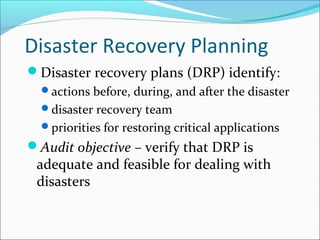
This document outlines the objectives and key topics to be covered in Chapter 15 of the textbook "Accounting Information Systems, 6th edition". It will discuss the key provisions of Sections 302 and 404 of the Sarbanes-Oxley Act, including management responsibilities for internal controls over financial reporting. It will also cover IT controls related to financial reporting, risks of incompatible functions in IT organizational structures, controls over computer facilities, and elements of an effective disaster recovery plan.