Where is the 6 GHz beef?
•
0 likes•79 views
Where is the 6 GHz beef? The low number of channels available today forces users to share available bandwidth and creates congestion. As each client station waits to transmit (or receive) data, congestion is caused by devices, Access Points and Stations, sharing the same channel. To better describe the impact of 6GHZ wifi, let us borrow the catchphrase "Where is the beef?". As a visual aid, begin with a hamburger bun with a 2.4GHz and 5GHz spectrum in the middle. The picture below may exaggerate a 20 years spectrum limitation. However, the visual expresses the potential of the 6GHz range to deliver the spectrum beef.
Report
Share
Report
Share
Download to read offline
Recommended
Where is the beef with 6 e

Where is the 6 GHz beef?
The low number of channels available today forces users to share available bandwidth and creates congestion. As each client station waits to transmit (or receive) data, congestion is caused by devices, Access Points and Stations, sharing the same channel. To better describe the impact of 6GHZ wifi, let us borrow the catchphrase "Where is the beef?". As a visual aid, begin with a hamburger bun with a 2.4GHz and 5GHz spectrum in the middle. The picture below may exaggerate a 20 years spectrum limitation. However, the visual expresses the potential of the 6GHz range to deliver the spectrum beef.
Where is the beef

Where is the 6 GHz beef?
The low number of channels available today forces users to share available bandwidth and creates congestion. As each client station waits to transmit (or receive) data, congestion is caused by devices, Access Points and Stations, sharing the same channel. To better describe the impact of 6GHZ wifi, let us borrow the catchphrase "Where is the beef?". As a visual aid, begin with a hamburger bun with a 2.4GHz and 5GHz spectrum in the middle. The picture below may exaggerate a 20 years spectrum limitation. However, the visual expresses the potential of the 6GHz range to deliver the spectrum beef.
What is Wi-Fi 6? - C&T RF Antennas Inc

Technically, Wi-Fi 6's single-user data rate is 37% faster than 802.11ac, but more importantly, the updated specification will provide four times the throughput and higher for each user in a crowded environment. Energy efficiency, which will increase the battery life of the device.
WiGig PPT

WiGig or IEEE 802.11ad, uses 60GHz spectrum to reach theoretical speeds as high as 7Gbps (bits per second), over a shorter range than today's Wi-Fi technologies. That's a lot more speed: The fastest Wi-Fi system, 802.11ac, tops out at just over 1Gbps.
Who's ready for 802.11ac and ad

Watch the full OnDemand Webcast: http://bit.ly/whoisready
We’re barely out of the gates with 802.11n, and we already have two new emerging standards that are likely to shake up the wireless world: 802.11ac and 802.11ad. 802.11ac is in many ways a "lessons learned" from 802.11n. It employs many of the same techniques to achieve even greater data rates, while requiring less power than with 802.11n – one of its biggest challenges. 802.11ad will expand data rates even further, taking advantage of new spectrum, which will enable entirely new uses cases for 802.11.
The future of Wi-Fi remains very strong. It is already way beyond critical mass, and with 802.11ac and 802.11ad it will remain the go-to-solution for the last 100 yards of any data network, and perhaps more. Users are now dependent on Wi-Fi, and there's nothing even close in the market that's ready to take its place. Please join us to discover how these new specifications will further entrench 802.11, where they’re likely to be used first, and whether or not you should be preparing yourself for a technology upgrade in the near future.
In this web seminar, we will cover:
- Current timeline in 802.11 development
- Characteristics of 802.11ac and 802.11ad
- Improvements over 802.11n
- Potential use cases for 802.11ac and 802.11ad
What you will learn:
- Whether 802.11ac and 802.11ad will have an enterprise footprint
- How 802.11ac and 802.11ad will integrate with current 802.11 deployments
- When you should be planning for a technology upgrade
Recommended
Where is the beef with 6 e

Where is the 6 GHz beef?
The low number of channels available today forces users to share available bandwidth and creates congestion. As each client station waits to transmit (or receive) data, congestion is caused by devices, Access Points and Stations, sharing the same channel. To better describe the impact of 6GHZ wifi, let us borrow the catchphrase "Where is the beef?". As a visual aid, begin with a hamburger bun with a 2.4GHz and 5GHz spectrum in the middle. The picture below may exaggerate a 20 years spectrum limitation. However, the visual expresses the potential of the 6GHz range to deliver the spectrum beef.
Where is the beef

Where is the 6 GHz beef?
The low number of channels available today forces users to share available bandwidth and creates congestion. As each client station waits to transmit (or receive) data, congestion is caused by devices, Access Points and Stations, sharing the same channel. To better describe the impact of 6GHZ wifi, let us borrow the catchphrase "Where is the beef?". As a visual aid, begin with a hamburger bun with a 2.4GHz and 5GHz spectrum in the middle. The picture below may exaggerate a 20 years spectrum limitation. However, the visual expresses the potential of the 6GHz range to deliver the spectrum beef.
What is Wi-Fi 6? - C&T RF Antennas Inc

Technically, Wi-Fi 6's single-user data rate is 37% faster than 802.11ac, but more importantly, the updated specification will provide four times the throughput and higher for each user in a crowded environment. Energy efficiency, which will increase the battery life of the device.
WiGig PPT

WiGig or IEEE 802.11ad, uses 60GHz spectrum to reach theoretical speeds as high as 7Gbps (bits per second), over a shorter range than today's Wi-Fi technologies. That's a lot more speed: The fastest Wi-Fi system, 802.11ac, tops out at just over 1Gbps.
Who's ready for 802.11ac and ad

Watch the full OnDemand Webcast: http://bit.ly/whoisready
We’re barely out of the gates with 802.11n, and we already have two new emerging standards that are likely to shake up the wireless world: 802.11ac and 802.11ad. 802.11ac is in many ways a "lessons learned" from 802.11n. It employs many of the same techniques to achieve even greater data rates, while requiring less power than with 802.11n – one of its biggest challenges. 802.11ad will expand data rates even further, taking advantage of new spectrum, which will enable entirely new uses cases for 802.11.
The future of Wi-Fi remains very strong. It is already way beyond critical mass, and with 802.11ac and 802.11ad it will remain the go-to-solution for the last 100 yards of any data network, and perhaps more. Users are now dependent on Wi-Fi, and there's nothing even close in the market that's ready to take its place. Please join us to discover how these new specifications will further entrench 802.11, where they’re likely to be used first, and whether or not you should be preparing yourself for a technology upgrade in the near future.
In this web seminar, we will cover:
- Current timeline in 802.11 development
- Characteristics of 802.11ac and 802.11ad
- Improvements over 802.11n
- Potential use cases for 802.11ac and 802.11ad
What you will learn:
- Whether 802.11ac and 802.11ad will have an enterprise footprint
- How 802.11ac and 802.11ad will integrate with current 802.11 deployments
- When you should be planning for a technology upgrade
Wi-Fi Module

A WI-Fi module presentation as a part of one complete course about using communication modules along with PIC-Micro-controller
Thanks.
How to migrate legacy serial devices to IP broadband

