2015 dot net list
•
1 like•88 views
DotNet, JAVA, NS2, NS3, J2EE, J2ME,MATLAB, HTML5, PHP, Angular JS, Python, Ruby and Web, Application Related Projects.
Report
Share
Report
Share
Download to read offline
Recommended
Bayesian networks for data integration in the absence of foreign keys

This document presents a framework for probabilistic data integration across multiple data sources in the absence of foreign keys. The framework uses Bayesian networks to integrate datasets and allow for probabilistic inference spanning attributes from different sources. It addresses the challenges of integrating data when the sources only share attributes like gender, age, and postal code that do not uniquely identify records. The framework automatically constructs Bayesian networks for integration and inference. It is shown to approximate the inference of a single global Bayesian network projected onto multiple local relations. The quality of inference under this framework is investigated based on properties of the local relations like the number and cardinality of shared attributes.
A unified framework for user identification across online and offline data

This document proposes a framework for user identification across both online and offline datasets. The framework consists of three steps: 1) Using clustering to map IP addresses to physical locations, 2) Developing a pairwise index to reduce space and time costs for computing co-occurrences, and 3) Applying a learning-to-rank method to merge effects of multiple features from the first two steps. The goal is to build connections between online and offline data types to identify users across different datasets. Experiments were designed to evaluate the efficiency and performance of the proposed framework.
Gap finder finding inconsistency of security information from unstructured text

GapFinder is a system for identifying semantic inconsistencies within cybersecurity domain texts. It examines technical inconsistencies that arise in functional descriptions of open source malware threat reporting information from various web-based sources. GapFinder utilizes natural language processing to transform unstructured text into structured forms that can then be analyzed to detect the presence of inconsistencies across different reports on the same malware threats. The system was evaluated using tens of thousands of relations derived from web-based malware threat reports, demonstrating its ability to successfully identify inconsistencies between different descriptions of the same threats.
Web Mining Projects Topics

MODERN CONCEPTS IN WEB MINING
FOREMOST TECHNOLOGIES IN WEB MINING
TOPMOST APPLICATIONS IN WEB MINING
Happy Together...

This short document promotes the creation of presentations using Haiku Deck on SlideShare. It features a stock photo and text that encourages the reader to get started making their own Haiku Deck presentation. A brief call to action is given to start creating presentations on the SlideShare platform.
DOCUMENTS NEEDED FOR PURCHASING APARTMENTS

This short document promotes creating presentations using Haiku Deck, a tool for making slideshows. It encourages the reader to get started making their own Haiku Deck presentation and sharing it on SlideShare. In a single sentence, it pitches the idea of using Haiku Deck to easily design presentations.
timroe_cv_linkedin

Tim Roe has over 20 years of experience as a graphic designer, working both as an employee and freelancer for various design firms. He has a diverse skill set including graphic design for print, web design, presentation design, and video tutorials. His career has included roles as a graphic designer, creative director, and freelance designer. He currently works as a freelance graphic designer providing services such as design work, project management, business development, and technical support to clients across the UK.
Recommended
Bayesian networks for data integration in the absence of foreign keys

This document presents a framework for probabilistic data integration across multiple data sources in the absence of foreign keys. The framework uses Bayesian networks to integrate datasets and allow for probabilistic inference spanning attributes from different sources. It addresses the challenges of integrating data when the sources only share attributes like gender, age, and postal code that do not uniquely identify records. The framework automatically constructs Bayesian networks for integration and inference. It is shown to approximate the inference of a single global Bayesian network projected onto multiple local relations. The quality of inference under this framework is investigated based on properties of the local relations like the number and cardinality of shared attributes.
A unified framework for user identification across online and offline data

This document proposes a framework for user identification across both online and offline datasets. The framework consists of three steps: 1) Using clustering to map IP addresses to physical locations, 2) Developing a pairwise index to reduce space and time costs for computing co-occurrences, and 3) Applying a learning-to-rank method to merge effects of multiple features from the first two steps. The goal is to build connections between online and offline data types to identify users across different datasets. Experiments were designed to evaluate the efficiency and performance of the proposed framework.
Gap finder finding inconsistency of security information from unstructured text

GapFinder is a system for identifying semantic inconsistencies within cybersecurity domain texts. It examines technical inconsistencies that arise in functional descriptions of open source malware threat reporting information from various web-based sources. GapFinder utilizes natural language processing to transform unstructured text into structured forms that can then be analyzed to detect the presence of inconsistencies across different reports on the same malware threats. The system was evaluated using tens of thousands of relations derived from web-based malware threat reports, demonstrating its ability to successfully identify inconsistencies between different descriptions of the same threats.
Web Mining Projects Topics

MODERN CONCEPTS IN WEB MINING
FOREMOST TECHNOLOGIES IN WEB MINING
TOPMOST APPLICATIONS IN WEB MINING
Happy Together...

