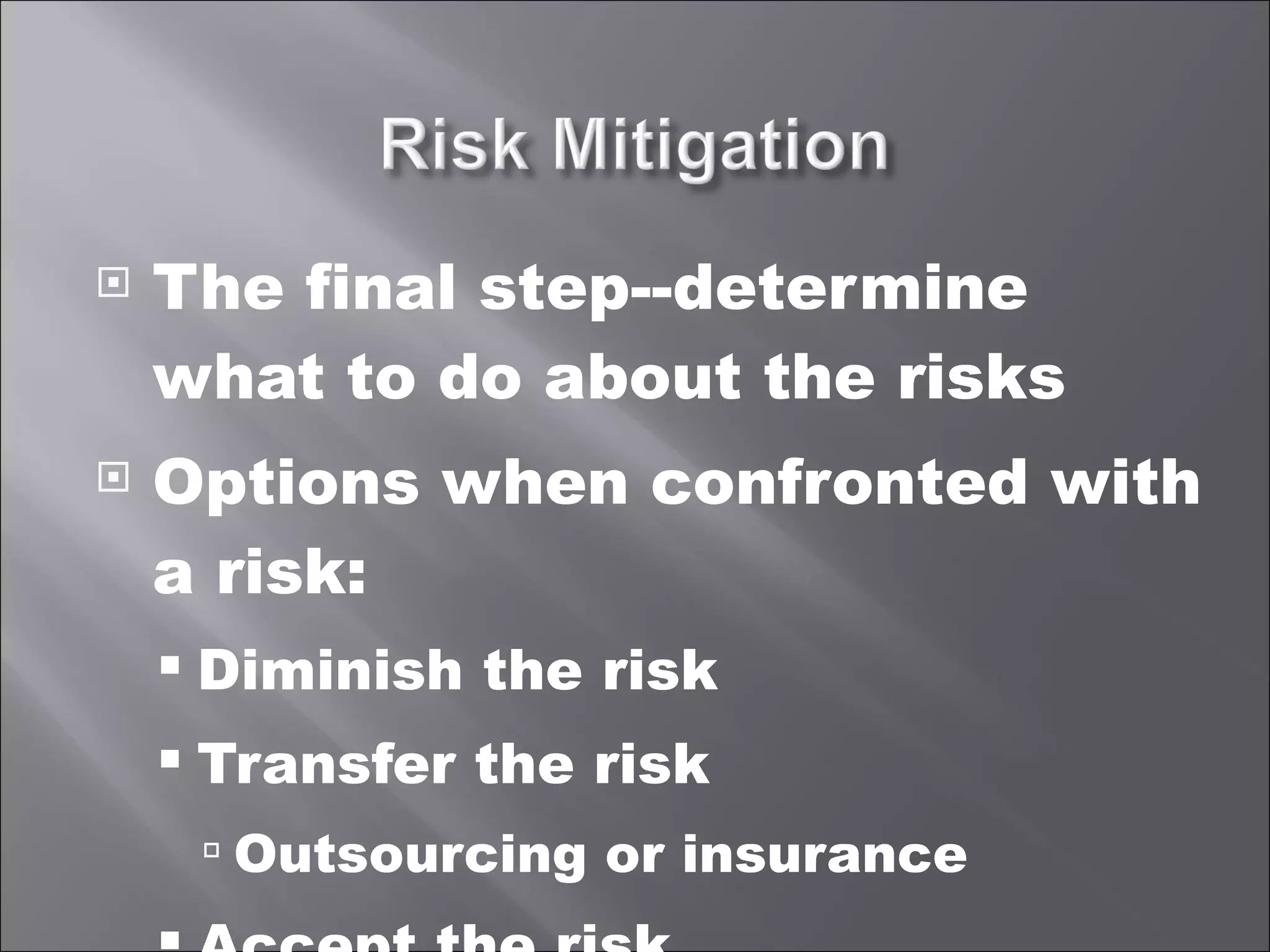
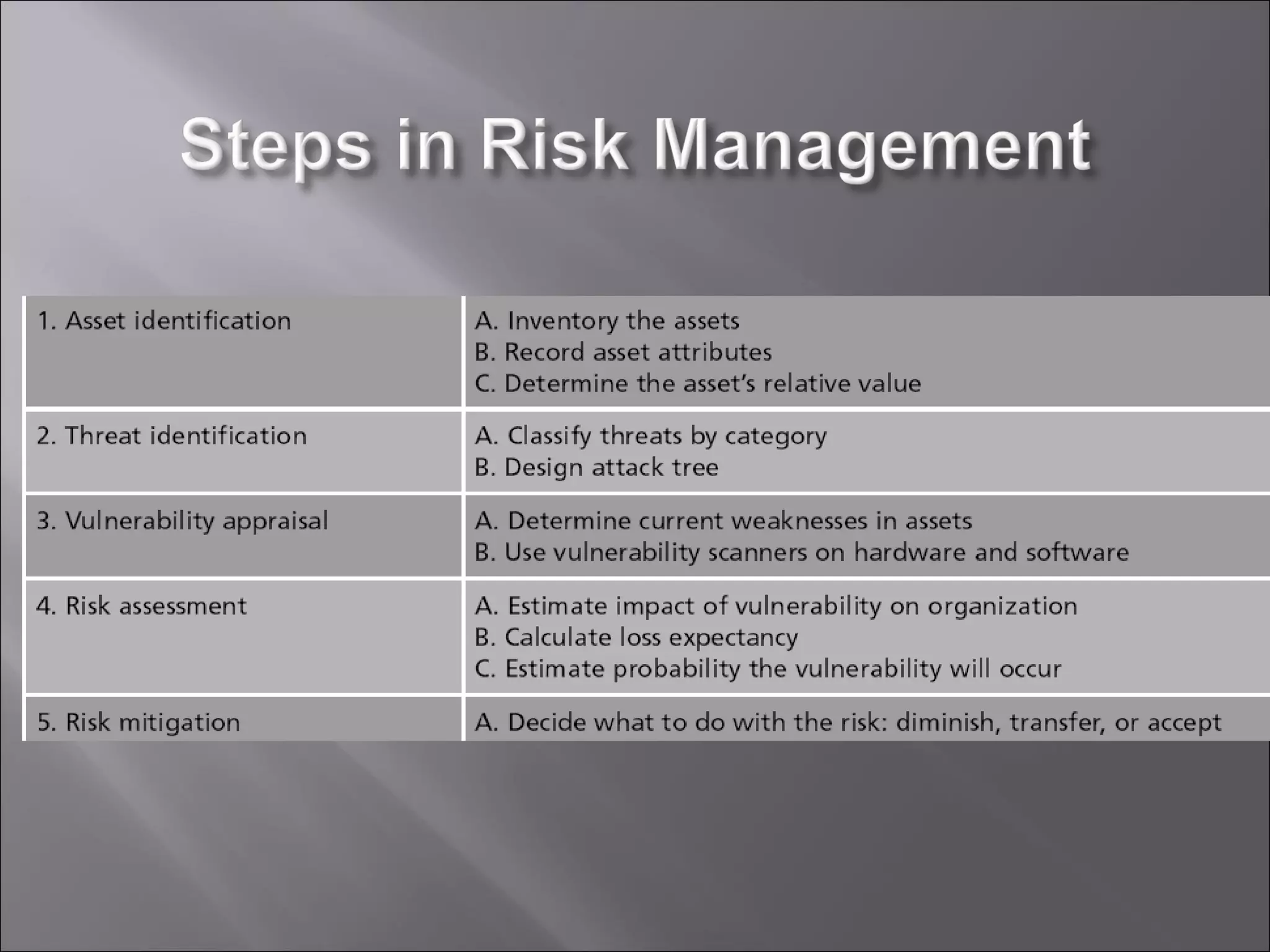
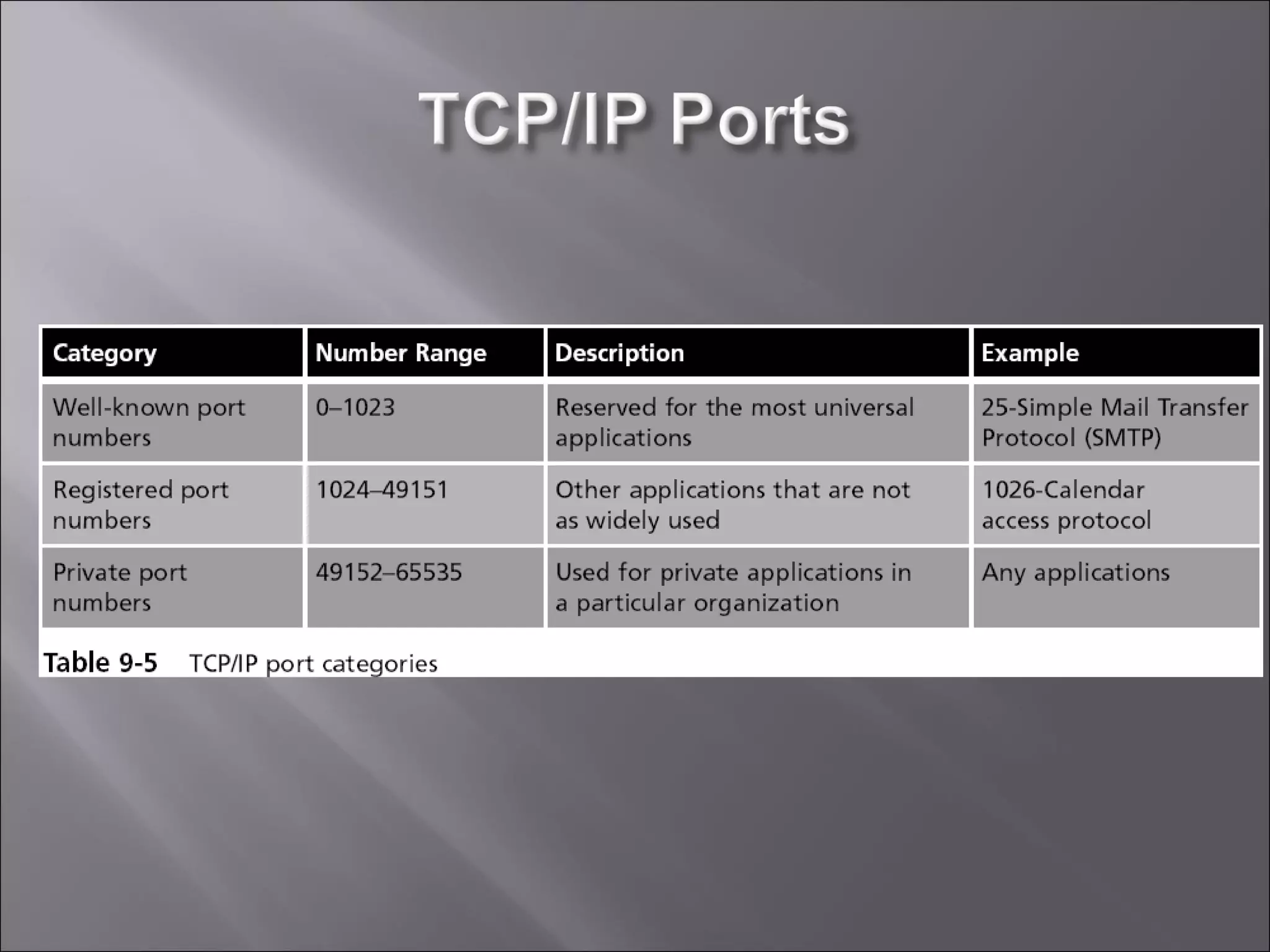