Ensure continued reliable operation of industrial systems that are using legacy serial (RS-232 and RS-485) modem connections and how to migrate to a future proof IP based solution.
This presentation by Westermo’s Technical Director Ray Lock is an integral part of the Westermo webinar covering Serial to IP migration: https://www.westermo.com/news-and-events/webinars/serial-modem-to-ip-broadband-migration
Lorawan: What you need to know

This presentation gives an overview of the technology, and some technical details. Also the operators in Belgium are listed.
WLAN(802.11AX - WI-FI 6) Evolution, frequency band, channels & use cases

WLAN(802.11AX - WI-FI 6) Evolution, frequency band, channels & use cases
How to secure your industrial network using segmentation and segregation

How to secure your industrial network using segmentation and segregationWestermo Network Technologies
This presentation by Westermo’s Cyber Security Product Manager Niklas Mörth and Network Applications Expert Dr. Jon-Olov Vatn is an integral part of the Westermo cybersecurity webinar on Network segmentation and segregation: https://www.westermo.com/news-and-events/webinars/cybersecurity-fundamentals-network-segmentation
The defense in depth value of segmenting your network into different security zones is widely recognized and should be a part of every company’s security strategy. A properly segmented network will reduce the attack surface, limit an attacker’s potential to move laterally in the network, and strongly limiting the potential damage of a cyber-attack. However, segmenting your network is a major project and will change how you are managing your network.Lora vs Zigbee

After the read, you will learn about what are the differences between Lora vs Zigbee.
What is the result of Lora vs ZigBee?
ZigBee is a low-power local area network protocol based on the IEEE802.15.4 standard. Lora is one of the LPWAN communication technologies. Lora vs ZigBee, Which one is better?
In the following, we will discuss the LoRa vs ZigBee differences, Comprehensive analysis of the technology of LoRa vs ZigBee.
Webinar how to prepare for the sunset of 2G and 3G cellular communications

Webinar how to prepare for the sunset of 2G and 3G cellular communicationsWestermo Network Technologies
ith the widespread adoption of 4G cellular technology as well as the growing availability of 5G products and services for remote industrial applications around the world, it is no longer a matter of if but rather a matter of when 2G and 3G services are being turned off.
But don't panic, we are here to help. In this short webinar, technical engineers Wesley Nel and Ant Lane walk you through what the phase out of 2G and 3G cellular communications mean, and most importantly, how you can prepare for it. IRJET- Wi-Fi, WiMAX & WiGig: A Comparative Study

https://www.irjet.net/archives/V5/i3/IRJET-V5I3512.pdf
Beginners: Top 10 Misconceptions About 5G

A short presentation looking at top 10 misconceptions about 5G.
1. 5G will be revolution, not Evolution
2. 5G requires millimetre waves (mmWave)
3. 5G needs new spectrum
4. 5G needs large amounts of bandwidth
5. 5G will give super-high speeds
6. 5G networks will have less than 1ms latency
7. 5G networks will be small cells
8. 5G needs Massive MIMO
9. 5G is needed for Autonomous Cars
10. 5G is dangerous for health
Latest Developments in WirelessNetworking and Wireless Security

http://www.iosrjournals.org/iosr-jce/pages/v12i1.html
Wi fi protected access

This is the the technology which is very basic understanding on Wi- Fi technology..
What is Wi-Fi technology and how is working and also the advantages of wi-fi.....
More Related Content
What's hot
Wi-Fi Module

A WI-Fi module presentation as a part of one complete course about using communication modules along with PIC-Micro-controller
Thanks.
How to migrate legacy serial devices to IP broadband

Ensure continued reliable operation of industrial systems that are using legacy serial (RS-232 and RS-485) modem connections and how to migrate to a future proof IP based solution.
This presentation by Westermo’s Technical Director Ray Lock is an integral part of the Westermo webinar covering Serial to IP migration: https://www.westermo.com/news-and-events/webinars/serial-modem-to-ip-broadband-migration
Lorawan: What you need to know

This presentation gives an overview of the technology, and some technical details. Also the operators in Belgium are listed.
WLAN(802.11AX - WI-FI 6) Evolution, frequency band, channels & use cases

WLAN(802.11AX - WI-FI 6) Evolution, frequency band, channels & use cases
How to secure your industrial network using segmentation and segregation

How to secure your industrial network using segmentation and segregationWestermo Network Technologies
This presentation by Westermo’s Cyber Security Product Manager Niklas Mörth and Network Applications Expert Dr. Jon-Olov Vatn is an integral part of the Westermo cybersecurity webinar on Network segmentation and segregation: https://www.westermo.com/news-and-events/webinars/cybersecurity-fundamentals-network-segmentation
The defense in depth value of segmenting your network into different security zones is widely recognized and should be a part of every company’s security strategy. A properly segmented network will reduce the attack surface, limit an attacker’s potential to move laterally in the network, and strongly limiting the potential damage of a cyber-attack. However, segmenting your network is a major project and will change how you are managing your network.Lora vs Zigbee

After the read, you will learn about what are the differences between Lora vs Zigbee.
What is the result of Lora vs ZigBee?
ZigBee is a low-power local area network protocol based on the IEEE802.15.4 standard. Lora is one of the LPWAN communication technologies. Lora vs ZigBee, Which one is better?
In the following, we will discuss the LoRa vs ZigBee differences, Comprehensive analysis of the technology of LoRa vs ZigBee.
Webinar how to prepare for the sunset of 2G and 3G cellular communications

Webinar how to prepare for the sunset of 2G and 3G cellular communicationsWestermo Network Technologies
ith the widespread adoption of 4G cellular technology as well as the growing availability of 5G products and services for remote industrial applications around the world, it is no longer a matter of if but rather a matter of when 2G and 3G services are being turned off.
But don't panic, we are here to help. In this short webinar, technical engineers Wesley Nel and Ant Lane walk you through what the phase out of 2G and 3G cellular communications mean, and most importantly, how you can prepare for it. IRJET- Wi-Fi, WiMAX & WiGig: A Comparative Study

https://www.irjet.net/archives/V5/i3/IRJET-V5I3512.pdf
Beginners: Top 10 Misconceptions About 5G

A short presentation looking at top 10 misconceptions about 5G.
1. 5G will be revolution, not Evolution
2. 5G requires millimetre waves (mmWave)
3. 5G needs new spectrum
4. 5G needs large amounts of bandwidth
5. 5G will give super-high speeds
6. 5G networks will have less than 1ms latency
7. 5G networks will be small cells
8. 5G needs Massive MIMO
9. 5G is needed for Autonomous Cars
10. 5G is dangerous for health
What's hot (18)
How to migrate legacy serial devices to IP broadband

How to migrate legacy serial devices to IP broadband
WLAN(802.11AX - WI-FI 6) Evolution, frequency band, channels & use cases

WLAN(802.11AX - WI-FI 6) Evolution, frequency band, channels & use cases
How to secure your industrial network using segmentation and segregation

How to secure your industrial network using segmentation and segregation
Webinar how to prepare for the sunset of 2G and 3G cellular communications

Webinar how to prepare for the sunset of 2G and 3G cellular communications
Similar to Where is the 6 GHz beef?
Latest Developments in WirelessNetworking and Wireless Security

http://www.iosrjournals.org/iosr-jce/pages/v12i1.html
Wi fi protected access

This is the the technology which is very basic understanding on Wi- Fi technology..
What is Wi-Fi technology and how is working and also the advantages of wi-fi.....
Living in the Jungle: Legitimate users in Legitimate Insecure Wireless Networks

Trabajo realizado para la medición del grado de inseguridad de una red WiFi a la que se conecta un equipo. En él se analizan las medidas de seguridad, el riesgo y los motivos por los que existen las redes WiFi inseguras
Throughput Analysis of IEEE WLAN "802.11 ac" Under WEP, WPA, and WPA2 Securit...

