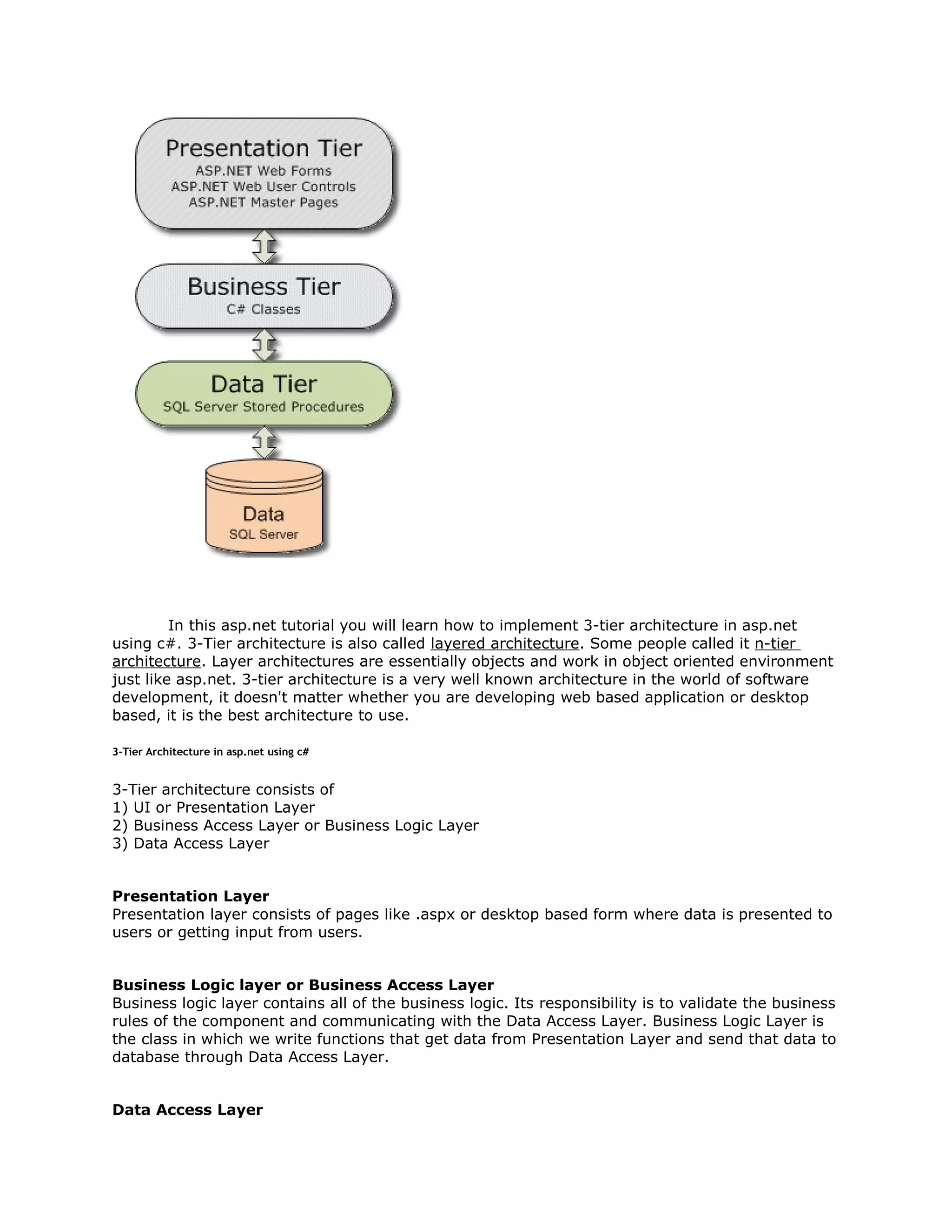
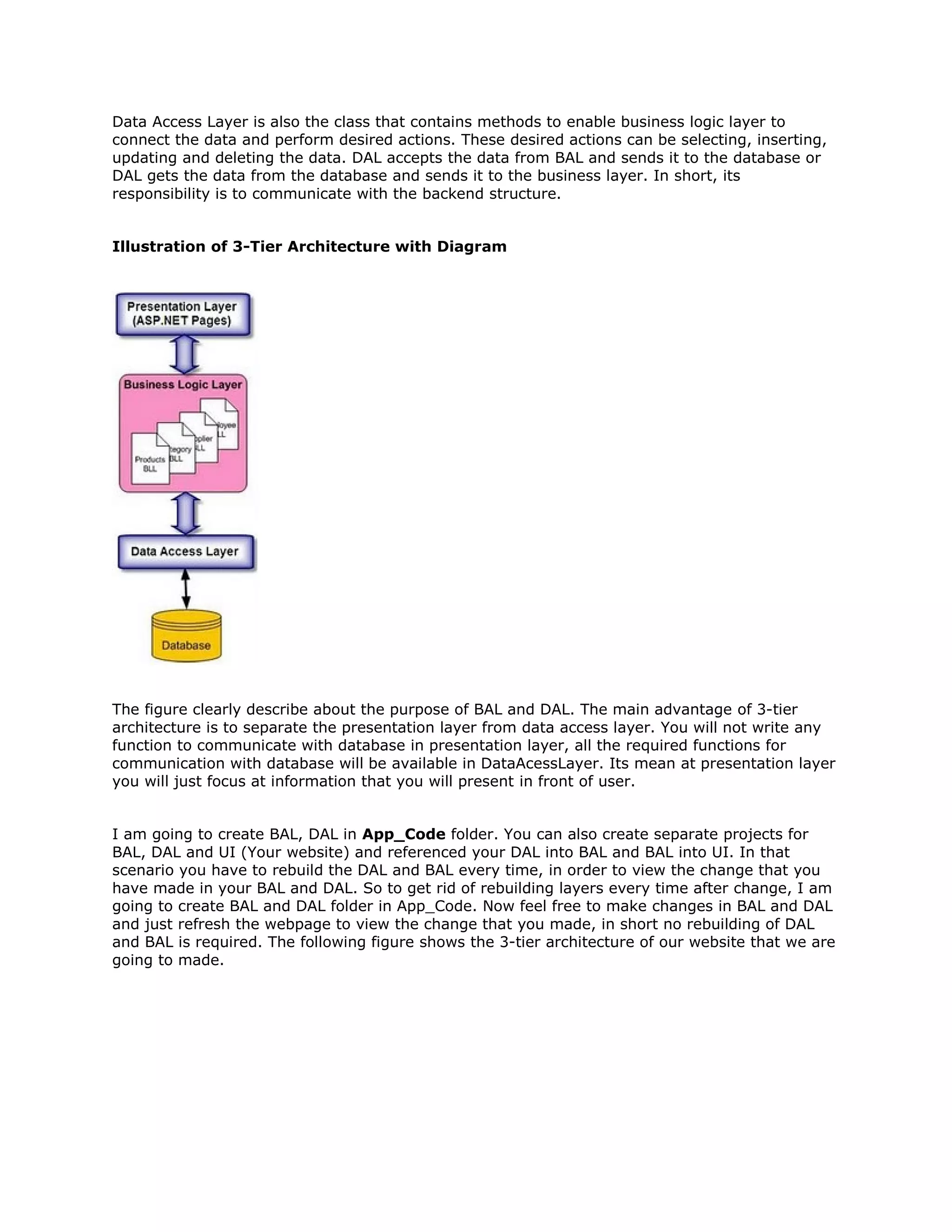
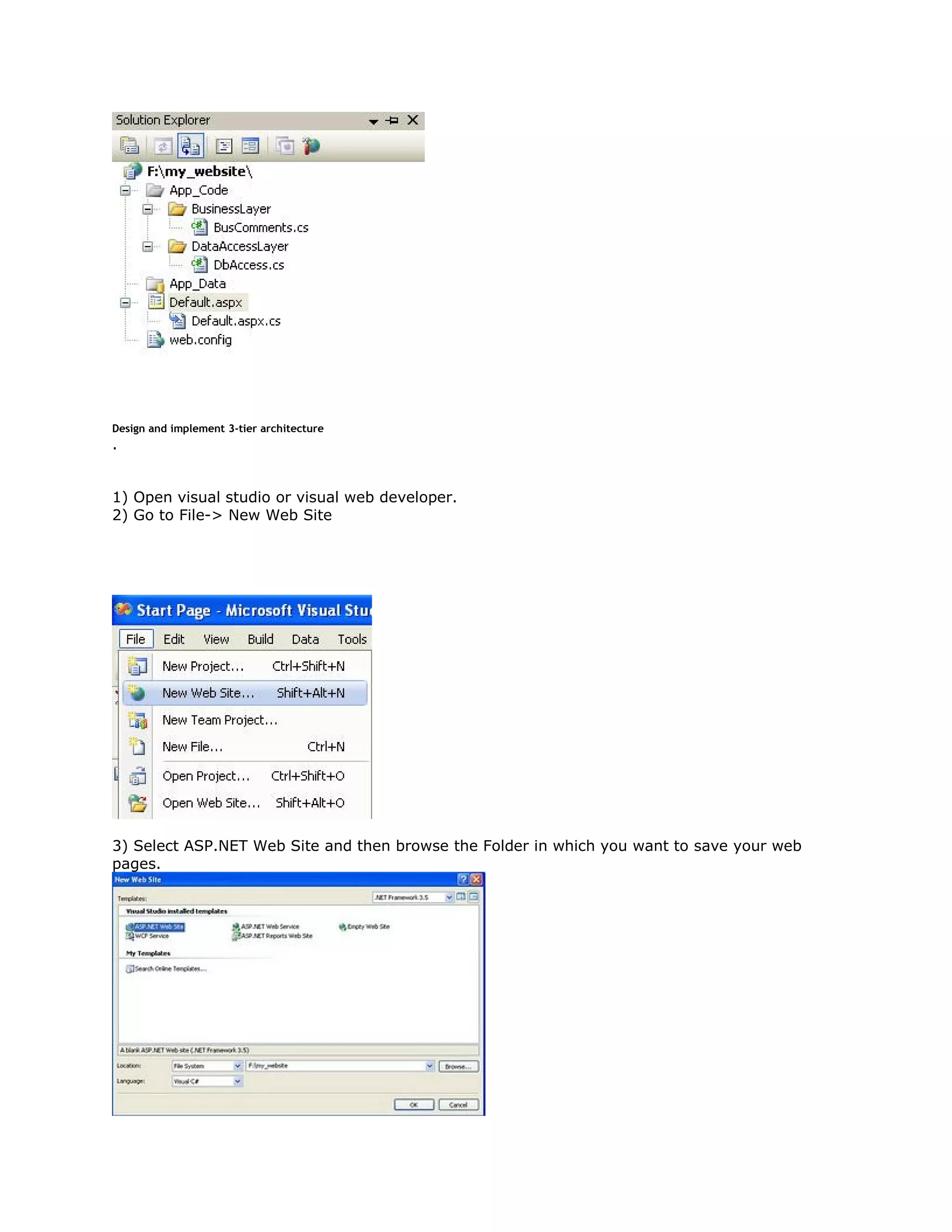
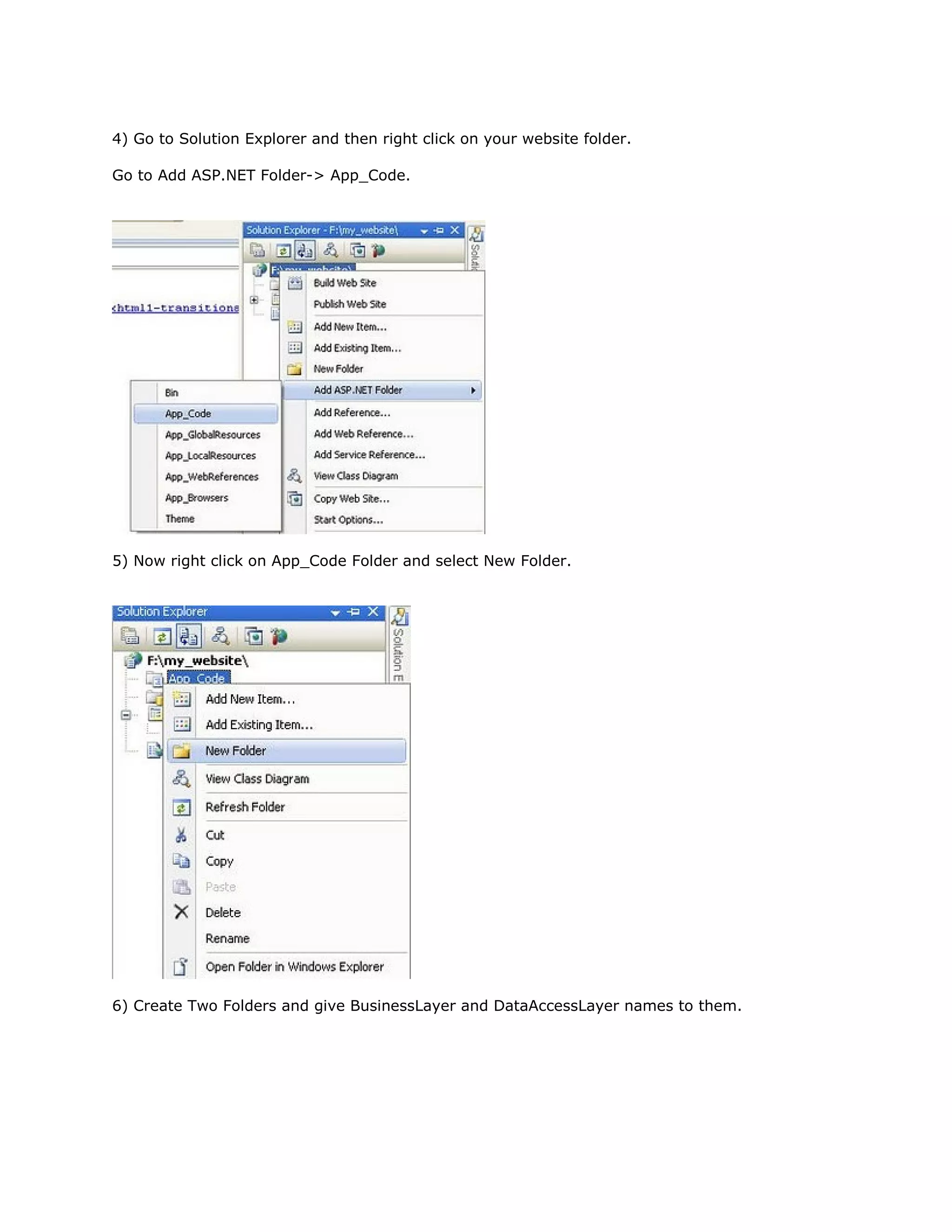