This short document promotes the creation of presentations using Haiku Deck on SlideShare. It features a stock photo and text that encourages the reader to get started making their own Haiku Deck presentation. A brief call to action is given to start creating presentations on the SlideShare platform.
DOCUMENTS NEEDED FOR PURCHASING APARTMENTS

This short document promotes creating presentations using Haiku Deck, a tool for making slideshows. It encourages the reader to get started making their own Haiku Deck presentation and sharing it on SlideShare. In a single sentence, it pitches the idea of using Haiku Deck to easily design presentations.
timroe_cv_linkedin

Tim Roe has over 20 years of experience as a graphic designer, working both as an employee and freelancer for various design firms. He has a diverse skill set including graphic design for print, web design, presentation design, and video tutorials. His career has included roles as a graphic designer, creative director, and freelance designer. He currently works as a freelance graphic designer providing services such as design work, project management, business development, and technical support to clients across the UK.
How google works

The document discusses the benefits of exercise for mental health. Regular physical activity can help reduce anxiety and depression and improve mood and cognitive functioning. Exercise causes chemical changes in the brain that may help boost feelings of calmness and well-being.
Scientific_Project_Report_on Wireless Monitoring and Control in Industries

This document discusses the use of wireless networks for monitoring and controlling industrial processes. It proposes integrating a wireless network to remotely collect data from areas that were previously difficult to access. The design includes a circuit that can overcome common wireless issues like multipath fade and interference using mesh networking. Microcontrollers communicate wirelessly via RF modules and display data, with one microcontroller controlling the other. The document reviews past studies on wireless technology in industries and cites successful applications in areas like offshore platforms and biomass plants.
Apresentação oral

Este documento fornece dicas para elaboração de apresentações, incluindo dominar o tema, planejar o número de slides de acordo com o tempo, usar texto curto e estrutura de princípio, meio e fim, além de cuidados com animações, proporções, cores e postura do apresentador.
Divisão de acesso público

O documento lista os resultados de 8 rodadas da Divisão de Acesso, incluindo os públicos em cada partida. As rodadas tiveram públicos totais variando de aproximadamente 1,7 mil a 3,8 mil pessoas. A partida com maior público foi Pelotas x Santa Cruz com 2,1 mil pessoas.
L2EP_report

This document summarizes a student's research internship developing an algorithm for distributing electric vehicle charging commands. The aim is to find an efficient solution for scheduling EV charging at stations. The algorithm considers factors like solar and wind power availability, total energy needs, and state of charge for each EV. MATLAB code is used to simulate charging 1200 EVs over days and years, accounting for home and work charging profiles. Effects of transmission delays are also modeled by introducing time shifts to the charging schedules. Results show higher delays lead to more EVs not receiving full charges.
2.Uluslararası İtibar Yönetimi Konferansı - Dünya Turizminde Türkiye Markasın...

2.Uluslararası İtibar Yönetimi Konferansı - Dünya Turizminde Türkiye Markasın...İtibar Yönetimi Enstitüsü
L1 basics

This document provides an introduction to the Java programming language, including its history, key concepts, and characteristics. It describes how Java was created in the early 1990s at Sun Microsystems to enable programming for the internet and be platform independent. The document outlines the core object-oriented programming concepts in Java like encapsulation, inheritance, and polymorphism. It also details Java's main characteristics such as being simple, secure, portable and having good performance. The life cycle of a Java program from writing source code to compilation and execution is summarized. Finally, a simple Java program is shown as an example.
Sport Obermeyer Case Solution

Sport Obermeyer is deciding how to allocate production of women's parkas between manufacturing in Hong Kong and China. Factors that influence this decision include minimum order quantities, production costs, quality differences, workforce skills, and lead times. Based on an analysis of forecast accuracy and risk for each style, Sport Obermeyer determines how many units of each style to produce in Hong Kong versus China in their initial production run while meeting their total quantity needs.
[20151106 Web Framework MeetUp] API 표준을 제시한 Ruby on Rails![[20151106 Web Framework MeetUp] API 표준을 제시한 Ruby on Rails](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[20151106 Web Framework MeetUp] API 표준을 제시한 Ruby on Rails](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
2015년 11월 6일 Web Framework MeetUp 발표 자료.
http://onoffmix.com/event/56470
주제에 맞춰서 하느라 좀 거시적인 얘기가 됐습니다.
MIPS 32 BITS

O documento descreve a arquitetura MIPS de 32 bits, incluindo exemplos de compilação de instruções em linguagem de montagem e máquina MIPS. Ele contém 10 exemplos de compilação de diferentes estruturas de programação como atribuições, acesso a memória, laços e condicionais compilados em instruções MIPS. Além disso, fornece tabelas com os códigos binários dos registradores, instruções e outros detalhes da arquitetura MIPS.
Arte y tecnología

El documento discute las relaciones entre el arte y la tecnología a lo largo de la historia y en la actualidad, donde dicha relación se presenta de manera tangible en grandes manifestaciones. También analiza el debate sobre las posibilidades del arte con nuevas tecnologías y el concepto de una "cultura libre", así como la disputa entre la industria musical tradicional y el mercado discográfico que lucha por su subsistencia ante la opción de distribución gratuita en Internet.
Tablet, laptop, bocinas, teclados

Este documento lista cuatro artículos electrónicos: una tableta, una laptop, bocinas y un teclado.
2015 cloud sim projects

