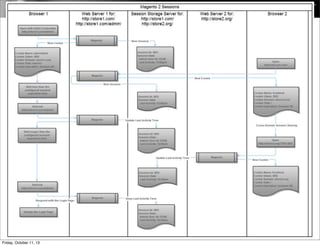
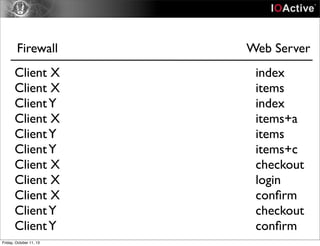
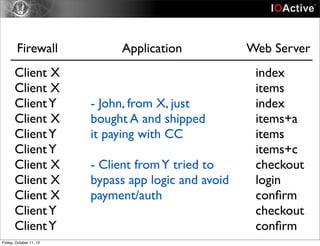
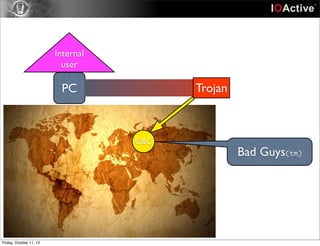
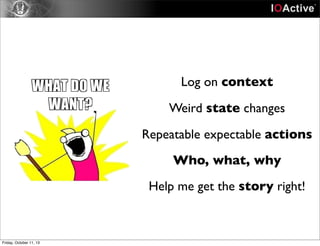
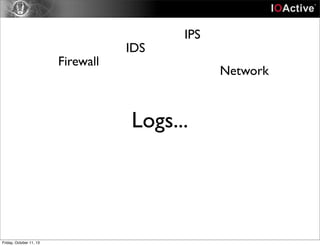
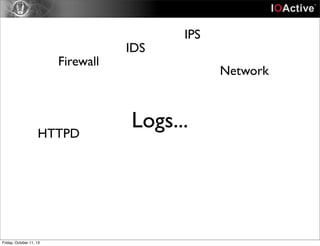
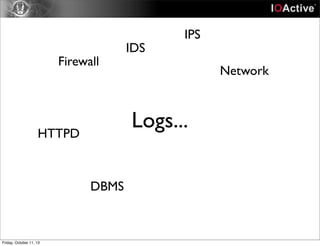
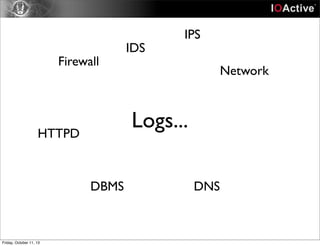
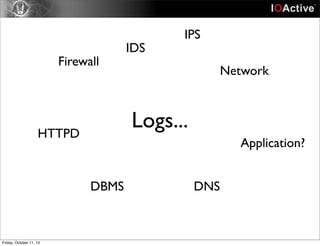
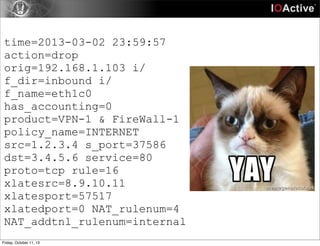
This document discusses the importance of application logs for security purposes. It notes that while network, system and other logs have improved, application logs are still often lacking crucial context about user actions and application state. To effectively investigate issues, security analysts need a unified view of all log data, including details applications have about user sessions, access and functionality used. The document urges application developers to make more of this type of contextual log data available to defenders to help connect dots between different system components and entities.



