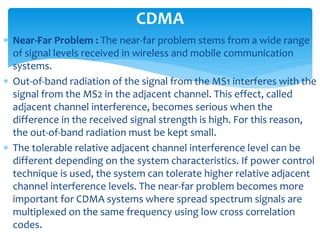
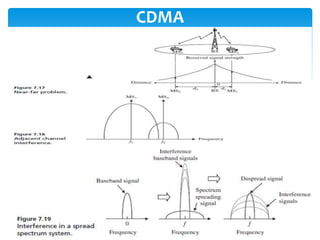
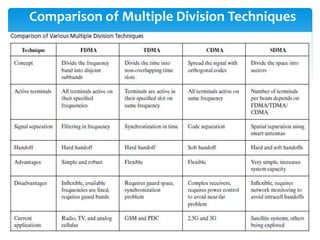
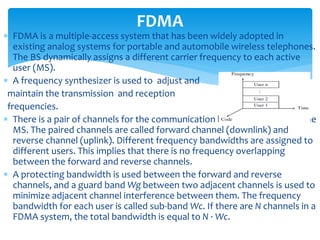
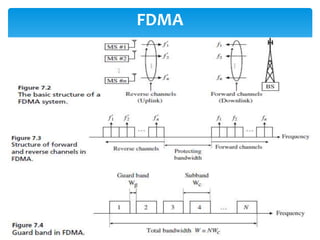
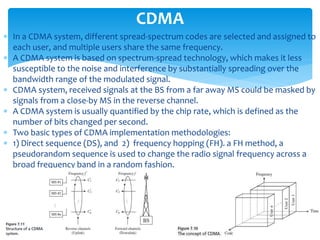
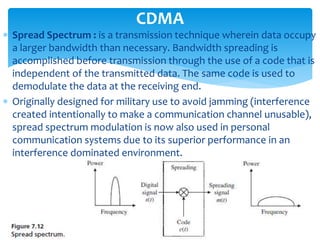
The document discusses various multiple access techniques used in wireless networks. It describes Frequency Division Multiple Access (FDMA), Time Division Multiple Access (TDMA), Code Division Multiple Access (CDMA), Orthogonal Frequency Division Multiplexing (OFDM), and Space Division Multiple Access (SDMA). It also covers concepts like duplexing methods, power control, modulation techniques, and the near-far problem in CDMA systems.
![ Walsh Codes : In CDMA, each user is assigned one or many
orthogonal waveforms derived from one orthogonal code. Since
the waveforms are orthogonal, users with different codes do not
interfere with each other.
CDMA requires synchronization among the users, since the
waveforms are orthogonal only if they are aligned in time. An
important set of orthogonal codes is the Walsh set . Walsh
functions are generated using an iterative process of constructing a
Hadamard matrix
starting with H0 = [0].
The Hadamard matrix
is built by using the
function :
CDMA](https://image.slidesharecdn.com/101771lec03-150523215917-lva1-app6891/85/three-12-320.jpg)