DotNet, JAVA, NS2, NS3, J2EE, J2ME,MATLAB, HTML5, PHP, Angular JS, Python, Ruby and Web, Application Related Projects.
Latest php projects

DotNet, JAVA, NS2, NS3, J2EE, J2ME,MATLAB, HTML5, PHP, Angular JS, Python, Ruby and Web, Application Related Projects.
Cloud computing

Shakas Technologies Provides, 2016-2017 Project titles, Real time project titles, IEEE Project Titles 2016-2017, NON-IEEE Project Titles, Latest project titles 2016, MCA Project titles, Final Year Project titles 2016-2017..
Contact As:
Shakas Technologies
#13/19, 1st Floor, Municipal Colony,
Kangeyanellore Road, Gandhi Nagar,
Vellore-632006,
Cell: 9500218218
Mobile: 0416-2247353 / 6066663
2015 big data project

DotNet, JAVA, NS2, NS3, J2EE, J2ME,MATLAB, HTML5, PHP, Angular JS, Python, Ruby and Web, Application Related Projects.
Project titles 2016-2017

Shakas Technologies Provides, 2016-2017 Project titles, Real time project titles, IEEE Project Titles 2016-2017, NON-IEEE Project Titles, Latest project titles 2016, MCA Project titles, Final Year Project titles 2016-2017..
Contact As:
Shakas Technologies
#13/19, 1st Floor, Municipal Colony,
Kangeyanellore Road, Gandhi Nagar,
Vellore-632006,
Cell: 9500218218
Mobile: 0416-2247353 / 6066663
Latest ieee2014 2015-2016 dotnet java projects list

This document provides a list of over 100 potential dotnet and Java project topics for students in various technical fields like computer engineering, information technology, and computer science. The projects are grouped into categories like secure computing, cloud computing, data mining, image processing, networking, and more. Each project provides a brief title and can be obtained by contacting the listed phone number for the base paper and abstract.
Shakastech thesis titles 2016

This document provides contact information for Shakastech, including their address, phone numbers, website, and email addresses. It then lists over 100 potential M.Phil thesis titles related to real-time network and wireless communication topics such as web caching, wireless sensor networks, TCP performance, network security, and more. The titles cover a wide range of current and emerging networking technologies.
K nearest neighbor classification over semantically secure encrypted

Data Mining has wide applications in many areas such as banking, medicine, scientific research and among government agencies. Classification is one of the commonly used tasks in data mining applications.
Shakas 2016 titles

This document contains a list of 98 project titles related to various topics including cloud computing, data mining, image processing, networking, parallel and distributed computing, wireless sensor networking, mobile computing, and dependable and secure computing. It also provides contact information for Shakastech, the organization offering these projects, including their address, phone number, website, and emails.
More Related Content
Viewers also liked
How google works

The document discusses the benefits of exercise for mental health. Regular physical activity can help reduce anxiety and depression and improve mood and cognitive functioning. Exercise causes chemical changes in the brain that may help boost feelings of calmness and well-being.
Scientific_Project_Report_on Wireless Monitoring and Control in Industries

This document discusses the use of wireless networks for monitoring and controlling industrial processes. It proposes integrating a wireless network to remotely collect data from areas that were previously difficult to access. The design includes a circuit that can overcome common wireless issues like multipath fade and interference using mesh networking. Microcontrollers communicate wirelessly via RF modules and display data, with one microcontroller controlling the other. The document reviews past studies on wireless technology in industries and cites successful applications in areas like offshore platforms and biomass plants.
Apresentação oral

Este documento fornece dicas para elaboração de apresentações, incluindo dominar o tema, planejar o número de slides de acordo com o tempo, usar texto curto e estrutura de princípio, meio e fim, além de cuidados com animações, proporções, cores e postura do apresentador.
Divisão de acesso público

O documento lista os resultados de 8 rodadas da Divisão de Acesso, incluindo os públicos em cada partida. As rodadas tiveram públicos totais variando de aproximadamente 1,7 mil a 3,8 mil pessoas. A partida com maior público foi Pelotas x Santa Cruz com 2,1 mil pessoas.
L2EP_report

This document summarizes a student's research internship developing an algorithm for distributing electric vehicle charging commands. The aim is to find an efficient solution for scheduling EV charging at stations. The algorithm considers factors like solar and wind power availability, total energy needs, and state of charge for each EV. MATLAB code is used to simulate charging 1200 EVs over days and years, accounting for home and work charging profiles. Effects of transmission delays are also modeled by introducing time shifts to the charging schedules. Results show higher delays lead to more EVs not receiving full charges.
2.Uluslararası İtibar Yönetimi Konferansı - Dünya Turizminde Türkiye Markasın...

