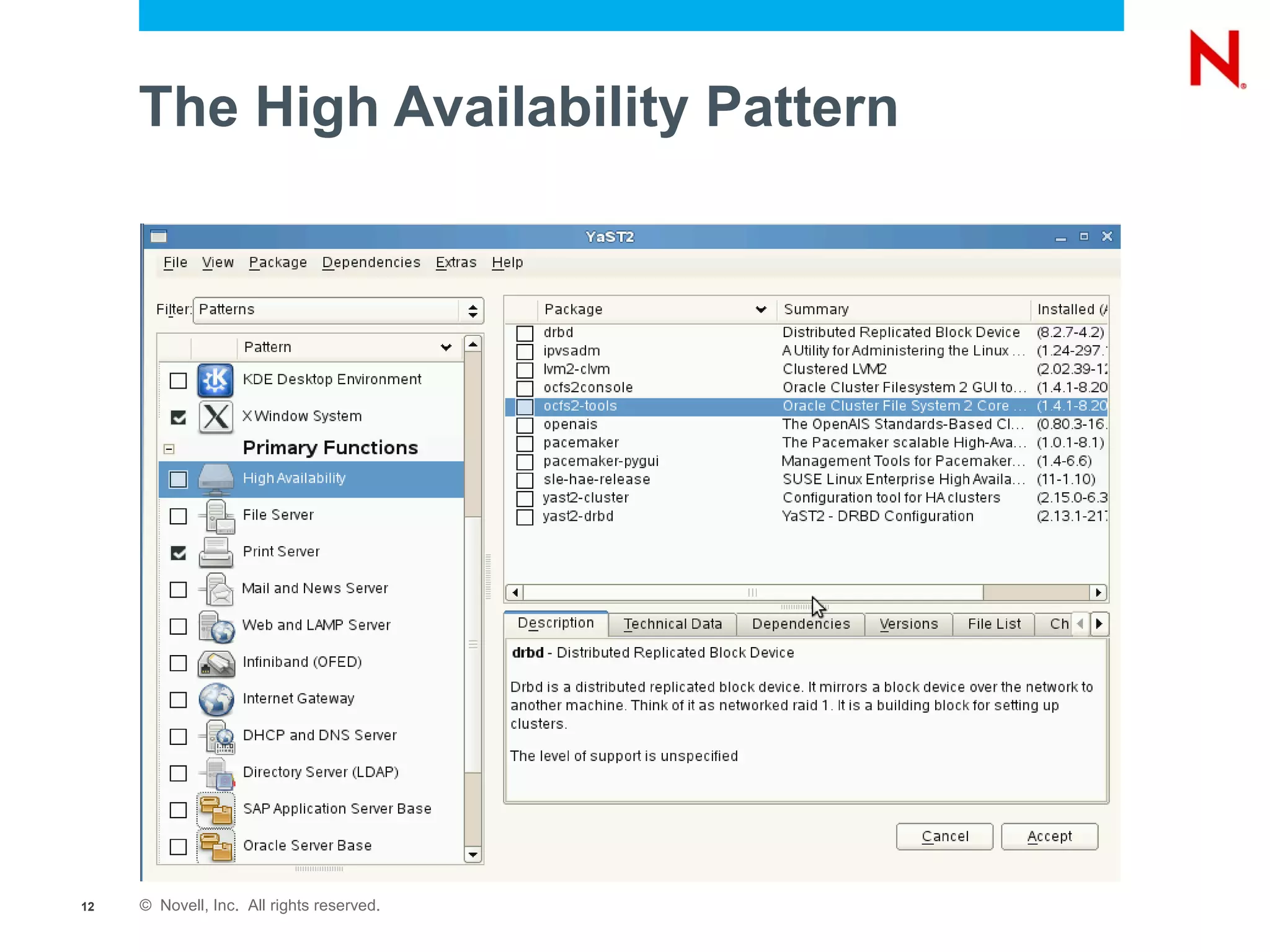
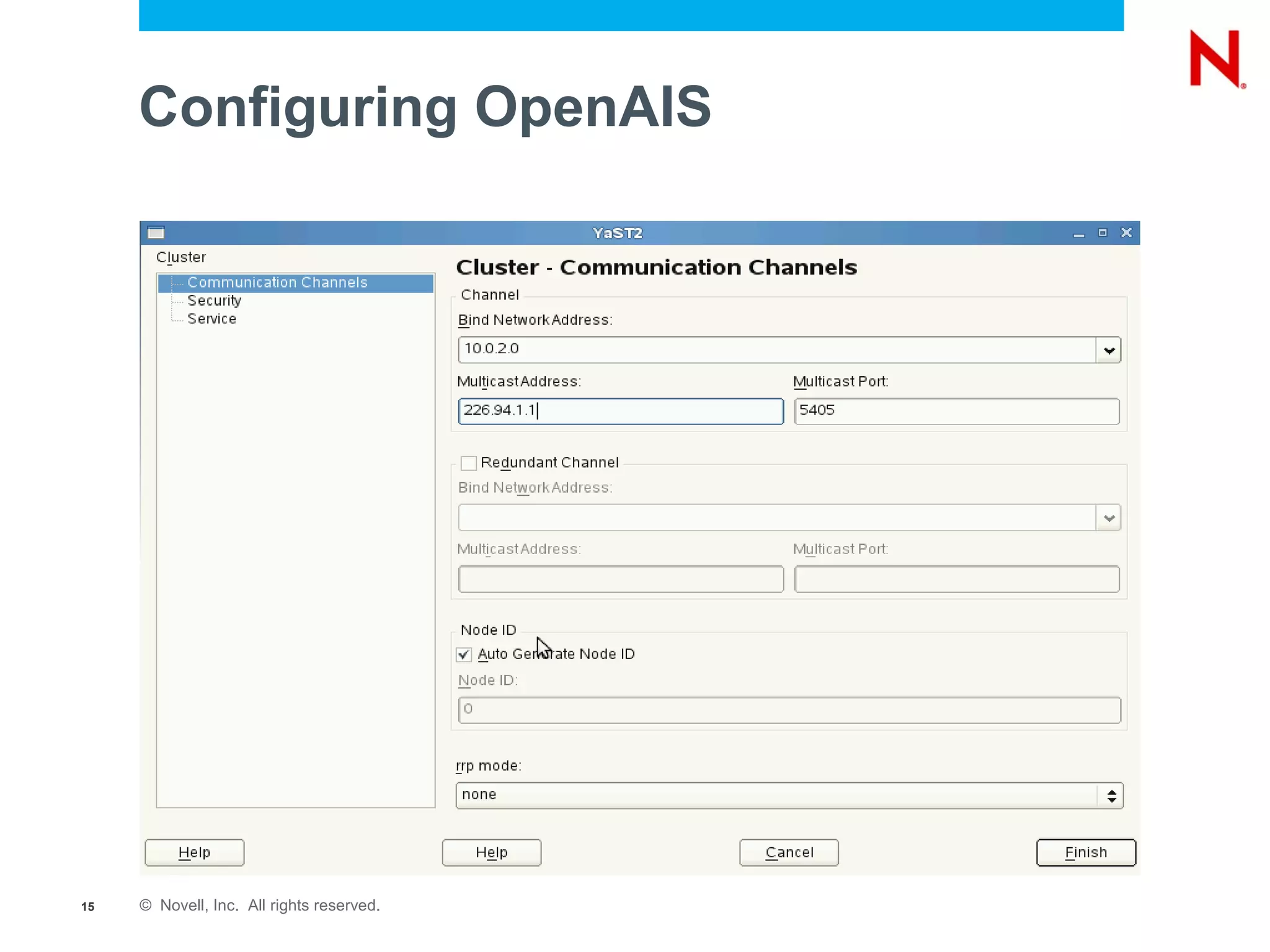
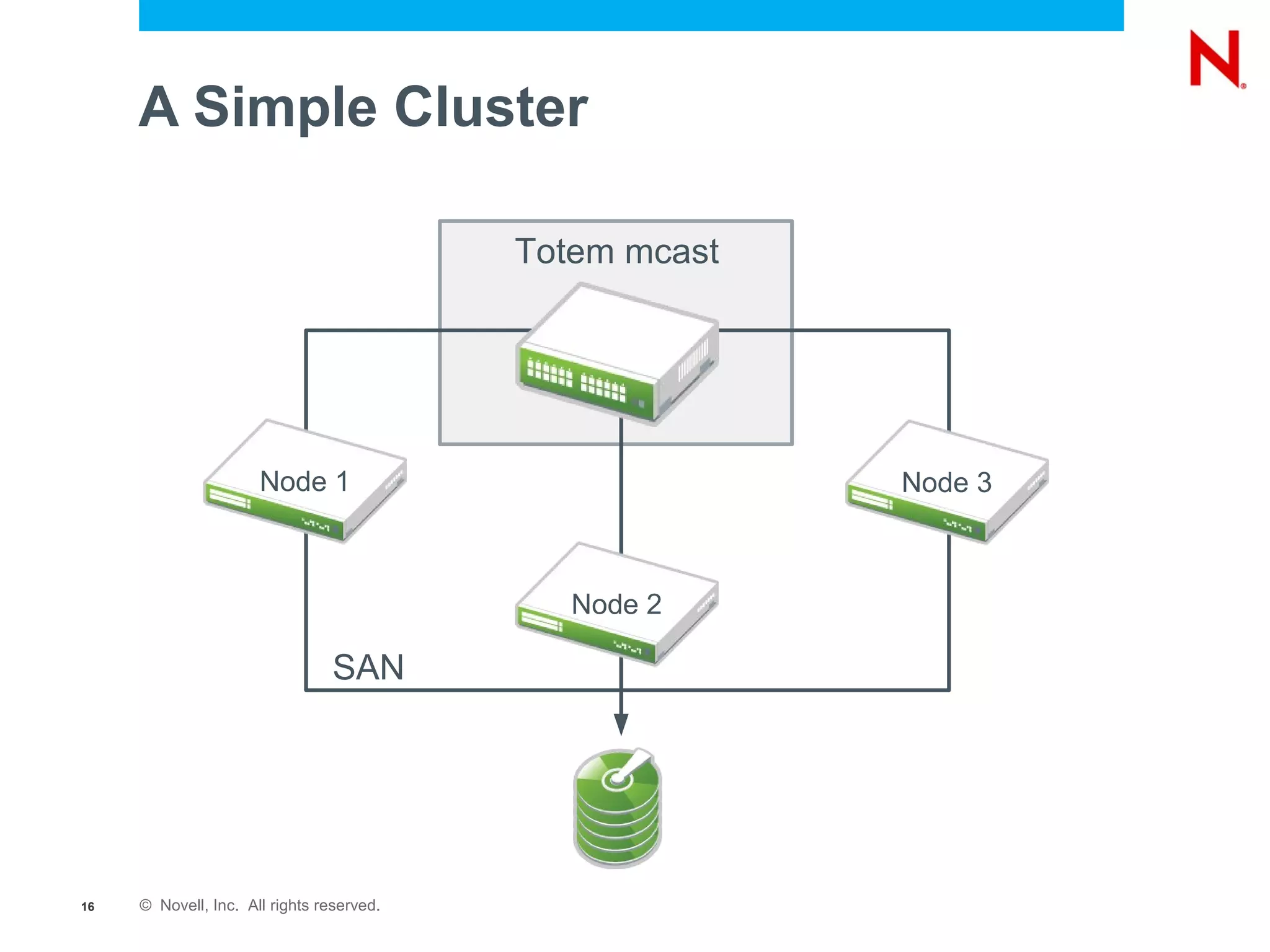
The document discusses the SUSE Linux Enterprise High Availability Extension 11, highlighting its installation, features, and benefits in minimizing downtime and managing resources effectively. It includes details on components such as clustering solutions, support for virtual workloads, and user-friendly tools for management, while also outlining significant improvements in the Service Pack 1. Additionally, it emphasizes the integration of various applications and resources, as well as features aimed at enhancing data replication and system reliability.