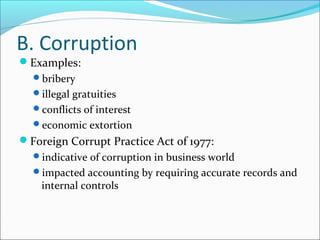
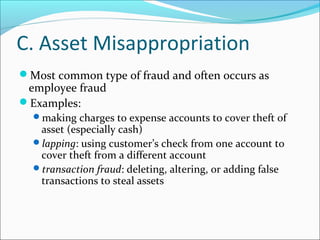
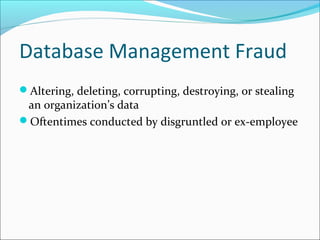
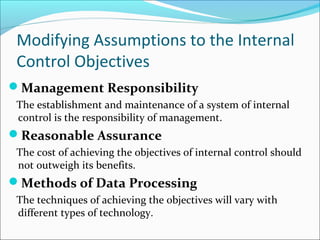
This document provides objectives and content for Chapter 3 of an accounting information systems textbook. It covers broad topics like business ethics, fraud, and internal controls. Regarding business ethics, it discusses how managers determine right conduct and achieve ethical goals. It defines fraud and common schemes, and internal controls aim to safeguard assets, ensure accurate records, promote efficiency, and ensure compliance. The Sarbanes-Oxley Act addressed auditor independence, corporate governance, and disclosure in response to scandals.



























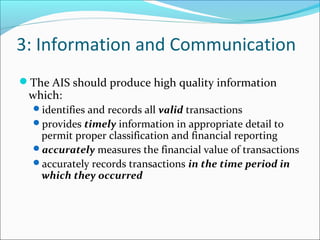
![Information and Communication
Auditors must obtain sufficient knowledge of the IS to
understand:
the classes of transactions that are material
how these transactions are initiated [input]
the associated accounting records and accounts used in
processing [input]
the transaction processing steps involved from the
initiation of a transaction to its inclusion in the financial
statements [process]
the financial reporting process used to compile financial
statements, disclosures, and estimates [output]
[red shows relationship to the general AIS model]](https://image.slidesharecdn.com/jameshallch3-150219114845-conversion-gate01/85/James-hall-ch-3-35-320.jpg)
![4: Monitoring
The process for assessing the quality of internal control
design and operation
[This is feedback in the general AIS model.]
Separate procedures—test of controls by internal auditors
Ongoing monitoring:
computer modules integrated into routine operations
management reports which highlight trends and
exceptions from normal performance
[red shows relationship to the general AIS model]](https://image.slidesharecdn.com/jameshallch3-150219114845-conversion-gate01/85/James-hall-ch-3-36-320.jpg)