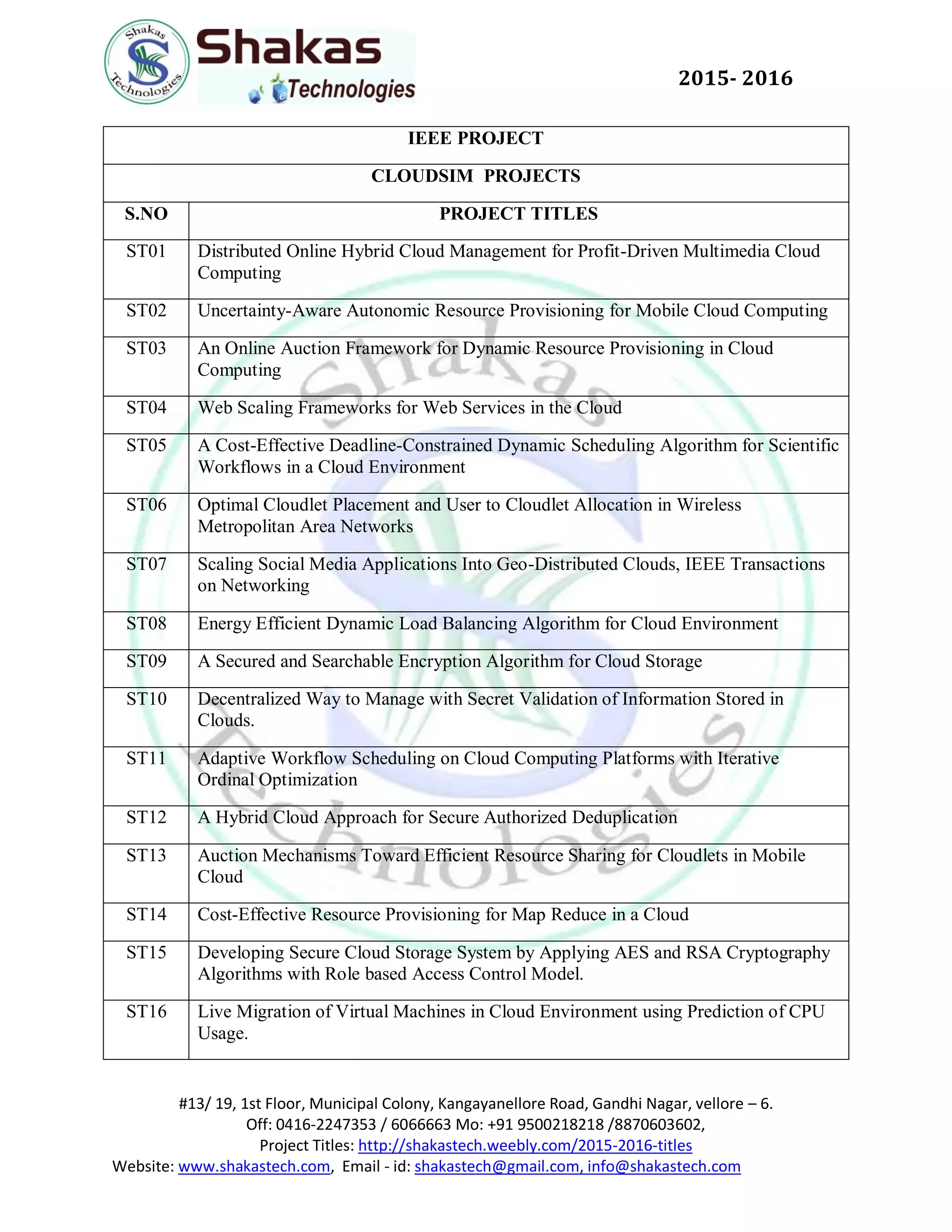
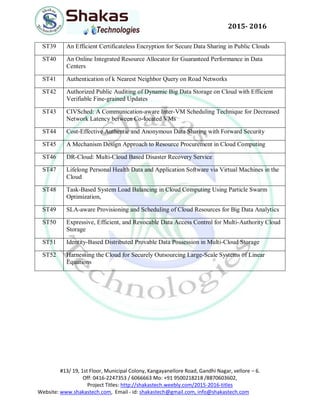
The document lists various project titles related to cloud computing for the year 2015-2016, highlighting 52 unique research topics including resource management, security, and optimization in cloud environments. Each title addresses specific challenges and developments in the field, such as dynamic scheduling, data storage solutions, and energy efficiency. Contact information and web links related to the projects are also provided.