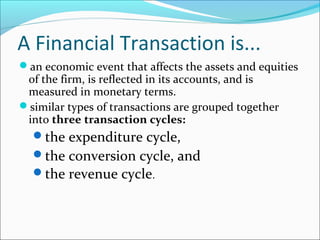
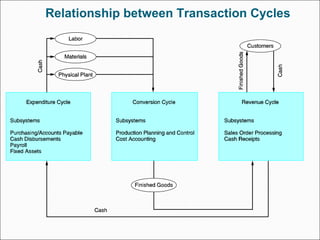
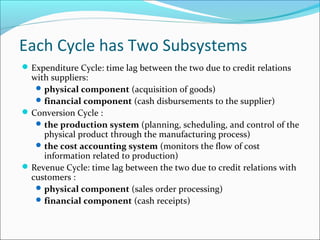
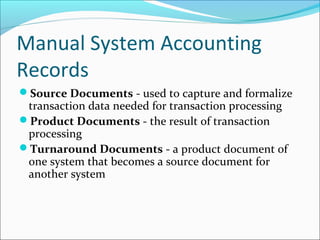
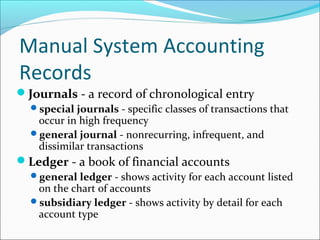
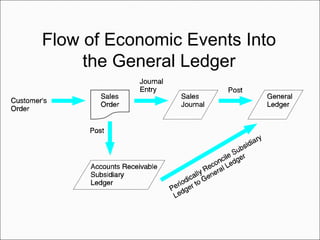
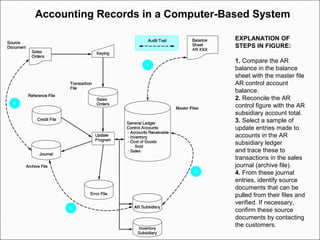
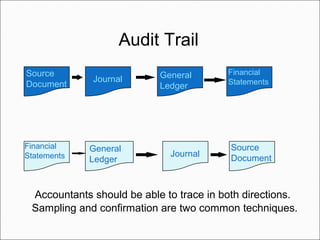
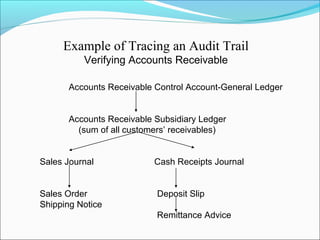
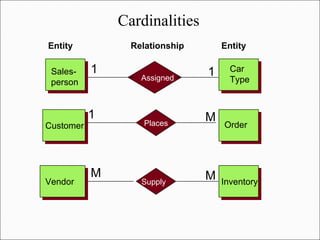
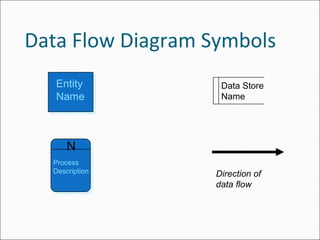
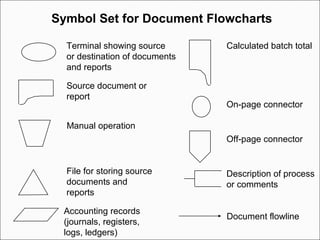
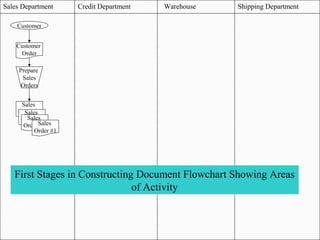
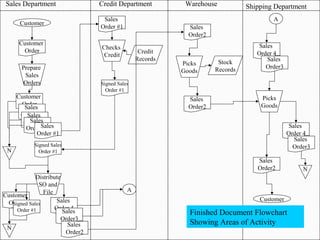
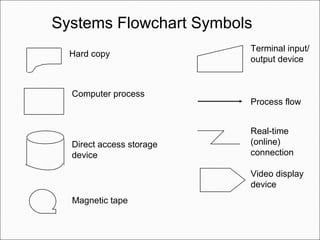
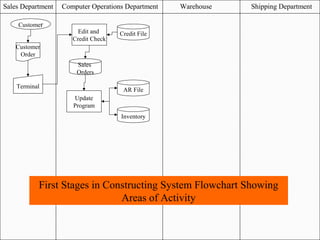
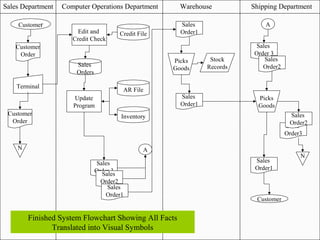
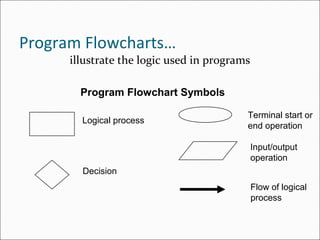
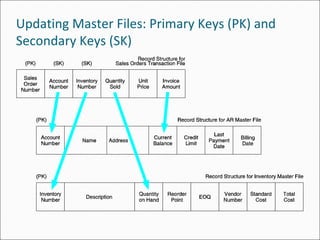
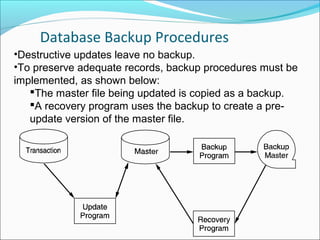
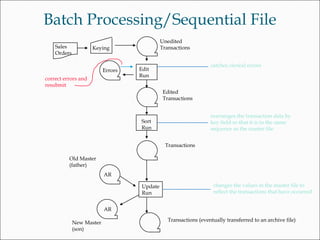
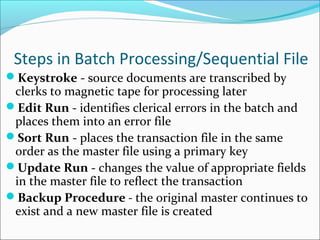
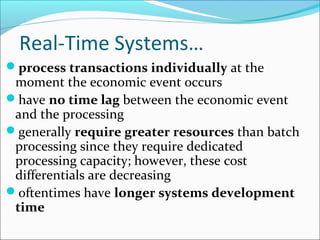
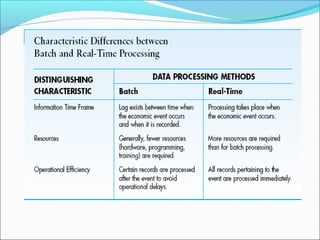
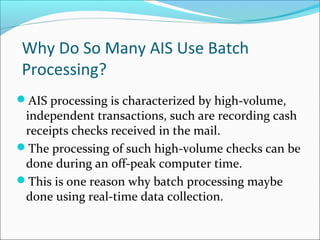
The document outlines the objectives and key concepts of transaction cycles and accounting information systems. It discusses the three transaction cycles - expenditure, conversion, and revenue - and the basic accounting records used in traditional and computer-based systems, including source documents, journals, ledgers, and documentation techniques like entity relationship diagrams and flowcharts. It also explains the differences between batch processing and real-time systems.