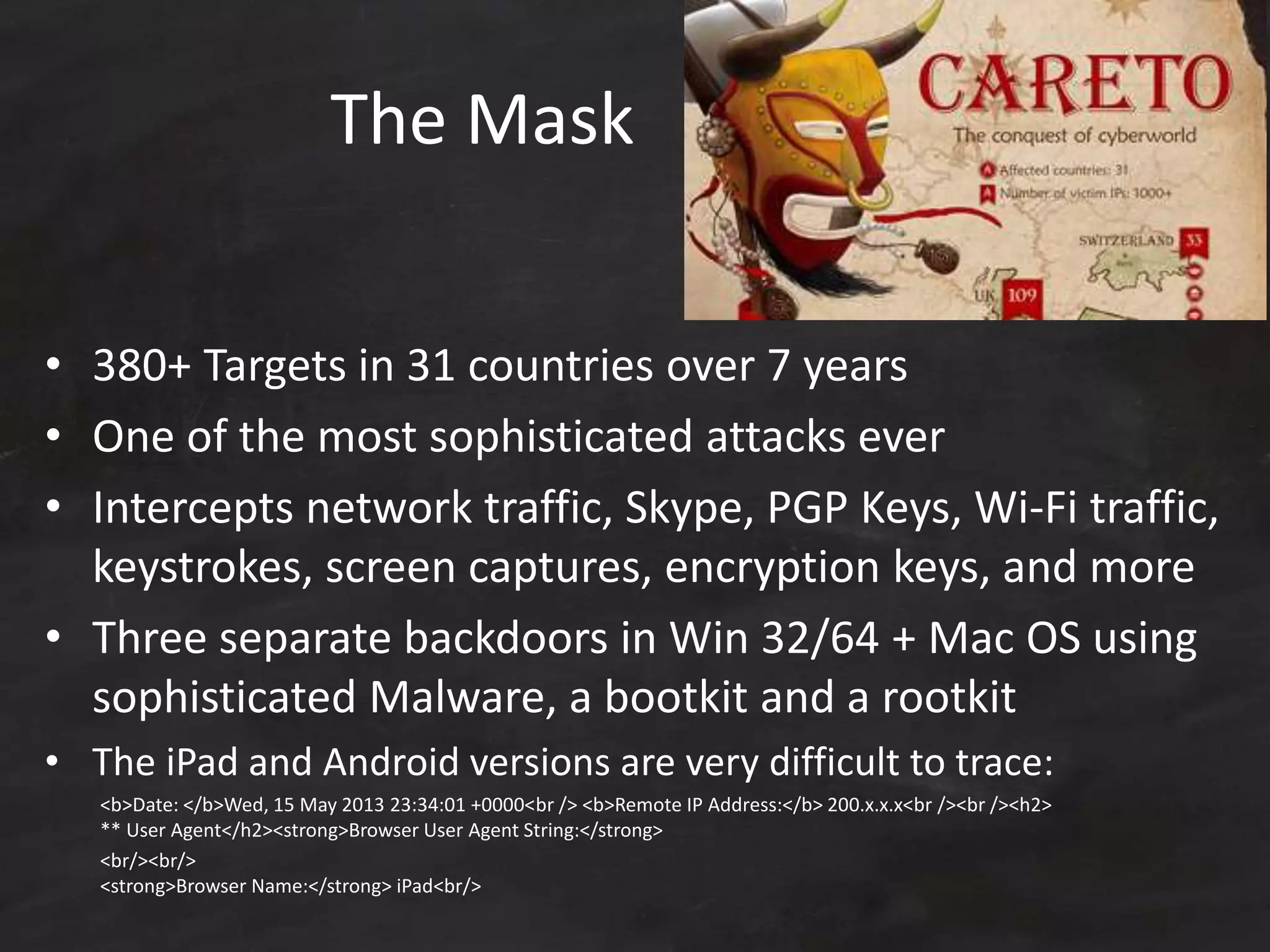
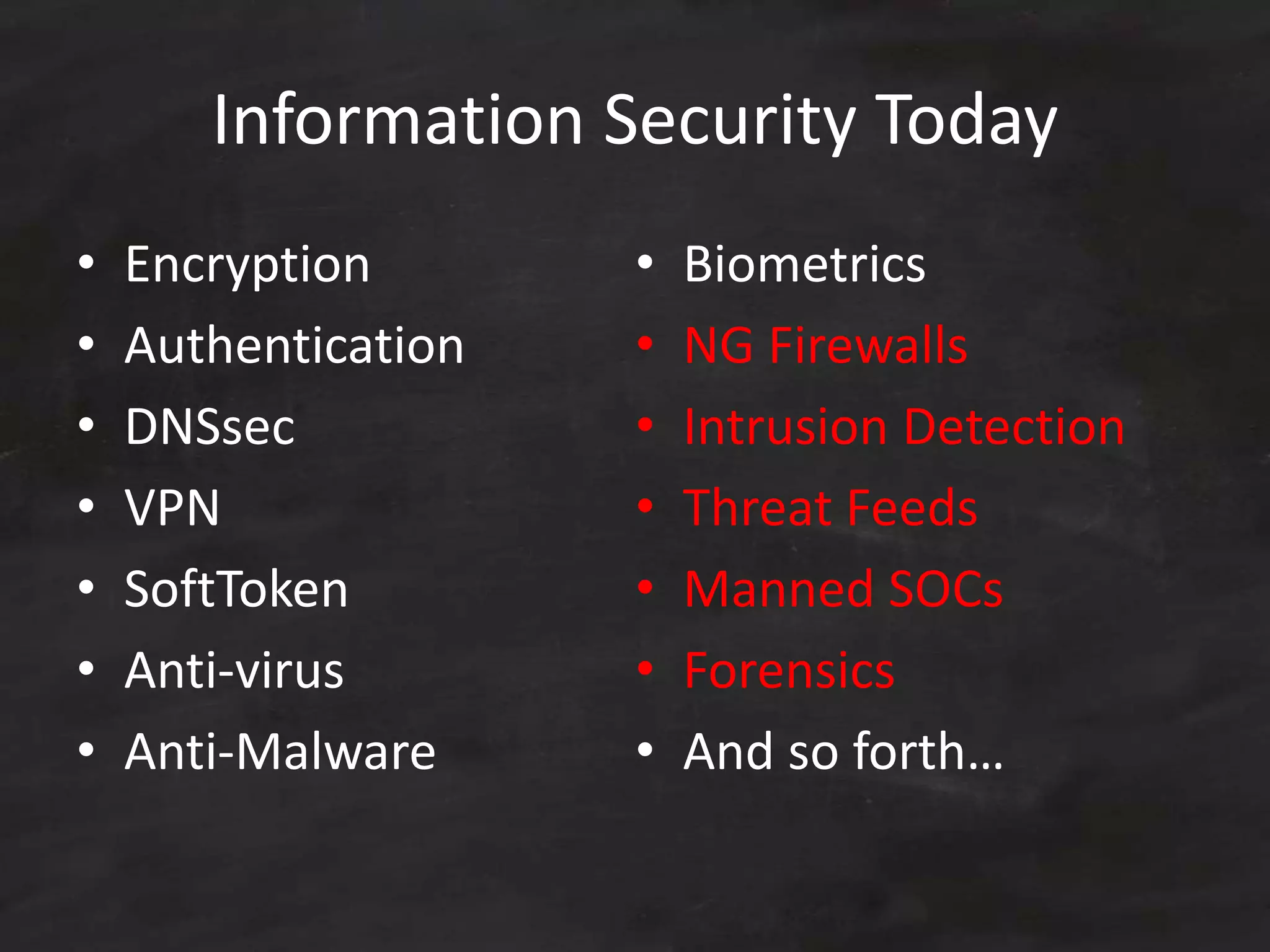
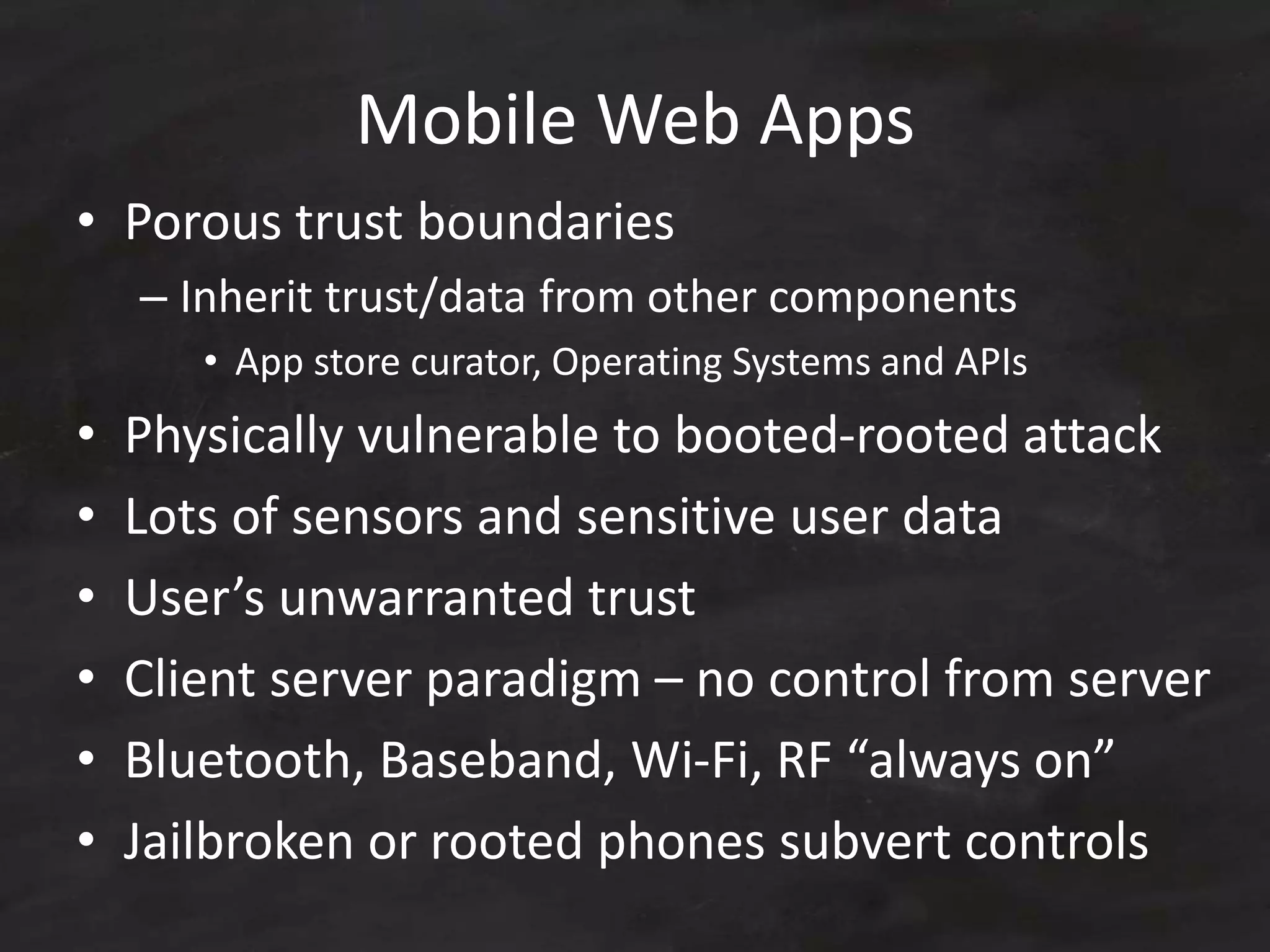
