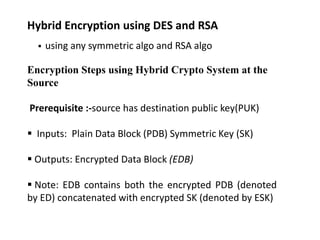
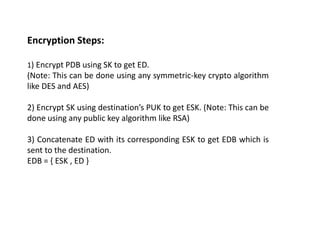
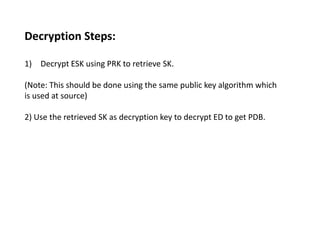
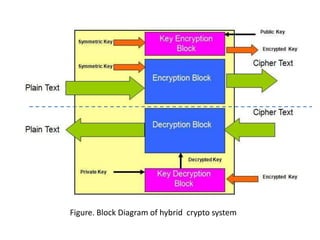
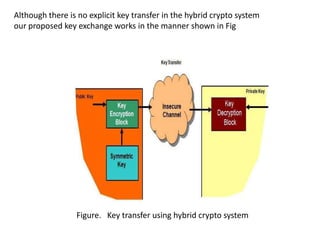
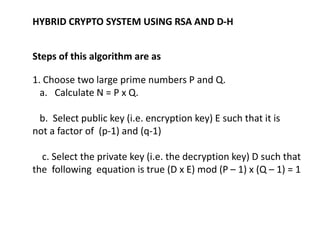
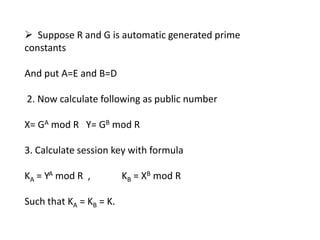
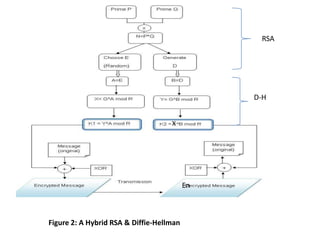
This document summarizes a technical seminar on hybrid encryption technology. Hybrid encryption combines both symmetric and asymmetric encryption algorithms to provide increased security. The seminar overviewed hybrid encryption using DES and RSA, as well as RSA and Diffie-Hellman. It also discussed how hybrid encryption can be applied to electronic documents, such as with Adobe Acrobat, to encrypt a document symmetrically but the symmetric key asymmetrically for different recipients. The seminar concluded that hybrid encryption removes the key distribution problem and increases security over only using a single cryptographic algorithm.