WLAN (Wireless Local Area Networks) are gaining their grounds, and widely deployed in organizations, college campuses, public places, and residential areas. This growing popularity of WLAN makes these networks more vulnerable towards attacks and data thefts. Attacker attempts unauthorized access to the network for accessing the sensitive data of the users. Thus, it's necessary to address all the security challenges and its countermeasures using various encryption algorithms to prevent the attacks. However, with the use of security protocols the performance of the WLAN network can be varied. Thus this paper addresses the impact of various security protocols on the WLAN network, keeping throughput as the benchmark for network performance.
IEEE 802.11 ac is the latest wireless standard that operates in 5 Ghz frequency band with higher data rate, compare to its previous standards. This research has also chosen IEEE 802.11 ac standard for investigating the impact of security protocols including WEP (Wired Equivalent Privacy), WPA (WiFi Protected Access), and WPA2 (WiFi Protected Access 2) on throughput of WLAN IEEE 802.11 ac in Windows environment using TCP and UDP traffic for both IP versions (IPv4 & IPv6). The research was launched in a real test-bed setup, with a Client/Server network structure. The results from the experiment showed that the performance of data throughput in the open system were higher comparable to secured systems. However, the results demonstrated that the performance of throughput have different behavior to different security protocols under TCP/UDP traffic with IPV4 & IPV6. A detailed comparison of results in all scenarios is explained in the paper.
SECURING IEEE 802.11G WLAN USING OPENVPN AND ITS IMPACT ANALYSIS

Like most advances, wireless LAN poses both opportunities and risks. The evolution of wireless networking in recent years has raised many serious security issues. These security issues are of great concern for this technology as it is being subjected to numerous attacks. Because of the free-space radio transmission in wireless networks, eavesdropping becomes easy and consequently a security breach may result in unauthorized access, information theft, interference and service degradation. Virtual Private Networks (VPNs) have emerged as an important solution to security threats surrounding the use of public networks for private communications. While VPNs for wired line networks have matured in both research and commercial environments, the design and deployment of VPNs for WLAN is still an evolving field. This paper presents an approach to secure IEEE 802.11g WLAN using OpenVPN, a transport layer VPN solution and its impact on performance of IEEE 802.11g WLAN.
Databook 2018 ver2

DrayTek, established in 1997 by a group of talented engineers is now the world-leading supplier of state-of-the-art networking solutions. We have migrated from the leading provider of remote access solutions to the customized networking solutions for diverse local markets around the world. At present, DrayTek's solutions ranging from enterprise-level firewalls, mission-critical VPN/VoIP facilities for SoHo, various xDSL/broadband CPE, to prospective telecommunication products and TR-069 central management solutions (e.g. VigorACS SI) can meet the market trend and go above and beyond customers' expectations.
Our success comes from the way how we build our brand. For us, DrayTek is not only a brand name but also as a commitment of quality and service.
Wireless network security 

ALL ABOUT THE PRECAUTIONS AND SECURITY MEASURES NEED TO BE TAKEN IN ORDER TO PREVENT UNAUTHORIZED ACCESS TO UR WIRELESS NETWORK
Wireless hacking

This ppt includes what is wireless hacking, types of wi-fi eg,wep,wpa,wpa/psk and terms related to it .this also conclude how to crack the wireless hacking ,the tools and commands required for it. this is very usefull . catch it..... :)
Module 15 (hacking wireless networks)

Wireless networks are accessible to anyone within the router’s transmission radius. This makes them vulnerable to attacks. Hotspots are available in public places such as airports, restaurants, parks, etc.
In this module, we will introduce you to common techniques used to exploit weaknesses in wireless network security implementations. We will also look at some of the countermeasures you can put in place to protect against such attacks.
Overview of WLAN security functions (ENG)

Source:Hirschmann
SSID broadcast
IPSec over Wlan
LEPS
MultiSSD
...
www.regeltechnieken.org
www.ie-net.be/reg
Wifi Security

For explaination of slides see write up
http://www.slideshare.net/shitalkr/wifi-technolgoy-writeup
Wireless LAN Deployment Best Practices

Wireless LAN Deployment Best Practices presentation for ISACA Singapore 2005/08/19
Securing wireless network

When setting up and maintaining Wi-Fi home networks, consider these tips for maximizing the security of the computers and data on these networks.
Securing Wireless Networks by maximizing the security of 802.11 standard and minimizing the Risk on Wireless network
Similar to Where is the 6 GHz beef? (20)
Latest Developments in WirelessNetworking and Wireless Security

Latest Developments in WirelessNetworking and Wireless Security
Living in the Jungle: Legitimate users in Legitimate Insecure Wireless Networks

Living in the Jungle: Legitimate users in Legitimate Insecure Wireless Networks
Throughput Analysis of IEEE WLAN "802.11 ac" Under WEP, WPA, and WPA2 Securit...

Throughput Analysis of IEEE WLAN "802.11 ac" Under WEP, WPA, and WPA2 Securit...
SECURING IEEE 802.11G WLAN USING OPENVPN AND ITS IMPACT ANALYSIS

SECURING IEEE 802.11G WLAN USING OPENVPN AND ITS IMPACT ANALYSIS
More from Jeff Green
The next generation ethernet gangster (part 3)

The original competitors in the Ethernet market remind me of gang members who each had their unique advantages to win over their turf. Over the past few years, Extreme assembled seven gangers from a variety of backgrounds with their strengths to perform a mission and deliver a new level of value to our customers. Extreme has adopted a gangster strategy going against the grain of the market leader. So far, the gangster strategy has been a winning strategy. When market leaders are proposing proprietary solutions, Extreme went open Linux with “superspec.” When they pushed DNA and its additional complexity, Extreme responded by re-thinking the way networks are designed, deployed, and managed without vendor lock-in. Final-ly, when they tied to service and to licensing together with Cisco One, Extreme responded with added flexibility in both licensing, services, and Extreme-as-a-service.
The next generation ethernet gangster (part 2)

The original competitors in the Ethernet market remind me of gang members who each had their unique advantages to win over their turf. Over the past few years, Extreme assembled seven gangers from a variety of backgrounds with their strengths to perform a mission and deliver a new level of value to our customers. Extreme has adopted a gangster strategy going against the grain of the market leader. So far, the gangster strategy has been a winning strategy. When market leaders are proposing proprietary solutions, Extreme went open Linux with “superspec.” When they pushed DNA and its additional complexity, Extreme responded by re-thinking the way networks are designed, deployed, and managed without vendor lock-in. Final-ly, when they tied to service and to licensing together with Cisco One, Extreme responded with added flexibility in both licensing, services, and Extreme-as-a-service.
The next generation ethernet gangster (part 1)