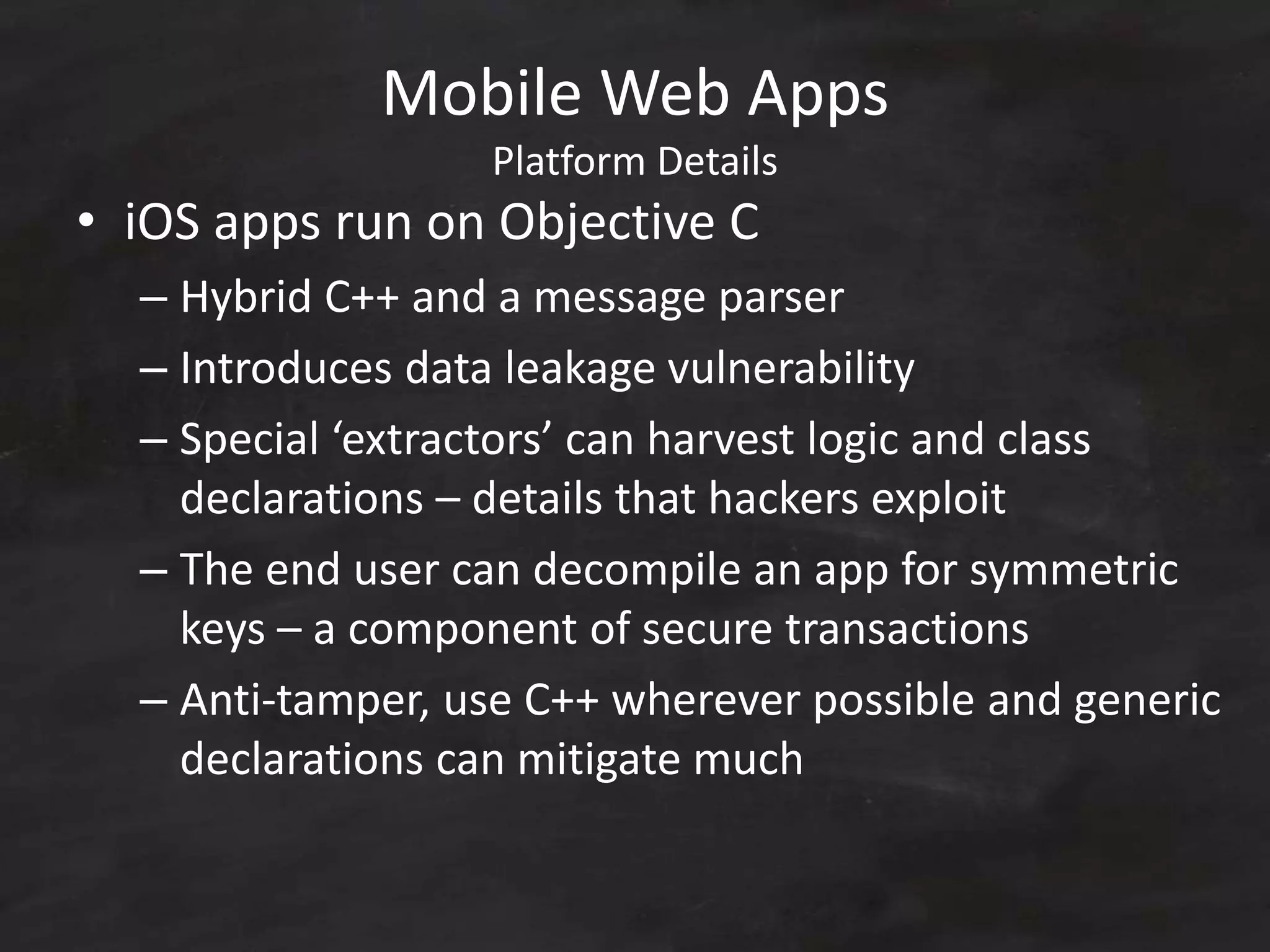
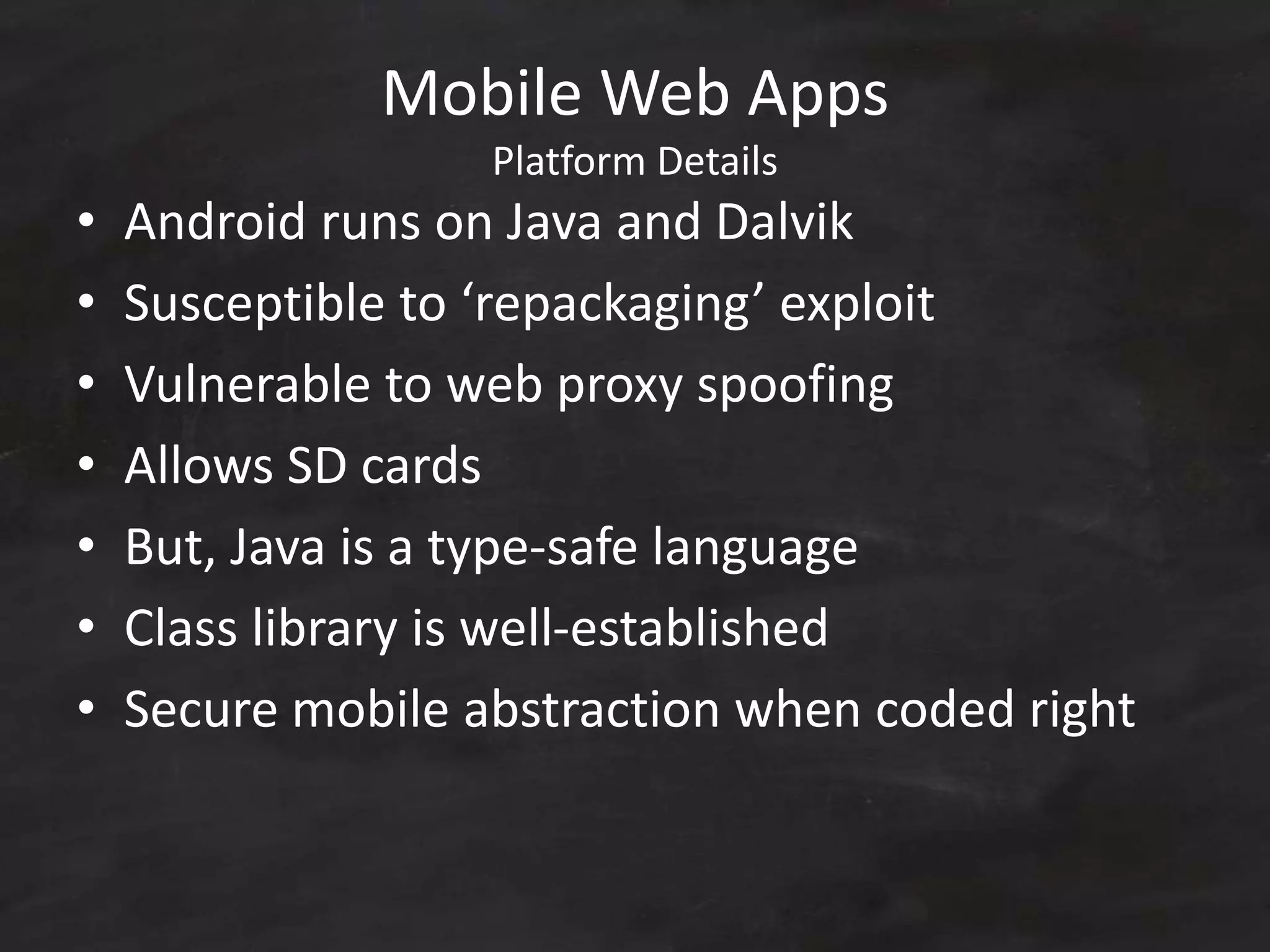
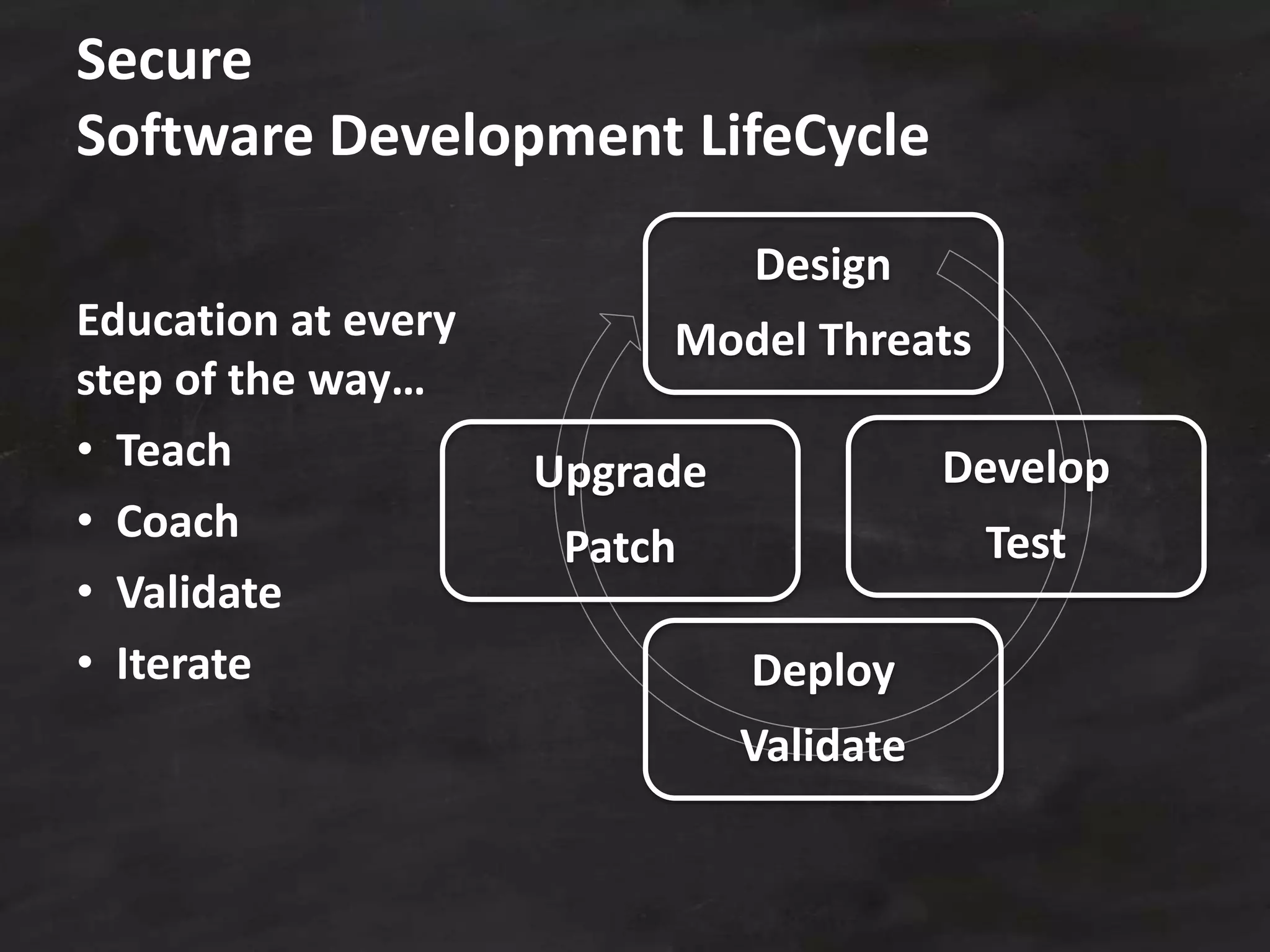
