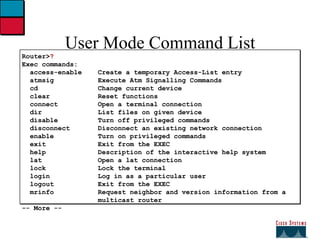
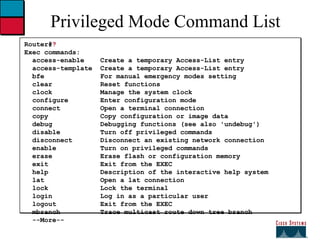
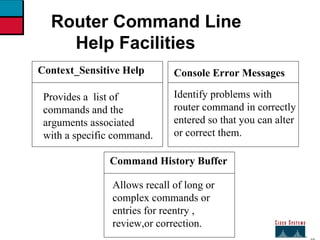
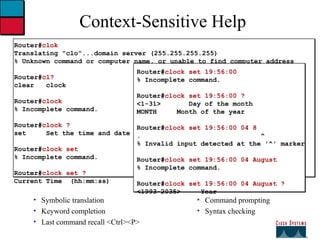
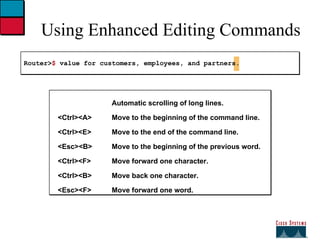
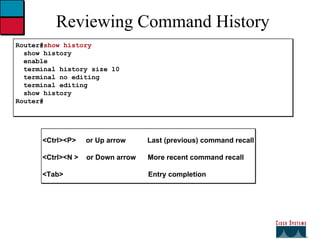
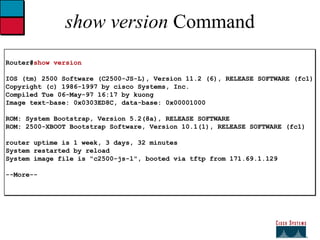
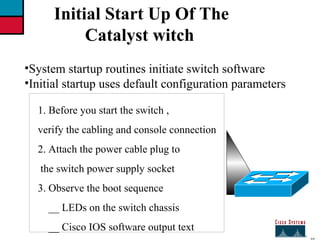
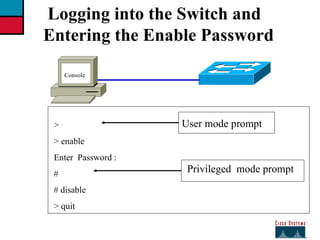
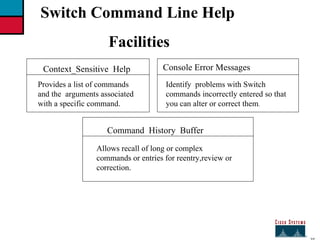
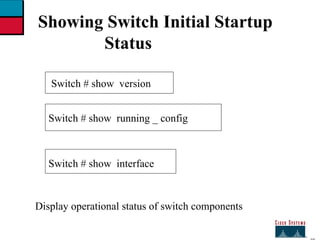
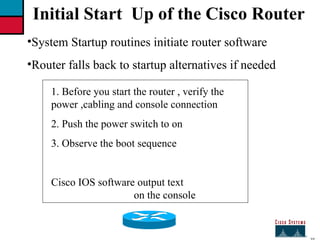
The document provides instructions for initial configuration of a Cisco switch and router. It describes the boot up processes, including observing LEDs and output text. It also explains how to access different command modes, set the switch and router names, configure IP addresses, and review the running configuration. Help features like context sensitive help and command history are also summarized.
