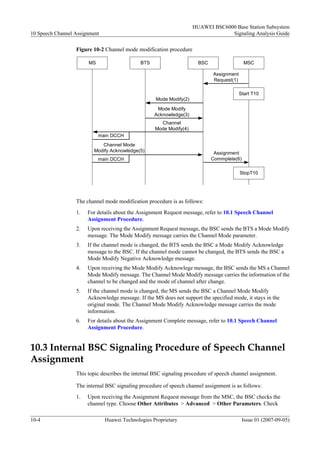
The document describes speech channel assignment and channel mode modification procedures in 3 G mobile networks. It discusses (1) how the BSC assigns TCH channels to an MS based on a service request, (2) the internal BSC signaling for channel assignment, and (3) how the BSC modifies the channel mode based on an assignment request from the MSC.