New rough
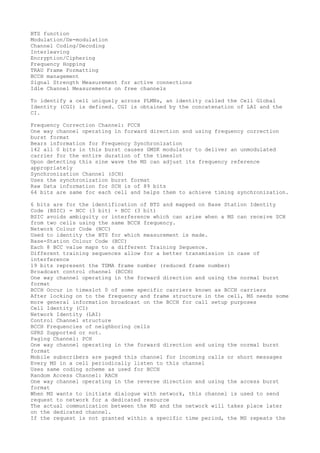
- 1. BTS function Modulation/De-modulation Channel Coding/Decoding Interleaving Encryption/Ciphering Frequency Hopping TRAU Frame Formatting BCCH management Signal Strength Measurement for active connections Idle Channel Measurements on free channels To identify a cell uniquely across PLMNs, an identity called the Cell Global Identity (CGI) is defined. CGI is obtained by the concatenation of LAI and the CI. Frequency Correction Channel: FCCH One way channel operating in forward direction and using frequency correction burst format Bears information for Frequency Synchronization 142 all 0 bits in this burst causes GMSK modulator to deliver an unmodulated carrier for the entire duration of the timeslot Upon detecting this sine wave the MS can adjust its frequency reference appropriately Synchronization Channel (SCH) Uses the synchronization burst format Raw Data information for SCH is of 89 bits 64 bits are same for each cell and helps them to achieve timing synchronization. 6 bits are for the identification of BTS and mapped on Base Station Identity Code (BSIC) = NCC (3 bit) + BCC (3 bit) BSIC avoids ambiguity or interference which can arise when a MS can receive SCH from two cells using the same BCCH frequency. Network Colour Code (NCC) Used to identity the BTS for which measurement is made. Base-Station Colour Code (BCC) Each 8 BCC value maps to a different Training Sequence. Different training sequences allow for a better transmission in case of interference 19 bits represent the TDMA frame number (reduced frame number) Broadcast control channel (BCCH) One way channel operating in the forward direction and using the normal burst format BCCH Occur in timeslot 0 of some specific carriers known as BCCH carriers After locking on to the frequency and frame structure in the cell, MS needs some more general information broadcast on the BCCH for call setup purposes Cell Identity (CI) Network Identity (LAI) Control Channel structure BCCH Frequencies of neighboring cells GPRS Supported or not. Paging Channel: PCH One way channel operating in the forward direction and using the normal burst format Mobile subscribers are paged this channel for incoming calls or short messages Every MS in a cell periodically listen to this channel Uses same coding scheme as used for BCCH Random Access Channel: RACH One way channel operating in the reverse direction and using the access burst format When MS wants to initiate dialogue with network, this channel is used to send request to network for a dedicated resource The actual communication between the MS and the network will takes place later on the dedicated channel. If the request is not granted within a specific time period, the MS repeats the
- 2. request on RACH Access Grant Channel: AGCH AGCH is a one way channel operating in forward direction and using the normal burst format In response to requests from different MS on RACH, the network allocates a specific dedicated signaling channel (SDCCH) against each request for further communication. The response to the request is sent on AGCH. Uses same coding scheme as used for BCCH Stand-alone Dedicated Control Channel: SDCCH Two way channel using normal burst format As per the allocation conveyed over the AGCH, both the MS & the BTS switch over to the assigned SDCCH for a further communication The Following tasks require the use of SDCCH Location Updates Call Setup SMS Uses the same coding scheme as used by BCCH Slow Associated Control Channel: SACCH Two way channel using normal burst format SACCH is always associated with TCH or SDCCH When associated with a TCH, the SACCH occurs in 12 or 25 frame of each 26-frame multi frame Each message comprises of 456 bits so 4 multi frames are required to transmit a message Since a 26-frame multiframe requires 120ms, a SAACH message over 4 multi-frame requires 480ms. Thus, power control that is linked to SAACH exchanges is hindered by the low rates of SAACH exchange. (But then, SAACH was meant to be slow!) Used to convey the periodic carrier-signal strength measurements to the network While an MS is busy on a call over a traffic channel (TCH) or in communication with MSC on the SDCCH, MS takes periodic carrier-signal strength measurements on own base station & neighboring base stations. Based on the analysis of measurements taken by BTS & the MS, the BSC conveys information on timing advance & MS transmitter power control Uses the same coding scheme as used by BCCH Fast Associated Control Channel: FACCH FACCH is a two way channel using normal burst format FACCH can be associated with SDCCH or TCH FACCH works on the principle of stealing The burst of speech is replaced