The original competitors in the Ethernet market remind me of gang members who each had their unique advantages to win over their turf. Over the past few years, Extreme assembled seven gangers from a variety of backgrounds with their strengths to perform a mission and deliver a new level of value to our customers. Extreme has adopted a gangster strategy going against the grain of the market leader. So far, the gangster strategy has been a winning strategy. When market leaders are proposing proprietary solutions, Extreme went open Linux with “superspec.” When they pushed DNA and its additional complexity, Extreme responded by re-thinking the way networks are designed, deployed, and managed without vendor lock-in. Final-ly, when they tied to service and to licensing together with Cisco One, Extreme responded with added flexibility in both licensing, services, and Extreme-as-a-service.
The next generation ethernet gangster (part 3)

Today Extreme can be more aggressive, with confidence in knowing we can compete with anyone in the market. As the #1 market alternative, there are three critical reasons for including Extreme in your technology considerations: our end-to-end portfolio, our fabric, and our customer service. We are moving Extreme from a reactive, tactical vendor to a pro-active, strategic partner. When Extreme gets a seat at the table, and we bring our unique “sizzle,” we are the customer’s choice. Our customer retention rate is unmatched in the industry, according to Gartner.
Jeff Green
Extreme Networks
jgreen@extremenetworks.com
Mobile (772) 925-2345
https://prezi.com/view/BFLC71PVkoYVKBOffPAv/
The next generation ethernet gangster (part 2)

Today Extreme can be more aggressive, with confidence in knowing we can compete with anyone in the market. As the #1 market alternative, there are three critical reasons for including Extreme in your technology considerations: our end-to-end portfolio, our fabric, and our customer service. We are moving Extreme from a reactive, tactical vendor to a pro-active, strategic partner. When Extreme gets a seat at the table, and we bring our unique “sizzle,” we are the customer’s choice. Our customer retention rate is unmatched in the industry, according to Gartner.
Jeff Green
Extreme Networks
jgreen@extremenetworks.com
Mobile (772) 925-2345
https://prezi.com/view/BFLC71PVkoYVKBOffPAv/
Places in the network (featuring policy)

Networks of the Future will be about a great user experience, devices and things…
In an industry that’s already defined, Extreme Network’s recent announcement of The Automated Campus is a significant advance in networking. For the first time, all the essential technologies, products, procedures and support are gathered together and integrated. All too often, the piecemeal/piecewise growth strategy, typically applied in network evolutions, results in too many tools, procedures, and techniques. The patchwork quilt approach precludes fast responsiveness, optimal operations staff productivity, and sacrifices the accuracy and efficiency required to keep end-users productive as well.
The most important opportunity to improve efficiency for governments today is in boosting both the productivity of end-users and network operators. The automated campus must address the productivity of network planners and network operations managers and staff. The often-significant number of elements required in an installation can demand significant staff time and can, consequentially, have an adverse impact on operating expenses (OpEx). While It is possible to build traditional networks that, when running correctly and optimally get the job done, they often embody such high operating expenses that cost becomes the overriding factor controlling the evolution of the campus network. The Automated Campus will allow XYZ Account to address all these issues and concerns. A key goal must be for XYZ Account to reduce the number of “moving parts” required to build and operate any campus and introduce a level of simplicity and automation that will address your future.
Extreme’s strategy for Campus Automation begins with re-thinking the way networks are designed, deployed and managed. Extreme’s Fabric-based networks enable faster configuration and troubleshooting; As a result, there is less opportunity for misconfiguration. Several automation solutions designed to enhance security often force network managers to accept complexity and degraded resilience to secure the network to meet local policies. Should a breach occur, containment to that segment protects even more sensitive parts of the network, resulting in a true dead-end for the hacker. With Extreme’s Automated Campus services can easily be defined and provisioned on-the-fly without disruption. Network operators specify what services are allowed or prohibited across the network.
Elephant & mice flows

The ubiquitous heavy-tailed distributions in the Internet im-plies an interesting feature of the Internet traffic: most (e.g. 80%) of the traffic is actually carried by only a small number of connections (elephants), while the remaining large amount of connections are very small in size or lifetime (mice). In a fair network environment, short connections expect rela-tively fast service than long connections. For these reasons, short TCP flows are generally more con-servative than long flows and thus tend to get less than their fair share when they compete for the bottleneck bandwidth. In this paper, we propose to give preferential treatment to short flows2 with help from an Active Queue Management (AQM) policy inside the network. We also rely on the pro-posed Differentiated Services (Diffserv) architecture [3] to classify flows into short and long at the edge of the network. More specifically, we maintain the length of each active flow (in packets3) at the edge routers and use it to classify incoming packets.
Fortinet ngf w extreme policy

Fortinet Firewall Integration - User to IP Mapping and Distributed Threat Response
oAccurate User ID to IP mapping eliminates potential attacks and provides reliable, out of the box User Information to firewalls
oImproves security by blocking/limiting user access at the point of entry without impacting other users
oMore accurate network mapping for dynamic policy enforcement and reporting
In an industry that’s already defined, Extreme Network’s recent announcement of The Automated Branch is a significant advance in networking. For the first time, all the essential technologies, products, procedures and support are gathered together and integrated. All too often, the piecemeal/piecewise growth strategy typically historically applied in organizational network evolution results in too many tools, procedures, and techniques at work, precluding fast responsiveness, optimal operations staff productivity, and the degree of accuracy and efficiency required to keep end-users productive as well.
Multi fabric sales motions jg v3

This reference design helps organizations design and configure a small to midsize data center (be¬tween 2 and 60 server racks) at headquarters or a server room at a remote site. You will learn how to configure the data center core, aggregation and access switches for connectivity to the servers and the campus network.
The Avaya Fabric Connect data center design supports high-speed 10 Gbps Ethernet connect-ed servers. The design can easily scale server bandwidth with link aggregation and servers can be connected to one or more switches in order to provide the level of availability required for the services delivered by the host. The design also supports legacy and low traffic servers that need 1 Gbps Ethernet connectivity,
The reference design presented in this guide is based on common network requirements and pro¬vides a tested starting point for network engineers to design and deploy an Avaya data center net¬work. This guide does not document every possible option and feature used to design and deploy networks but instead presents the tested and recommended options that will meet the majority of customer needs.
This design uses Avaya Fabric Connect in order to provide benefits over traditional data center design.
IT departments face several challenges in today’s data center:
· Data center traffic flow is not the same as campus traffic flow. Over 80% of the traffic is east-west, server-to-server, vs. north-south, client-to-server, like in a campus.
· Server virtualization allows a virtual machine or workload to be located anywhere in the physi¬cal data center. Data center networks can make it difficult to extend virtual local area networks (VLANs) and subnets anywhere in the data center.
· Server virtualization means that new services can be brought online in minutes or migrated in real time. Reconfiguring the network to support this is difficult because it can interrupt other services.
· Server virtualization means that the load on a physical box is much higher. Physical servers regularly host 10-50 workloads, driving network utilization well past 1 Gbps.
Data center pov 2017 v3