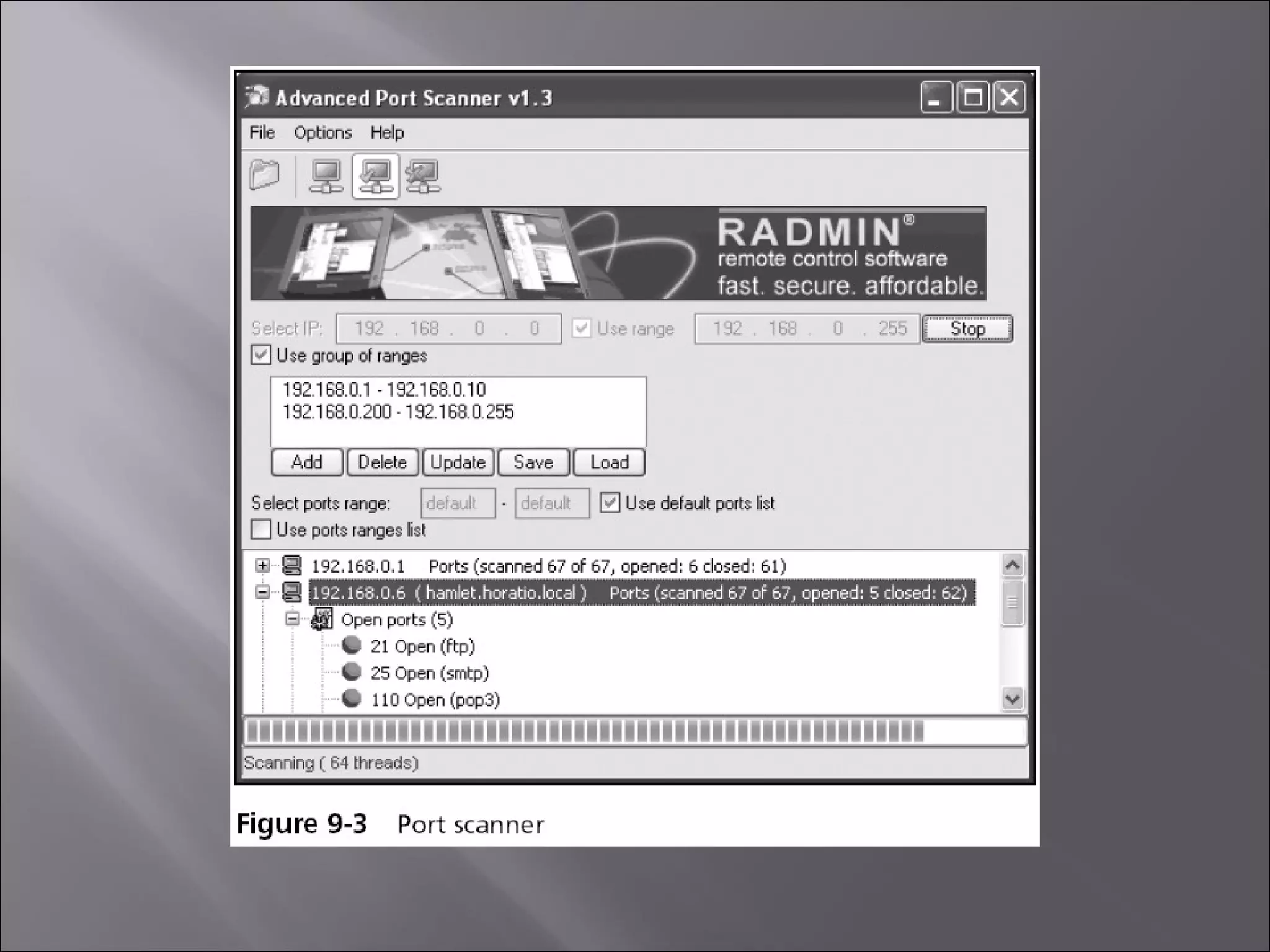
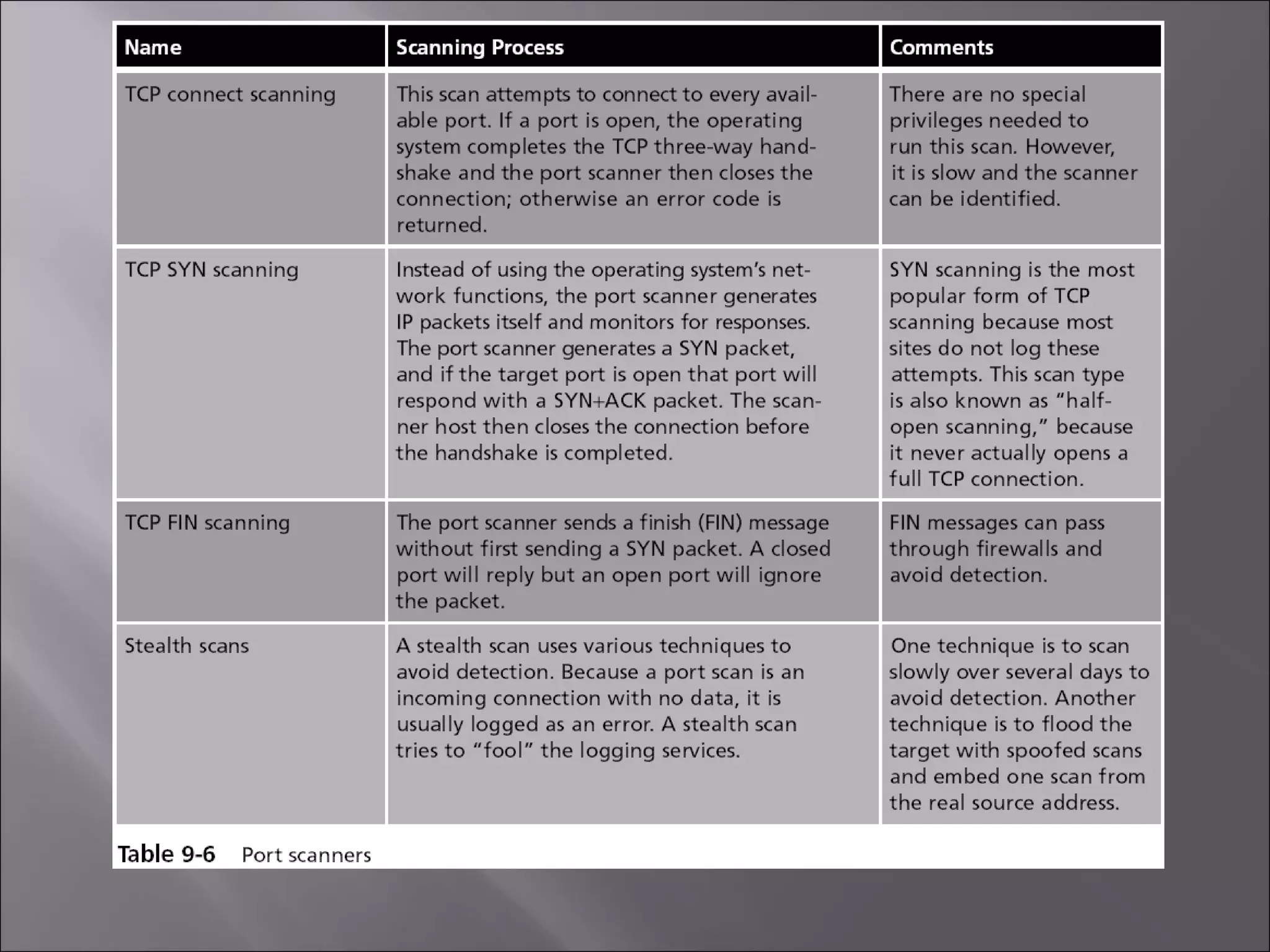
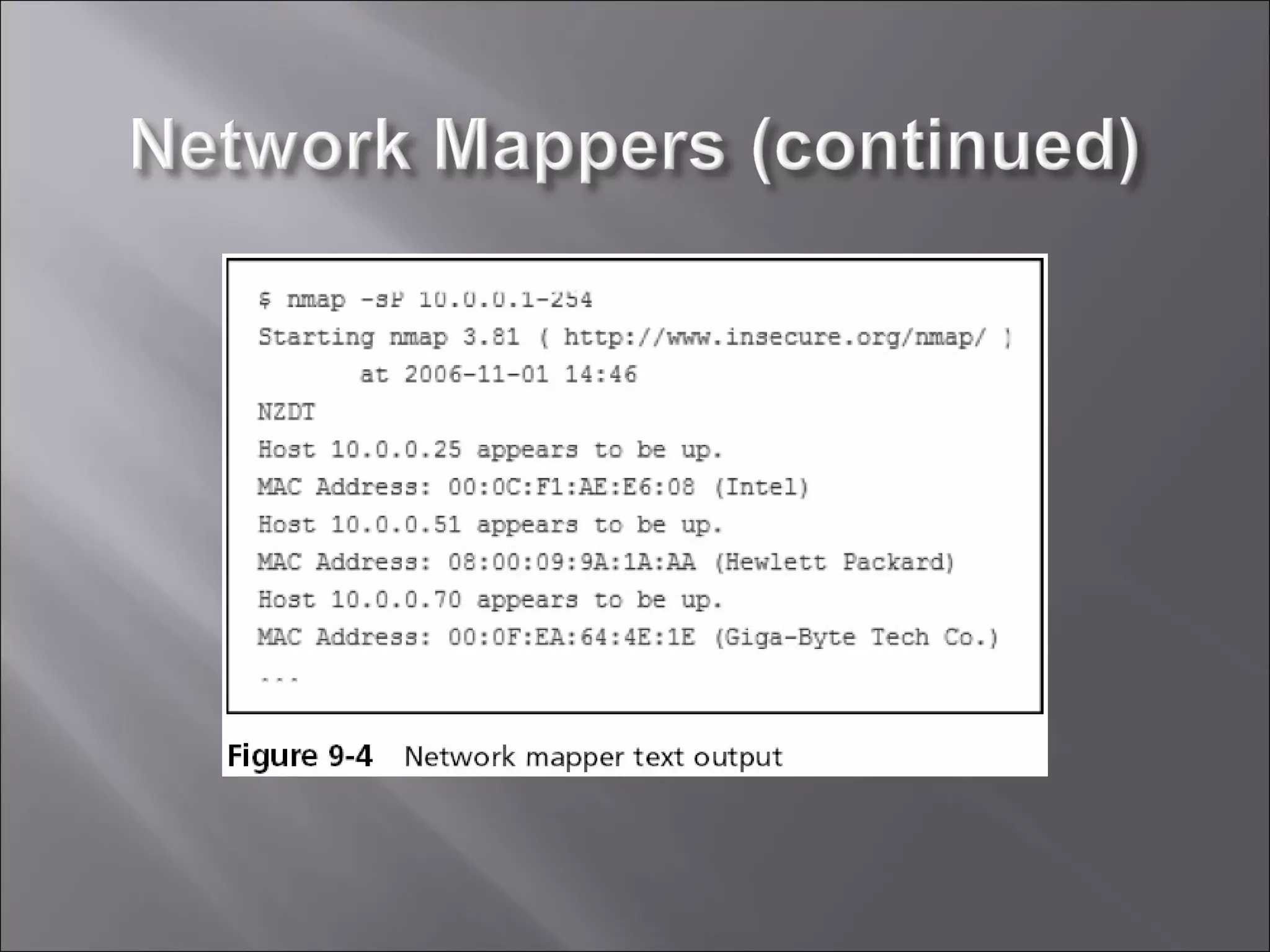