by FACCH signaling FACCH is used to convey Handover information Uses the same coding scheme as used by BCCH Full Rate Traffic Channel This channel carries information at rate of 22.8 Kbps Half Rate Traffic Channel This channel carries information at rate of 11.4 Kbps Enhanced Full Rate Speech GMSK Adaptive Multi Rate (Half Rate and Full Rate) Circuit Switched Data (Transparent): 600/1200, 2400, 4800, 9600, 14400. Circuit Switched Data (Non-transparent): 9600, 14400. Group 3 Fax: 2400, 4800, 9600, 14400. CS 1 to 4 MCS 1 to 9 High-Speed Circuit Switched Data (HSCSD) for 9.6/14.4 kbps Enhanced Circuit Switched Data 28.8/32.0/43.2 Kbps per TS Generally two configurations are mainly used Separate SDCCH: FCCH + SCH + BCCH + CCCH Addresses a channel configuration in which no SDCCH are available on TS 0. In this case SDCCH sub channels are defined on TS 1 Rest of the TS are used by Traffic channels Combined SDCCH: FCCH + SCH + BCCH + CCCH + SDCCH/4
- 3. Addresses a channel configuration in which all control channels are assigned to TS 0 In this case TS1 is also available for Traffic channels The downlink direction of TS 0 of the BCCH-TRX is used by various channels. FCCH SCH BCCH Four SDCCH sub channels (optional); CCCH This use is possible because the logical channels can time-share TS 0 in different TDMA frames of 51 frame Multi frame Multiplexing of FCCH + SCH + BCCH + CCCH on TS 0 of radio frequency C0 (51 Frame Multiframe) Cycle of 51 TDMA frame (0-50), The structure is repeated after IDLE frame It contains one block of 4 frames for BCCH and 9 Blocks of 4 frames for CCCH (AGCH/PCH) Referred to as OMUSIG channel There is one OMUSIG channel per BTS (typically 16 to 64Kbps). BSC controls operations of the whole BTS through this channel. There is O&M SW running on BTS that handles all command on O&M channel. OMUSIG uses LAPD as link layer protocol. Typical operations include: Initialization Configuration SW Download Alarm handling and Fault reporting Block and Reset Loop Test and other test operations Referred to as TRXSIG channel There is one TRXSIG channel per TRX (typically 16 Kbps). All mobile signalling (including RR signalling) is carried over TRXSIG channel. There is RR SW running on each TRX that handles all command on TRX signaling channel. TRXSIG uses LAPD as link layer protocol. Typical operations is explained in subsequent slides. Apart from the OMUSIG and TRXSIG channels, there are traffic channels for each Timeslot of a TRX. Thus, if there are N TRX, then there are 8N traffic channels, each of 16Kbps link speed. A host of traffic types can be carried, each with different channel coding. The following are some of the basic traffic channel types: Full Rate Half Rate Speech The traffic channels are carried over either TRAU frame format or GPRS Layer 1 frame format. These frame formats define how BTS and BSC exchange stream of information at layer 1. For example, while 13Kbps is required for carrying user traffic on Abis, the TRAU frame is allocated 3Kbps. Thus, there is bandwidth for signaling traffic. Note: There is no LAPD for traffic channels. LAPD provides reliable delivery and is not feasible for user traffic. PAGE119 At L3, Abis Interface defines a set of sub-procedures (48.058) At L2, the LAPD protocol is followed based on Q.931(48.056) At L1, the E1 PCM structure is followed The TRXSIG Layer 3 Signaling has four basic set of procedures: Common Channel Management Dedicated Channel Management
- 4. Radio Link Management TRX Management Refer 3GPP 48.058 for details Common Channel Management includes procedures for enabling mobile to obtain dedicated channels (I.e. SDCCH and TCH) for communication. Till such state is reached, the communication takes place through RACH and AGCH. The procedures belonging to this category include: System Information Broadcast (over BCCH) Paging (over PCH) Initial Channel Request (via RACH) Immediate Assignment (over AGCH) Note: The logical channels shown in brackets do not apply for Abis. It only indicates for example that Paging message received over Abis is sent over PCH channel or random access received over RACH is relayed over Abis. Dedicated Channel Management includes procedures for managing the state of dedicated channels (I.e. SDCCH and TCH). The procedures belonging to this category include: Channel Activation/release Handover support Mode modify Power Control Measurement Reporting Ciphering Control Radio Link Management procedures relay the actions on air interface to BSC over Abis or receive instructions from BSC to trigger actions over air interface. The procedures belonging to this category include: Request/Indication for Link Establishment Request/Indication for Link Release Transparent data transfer from MS to BSC Transparent data transfer from BSC to MS TRX Management procedures include few other procedures related to measurement handling. The procedures belonging to this category include: Interference on idle channels Note: Measurement of interference on idle channels is different from measurements for dedicated channels. The latter form part of dedicated channel handling procedures. Some form of flow control Error control LAPD frame format is specified by ITU Q.920 and Q.921. 