![193.205.210.42 - - [09/Oct/2013:00:57:17 -0700] "GET /blog/2013/07/mail-encryption-for-android/ HTTP/1.1" 200 32064 "https://
www.google.it/" "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_8_5) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/30.0.1599.69 Safari/
537.36"
193.205.210.42 - - [09/Oct/2013:00:57:19 -0700] "GET /blog/wp-includes/js/comment-reply.min.js?ver=3.6.1 HTTP/1.1" 200 1068 "http://
www.iamit.org/blog/2013/07/mail-encryption-for-android/" "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_8_5) AppleWebKit/537.36
(KHTML, like Gecko) Chrome/30.0.1599.69 Safari/537.36"
193.205.210.42 - - [09/Oct/2013:00:57:19 -0700] "GET /blog/wp-content/plugins/podpress/js/podpress.js?ver=3.6.1 HTTP/1.1" 200 40786
"http://www.iamit.org/blog/2013/07/mail-encryption-for-android/" "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_8_5) AppleWebKit/537.36
(KHTML, like Gecko) Chrome/30.0.1599.69 Safari/537.36"
193.205.210.42 - - [09/Oct/2013:00:57:19 -0700] "GET /blog/wp-content/plugins/jetpack/modules/sharedaddy/sharing.css?ver=2.5 HTTP/
1.1" 200 11641 "http://www.iamit.org/blog/2013/07/mail-encryption-for-android/" "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_8_5)
AppleWebKit/537.36 (KHTML, like Gecko) Chrome/30.0.1599.69 Safari/537.36"
193.205.210.42 - - [09/Oct/2013:00:57:19 -0700] "GET /blog/wp-content/plugins/lightbox-2/lightbox.js?ver=1.8 HTTP/1.1" 200 21623
"http://www.iamit.org/blog/2013/07/mail-encryption-for-android/" "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_8_5) AppleWebKit/537.36
(KHTML, like Gecko) Chrome/30.0.1599.69 Safari/537.36"
193.205.210.42 - - [09/Oct/2013:00:57:19 -0700] "GET /blog/wp-includes/js/jquery/jquery-migrate.min.js?ver=1.2.1 HTTP/1.1" 200 7484
"http://www.iamit.org/blog/2013/07/mail-encryption-for-android/" "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_8_5) AppleWebKit/537.36
(KHTML, like Gecko) Chrome/30.0.1599.69 Safari/537.36"
193.205.210.42 - - [09/Oct/2013:00:57:20 -0700] "GET /blog/wp-content/plugins/podpress/players/1pixelout/1pixelout_audio-player.js
HTTP/1.1" 200 12305 "http://www.iamit.org/blog/2013/07/mail-encryption-for-android/" "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_8_5)
AppleWebKit/537.36 (KHTML, like Gecko) Chrome/30.0.1599.69 Safari/537.36"
193.205.210.42 - - [09/Oct/2013:00:57:20 -0700] "GET /blog/wp-content/plugins/jetpack/modules/wpgroho.js?ver=3.6.1 HTTP/1.1" 200
1212 "http://www.iamit.org/blog/2013/07/mail-encryption-for-android/" "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_8_5) AppleWebKit/
537.36 (KHTML, like Gecko) Chrome/30.0.1599.69 Safari/537.36"
193.205.210.42 - - [09/Oct/2013:00:57:20 -0700] "GET /blog/wp-content/plugins/jetpack/modules/sharedaddy/sharing.js?ver=20121205
HTTP/1.1" 200 39040 "http://www.iamit.org/blog/2013/07/mail-encryption-for-android/" "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_8_5)
AppleWebKit/537.36 (KHTML, like Gecko) Chrome/30.0.1599.69 Safari/537.36"
193.205.210.42 - - [09/Oct/2013:00:57:21 -0700] "GET /blog/wp-content/plugins/contact-form-7/includes/js/scripts.js?ver=3.5.2 HTTP/1.1"
200 8610 "http://www.iamit.org/blog/2013/07/mail-encryption-for-android/" "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_8_5) AppleWebKit/
537.36 (KHTML, like Gecko) Chrome/30.0.1599.69 Safari/537.36"
193.205.210.42 - - [09/Oct/2013:00:57:21 -0700] "GET /blog/wp-content/plugins/contact-form-7/includes/js/jquery.form.min.js?
ver=3.40.0-2013.08.13 HTTP/1.1" 200 14910 "http://www.iamit.org/blog/2013/07/mail-encryption-for-android/" "Mozilla/5.0 (Macintosh;
Intel Mac OS X 10_8_5) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/30.0.1599.69 Safari/537.36"
193.205.210.42 - - [09/Oct/2013:00:57:23 -0700] "GET /favicon.ico HTTP/1.1" 200 1351 "-" "Mozilla/5.0 (Macintosh; Intel Mac OS X
10_8_5) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/30.0.1599.69 Safari/537.36"
193.205.210.42 - - [09/Oct/2013:00:57:23 -0700] "GET /blog/wp-includes/js/jquery/jquery.js?ver=1.10.2 HTTP/1.1" 200 93371 "http://
www.iamit.org/blog/2013/07/mail-encryption-for-android/" "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_8_5) AppleWebKit/537.36Friday, October 11, 13](https://image.slidesharecdn.com/armorizingapplications-131011124412-phpapp01/85/Armorizing-applications-33-320.jpg)