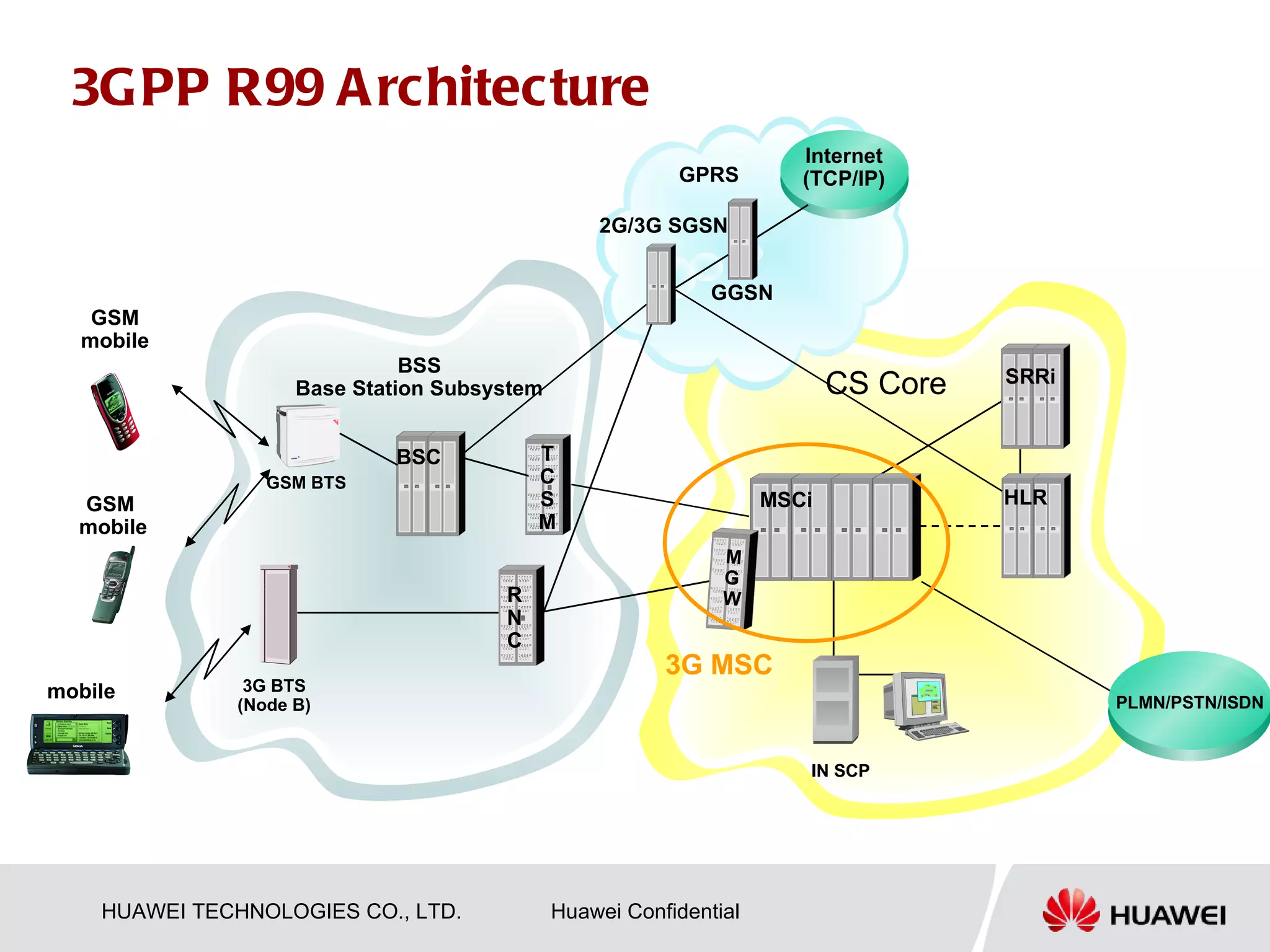
This document describes the evolution of 2G and 3G mobile network architectures. It shows:
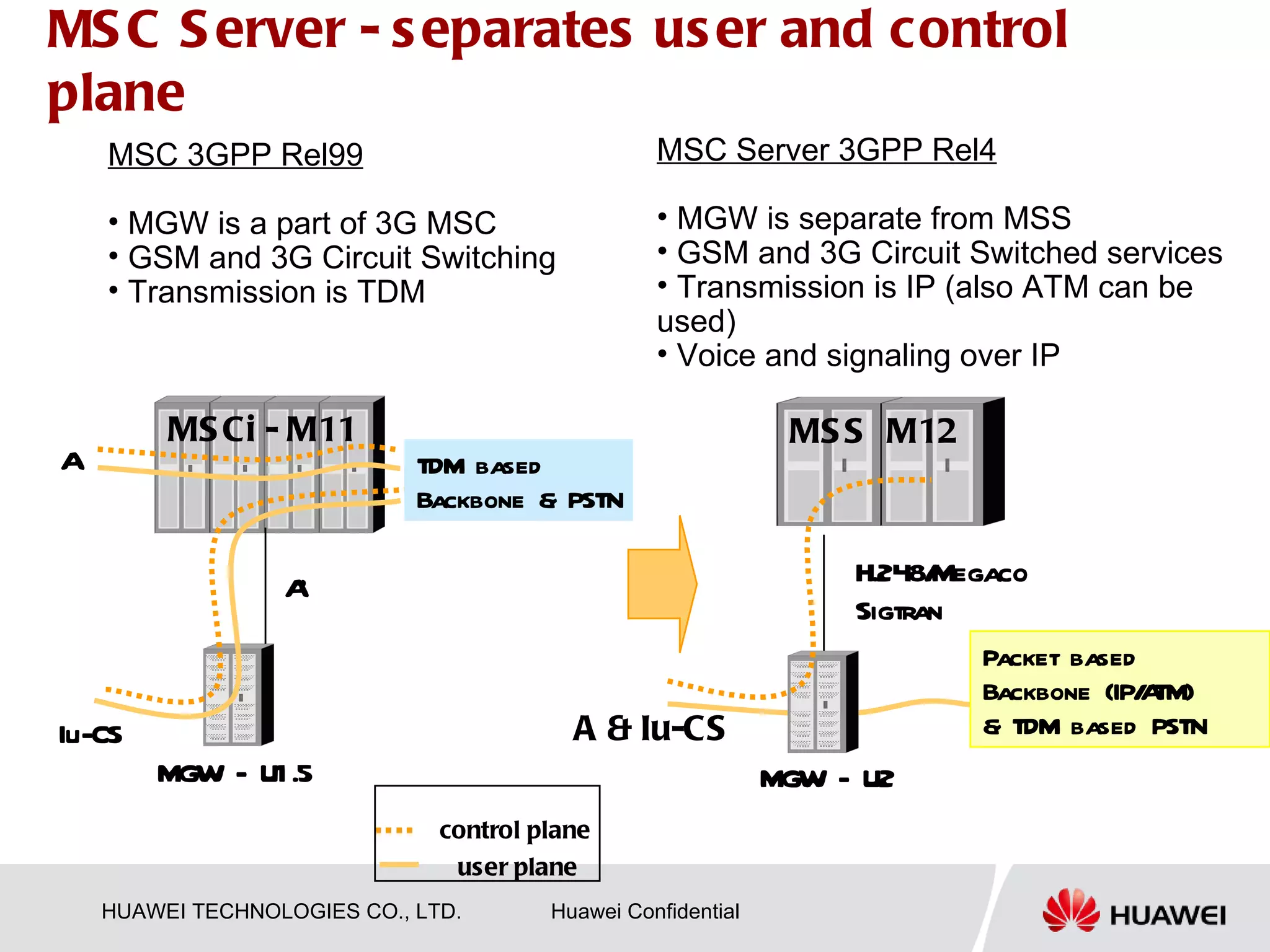
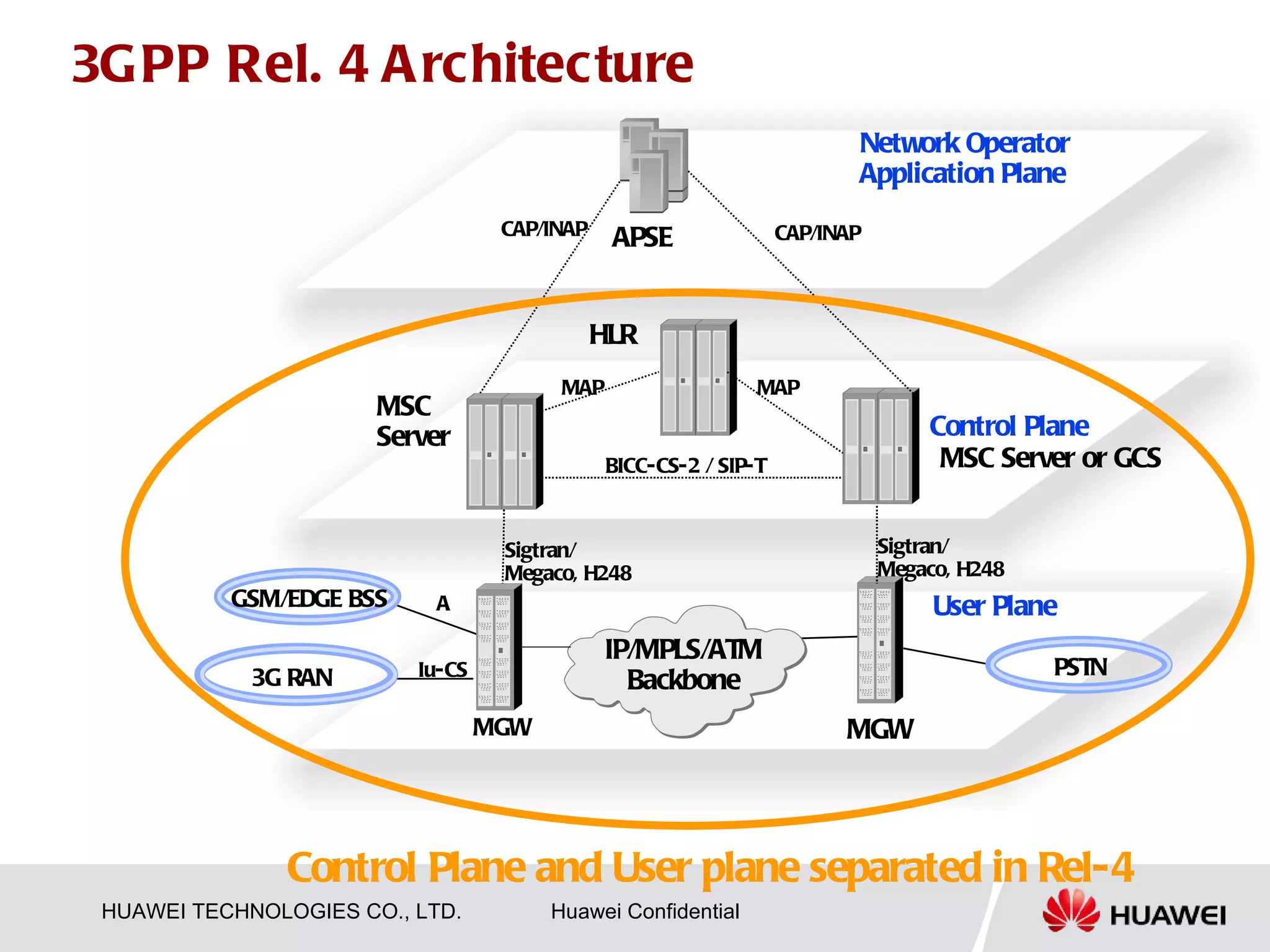
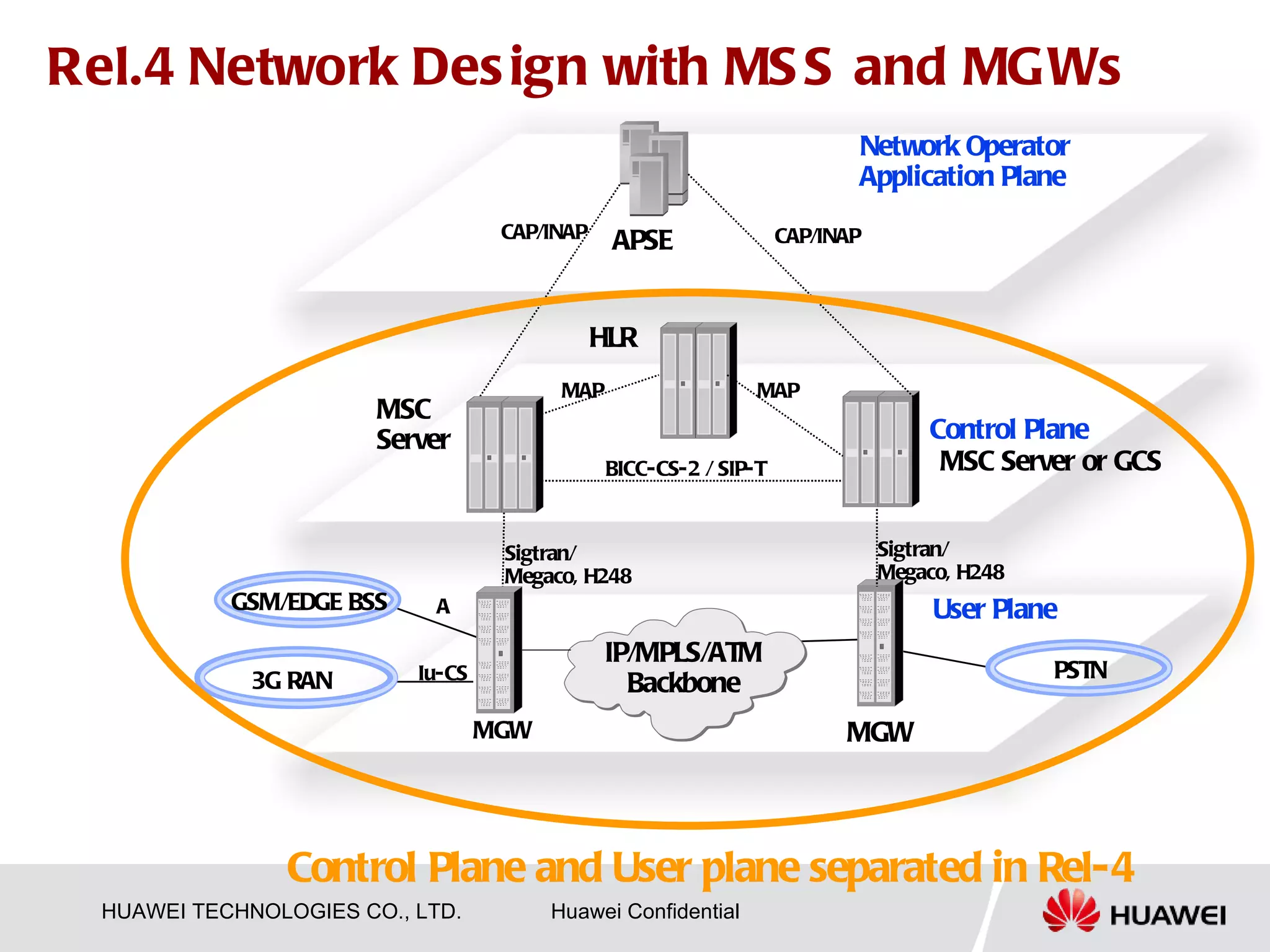