2.Uluslararası İtibar Yönetimi Konferansı - Dünya Turizminde Türkiye Markasın...İtibar Yönetimi Enstitüsü
L1 basics

This document provides an introduction to the Java programming language, including its history, key concepts, and characteristics. It describes how Java was created in the early 1990s at Sun Microsystems to enable programming for the internet and be platform independent. The document outlines the core object-oriented programming concepts in Java like encapsulation, inheritance, and polymorphism. It also details Java's main characteristics such as being simple, secure, portable and having good performance. The life cycle of a Java program from writing source code to compilation and execution is summarized. Finally, a simple Java program is shown as an example.
Sport Obermeyer Case Solution

Sport Obermeyer is deciding how to allocate production of women's parkas between manufacturing in Hong Kong and China. Factors that influence this decision include minimum order quantities, production costs, quality differences, workforce skills, and lead times. Based on an analysis of forecast accuracy and risk for each style, Sport Obermeyer determines how many units of each style to produce in Hong Kong versus China in their initial production run while meeting their total quantity needs.
[20151106 Web Framework MeetUp] API 표준을 제시한 Ruby on Rails![[20151106 Web Framework MeetUp] API 표준을 제시한 Ruby on Rails](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[20151106 Web Framework MeetUp] API 표준을 제시한 Ruby on Rails](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
2015년 11월 6일 Web Framework MeetUp 발표 자료.
http://onoffmix.com/event/56470
주제에 맞춰서 하느라 좀 거시적인 얘기가 됐습니다.
MIPS 32 BITS

O documento descreve a arquitetura MIPS de 32 bits, incluindo exemplos de compilação de instruções em linguagem de montagem e máquina MIPS. Ele contém 10 exemplos de compilação de diferentes estruturas de programação como atribuições, acesso a memória, laços e condicionais compilados em instruções MIPS. Além disso, fornece tabelas com os códigos binários dos registradores, instruções e outros detalhes da arquitetura MIPS.
Arte y tecnología

El documento discute las relaciones entre el arte y la tecnología a lo largo de la historia y en la actualidad, donde dicha relación se presenta de manera tangible en grandes manifestaciones. También analiza el debate sobre las posibilidades del arte con nuevas tecnologías y el concepto de una "cultura libre", así como la disputa entre la industria musical tradicional y el mercado discográfico que lucha por su subsistencia ante la opción de distribución gratuita en Internet.
Tablet, laptop, bocinas, teclados

Este documento lista cuatro artículos electrónicos: una tableta, una laptop, bocinas y un teclado.
Viewers also liked (13)
Scientific_Project_Report_on Wireless Monitoring and Control in Industries

Scientific_Project_Report_on Wireless Monitoring and Control in Industries
2.Uluslararası İtibar Yönetimi Konferansı - Dünya Turizminde Türkiye Markasın...

2.Uluslararası İtibar Yönetimi Konferansı - Dünya Turizminde Türkiye Markasın...
[20151106 Web Framework MeetUp] API 표준을 제시한 Ruby on Rails![[20151106 Web Framework MeetUp] API 표준을 제시한 Ruby on Rails](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[20151106 Web Framework MeetUp] API 표준을 제시한 Ruby on Rails](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[20151106 Web Framework MeetUp] API 표준을 제시한 Ruby on Rails
Similar to 2015 dot net list
2015 cloud sim projects

DotNet, JAVA, NS2, NS3, J2EE, J2ME,MATLAB, HTML5, PHP, Angular JS, Python, Ruby and Web, Application Related Projects.
Latest php projects

DotNet, JAVA, NS2, NS3, J2EE, J2ME,MATLAB, HTML5, PHP, Angular JS, Python, Ruby and Web, Application Related Projects.
Cloud computing

Shakas Technologies Provides, 2016-2017 Project titles, Real time project titles, IEEE Project Titles 2016-2017, NON-IEEE Project Titles, Latest project titles 2016, MCA Project titles, Final Year Project titles 2016-2017..
Contact As:
Shakas Technologies
#13/19, 1st Floor, Municipal Colony,
Kangeyanellore Road, Gandhi Nagar,
Vellore-632006,
Cell: 9500218218
Mobile: 0416-2247353 / 6066663
2015 big data project

DotNet, JAVA, NS2, NS3, J2EE, J2ME,MATLAB, HTML5, PHP, Angular JS, Python, Ruby and Web, Application Related Projects.
Project titles 2016-2017

Shakas Technologies Provides, 2016-2017 Project titles, Real time project titles, IEEE Project Titles 2016-2017, NON-IEEE Project Titles, Latest project titles 2016, MCA Project titles, Final Year Project titles 2016-2017..
Contact As:
Shakas Technologies
#13/19, 1st Floor, Municipal Colony,
Kangeyanellore Road, Gandhi Nagar,
Vellore-632006,
Cell: 9500218218
Mobile: 0416-2247353 / 6066663
Latest ieee2014 2015-2016 dotnet java projects list

This document provides a list of over 100 potential dotnet and Java project topics for students in various technical fields like computer engineering, information technology, and computer science. The projects are grouped into categories like secure computing, cloud computing, data mining, image processing, networking, and more. Each project provides a brief title and can be obtained by contacting the listed phone number for the base paper and abstract.
Shakastech thesis titles 2016

This document provides contact information for Shakastech, including their address, phone numbers, website, and email addresses. It then lists over 100 potential M.Phil thesis titles related to real-time network and wireless communication topics such as web caching, wireless sensor networks, TCP performance, network security, and more. The titles cover a wide range of current and emerging networking technologies.
K nearest neighbor classification over semantically secure encrypted