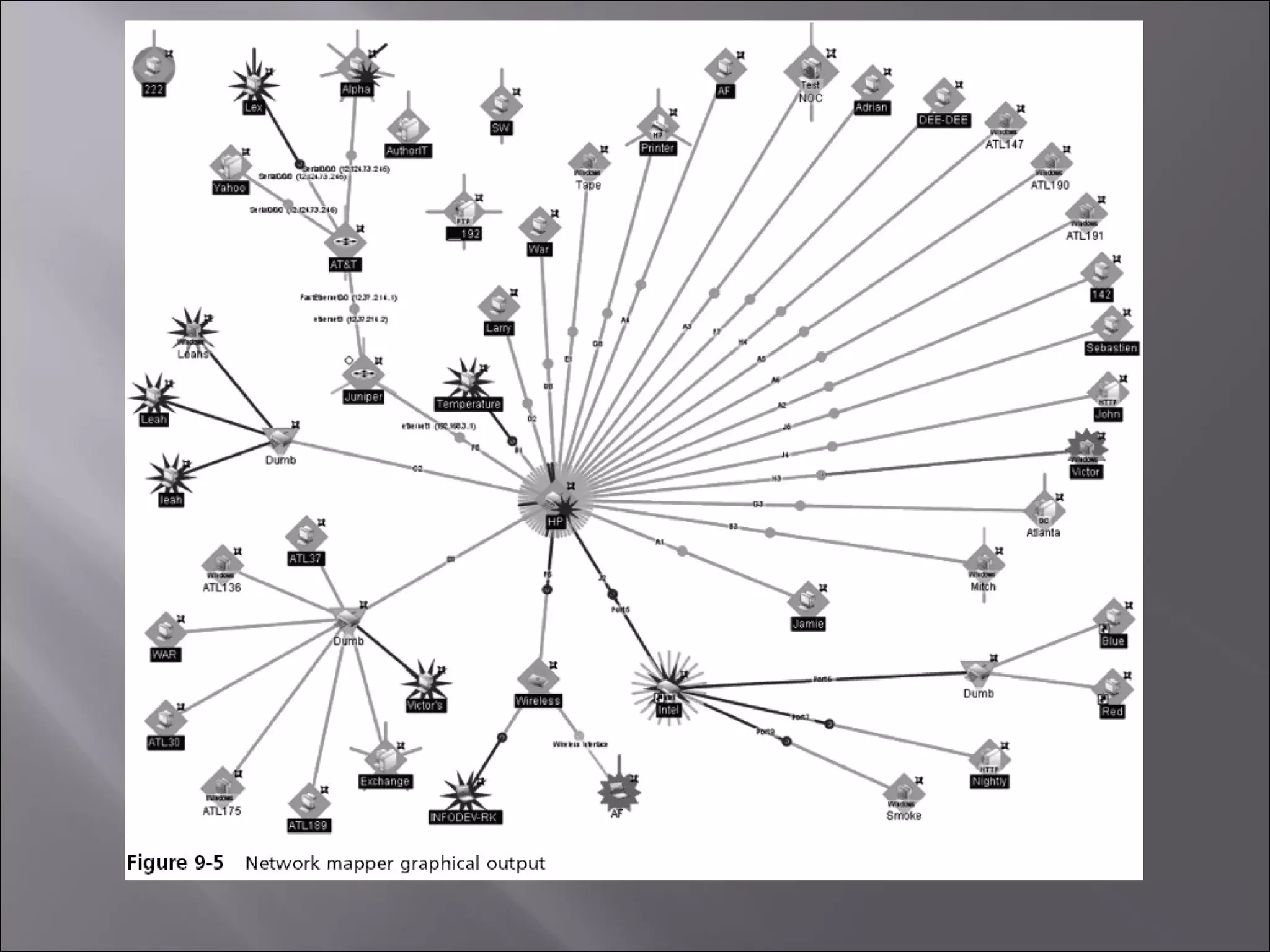
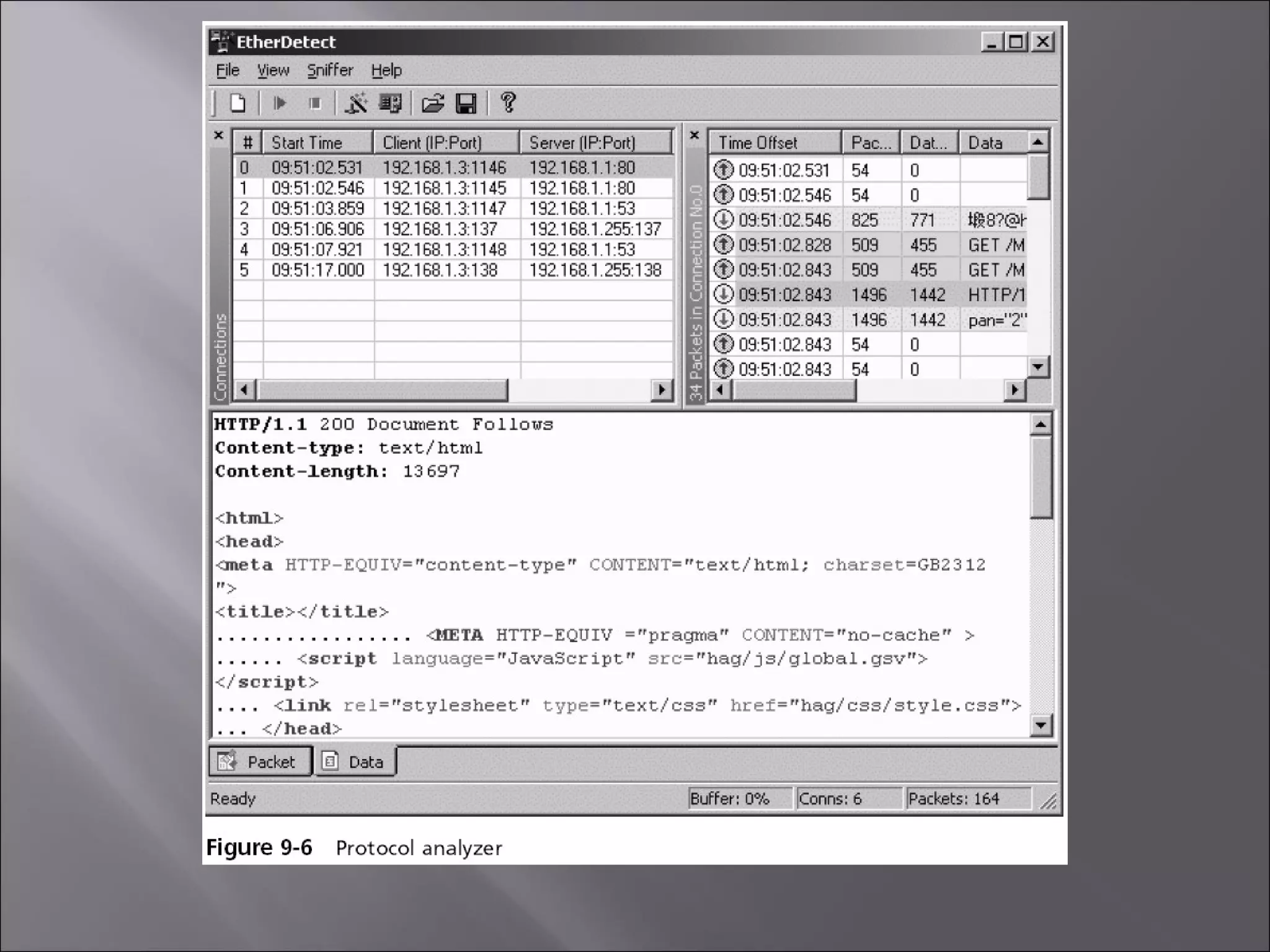