LANs are constantly evolving, build your XYZ Account Network with that baked-in…
Extreme Networks brings XYZ Account simplicity, agility, and optimized performance to your most strategic business asset. The data center is critically important to business operations in the enterprise, but often organizations have difficulty leveraging their data centers as a strategic business asset. At Extreme Networks, we focus on providing an Intelligent Enterprise Data Center Network that’s purpose-built for enterprise requirements. Our OneFabric Data Center Solution:
XoS “can be like an elastic Fabric” for XYZ Account Network…
Demand for application availability has changed how applications are hosted in today’s datacenter. Evolutionary changes have occurred throughout the various elements of the data center, starting with server and storage virtualization and network virtualization. Motivations for server virtualization were initially associated with massive cost reduction and redundancy but have now evolved to focus on greater scalability and agility within the data center. Data center focused LAN technologies have taken a similar path; with a goal of redundancy and then to create a more scalable fabric within and between data centers.
As vendors continue to tout networking architectures that decouple software from hardware, bare-metal switches are moving into the spotlight. These switches are built on merchant silicon deliver a lower-cost and more flexible switching alternative. Extreme Purple Metal switches are open enough to allow our customers to choose their network architecture based on their specific needs without going all the way to bare metal. We believe in the disaggregation of traditional enterprise networking. Extreme uses merchant silicon versus custom ASICs. Custom ASICs have fallen behind. Unless a vendor can build and compete against merchant silicon, there's no point in doing custom ASICs.
Audio video ethernet (avb cobra net dante)

AVB fits low-cost, small-form-factor products such as this microphone. The overall trend is that music no longer lives on shelves or in CD racks, but in hard drives in home computers, and increasingly in the cloud. This brings about its own unique problems, not in the encoding system used, or the storage technology, but in distributing the audio from the storage media to the speakers. AVB features are all enabled by a global and port level configuration. Connecting these elements is the AVB-enabled switch (in the graphic above, the Extreme Networks® Summit® X440.) The role of the switch is to provide support for the control protocols: AVB is Ethernet’s next stage of convergence, delivering pitch perfect audio and crystal clear video seamlessly over the network
IP/Ethernet is bringing simplicity and features to audio and video as it has brought to services like VoIP, Storage and many more
High quality, perfectly synchronized A/V until now has been difficult to maintain
Standards work by the IEEE and the AVB standard changes everything, creating interoperability and mass-marketing equipment pricing
Benefits of AVB - Delivers predictable latency and precise synchronization, maximizing the functionality of AV – time synchronization and quality or service
Reduced complexity and Ease of use through interoperability between devices
Streamlines complex network set-up and management, the Infrastructure negotiates and manages the network for optimal prioritized media transport
AV traffic can co-exist with non-AV traffic on same Ethernet infrastructure
Role based control at the XYZ Account - XYZ Account can identify devices and apply policies based on device type all the way down to the port and or the AP. Policies can dynamically change based on the device a user is connecting with and where that user is located. Extreme Networks provides infrastructure to deliver customizable prioritization and scalable capacity via configurable and built-in intelligence, ensuring a comprehensive, superior quality experience. Furthermore, when deployed with Extreme Wireless XYZ Account can configure the network to ensure applications receive the bandwidth they require, while still limiting or preventing high speed streaming of music of video or even games.
Avb pov 2017 v2

The Pug is a breed of dog with a wrinkly, short-muzzled face, and curled tail. The breed has a fine, glossy coat that comes in a variety of colours, most often fawn or black, and a compact square body with well-developed muscles.
Pugs were brought from China to Europe in the sixteenth century and were popularized in Western Europe by the House of Orange of the Netherlands, and the House of Stuart.In the United Kingdom, in the nineteenth century, Queen Victoria developed a passion for pugs which she passed on to other members of the Royal family. Pugs are known for being sociable and gentle companion dogs.[3] The breed remains popular into the twenty-first century, with some famous celebrity owners. A pug was judged Best in Show at the World Dog Show in 2004.
Donald J. Trump For President, Inc. –– Why Now?
On November 8, 2016, the American People delivered a historic victory and took our country back. This victory was the result of a Movement to put America first, to save the American economy, and to make America once again a shining city on the hill. But our Movement cannot stop now - we still have much work to do.
This is why our Campaign Committee, Donald J. Trump for President, Inc., is still here.
We will provide a beacon for this historic Movement as our lights continue to shine brightly for you - the hardworking patriots who have paid the price for our freedom. While Washington flourished, our American jobs were shipped overseas, our families struggled, and our factories closed - that all ended on January 20, 2017.
This Campaign will be a voice for all Americans, in every city near and far, who support a more prosperous, safe and strong America. That’s why our Campaign cannot stop now - our Movement is just getting started.
Together, we will Make America Great Again!
Layer 2 forwarding on an spb fabric

In an industry that’s already defined, Extreme Network’s recent announcement of The Automated Campus is a significant advance in networking. For the first time, all the essential technologies, products, procedures and support are gathered together and integrated. All too often, the piecemeal/piecewise growth strategy typically historically applied in organizational network evolution results in too many tools, procedures, and techniques at work, precluding fast responsiveness, optimal operations staff productivity, and the degree of accuracy and efficiency required to keep end-users productive as well.
The most important opportunity today is in boosting both productivity of end-users and network operators. The automated campus must address the productivity of network planners and network operations managers and staff. The often-significant number of elements required in an installation can demand significant staff time and can consequentially have an adverse impact on operating expenses (OpEx). While It is possible to build traditional networks that, when running correctly and optimally, get the job done – unfortunately, they often embody such high operating expenses that cost becomes the overriding factor controlling the evolution of the campus network overall. The Automated Campus will allow XYZ Account to address all these issues and concerns. A key goal here must be, of course, to reduce the number of “moving parts” required to build and operate any campus.
Extreme’s strategy for Campus Automation begins with re-thinking the way networks are designed, deployed and managed. Extreme’s Fabric-based networks enable faster configuration and troubleshooting; As a result, there is less opportunity for misconfiguration. Several automation solutions designed to enhance security often force network managers to accept complexity and degraded resilience to secure the network to meet local policies. Should a breach occur, containment to that segment protects even more sensitive parts of the network, resulting in a true dead-end for the hacker. With Extreme’s Automated Campus services can easily be defined and provisioned on-the-fly without disruption. Network operators specify what services are allowed or prohibited across the network.
8.) xo s as a platform (on off premise)