Data Mining has wide applications in many areas such as banking, medicine, scientific research and among government agencies. Classification is one of the commonly used tasks in data mining applications.
Shakas 2016 titles

This document contains a list of 98 project titles related to various topics including cloud computing, data mining, image processing, networking, parallel and distributed computing, wireless sensor networking, mobile computing, and dependable and secure computing. It also provides contact information for Shakastech, the organization offering these projects, including their address, phone number, website, and emails.
Ieee 2014 2014 java project titles

The document lists potential 2014-2015 Java project titles from the IEEE across several domains: Big Data, Cloud Computing, Data Mining, Secure Computing, Networking, Parallel & Distributed Systems, Mobile Computing, and Cloudsim. The projects focus on topics like big data analysis, cloud security and scalability, data mining techniques, privacy and anonymity in networks and databases, mobile and distributed systems, and simulating cloud infrastructure.
IEEE JAVA 2013 Titles

This document provides contact information for the head office and two branch offices of iGenuine Soft Solutions Pvt Ltd in Chennai and Coimbatore, India. It also lists 20 Java conference papers from 2013 related to topics including cloud computing, data mining, image processing, and mobile computing. Finally, it presents a table with the title and publication details of 200 papers from 2013 on various computer science topics.
Dotnet titles

Shakas Technologies Provides, 2016-2017 Project titles, Real time project titles, IEEE Project Titles 2016-2017, NON-IEEE Project Titles, Latest project titles 2016, MCA Project titles, Final Year Project titles 2016-2017..
Contact As:
Shakas Technologies
#13/19, 1st Floor, Municipal Colony,
Kangeyanellore Road, Gandhi Nagar,
Vellore-632006,
Cell: 9500218218
Mobile: 0416-2247353 / 6066663
M.Tech NS2 List 

This document lists 16 projects related to mobile computing, communications networks, intelligent transportation systems, and other domains. The projects focus on topics like detection of distributed denial of service attacks, geographic routing in mobile ad hoc networks, anonymous and efficient routing protocols, node autoconfiguration in ad hoc networks, adaptive routing in communication networks, routing in vehicular ad hoc networks, cache consistency in wireless networks, neighbor discovery in wireless networks, cooperative caching in social wireless networks, intrusion detection in mobile ad hoc networks, neighbor discovery algorithms, defense against denial of service attacks, opportunistic mobile ad hoc networks, multicast capacity and delay tradeoffs, cooperative transmission in wireless networks, target tracking with mobile sensors, and source anonymity in sensor networks. Contact
2020 and 2021 Data Mining Projects

2020 IEEE Transaction on Knowledge and Data Engineering
For More Details::Contact::K.Manjunath - 09535866270
http://www.tmksinfotech.com and http://www.bemtechprojects.com
2020 and 2021 IEEE Projects@ TMKS Infotech,Bangalore
2020 and 2021 java Cloud computing

2019 IEEE Transaction on Knowledge and Data Engineering
For More Details::Contact::K.Manjunath - 09535866270
http://www.tmksinfotech.com and http://www.bemtechprojects.com
2019 and 2020 IEEE Projects@ TMKS Infotech,Bangalore
2020 and 2021 Cloud Computing Projects

2020 IEEE Transaction on Knowledge and Data Engineering
For More Details::Contact::K.Manjunath - 09535866270
http://www.tmksinfotech.com and http://www.bemtechprojects.com
2020 and 2021 IEEE Projects@ TMKS Infotech,Bangalore
Java titles

Shakas Technologies Provides, 2016-2017 Project titles, Real time project titles, IEEE Project Titles 2016-2017, NON-IEEE Project Titles, Latest project titles 2016, MCA Project titles, Final Year Project titles 2016-2017..
Contact As:
Shakas Technologies
#13/19, 1st Floor, Municipal Colony,
Kangeyanellore Road, Gandhi Nagar,
Vellore-632006,
Cell: 9500218218
Mobile: 0416-2247353 / 6066663
2013-2014 IEEE Projects & Application Projects

B.E, B.TECH, M.TECH, M.E, MS, BSC, MSC, BCA, MCA, MBA, BBA, PHD, B.E (ECE, CSE, IT) B.TECH (ECE, CSE, IT) M.TECH (COMPUTER SCIENCE, SOFTWARE ENGINEERING, M.E (COMMUNICATION SYSTEMS, COMPUTER SCIENCE, SOFTWARE ENGINEERING) DIPLOMA (CSE, IT)
Enabling fine grained multi-keyword search supporting classified sub-dictiona...

Using cloud computing, individuals can store their data on remote servers and allow data access to public users through the cloud servers. As the outsourced data are likely to contain sensitive privacy information, they are typically encrypted before uploaded to the cloud.
Enabling fine grained multi-keyword search supporting classified sub-dictiona...

Using cloud computing, individuals can store their data on remote servers and allow data access to public users through the cloud servers. As the outsourced data are likely to contain sensitive privacy information, they are typically encrypted before uploaded to the cloud.
Similar to 2015 dot net list (20)
Latest ieee2014 2015-2016 dotnet java projects list

Latest ieee2014 2015-2016 dotnet java projects list
K nearest neighbor classification over semantically secure encrypted

K nearest neighbor classification over semantically secure encrypted
Enabling fine grained multi-keyword search supporting classified sub-dictiona...