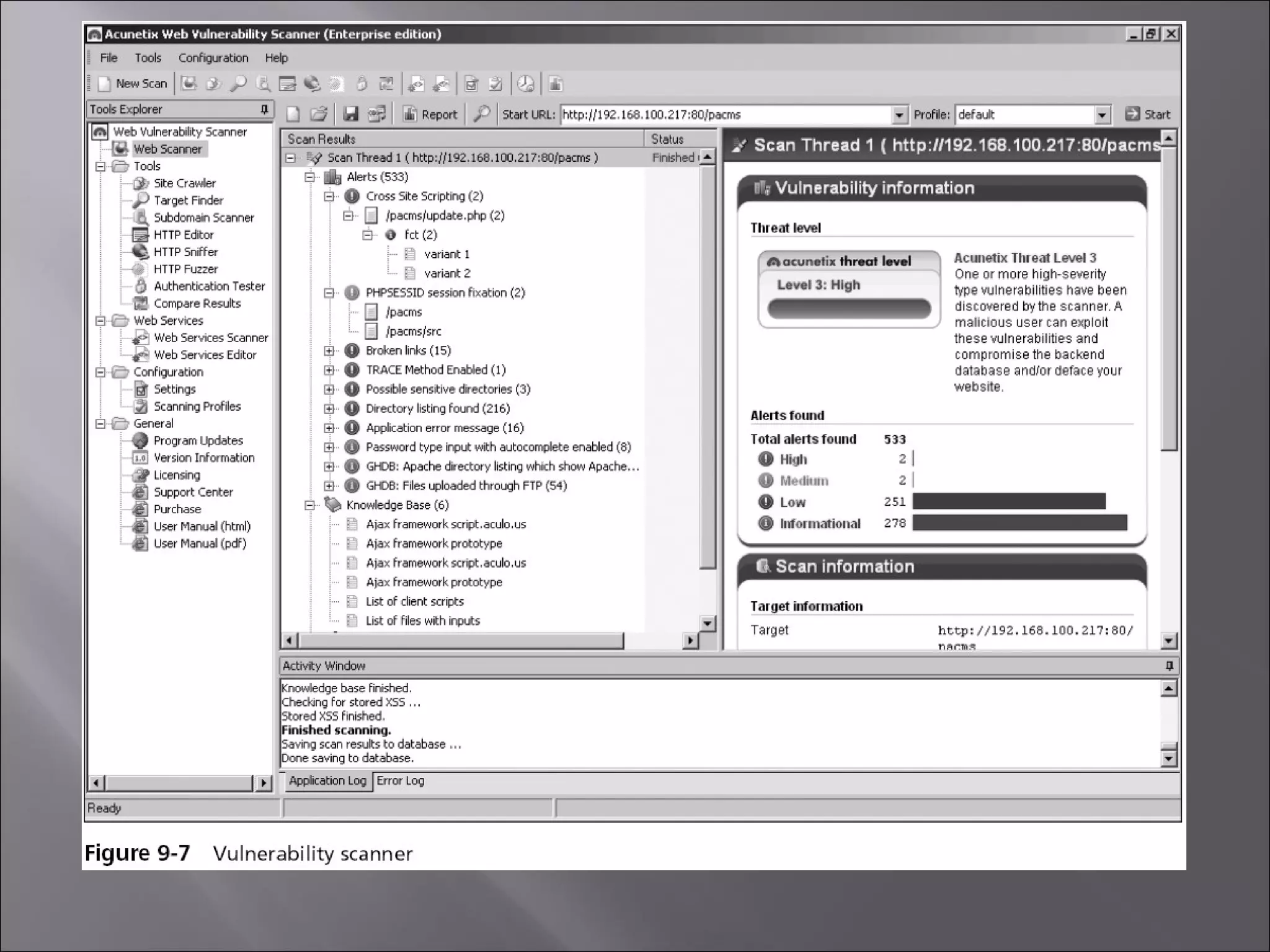
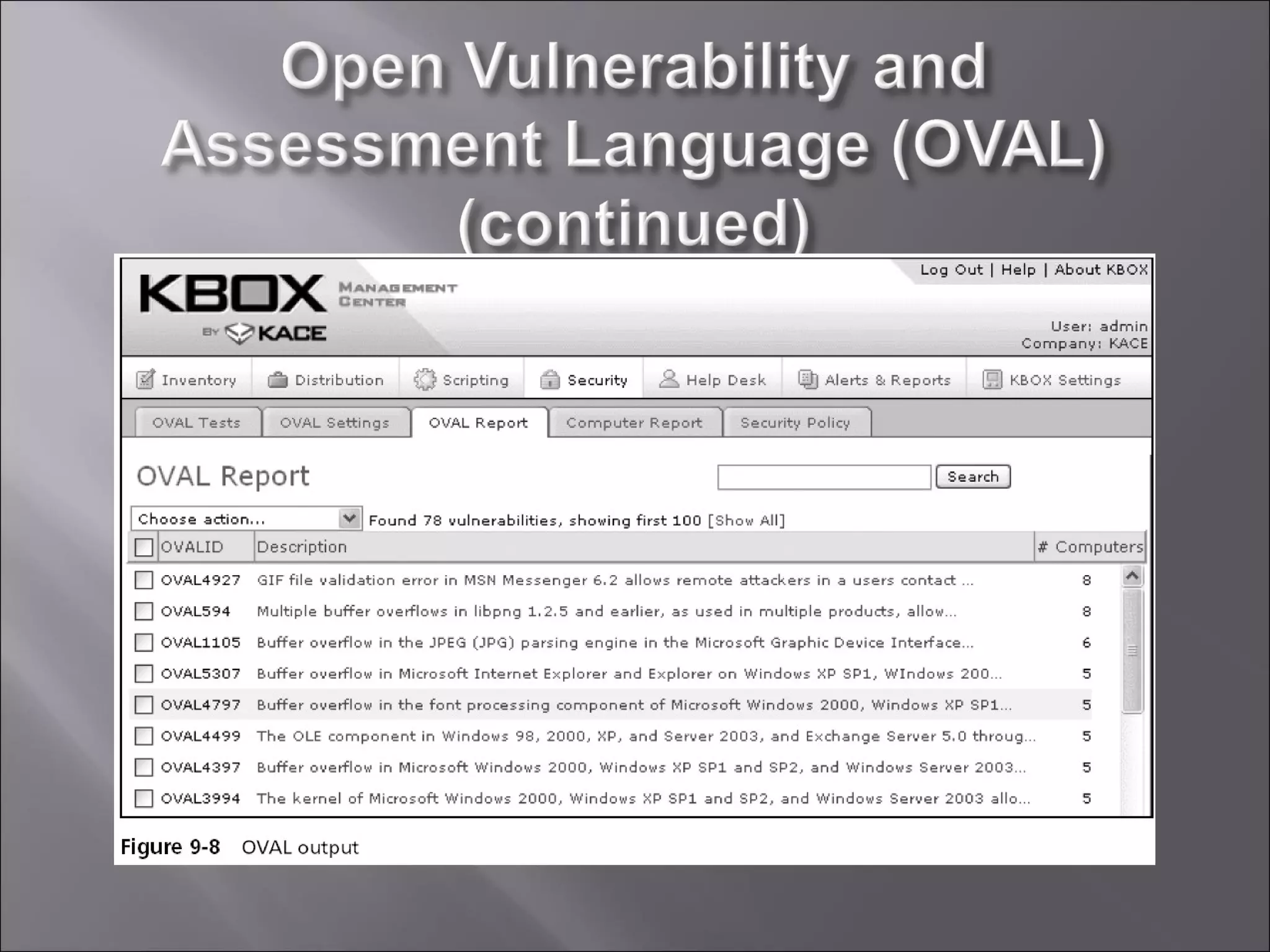
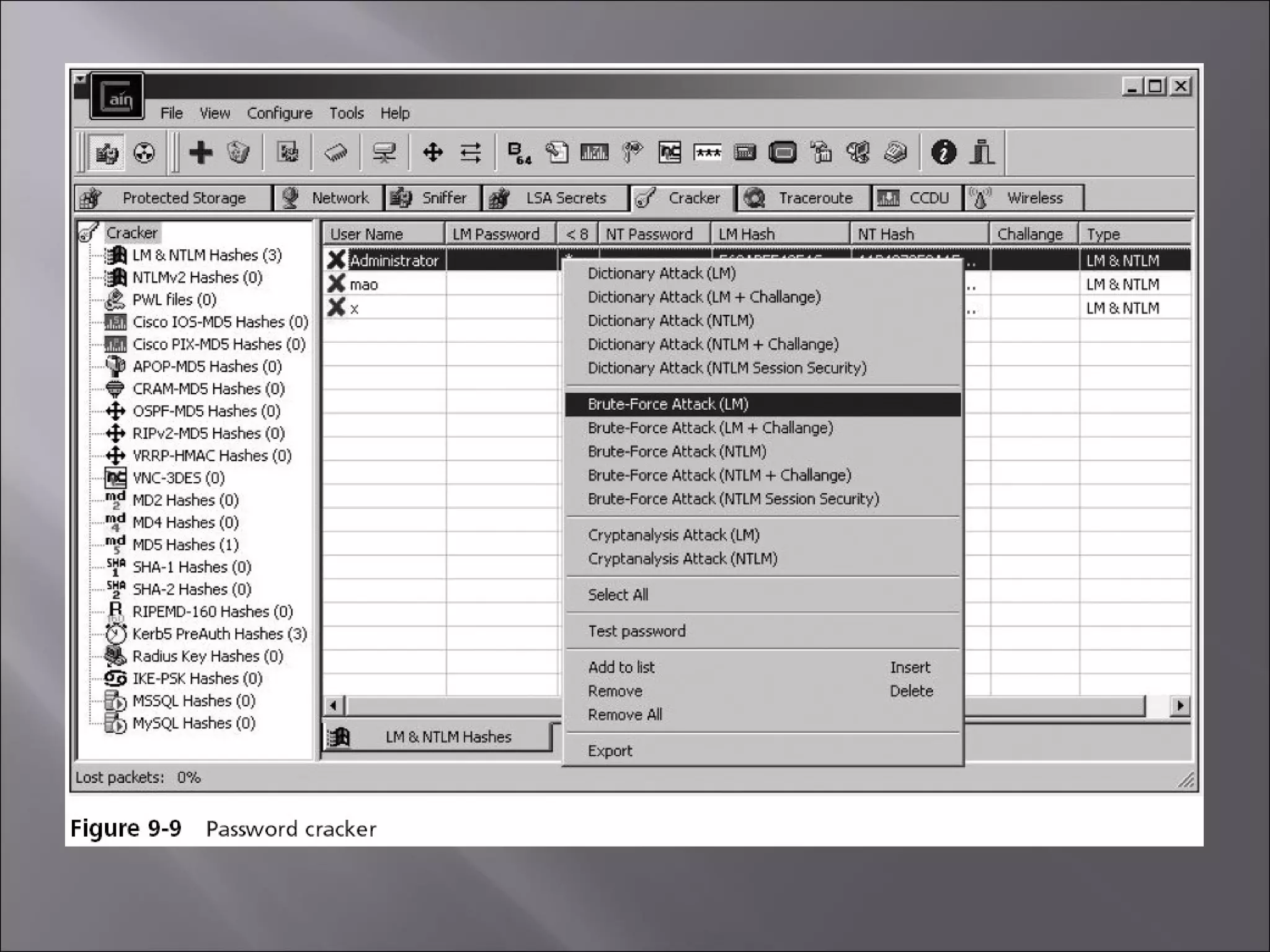
Chapter 9 discusses performing vulnerability assessments, emphasizing the importance of risk management in protecting organizational assets, particularly data. It details the steps in risk management, such as identifying assets and threats, assessing vulnerabilities, and choosing risk response strategies. The chapter also describes various tools for vulnerability scanning and penetration testing, highlighting their roles in identifying security weaknesses.