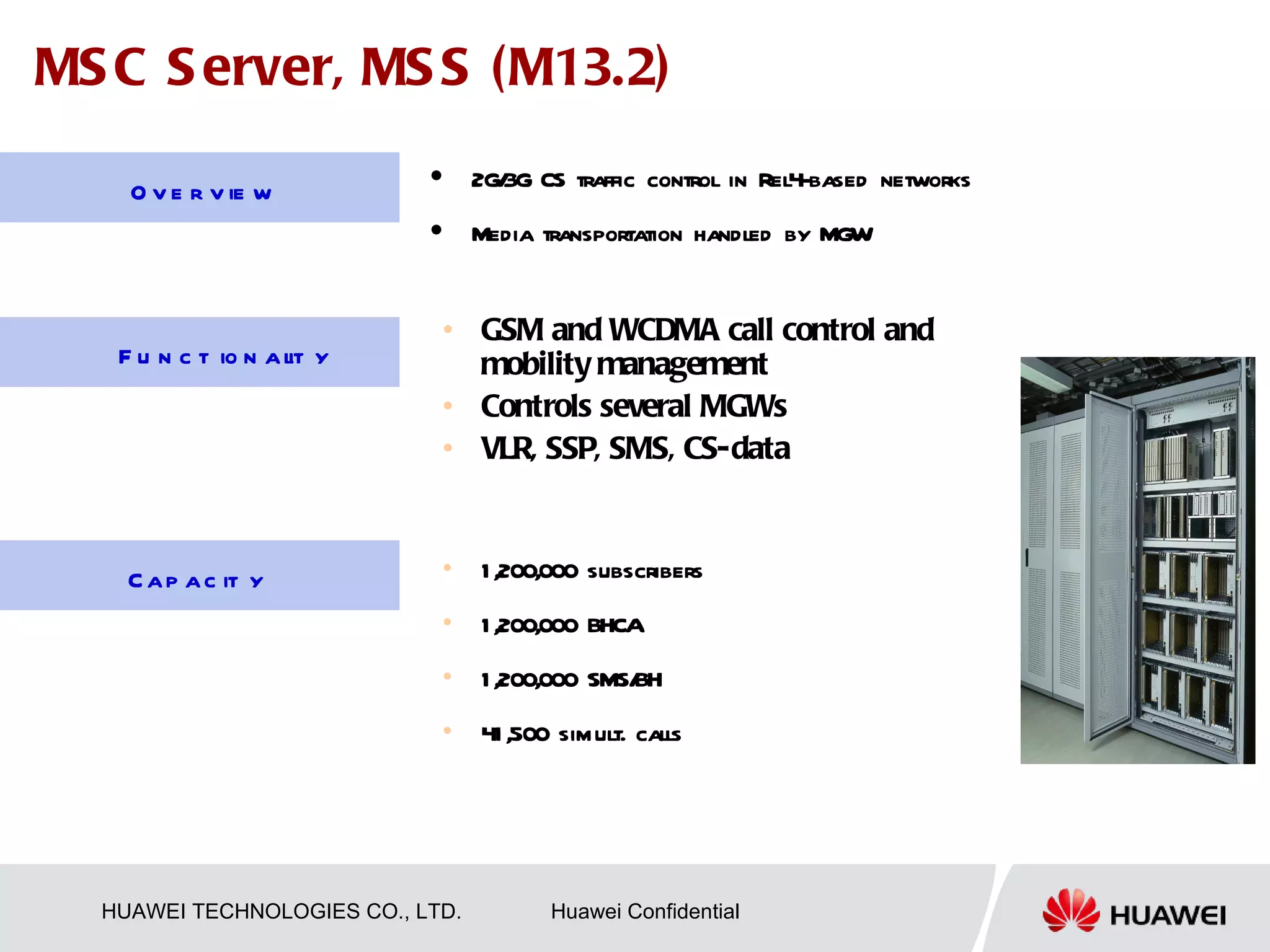
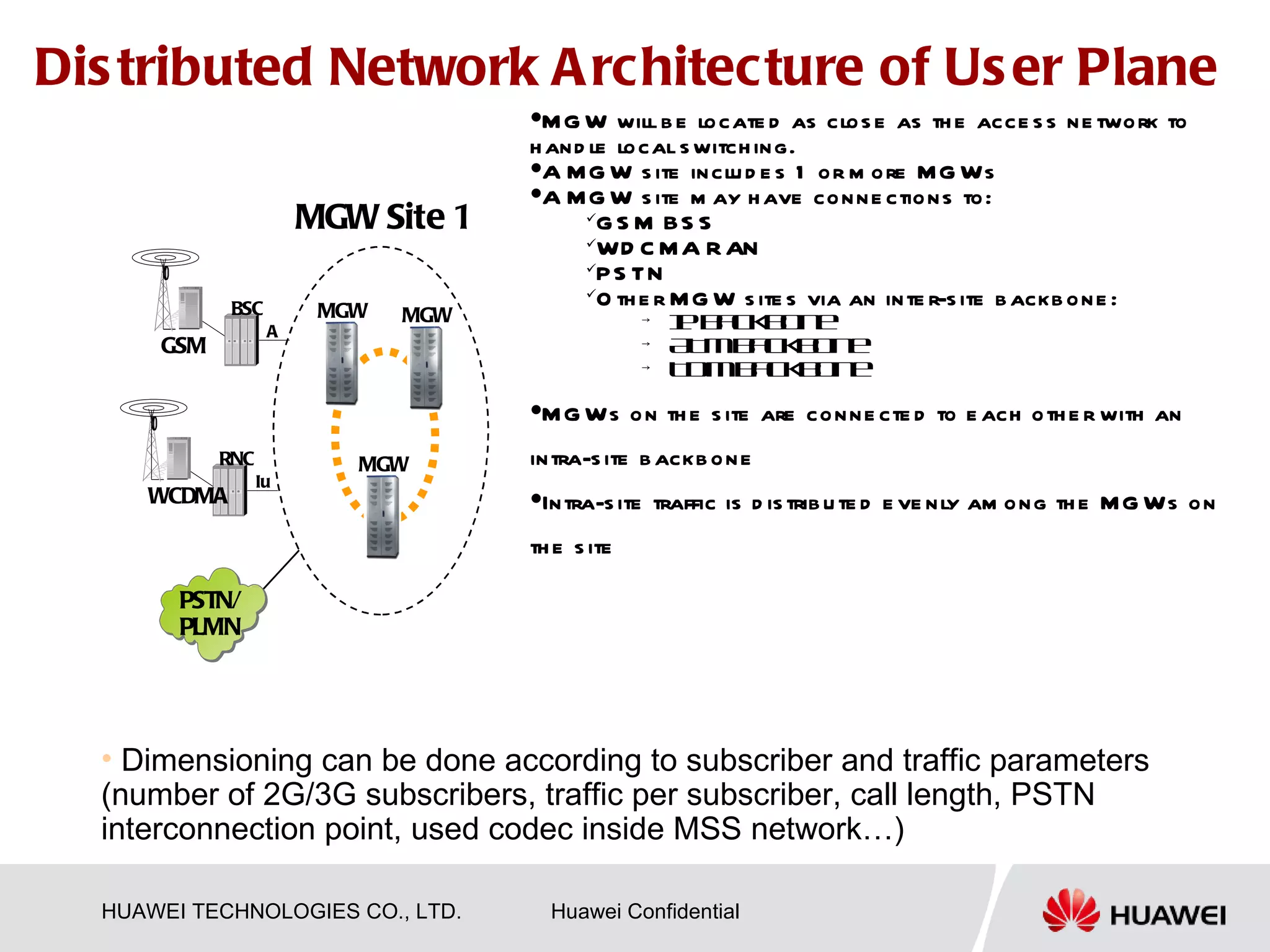
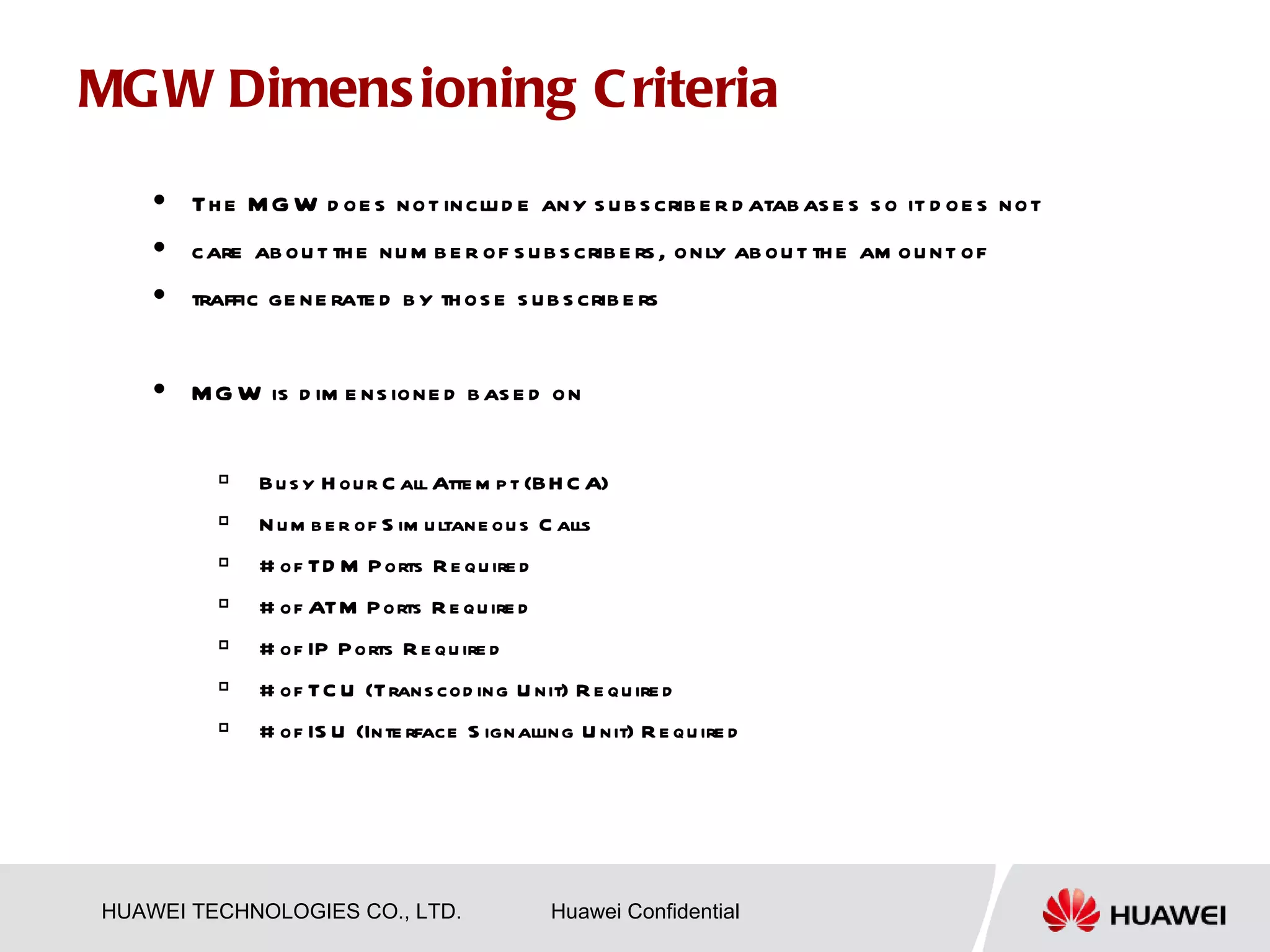
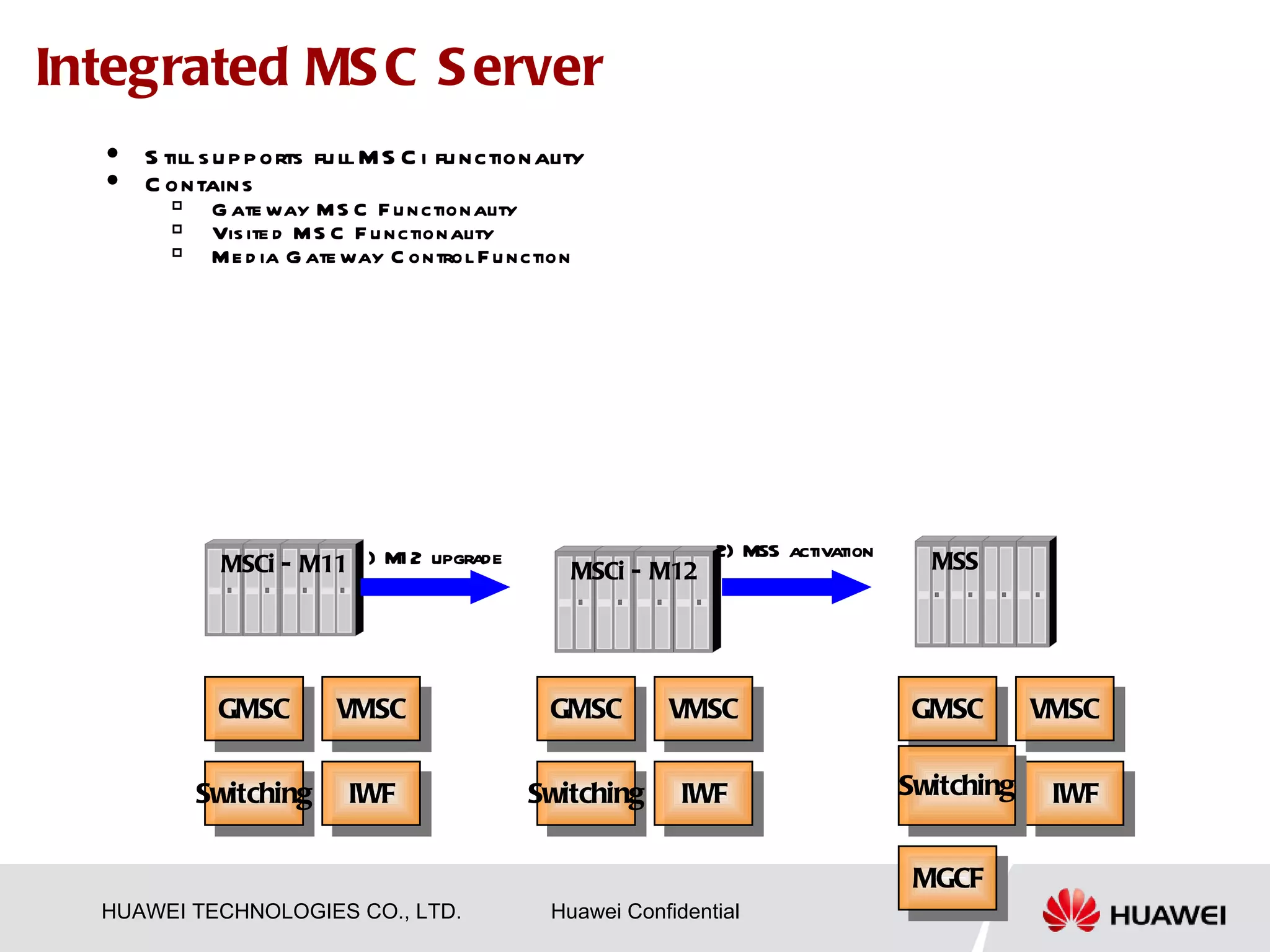