Enabling fine grained multi-keyword search supporting classified sub-dictiona...
Enabling fine grained multi-keyword search supporting classified sub-dictiona...

Enabling fine grained multi-keyword search supporting classified sub-dictiona...
More from Hari Krishnan
latest IEEE NetworkingProjects titles

DotNet, JAVA, NS2, NS3, J2EE, J2ME,MATLAB, HTML5, PHP, Angular JS, Python, Ruby and Web, Application Related Projects.
latest Ieee projects ns2

DotNet, JAVA, NS2, NS3, J2EE, J2ME,MATLAB, HTML5, PHP, Angular JS, Python, Ruby and Web, Application Related Projects.
Latest IEEE 2015 2016 Project Titles 

DotNet, JAVA, NS2, NS3, J2EE, J2ME,MATLAB, HTML5, PHP, Angular JS, Python, Ruby and Web, Application Related Projects.
Ieee projects ns2

DotNet, JAVA, NS2, NS3, J2EE, J2ME,MATLAB, HTML5, PHP, Angular JS, Python, Ruby and Web, Application Related Projects.
Ieee projects list java 2015

DotNet, JAVA, NS2, NS3, J2EE, J2ME,MATLAB, HTML5, PHP, Angular JS, Python, Ruby and Web, Application Related Projects.
latest IEEE 2015 wireless security

DotNet, JAVA, NS2, NS3, J2EE, J2ME,MATLAB, HTML5, PHP, Angular JS, Python, Ruby and Web, Application Related Projects.
Latest IEEE 2015 vehicular ad hoc networks

DotNet, JAVA, NS2, NS3, J2EE, J2ME,MATLAB, HTML5, PHP, Angular JS, Python, Ruby and Web, Application Related Projects.
Latest Ieee 2015 multimedia projects

DotNet, JAVA, NS2, NS3, J2EE, J2ME,MATLAB, HTML5, PHP, Angular JS, Python, Ruby and Web, Application Related Projects.
2015 mobile wireless networks

DotNet, JAVA, NS2, NS3, J2EE, J2ME,MATLAB, HTML5, PHP, Angular JS, Python, Ruby and Web, Application Related Projects.
2015 application projects

This document lists 156 project titles completed between 2015-2016 related to dot net and web application projects. The projects cover a wide range of topics including cloud computing, cyber security, healthcare, networking, image processing, gaming, and more.
2015 android project

DotNet, JAVA, NS2, NS3, J2EE, J2ME,MATLAB, HTML5, PHP, Angular JS, Python, Ruby and Web, Application Related Projects.
About us

Shakas is a consulting, technology, and outsourcing firm based in Vellore, India with over 60 employees and $1 million in annual revenue. It provides strategic consulting, operational leadership, and customized solutions to help enterprises transform and adapt to changing conditions. Founded in 2013 by 4 graduates with $1,000, Shakas has grown rapidly by focusing on bringing clients' ideas to life and maintaining strong client relationships, with 99% of revenue from existing clients.
Shakas Technologies in vellore

B.E, B.TECH, M.TECH, M.E, MS, BSC, MSC, BCA, MCA, MBA, BBA, PHD, B.E (ECE, CSE, IT) B.TECH (ECE, CSE, IT) M.TECH (COMPUTER SCIENCE, SOFTWARE ENGINEERING, M.E (COMMUNICATION SYSTEMS, COMPUTER SCIENCE, SOFTWARE ENGINEERING) DIPLOMA (CSE, IT)
IEEE Projects 2012

The document provides a list of 82 titles and keywords related to various topics in information technology including cloud computing, parallel and distributed systems, mobile computing, data mining, image processing and MATLAB, and network security. The titles involve research on efficient data processing in clouds, privacy-preserving search, data integrity proofs, load balancing, intrusion detection, and more. The keywords indicate that the research involves programming languages including Java, .NET, and NS2.
IEEE Projects Low Cost 

The document lists various IEEE projects from 2012 in the areas of cloud computing, networking, wireless networking, and image processing. The cloud computing projects focused on securely outsourcing linear equations, remote data integrity checking, and network throughput optimization. The networking projects addressed topics like collective multicast, failure localization, and streaming media distribution. Wireless networking and image processing projects also explored related technical challenges.
More from Hari Krishnan (15)
Recently uploaded
How to Manage Your Lost Opportunities in Odoo 17 CRM

Odoo 17 CRM allows us to track why we lose sales opportunities with "Lost Reasons." This helps analyze our sales process and identify areas for improvement. Here's how to configure lost reasons in Odoo 17 CRM
Your Skill Boost Masterclass: Strategies for Effective Upskilling

Your Skill Boost Masterclass: Strategies for Effective UpskillingExcellence Foundation for South Sudan
Strategies for Effective Upskilling is a presentation by Chinwendu Peace in a Your Skill Boost Masterclass organisation by the Excellence Foundation for South Sudan on 08th and 09th June 2024 from 1 PM to 3 PM on each day.বাংলাদেশ অর্থনৈতিক সমীক্ষা (Economic Review) ২০২৪ UJS App.pdf