![27 Initial Bootup Output from the Switch Catalyst 1900 Management Console Copyright © Cisco Systems ,Inc. 1993_1998 All rights reserved. Enterprise Edition Software Ethernet Address : 00-50-BD-73-E2-c0 PCA Number : 73-3121-01 PCA Serial Number : FAA0252A0QX Model Number: WS-C1924-EN System Serial Number : FAA0304s003 Power Supply S/N : PHI025101F3 ----------------------------------------------------------------- 1 User (s) now active on Management Console. User Interface Menu [ H ] Menus [ K ] Command Line [ I ] IP Configuration Enter Selection : Console connection](https://image.slidesharecdn.com/04-moduleoperatingconfiguringios-100917011627-phpapp01/85/04-module-operating-configuring-ios-10-320.jpg)
![27 ---- system configuration dialog ----- continue with configuration dialog ? [ yes/no] : yes at any point you may enter a question mark ‘ ?‘ for help. Use ctrl_c to abort configuration dialog at any prompt default setting are in square bra Wg_ ro_ c con0 is now available press return to get started. Wg_ ro_c> User - mode prompt Setup mode Bootup Output from the Router Unconfigured versus configured router Console](https://image.slidesharecdn.com/04-moduleoperatingconfiguringios-100917011627-phpapp01/85/04-module-operating-configuring-ios-22-320.jpg)
![27 Setup : The initial configuration Dialog Router # setup ----- system configuration dialog ----- continue with configuration dialog ? [ yes/no] : y at any point you may enter a question mark ‘?’ for help . Basic management setup configures only enough connectivity for management of the system , extended setup will ask you to configure each interface on the systems Would you like to enter basic management setup ? [ yes/no ] : n](https://image.slidesharecdn.com/04-moduleoperatingconfiguringios-100917011627-phpapp01/85/04-module-operating-configuring-ios-23-320.jpg)
![27 Setup Global Parameters Configuration global parameters: Enter host name [router ] : wg_ro_c The enable secret is a password used to protect access to privileged EXEC and configuration modes. This password after entered , because encrypted in the configuration . Enter enable secret : cisco The enable password is used when you do not specify an enable secret password , with some older software versions , and some boot images. Enter enable password : sanfran the virtual terminal password is used to protect access to the router over a network interface. Enter virtual terminal password : san jose Configure SNMP network Management ? [no] : Initial global parameters](https://image.slidesharecdn.com/04-moduleoperatingconfiguringios-100917011627-phpapp01/85/04-module-operating-configuring-ios-24-320.jpg)
![27 Setup Global Parameters (cont.) Configure LAT ? [yes ] : n configure AppleTalk? [no] : configure DECnet ? [no ] : configure IP ? [yes] : configure IGRP routing ? [ yes] :n configure RIP routing ? [no] : configure CLNS ? [ no ] : configure IPX ? [ no ] : configure Vines ? [no] : configure XNS ? [ no ] : configure Apollo ? [ no ] : Initial Protocol configurations](https://image.slidesharecdn.com/04-moduleoperatingconfiguringios-100917011627-phpapp01/85/04-module-operating-configuring-ios-25-320.jpg)
![27 Setup Interface Parameters BRI interfaces needs isdn switch _type to be configured valid switch types are : [ 0 ] none ……………. Only if you don,t want to configure BRI [ 1 ] basic _ltr ………... ltr 6 switch type for Germany [ 2 ] basic_5ess………...ATRT 5ESS switch type for the us / Canada. [ 3 ] basic_ dms 100 …. Northern DMS_100 switch type for us/ Canada [ 4 ] basic_ net 3 ………NET 3 switch type for UK and Europe [ 5 ] basic_ ni …………National ISDN switch type [ 6 ] basic ts 013……… TS013 switch type for Australia [ 7 ] ntt ………………... NTT switch type for Japan [ 8 ] vn3 …………….. Vn3 and vn4 switch types for France Choose ISDN BRI switch type [ 2 ] : Configuring interface parameters : Do you want to configure BRI0 ( BRI d_channel ) interface ? [ no ] : Do you want to configure Ethernet 0 interface ? [no ] :y Configure ip on this interface [ no ] :y IP address for this interface : 10.1.1.33 Subnet mask for this interface [255.0.0.0 ] : 255.255.255.0 Class A network is 10.0.0.0 , 24 subnet bits ; mask is /24 Do you want to configure serial 0 interface ? [ no ] :](https://image.slidesharecdn.com/04-moduleoperatingconfiguringios-100917011627-phpapp01/85/04-module-operating-configuring-ios-26-320.jpg)
![27 Setup Script Review and Use The following configuration command script was created: Hostname Rout enable secret enable password line vty 0 4 password sanjose no snmp_server: ! No appletalk no decnet rou ip routing no clns routing no ipx routing no vines rout no xns routing no apollo rout isdn switch _ty Interface BRI0 shutdown no ip address ! Interface Ethernet 0 no shutdown ip address 10.1.1.31 255.255.255.0 no map enabled ! Interface serial 0 shutdown no ip address <text omitted> end [0] Go to the IOS command prompt without saving this config. [1] Return back to the setup without saving this config. [2] Save this configuration to nvram and exit. Enter your selection [2] :](https://image.slidesharecdn.com/04-moduleoperatingconfiguringios-100917011627-phpapp01/85/04-module-operating-configuring-ios-27-320.jpg)