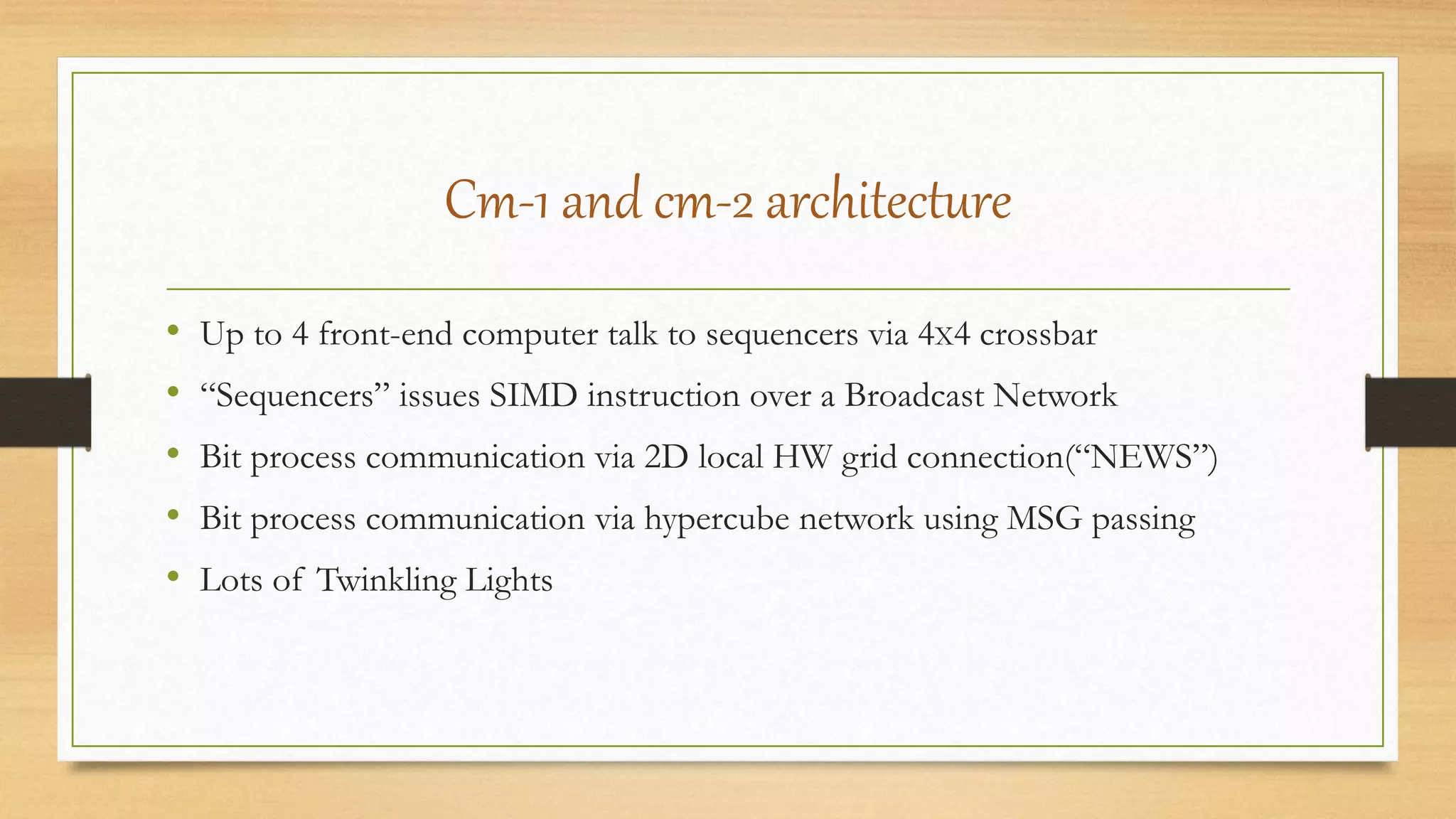
The document is a seminar presentation on Connection Machines, specifically focusing on the CM-5 architecture. It details the evolution of Connection Machines from CM-1 and CM-2 to CM-5, highlighting significant architectural changes, such as the shift to commercial off-the-shelf components and new programming capabilities. The presentation also covers various applications of the CM-5, including machine learning and computer graphics.