বাংলাদেশের অর্থনৈতিক সমীক্ষা ২০২৪ [Bangladesh Economic Review 2024 Bangla.pdf] কম্পিউটার , ট্যাব ও স্মার্ট ফোন ভার্সন সহ সম্পূর্ণ বাংলা ই-বুক বা pdf বই " সুচিপত্র ...বুকমার্ক মেনু 🔖 ও হাইপার লিংক মেনু 📝👆 যুক্ত ..
আমাদের সবার জন্য খুব খুব গুরুত্বপূর্ণ একটি বই ..বিসিএস, ব্যাংক, ইউনিভার্সিটি ভর্তি ও যে কোন প্রতিযোগিতা মূলক পরীক্ষার জন্য এর খুব ইম্পরট্যান্ট একটি বিষয় ...তাছাড়া বাংলাদেশের সাম্প্রতিক যে কোন ডাটা বা তথ্য এই বইতে পাবেন ...
তাই একজন নাগরিক হিসাবে এই তথ্য গুলো আপনার জানা প্রয়োজন ...।
বিসিএস ও ব্যাংক এর লিখিত পরীক্ষা ...+এছাড়া মাধ্যমিক ও উচ্চমাধ্যমিকের স্টুডেন্টদের জন্য অনেক কাজে আসবে ...
BÀI TẬP BỔ TRỢ TIẾNG ANH 8 CẢ NĂM - GLOBAL SUCCESS - NĂM HỌC 2023-2024 (CÓ FI...

BÀI TẬP BỔ TRỢ TIẾNG ANH 8 CẢ NĂM - GLOBAL SUCCESS - NĂM HỌC 2023-2024 (CÓ FI...Nguyen Thanh Tu Collection
https://app.box.com/s/y977uz6bpd3af4qsebv7r9b7s21935vdMain Java[All of the Base Concepts}.docx

This is part 1 of my Java Learning Journey. This Contains Custom methods, classes, constructors, packages, multithreading , try- catch block, finally block and more.
The Diamonds of 2023-2024 in the IGRA collection

A review of the growth of the Israel Genealogy Research Association Database Collection for the last 12 months. Our collection is now passed the 3 million mark and still growing. See which archives have contributed the most. See the different types of records we have, and which years have had records added. You can also see what we have for the future.
The simplified electron and muon model, Oscillating Spacetime: The Foundation...

Discover the Simplified Electron and Muon Model: A New Wave-Based Approach to Understanding Particles delves into a groundbreaking theory that presents electrons and muons as rotating soliton waves within oscillating spacetime. Geared towards students, researchers, and science buffs, this book breaks down complex ideas into simple explanations. It covers topics such as electron waves, temporal dynamics, and the implications of this model on particle physics. With clear illustrations and easy-to-follow explanations, readers will gain a new outlook on the universe's fundamental nature.
Assessment and Planning in Educational technology.pptx

In an education system, it is understood that assessment is only for the students, but on the other hand, the Assessment of teachers is also an important aspect of the education system that ensures teachers are providing high-quality instruction to students. The assessment process can be used to provide feedback and support for professional development, to inform decisions about teacher retention or promotion, or to evaluate teacher effectiveness for accountability purposes.
Digital Artifact 1 - 10VCD Environments Unit

Digital Artifact 1 - 10VCD Environments Unit - NGV Pavilion Concept Design
Hindi varnamala | hindi alphabet PPT.pdf

हिंदी वर्णमाला पीपीटी, hindi alphabet PPT presentation, hindi varnamala PPT, Hindi Varnamala pdf, हिंदी स्वर, हिंदी व्यंजन, sikhiye hindi varnmala, dr. mulla adam ali, hindi language and literature, hindi alphabet with drawing, hindi alphabet pdf, hindi varnamala for childrens, hindi language, hindi varnamala practice for kids, https://www.drmullaadamali.com
DRUGS AND ITS classification slide share

Any substance (other than food) that is used to prevent, diagnose, treat, or relieve symptoms of a
disease or abnormal condition
Azure Interview Questions and Answers PDF By ScholarHat

Azure Interview Questions and Answers PDF By ScholarHat
Recently uploaded (20)
How to Manage Your Lost Opportunities in Odoo 17 CRM

How to Manage Your Lost Opportunities in Odoo 17 CRM
Your Skill Boost Masterclass: Strategies for Effective Upskilling

Your Skill Boost Masterclass: Strategies for Effective Upskilling
বাংলাদেশ অর্থনৈতিক সমীক্ষা (Economic Review) ২০২৪ UJS App.pdf

বাংলাদেশ অর্থনৈতিক সমীক্ষা (Economic Review) ২০২৪ UJS App.pdf
BÀI TẬP BỔ TRỢ TIẾNG ANH 8 CẢ NĂM - GLOBAL SUCCESS - NĂM HỌC 2023-2024 (CÓ FI...