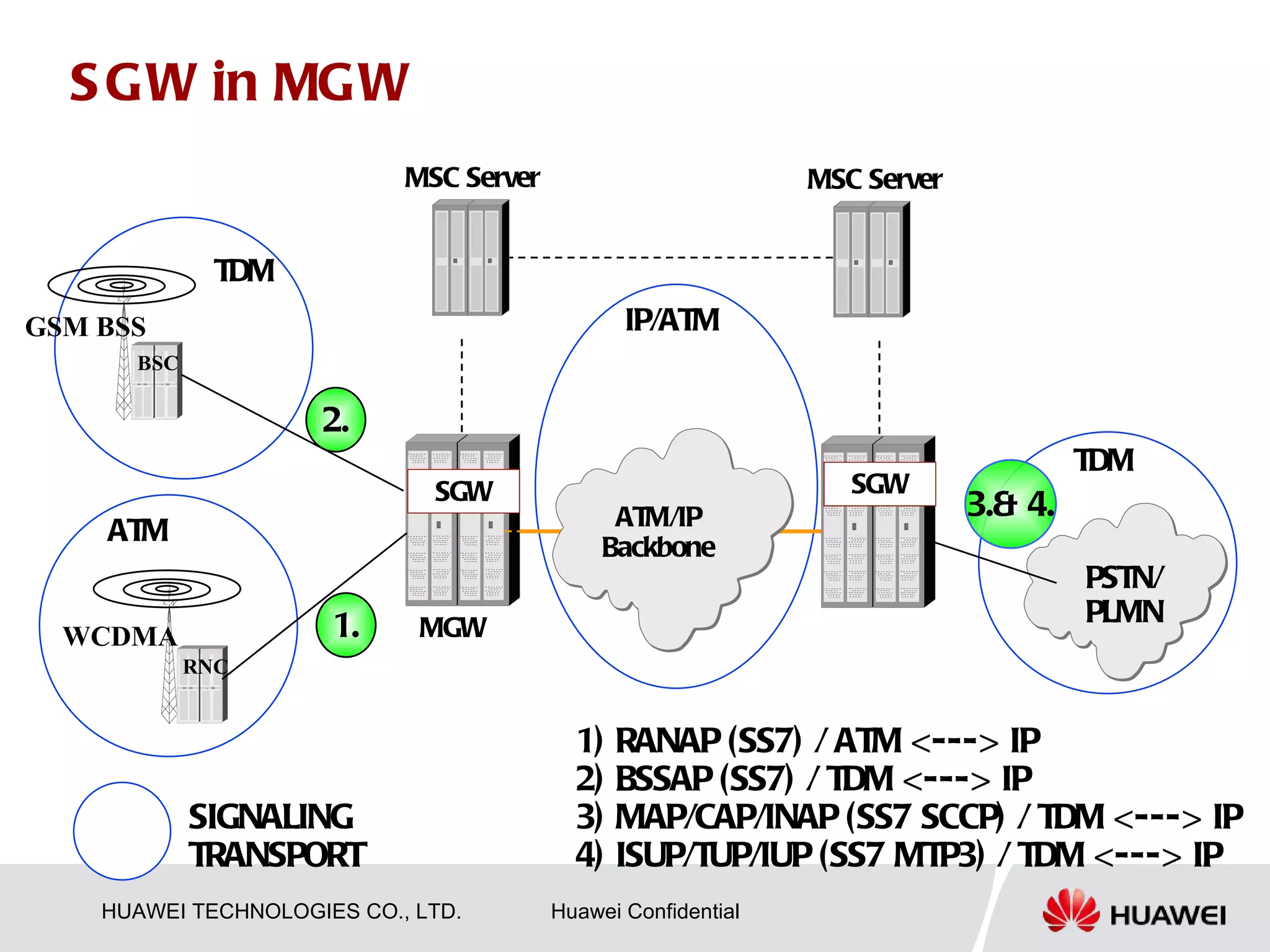
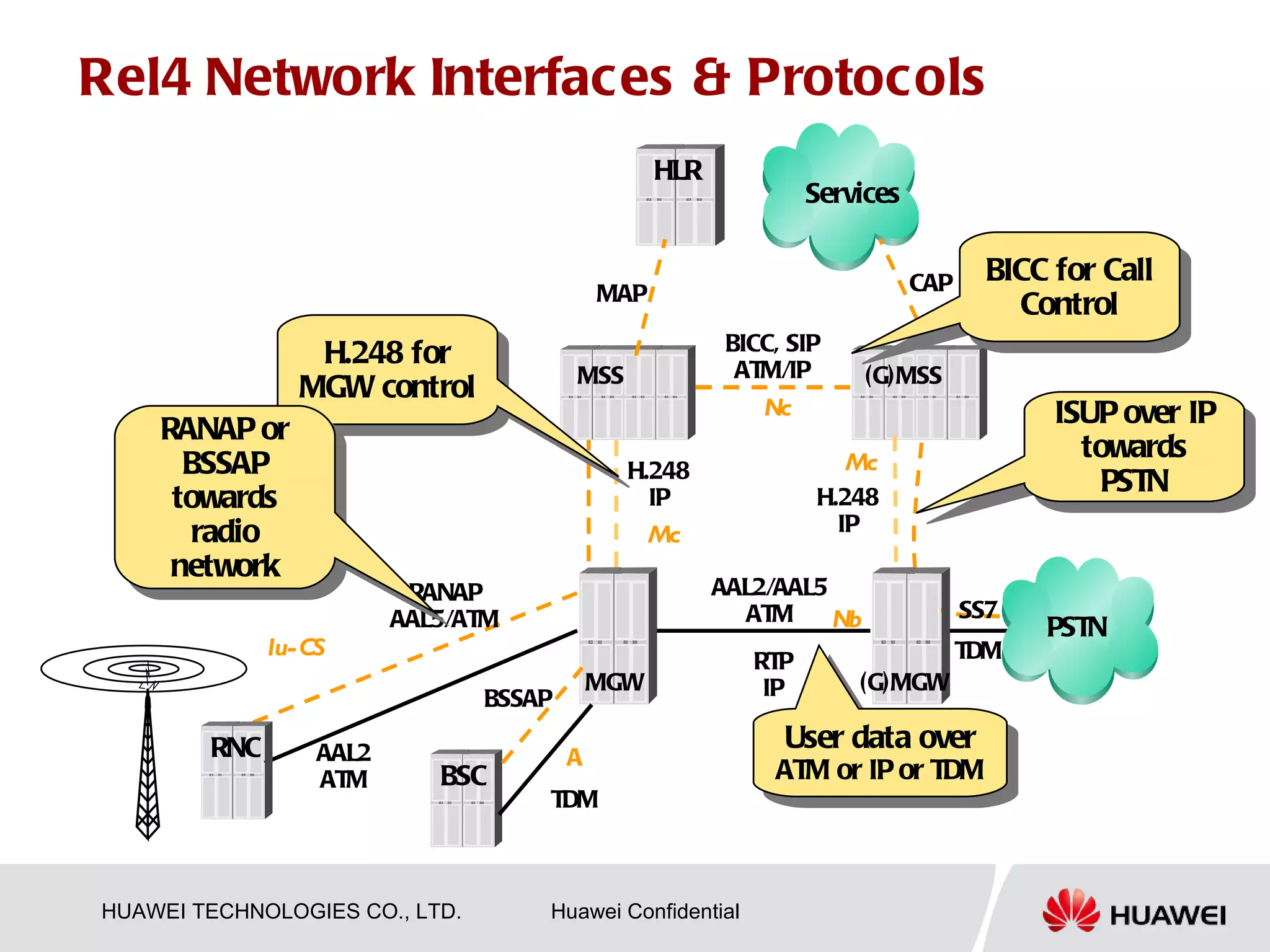
1) The separation of the control