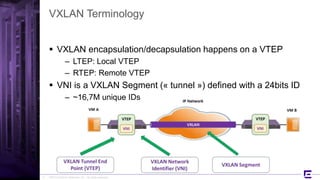
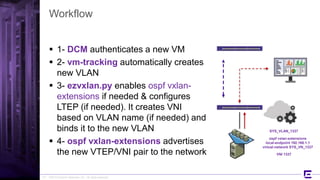
The document provides a comprehensive overview of VXLAN encapsulation, including its terminology, scalability limits, and configuration methods for Extreme Networks. It discusses the hardware requirements, network topologies, and design considerations, highlighting features like dynamic VNI learning and automation through the 'ezvxlan.py' script. Key points include the lack of IP multicast support and specific limits on virtual network identifiers across switches.