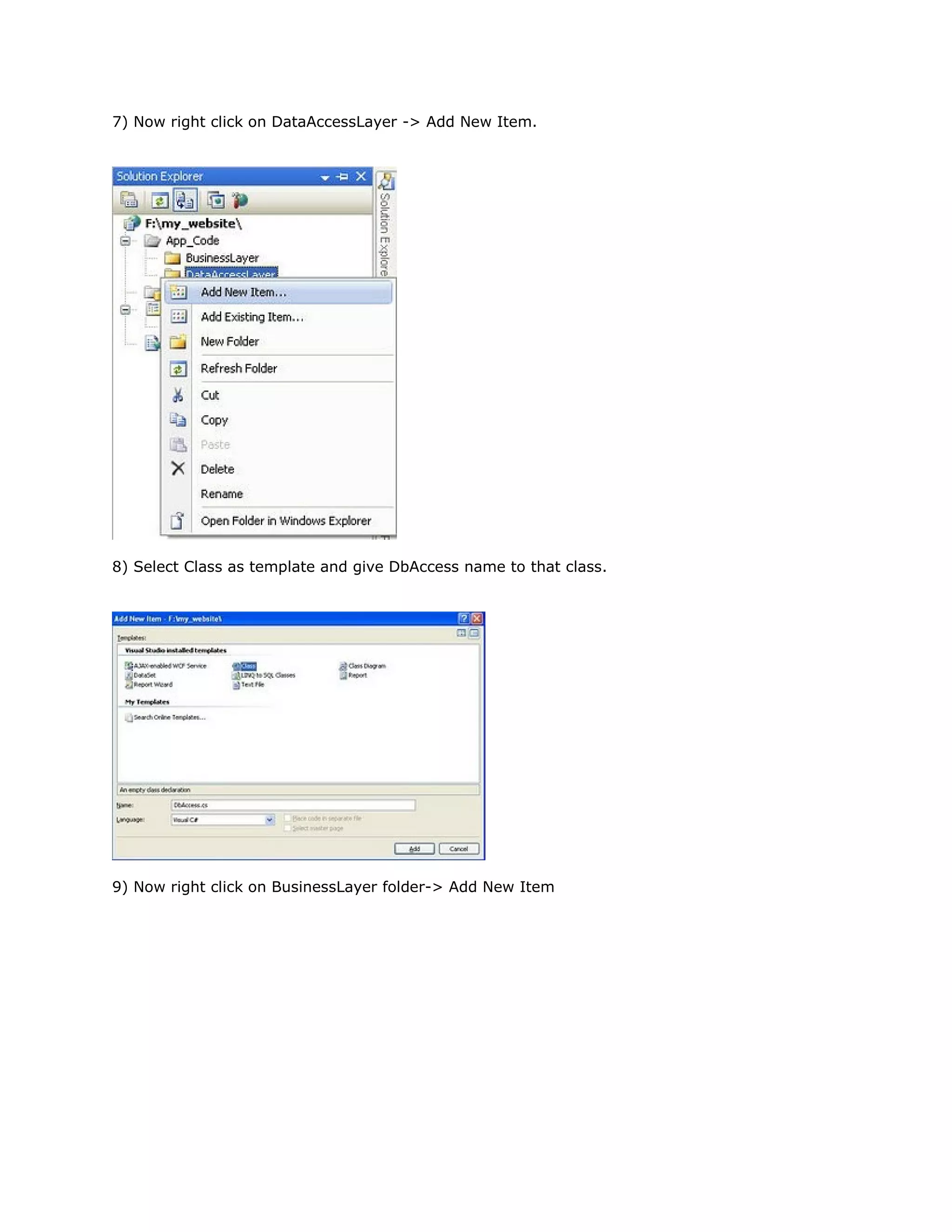
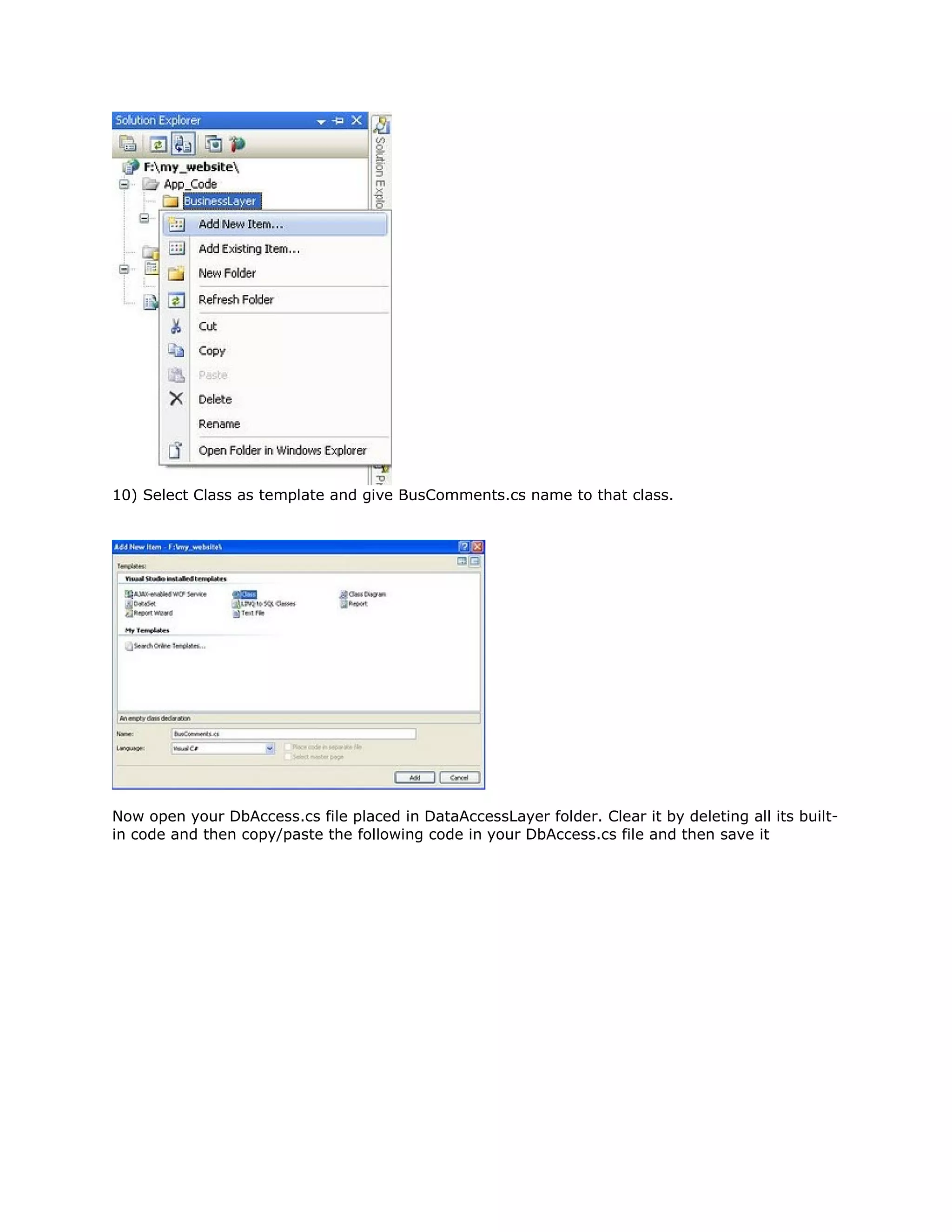
This document provides an overview of implementing a 3-tier architecture in ASP.NET using C#. It describes the 3 tiers - presentation layer, business logic layer, and data access layer. The presentation layer handles user input/output. The business logic layer contains application logic and communicates with the data access layer. The data access layer connects to the database and performs CRUD operations. The document outlines setting up the project structure with App_Code/BusinessLayer and App_Code/DataAccessLayer folders and creating sample BusinessLogic and DataAccess classes.