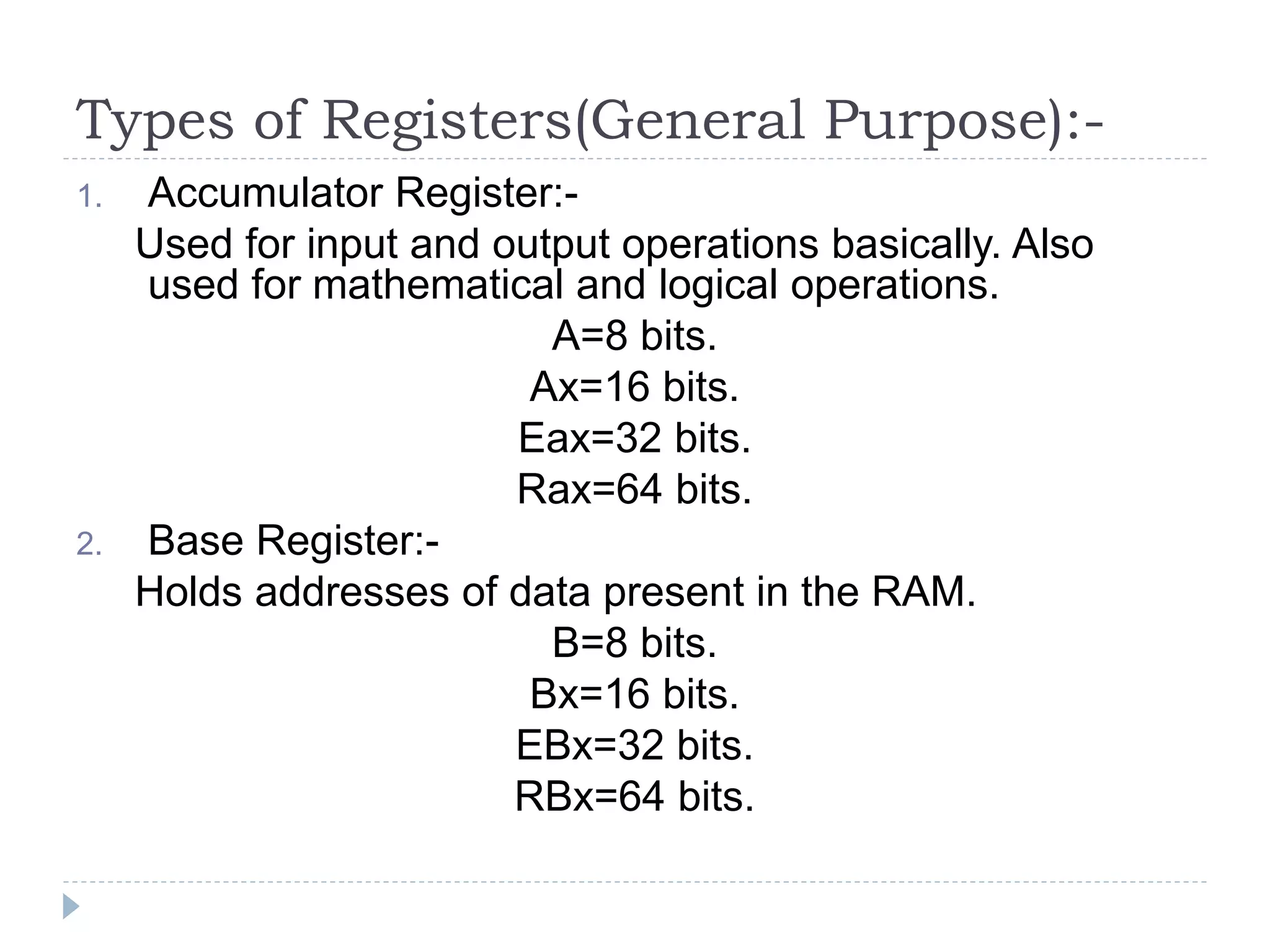
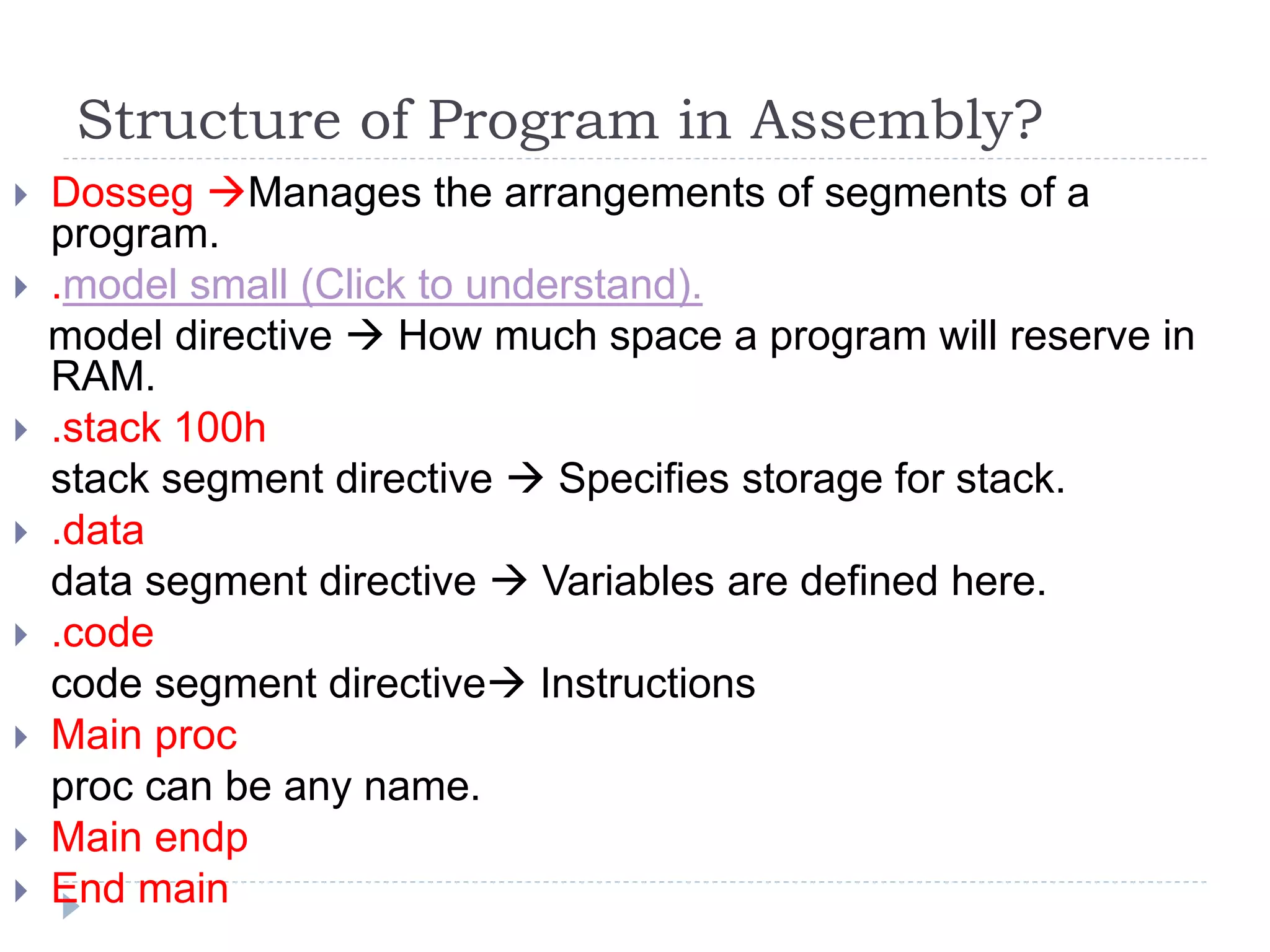
The document explains the uses and origins of assembly language, highlighting its role in optimizing processing time and managing hardware-software interactions. It covers various types of registers within the CPU, their purposes, and addressing modes for data access. Additionally, it outlines the structure of an assembly program, programming rules, and data management techniques in assembly language.