XoS Performance - Separation between control and forwarding planes - The "SDN Classic" model, as illustrated by this graphic from the Open Networking Foundation, offers many potential benefits:
In the forwarding plane all switching, and feature implementation such as deep packet inspection , QoS scheduling, MAC learning and filtering, etc are performed in dedicated ASIC hardware
Wire speed performance across entire product line (Backplane resources, packet /frame forwarding rate, Bits per second throughput) Local switching on all line cards at no additional cost ,increasing throughput and reducing latency. Dedicated stacking interfaces, and stacking over fiber.
Low latency with Exceptional QoS
We build networks to deliver on today’s Experience Economy. Extreme Networks combines high performance wired and wireless hardware with a software-defined architecture that makes it simple, fast and smart for the user to connect with their device of choice. We provide a comprehensive portfolio, including Campus Mobility and Data Center solutions, which allow our customers to deliver a positive and consistent experience to each and every user in their environment. As SDN excitement grew, the term software-defined was adopted by marketers and applied liberally to all kinds of products and technologies: software-defined storage, software-defined security, software-defined data center.
What technologies allow me to do this today?
Key Features: Loop free load balancing, density, L2 overlays
VXLAN fabric in EXOS / EOS
MLAG: L2 Leaf/Spine with two spine members
VPLS: L2 Leaf/Spine for HPC deployments
SPB-V: S/K-Series for small enterprise data center
Evolution ExtremeFabric: fully automated
Why VxLAN? It’s a really easy L2 over L3 transport
MLAG technology Leaf/Spine Fabric
MLAG is a special case of Leaf/Spine with only two spine members and everything on L2 (We kill the spanning tree and maintain state between the spines) – We’ve been leading in MLAG for a while
VPLS technology Leaf/Spine Fabric
We have successfully built VPLS mesh Leaf/Spine networks for HPC deployments
Key Features: Loop free load balancing, density, L2 overlays
We need more scale!
21.x / 22.x bring some interesting new features that fix this
NEW with 21.1: The Scalable Layer 2 Fabric with VxLAN Technology
VXLAN – Overlay on routing for efficient load balancing and reachability
OSPF extensions massively simplify deployment
The Layer 2 traffic tunnels over any Layer 3 network
Can be used in any topology, but highest performance is Leaf/Spine
Removes the limitation on transit overlay in the spine
Easy setup, small configuration
X670-G2 and X770, S and K, and will be available on X870 at launch
Scale to 2592 10G ports (X670-G2-72, 1:1), 512 40G (X770, 1:1)
Available on EOS and EXOS NOW
NEW with EXOS 22.x and EOS 8.81: Future Fabric Technology
12.) fabric (your next data center)

Extreme is rethinking the data plane, the control plane, and the management plane. Extreme is a better mouse trap which delivers new features, advanced function, and wire-speed performance. Our switches deliver deterministic performance independent of load or what features are enabled. All Extreme Switches are based on XOS, the industries first and only truly modular operating system. Having a modular OS provides higher availability of critical network resources. By isolating each critical process in its own protected memory space, a single failed process can not take down the entire switch. Application modules can be loaded and unloaded without the need for rebooting the switch. This is the level of functionality that users expect on other technology. Reaching the twenty million port milestone is a significant achievement demonstrating how our highly effective network solutions, with rich features, innovative software and integrated support for secure convergence. VoIP/Unified Communica Fons/Infrastructure/SIP Trunking (SBC) – Because of strong ROI, investment in this segment remains on a very strong growth trajectory.
Enterprises depend on modular switching solutions for all aspects of the enterprise network: in the enterprise core and data center, the distribution layer that lies between the core and wiring closet, and in the wiring closet itself. Modular solutions provide port diversity and density that fixed solutions simply cannot match. There are also high-capacity modular solutions that only the largest of enterprises and institutions use for high-density and high-speed deployments. Modular solutions are generally much more expensive than their fixed cousins, especially in situations where density or flexibility are not required.
Fixed-configuration stackable switches are typically cost- optimized, but they offer no real port diversity on an individual switch. Port diversity means the availability of different port types, such as fiber versus copper ports. Stackable switches have gotten better at offering port diversity, but they still cannot match their modular cousins. Many of these products now offer high-end features such as 802.3af PoE, QoS, and multi-layer intelligence that were only found on modular switches in the past. This is due to the proliferation of third-party merchant silicon in the fixed configuration market. Generally, a stack of fixed configuration switches can be managed as a single virtual entity. Fixed configuration switches generally cannot be used to provision an entire large enterprise, but instead are mostly used out at the edge or departmental level as a low-cost alternative to modular products.
Assumptions:
Ethernet is Open
Active/Active in the Fabric
Therefore:
Open at the Edge
Active/Active at the edge
10.) vxlan

The Secret Sauce is the Control Plane, not the Encapsulation
Host Route Distribution decoupled from the Underlay protocol
Use MultiProtocol-BGP (MP-BGP) on the Leaf nodes to distribute internal Host/Subnet Routes and external reachability information
Route-Reflectors deployed for scaling purposes
VXLAN terminates its tunnels on VTEPs (Virtual Tunnel End Point).
Each VTEP has two interfaces, one is to provide bridging function for local hosts, the other has an IP identification in the core network for VXLAN encapsulation/decapsulation.
VXLAN Encapsulation and De-encapsulation occur on T2
Bridging and Gateway are independent of the port type (1/10/40G ports)
Encapsulation happens on the egress port
Decapsulation happens on the ingress port
Service Oriented Architecture
2 or 3 layer network to Leaf & Spine
High density and bandwidth required
Layer 3 ECMP
No oversubscription
Low and uniform delay characteristic
Wire & configure once network
Uniform network configuration
Workload Mobility
Workload Placement
Segmentation
Scale
Automation & Programmability
L2 + L3 Connectivity
Physical + Virtual
Open
4.) switch performance (w features)

Where Does Networking Fit In? To gain the full benefits of cloud computing and virtualization and achieve a business agile IT infrastructure, organizations need a reliable, high-performance data center networking infrastructure with built-in investment protection. Several technology inflection points are coming together that are fundamentally changing the way networks are architected, deployed and operated both in the public cloud as well as the private cloud. From performance, to scale, to virtualization support and automation to simplified orchestration, the requirements are rapidly changing and driving new approaches to building data center networks.
With Extreme Networks, IT can manage more with less. Automated intelligence and analytics for compliance, forensics, and traffic patterns translates into reduced help desk calls. Businesses can predict costs and return on investment, and increase employee productivity by securely onboarding BYOD, increasing both customer and employee satisfaction. A constant risk to the network, and ultimately the hospital, are unapproved applications and rogue devices that may appear on the network and either permit unauthorized access or interfere with other devices. A means to monitor all devices and applications that operate across the network is vital. Just as important are the audit and reporting capabilities necessary to report on who, what, where, when, and how patient data is accessed.
What is SDN? What software-defined networking really means has evolved dramatically and now includes automation and virtualization. Hardware is still a critical component in data center networking equipment, but the influence of switch software shouldn’t be overlooked. When everyone began to get excited about SDN a few years ago, we thought of it as only one thing: the separation of network control from network data packet handling. Traditional networks had already started down this path, with the addition of controller cards to manage line cards in scalable chassis-based switches, and with various data center fabric technologies. SDN took the idea to its logical end, removing the need for the controller and the packet handlers to be on the same backplane or even from the same vendor.
Cost. Reducing costs in the data center and contributing to corporate profitability is an increasingly important trend in today’s economic climate. For example, energy costs for the data center are increasing at 12% a year. Moreover, increased application requirements such as 100% availability necessitate additional hardware and services to manage storage and performance thus raising total cost of ownership.
20.) physical (optics copper and power)