plane and user plane in 3GPP Release 4, with the MSC Server handling signaling and Media Gateways handling transmission.
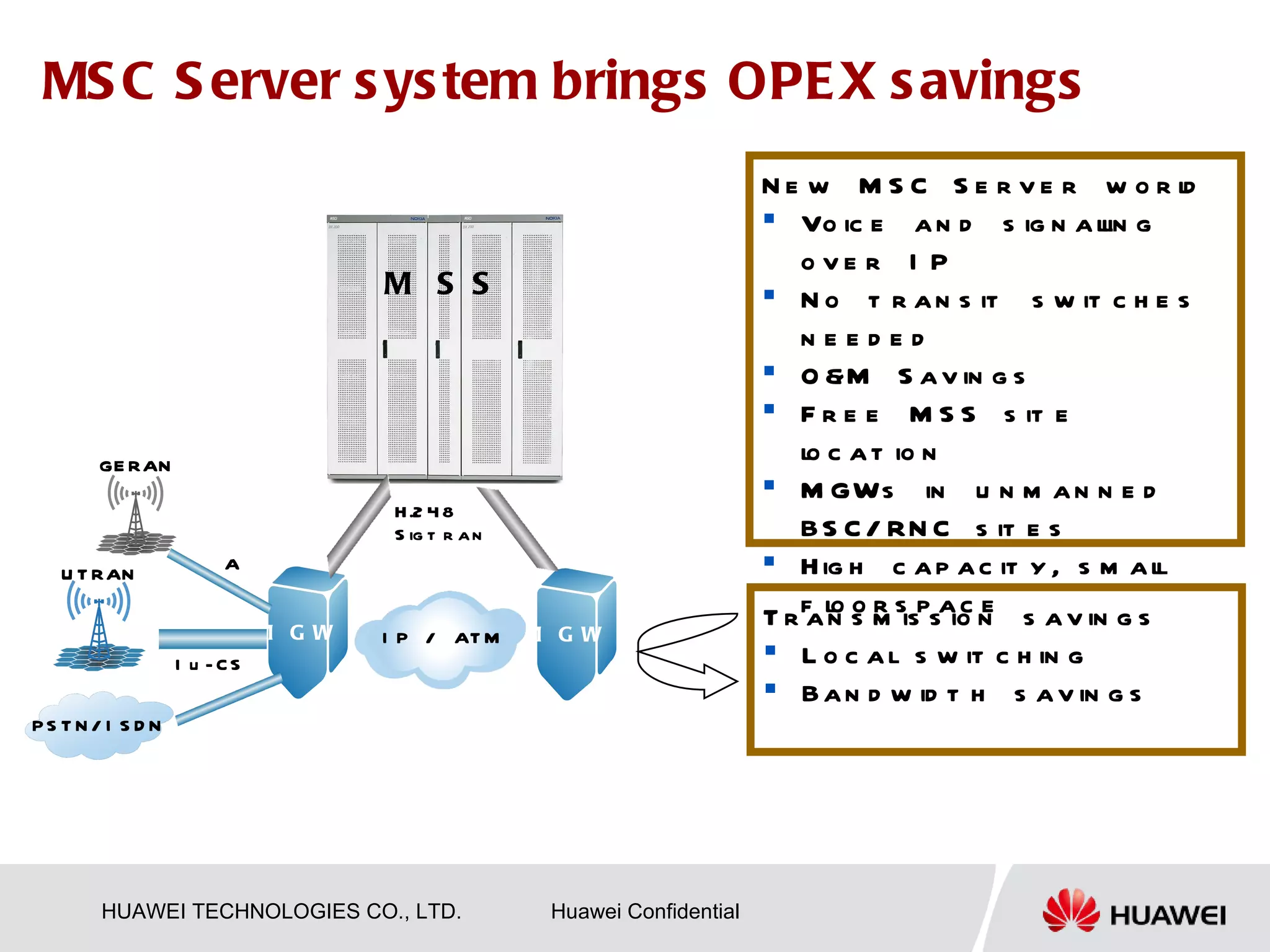
2) How the MSC Server system provides operational expenditure savings by moving voice and signaling