This document summarizes steps for auditing a Checkpoint firewall, including:
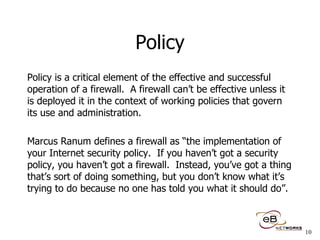
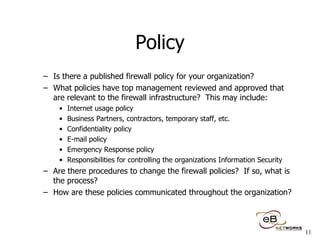
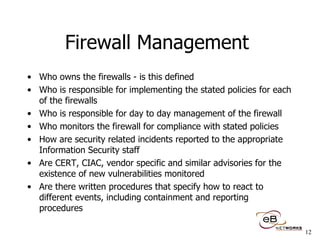
1) Reviewing the corporate firewall policy and network infrastructure.
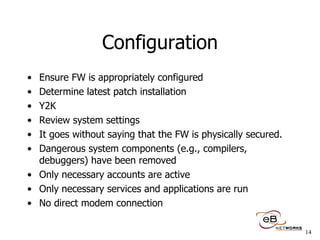
2) Running host and network assessment scans to analyze the firewall configuration and rulebase.
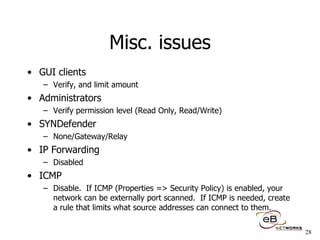
3) Ensuring the firewall is properly configured, such as having the latest patches installed and unnecessary services disabled.
4) Examining the firewall's physical security, change control procedures, and backup/contingency plans.
![Auditing Checkpoint Firewalls CSI Annual Conference 1999 Session J7 Ben Rothke, CISSP Network Security Engineer eB Networks, Inc. Iselin, New Jersey [email_address]](https://image.slidesharecdn.com/csi99auditingcheckpointfirewalls-100108122817-phpapp02/85/Auditing-Check-Point-Firewalls-1-320.jpg)



![Mailing lists CERT cert-advisory-request@ cert.org CIAC [email_address] Firewall-1 mailing list [email_address] Firewalls mailing List [email_address] Firewall Wizards List [email_address] Newsgroups comp.security.firewalls news.checkpoint.com COAST [email_address] Bugtraq [email_address] NTBugtraq [email_address] ISS X-Force Advisories [email_address]](https://image.slidesharecdn.com/csi99auditingcheckpointfirewalls-100108122817-phpapp02/85/Auditing-Check-Point-Firewalls-35-320.jpg)
![Thank You!! Ben Rothke, CISSP, CCO Network Security Engineer eB Networks, Inc. [email_address] www.ebnetworks.com Iselin, New Jersey USA](https://image.slidesharecdn.com/csi99auditingcheckpointfirewalls-100108122817-phpapp02/85/Auditing-Check-Point-Firewalls-38-320.jpg)