An alternative to the core/aggregation/access layer network topology has emerged known as leaf-spine. In a leaf-spine architecture, a series of leaf switches form the access layer. These switches are fully meshed to a series of spine switches. One way is to create a Spine and Leaf architecture, also known as a Distributed Core. This architecture has two main components: Spine switches and Leaf switches. Intuition Systems can think of spine switches as the core, but instead of being a large, chassis-based switching platform, the spine is composed of many high-throughput Layer 3 switches with high port density. The mesh ensures that access-layer switches are no more than one hop away from one another, minimizing latency and the likelihood of bottlenecks between access-layer switches. When networking vendors speak of an Ethernet fabric, this is generally the sort of topology they have in mind.
Haven’t we spent the last few decades disaggregating datacenter architecture? And if so, what does disaggregation mean now, is it something different? Strictly speaking, to “disaggregate” means to divide
19.) security pivot (policy byod nac)

Data Center Aggregation/Core Switch
The proposed solution must provide a high-density chassis based switch solution that meets the requirements provided below. Your response should describe how your offering would meet these requirements. Vendors must provide clear and concise responses, illustrations can be provided where appropriate. Any additional feature descriptions for your offering can be provided, if applicable.
• Must offer a chassis-based switch solution that provides eight I/O module slots, two management module slots and four fabric module slots. Must support a variety of I/O modules providing support for 1GbE, 10GbE, 40GbE and 100GbE interfaces. Please describe the recommended switching solution and the available I/O modules.
• Switch must offer switching capacity up to 20.48 Tbps. Please describe the performance levels for the recommended switching solution.
• Switch system must support high availability for the hardware preventing single points of failure. Please describe the high availability features.
• It is preferred that the 10 Gigabit Ethernet modules will also be able to accept standard Gigabit SFP transceivers. Please describe the capability of your switch.
• Must support an N+1 redundant power supplies
• Must support N+1 redundant fan trays
• Must support a modular operating system that is common across the entire switching profile. Please describe the OS and advantages.
More from Jeff Green (20)
Recently uploaded
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head of Product, Amazon Games
Epistemic Interaction - tuning interfaces to provide information for AI support

Paper presented at SYNERGY workshop at AVI 2024, Genoa, Italy. 3rd June 2024
https://alandix.com/academic/papers/synergy2024-epistemic/
As machine learning integrates deeper into human-computer interactions, the concept of epistemic interaction emerges, aiming to refine these interactions to enhance system adaptability. This approach encourages minor, intentional adjustments in user behaviour to enrich the data available for system learning. This paper introduces epistemic interaction within the context of human-system communication, illustrating how deliberate interaction design can improve system understanding and adaptation. Through concrete examples, we demonstrate the potential of epistemic interaction to significantly advance human-computer interaction by leveraging intuitive human communication strategies to inform system design and functionality, offering a novel pathway for enriching user-system engagements.
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scalable Platform by VP of Product, The New York Times
AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...

AI for Every Business: Unlocking Your Product's Universal Potential by VP of Product, Slack
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

Do you want to learn how to model and simulate an electrical network from scratch in under an hour?
Then welcome to this PowSyBl workshop, hosted by Rte, the French Transmission System Operator (TSO)!
During the webinar, you will discover the PowSyBl ecosystem as well as handle and study an electrical network through an interactive Python notebook.
PowSyBl is an open source project hosted by LF Energy, which offers a comprehensive set of features for electrical grid modelling and simulation. Among other advanced features, PowSyBl provides:
- A fully editable and extendable library for grid component modelling;
- Visualization tools to display your network;
- Grid simulation tools, such as power flows, security analyses (with or without remedial actions) and sensitivity analyses;
The framework is mostly written in Java, with a Python binding so that Python developers can access PowSyBl functionalities as well.
What you will learn during the webinar:
- For beginners: discover PowSyBl's functionalities through a quick general presentation and the notebook, without needing any expert coding skills;
- For advanced developers: master the skills to efficiently apply PowSyBl functionalities to your real-world scenarios.
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Presented by Suzanne Phillips and Alex Marcotte
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

As AI technology is pushing into IT I was wondering myself, as an “infrastructure container kubernetes guy”, how get this fancy AI technology get managed from an infrastructure operational view? Is it possible to apply our lovely cloud native principals as well? What benefit’s both technologies could bring to each other?
Let me take this questions and provide you a short journey through existing deployment models and use cases for AI software. On practical examples, we discuss what cloud/on-premise strategy we may need for applying it to our own infrastructure to get it to work from an enterprise perspective. I want to give an overview about infrastructure requirements and technologies, what could be beneficial or limiting your AI use cases in an enterprise environment. An interactive Demo will give you some insides, what approaches I got already working for real.
From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...

From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP of Product, Amplitude
Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...

Sidekick Solutions uses Bonterra Impact Management (fka Social Solutions Apricot) and automation solutions to integrate data for business workflows.
We believe integration and automation are essential to user experience and the promise of efficient work through technology. Automation is the critical ingredient to realizing that full vision. We develop integration products and services for Bonterra Case Management software to support the deployment of automations for a variety of use cases.
This video focuses on the notifications, alerts, and approval requests using Slack for Bonterra Impact Management. The solutions covered in this webinar can also be deployed for Microsoft Teams.
Interested in deploying notification automations for Bonterra Impact Management? Contact us at sales@sidekicksolutionsllc.com to discuss next steps.
Software Delivery At the Speed of AI: Inflectra Invests In AI-Powered Quality

In this insightful webinar, Inflectra explores how artificial intelligence (AI) is transforming software development and testing. Discover how AI-powered tools are revolutionizing every stage of the software development lifecycle (SDLC), from design and prototyping to testing, deployment, and monitoring.
Learn about:
• The Future of Testing: How AI is shifting testing towards verification, analysis, and higher-level skills, while reducing repetitive tasks.
• Test Automation: How AI-powered test case generation, optimization, and self-healing tests are making testing more efficient and effective.
• Visual Testing: Explore the emerging capabilities of AI in visual testing and how it's set to revolutionize UI verification.
• Inflectra's AI Solutions: See demonstrations of Inflectra's cutting-edge AI tools like the ChatGPT plugin and Azure Open AI platform, designed to streamline your testing process.
Whether you're a developer, tester, or QA professional, this webinar will give you valuable insights into how AI is shaping the future of software delivery.
DevOps and Testing slides at DASA Connect

My and Rik Marselis slides at 30.5.2024 DASA Connect conference. We discuss about what is testing, then what is agile testing and finally what is Testing in DevOps. Finally we had lovely workshop with the participants trying to find out different ways to think about quality and testing in different parts of the DevOps infinity loop.
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

💥 Speed, accuracy, and scaling – discover the superpowers of GenAI in action with UiPath Document Understanding and Communications Mining™:
See how to accelerate model training and optimize model performance with active learning
Learn about the latest enhancements to out-of-the-box document processing – with little to no training required
Get an exclusive demo of the new family of UiPath LLMs – GenAI models specialized for processing different types of documents and messages
This is a hands-on session specifically designed for automation developers and AI enthusiasts seeking to enhance their knowledge in leveraging the latest intelligent document processing capabilities offered by UiPath.
Speakers:
👨🏫 Andras Palfi, Senior Product Manager, UiPath
👩🏫 Lenka Dulovicova, Product Program Manager, UiPath
Connector Corner: Automate dynamic content and events by pushing a button

Here is something new! In our next Connector Corner webinar, we will demonstrate how you can use a single workflow to:
Create a campaign using Mailchimp with merge tags/fields
Send an interactive Slack channel message (using buttons)
Have the message received by managers and peers along with a test email for review
But there’s more:
In a second workflow supporting the same use case, you’ll see:
Your campaign sent to target colleagues for approval
If the “Approve” button is clicked, a Jira/Zendesk ticket is created for the marketing design team
But—if the “Reject” button is pushed, colleagues will be alerted via Slack message
Join us to learn more about this new, human-in-the-loop capability, brought to you by Integration Service connectors.
And...
Speakers:
Akshay Agnihotri, Product Manager
Charlie Greenberg, Host
Securing your Kubernetes cluster_ a step-by-step guide to success !