transmission to IP networks and separating equipment for more flexible siting.
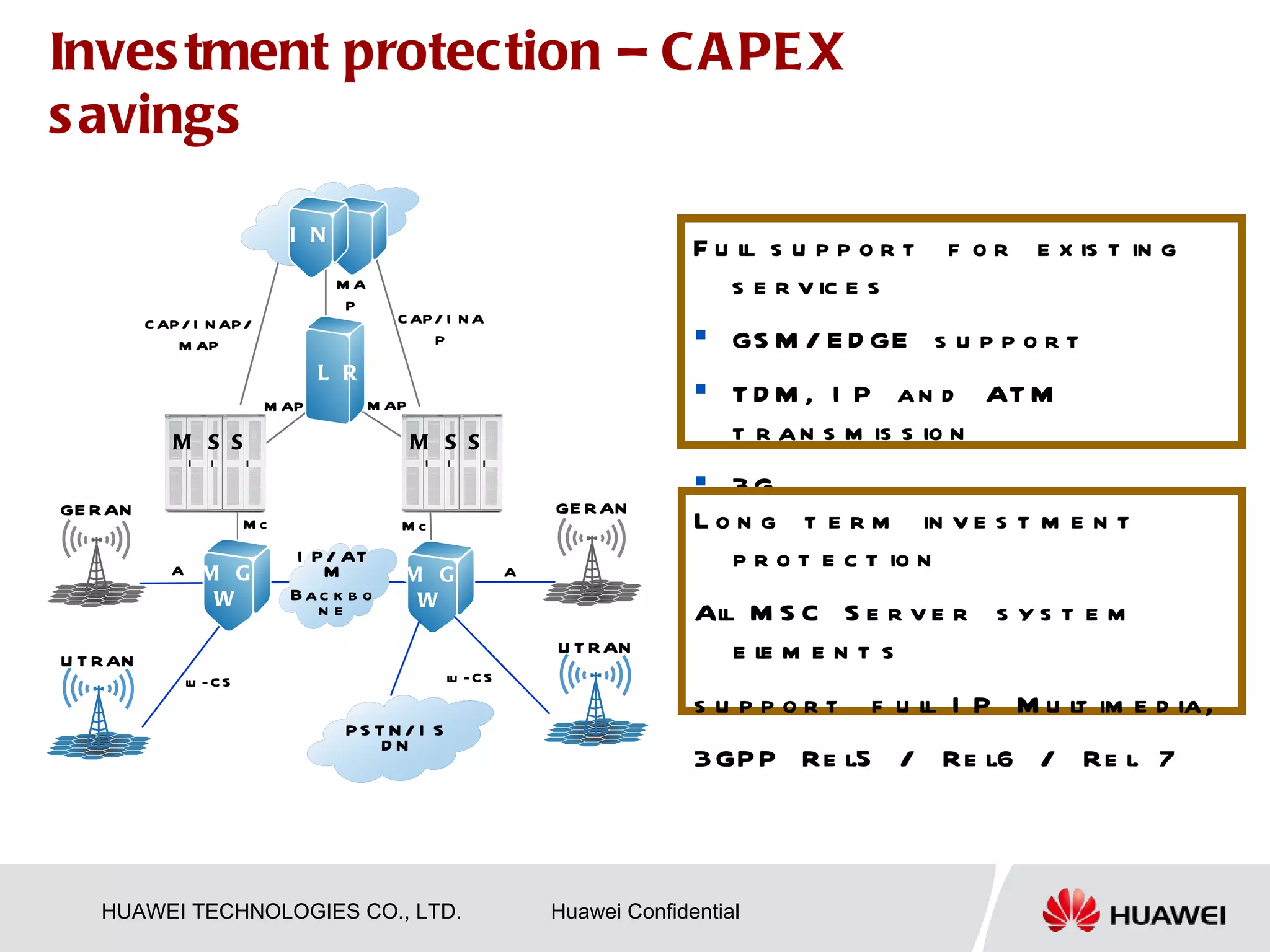
3) How the MSC Server system allows investment protection by supporting existing services on GSM, EDGE, 3G and TDM, IP, and ATM transmission networks.