3GPP TS 48.056 adapts this to provide signaling on Abis interface. LAPD provides reliable data link layer for information transfer. Option is available to send relatively less important messages in un- acknowledged mode. The mobile sees various protocol layers: Layer 1: GSM Physical layer with BTS (already covered) Layer 2: LAPDm layer with BTS Layer 3a: RR layer with BSC Layer 3b: MM/CC layer with MSC Based on LAPD protocol, but adapted for mobile environment. That is why it is referred to as modified LAPD or simply LAPDm. The modifications from LAPD are as follows: There is no Frame Check This functionality is provided by channel coding/interleaving There is no start and end flag Frame delineation is done by use of burst The first set of messages (I.e. SABME) can carry layer 3 data to save air interface resources. LAPDm carries ‘maximum‘ message size of 18 to 23bytes. LAPDm is defined in 3GPP TS 04.05 and 04.06 There are different types of LAPDm format: A-format: A frame in the A-format generally can be sent on any DCCH in both
- 5. directions, uplink and downlink. The A-format frame is sent as a fill frame when no payload is available on an active connection. B-format: The B-format is used on the Air-interface to transport the actual signaling data; hence, every DCCH and every ACCH use this format. If the information to be transmitted requires less space, this space has to be filled with fill-in octets. Bbis format: Most simple one is the Bbis in which there is no header/trailer (just the information field). This is used for BCCH, PCH, and AGCH. For this, addressing is not necessary, since these are CCCHs, in which addressing is not required. In contrast to the DCCH, the CCCH transports only point-to-multipoint messages. Note: For CCCH, the LAPDm is effectively short-circuited (I.e. no LAPDm). Note: For traffic channels, there is no LAPDm. Important LAPDm parameters: SAPI: 0 for RR, MM and CC 3 for SMS and SS Um Protocols: L3 protocol At L3, the protocols residing on Um interface are: Radio Resource Protocol Mobility Management Protocol Call Control Supplementary Service Short Message Service The message type is identified by the Protocol Discriminator. L3 Um Protocols: Radio Resource Management The RR protocol is specified in 04.18 The messages are processed in the BSS or even in the MSC. The RR protocol is required for managing physical and logical channels of GSM Air interface Important procedures are: Channel Request Procedures System Information Broadcast Procedures Paging Procedures Cipher mode Handling Handover Related Procedures Measurement Reports Some of these procedures are explained in Procedure section. L3 Um Protocols: Mobility Management The MM protocol is specified in 24.008 The MM messages are processed between MS and MSC/VLR. The MM protocol is required for managing terminal mobility, temporary identity management, authentication, etc. Important procedures are: IMSI Attach/Location Updated IMSI Detach Authentication Request/Response Identity Request TMSI Re-allocation Service Request L3 Um Protocols: Call Control The CC protocol is specified in 24.008 The CC messages are processed between MS and MSC/VLR. The CC protocol is required for managing calls. Important procedures are: Setup Call Proceeding Alerting Connect Release
- 6. Release Complete L3 Um Protocols: SS and SMS The SS and SMS related L3 protocol is specified in 24.010/011 These messages are processed between MS and MSC/VLR. Important procedures are: Register/Facility for SS procedure Similarly, there are procedures for sending/receiving SMS A Interface Protocol: BSSAP Used between MSC and BSS The BSS Application Part (BSSAP) is split into two sub application parts, these are: BSS Management Application Part (BSSMAP) Supports the procedures between MSC and BSS for call handling and resource management. For e.g. Paging, Reset, etc. Direct Transfer Application Part (DTAP). This includes the MM and CC messages as discussed earlier. These messages are transparent to the BSS Defined in 3GPP TS 08.08 A Interface Protocol: BSSmAP Used between MSC and BSS Defined in 3GPP TS 08.08 Important procedures include Assignment Handover Reset Cipher Mode Others