BÀI TẬP BỔ TRỢ TIẾNG ANH 8 CẢ NĂM - GLOBAL SUCCESS - NĂM HỌC 2023-2024 (CÓ FI...
The simplified electron and muon model, Oscillating Spacetime: The Foundation...

The simplified electron and muon model, Oscillating Spacetime: The Foundation...
Assessment and Planning in Educational technology.pptx

Assessment and Planning in Educational technology.pptx
Film vocab for eal 3 students: Australia the movie

Film vocab for eal 3 students: Australia the movie
Digital Artefact 1 - Tiny Home Environmental Design

Digital Artefact 1 - Tiny Home Environmental Design
Azure Interview Questions and Answers PDF By ScholarHat

Azure Interview Questions and Answers PDF By ScholarHat
2015 dot net list
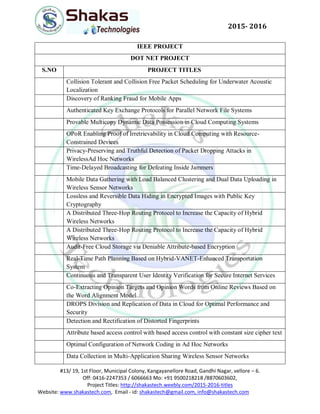
- 1. #13/ 19, 1st Floor, Municipal Colony, Kangayanellore Road, Gandhi Nagar, vellore – 6. Off: 0416-2247353 / 6066663 Mo: +91 9500218218 /8870603602, Project Titles: http://shakastech.weebly.com/2015-2016-titles Website: www.shakastech.com, Email - id: shakastech@gmail.com, info@shakastech.com 2015- 2016 IEEE PROJECT DOT NET PROJECT S.NO PROJECT TITLES Collision Tolerant and Collision Free Packet Scheduling for Underwater Acoustic Localization Discovery of Ranking Fraud for Mobile Apps Authenticated Key Exchange Protocols for Parallel Network File Systems Provable Multicopy Dynamic Data Possession in Cloud Computing Systems OPoR Enabling Proof of Irretrievability in Cloud Computing with Resource- Constrained Devices Privacy-Preserving and Truthful Detection of Packet Dropping Attacks in WirelessAd Hoc Networks Time-Delayed Broadcasting for Defeating Inside Jammers Mobile Data Gathering with Load Balanced Clustering and Dual Data Uploading in Wireless Sensor Networks Lossless and Reversible Data Hiding in Encrypted Images with Public Key Cryptography A Distributed Three-Hop Routing Protocol to Increase the Capacity of Hybrid Wireless Networks A Distributed Three-Hop Routing Protocol to Increase the Capacity of Hybrid Wireless Networks Audit-Free Cloud Storage via Deniable Attribute-based Encryption Real-Time Path Planning Based on Hybrid-VANET-Enhanced Transportation System Continuous and Transparent User Identity Verification for Secure Internet Services Co-Extracting Opinion Targets and Opinion Words from Online Reviews Based on the Word Alignment Model DROPS Division and Replication of Data in Cloud for Optimal Performance and Security Detection and Rectification of Distorted Fingerprints Attribute based access control with based access control with constant size cipher text Optimal Configuration of Network Coding in Ad Hoc Networks Data Collection in Multi-Application Sharing Wireless Sensor Networks
- 2. #13/ 19, 1st Floor, Municipal Colony, Kangayanellore Road, Gandhi Nagar, vellore – 6. Off: 0416-2247353 / 6066663 Mo: +91 9500218218 /8870603602, Project Titles: http://shakastech.weebly.com/2015-2016-titles Website: www.shakastech.com, Email - id: shakastech@gmail.com, info@shakastech.com 2015- 2016 EMR A Scalable Graph-based Ranking Model for Content-based Image Retrieval An Attribute-Assisted Reranking Model for Web Image Search TEES An Efficient Search Scheme over Encrypted Data on Mobile Cloud Automatic Face Naming by Learning Discriminative Affinity Matrices From Weakly Labeled Images Head Pose Estimation From a 2D Face Image Using 3D Face Morphing With Depth Parameters Face Recognition Across Non Uniform Motion Blur, Illumination, and Pose Single Image Super-Resolution Based on Gradient Profile Sharpness Friendbook A Semantic-Based Friend Recommendation System for Social Networks Cloud-Based Multimedia Content Protection System Energy-aware Load Balancing and Application Scaling for the Cloud Ecosystem Universal Network Coding-Based Opportunistic Routing for Unicast Malware Propagation in Large-Scale Networks BRACER A Distributed Broadcast Protocol in Multi-Hop Cognitive Radio Ad Hoc Networks Fiducial Facial Point Extraction Using a Novel Projective Invariant A Distortion-Resistant Routing Framework for Video Traffic in Wireless Multihop Networks Effective Key Management in Dynamic Wireless Sensor Network Improved Privacy-Preserving P2P Multimedia Distribution Based on Recombined Fingerprints Passive IP Traceback Disclosing the Locations of IP Spoofers from Path Backscatter Behavior Rule Specification-Based Intrusion Detection for Safety Critical Medical Cyber Physical Systems Integrated Foreground Segmentation and Boundary Matting for Live Videos