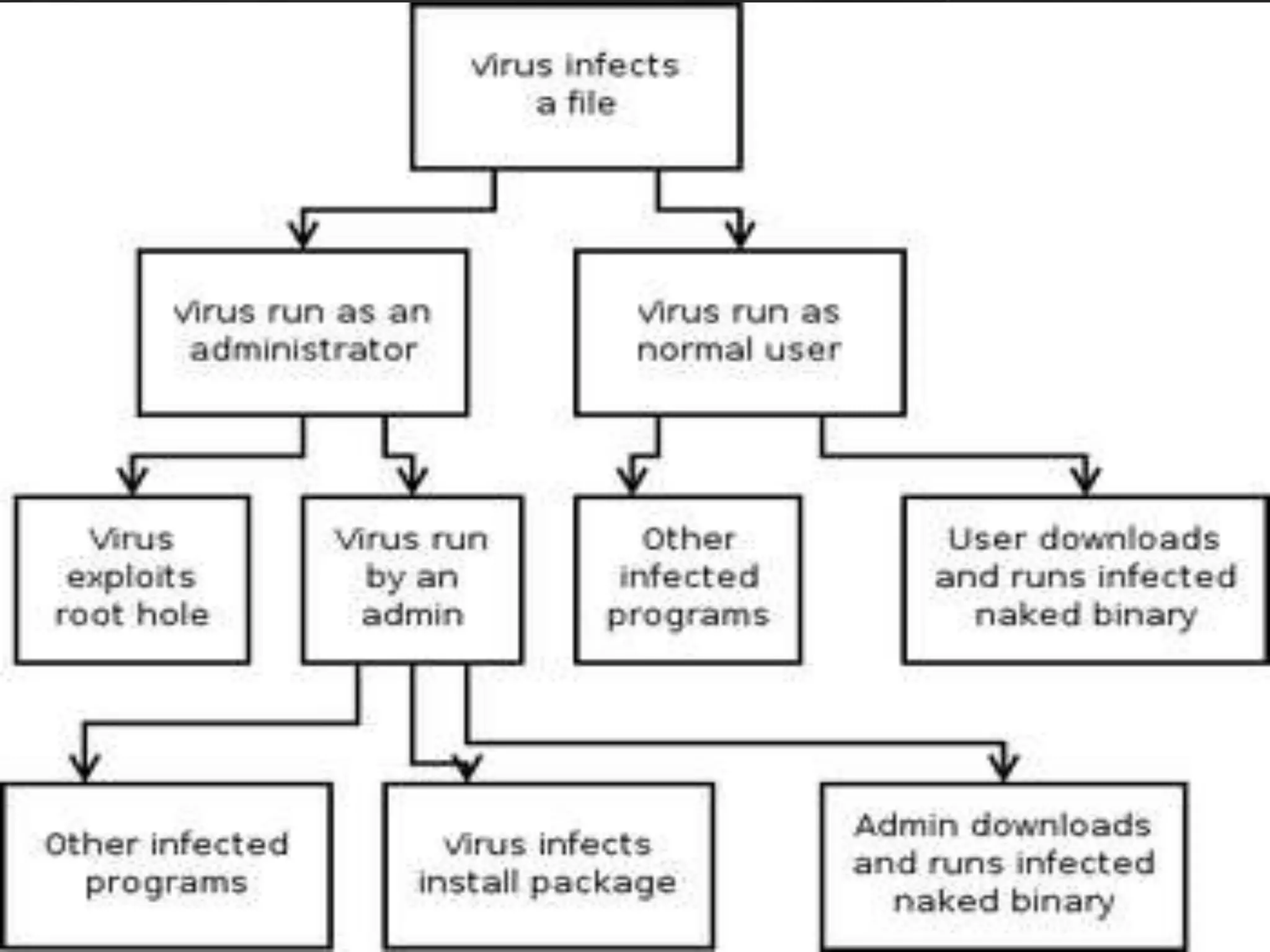
This document summarizes an information security presentation about keeping secrets in the Internet of Things era. It discusses increasing vulnerabilities and dependencies, limitations of current security approaches, and motivations for lack of trust. It then covers secure software development best practices including threat modeling techniques. Lastly, it discusses solutions for organizations and end users, including encryption, authentication, firewalls, intrusion detection and more. Specific examples of security breaches like Heartbleed, Snapchat, and PlaceRaider are also summarized.