Today, after several years of existence, an extremely active community and an ultra-dynamic ecosystem, Kubernetes has established itself as the de facto standard in container orchestration. Thanks to a wide range of managed services, it has never been so easy to set up a ready-to-use Kubernetes cluster.
However, this ease of use means that the subject of security in Kubernetes is often left for later, or even neglected. This exposes companies to significant risks.
In this talk, I'll show you step-by-step how to secure your Kubernetes cluster for greater peace of mind and reliability.
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

In this session I delve into the encryption technology used in Microsoft 365 and Microsoft Purview. Including the concepts of Customer Key and Double Key Encryption.
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase Enterprise-Wide Efficiency by VP Data Platform, American Express
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

The publishing industry has been selling digital audiobooks and ebooks for over a decade and has found its groove. What’s changed? What has stayed the same? Where do we go from here? Join a group of leading sales peers from across the industry for a conversation about the lessons learned since the popularization of digital books, best practices, digital book supply chain management, and more.
Link to video recording: https://bnctechforum.ca/sessions/selling-digital-books-in-2024-insights-from-industry-leaders/
Presented by BookNet Canada on May 28, 2024, with support from the Department of Canadian Heritage.
Recently uploaded (20)
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...
Epistemic Interaction - tuning interfaces to provide information for AI support

Epistemic Interaction - tuning interfaces to provide information for AI support
FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf

FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...
AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...

AI for Every Business: Unlocking Your Product's Universal Potential by VP of ...
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Assuring Contact Center Experiences for Your Customers With ThousandEyes
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024
From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...

From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...
Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...

Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...
Software Delivery At the Speed of AI: Inflectra Invests In AI-Powered Quality

Software Delivery At the Speed of AI: Inflectra Invests In AI-Powered Quality
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...
Connector Corner: Automate dynamic content and events by pushing a button

Connector Corner: Automate dynamic content and events by pushing a button
Securing your Kubernetes cluster_ a step-by-step guide to success !

Securing your Kubernetes cluster_ a step-by-step guide to success !
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

Encryption in Microsoft 365 - ExpertsLive Netherlands 2024
Mission to Decommission: Importance of Decommissioning Products to Increase E...

Mission to Decommission: Importance of Decommissioning Products to Increase E...
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

Transcript: Selling digital books in 2024: Insights from industry leaders - T...
Where is the 6 GHz beef?
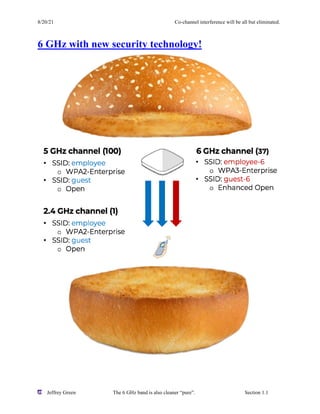
- 1. 8/20/21 Co-channel interference will be all but eliminated. Jeffrey Green The 6 GHz band is also cleaner “pure”. Section 1.1 6 GHz with new security technology!
- 2. 8/20/21 Co-channel interference will be all but eliminated. Jeffrey Green The 6 GHz band is also cleaner “pure”. Section 1.2 OWE – Enhanced Open. The OWE protocol integrates cryptography mechanisms to provide each user with unique individual encryption, protecting the data exchange. The experience for the user is the same as with open security because there is no need to enter a password or passphrase. Mitigation of Malicious eavesdropping. SAE – Simultaneous Authentication of Equals. A WPA3-Personal access point (AP) in transition mode enables WPA2-Personal and WPA3- Personal simultaneously on a single basic service set (BSS) to support client devices using a mix of WPA2-Personal and WPA3-Personal with the same passphrase. Client devices that support both WPA2-Personal and WPA3-Personal connect using the higher-security method of WPA3- Personal when available. OWE provides encryption without authentication. By far, the most significant change defined by WPA3 is the replacement of PSK authentication with Simultaneous Authentication of Equals(SAE), which is resistant to offline dictionary attacks. SAE leverages on a Dragonfly key exchange. Dragonfly is a patent-free and royalty-free technology that uses a zero-knowledge proof key exchange. • Opportunistic Wireless Encryption (OWE) • Encryption without authentication • Enhanced Open certification is not part of WPA3 and is an entirely different and optional security certification WPA3 Personal • WPA3 replacement for PSK. • Password key exchange based on a zero-knowledge proof. • Prove you know the credentials without compromising the credentials. • No forging, modification or replay attacks. • No offline dictionary attacks.
- 3. 8/20/21 Co-channel interference will be all but eliminated. Jeffrey Green The 6 GHz band is also cleaner “pure”. Section 1.3 The goal is to provide the same user experience by still using a passphrase.i The OWE experience for the user is the same as open security because there is no need to enter a password or passphrase before joining the network. Data privacy protects against malicious eavesdropping attacks. Nevertheless, please understand that there is zero authentication security. Enhanced Open is not part of WPA3 and is an entirely different and optional security certification for 2.4 GHz and 5 GHz frequency bands.ii SAE leverages Dragonfly key exchange. Customers understand that Enhanced Open meets only half of the requirements for well- rounded Wi-Fi security. OWE does provide encryption and data privacy, but there is no authentication whatsoever. As previously mentioned, Enhanced Open is an optional security certification. As a result, many WLAN vendors still do not support OWE, and client-side support is marginal at best but growing. Therefore, tactical deployments of OWE in the 2.4 and 5 GHz frequency bands are currently scarce. iiiiv WIPs and 6 GHz. Existing WIPS solutions will NOT be able to detect 6 GHz rogue APs and attacks. Current sensors do not have 6 GHz radios. The vendors with tri-band sensor capabilities will take the lead for WIPs in the 6 GHz band.
- 4. 8/20/21 Co-channel interference will be all but eliminated. Jeffrey Green The 6 GHz band is also cleaner “pure”. Section 1.4 i https://www.extremenetworks.com/extreme-networks-blog/wireless-security-in-a-6-ghz-wi-fi-6e-world/ ii https://www.extremenetworks.com/extreme-networks-blog/wireless-security-in-a-6-ghz-wi-fi-6e-world/ iv ttps://www.extremenetworks.com/extreme-networks-blog/wireless-security-in-a-6-ghz-wi-fi-6e-world/
