This document provides an overview of smart cards, including:
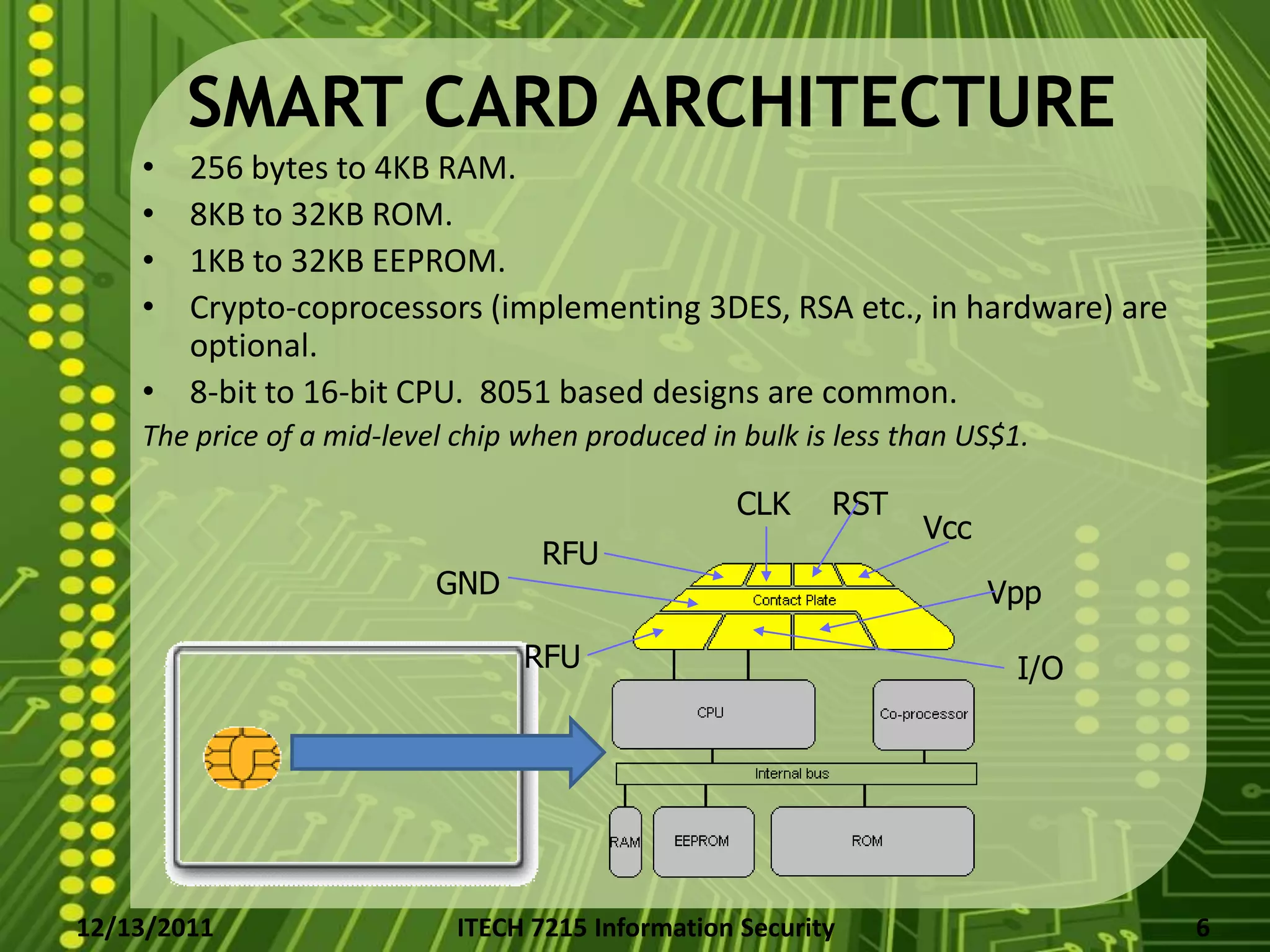
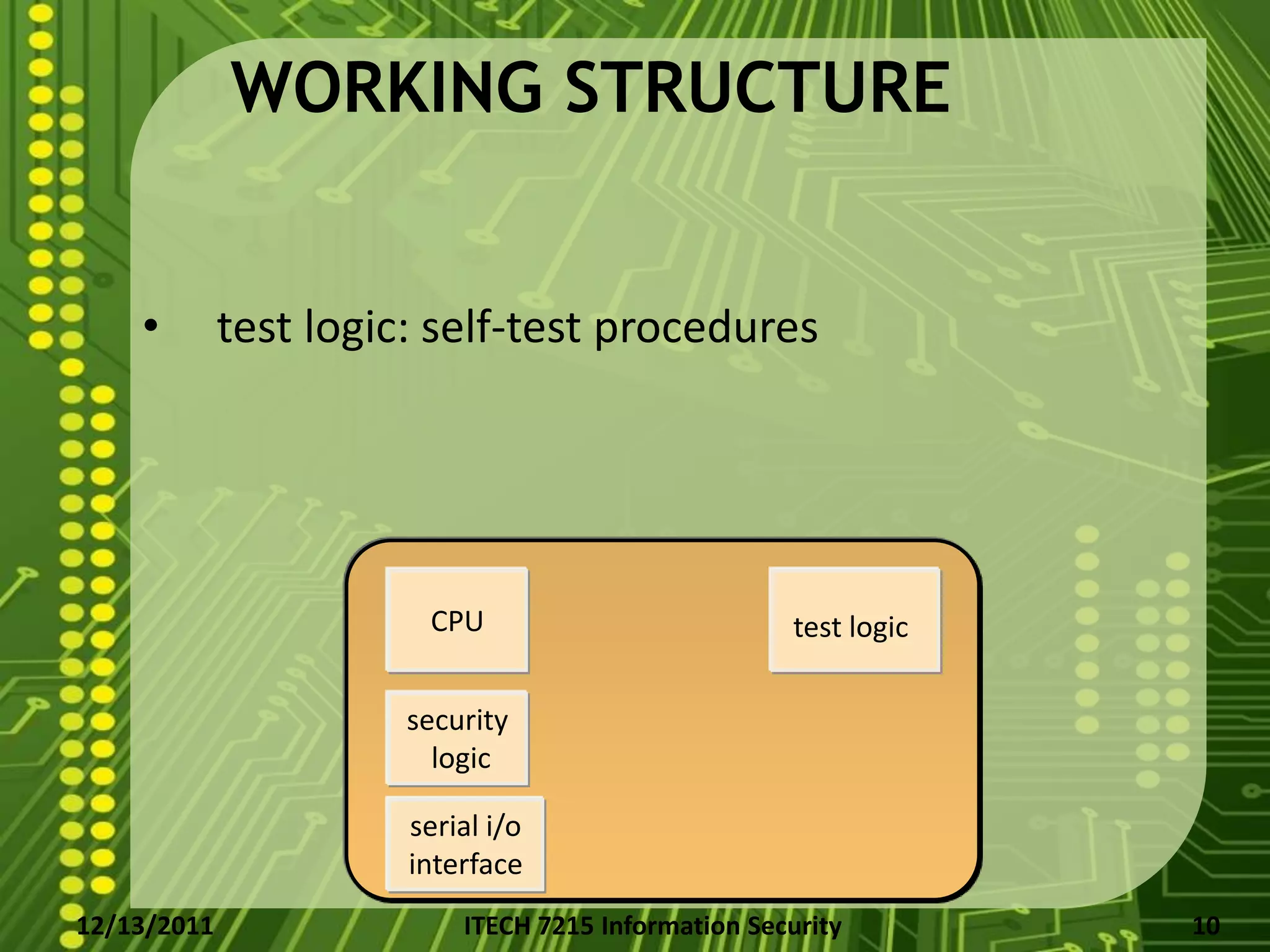
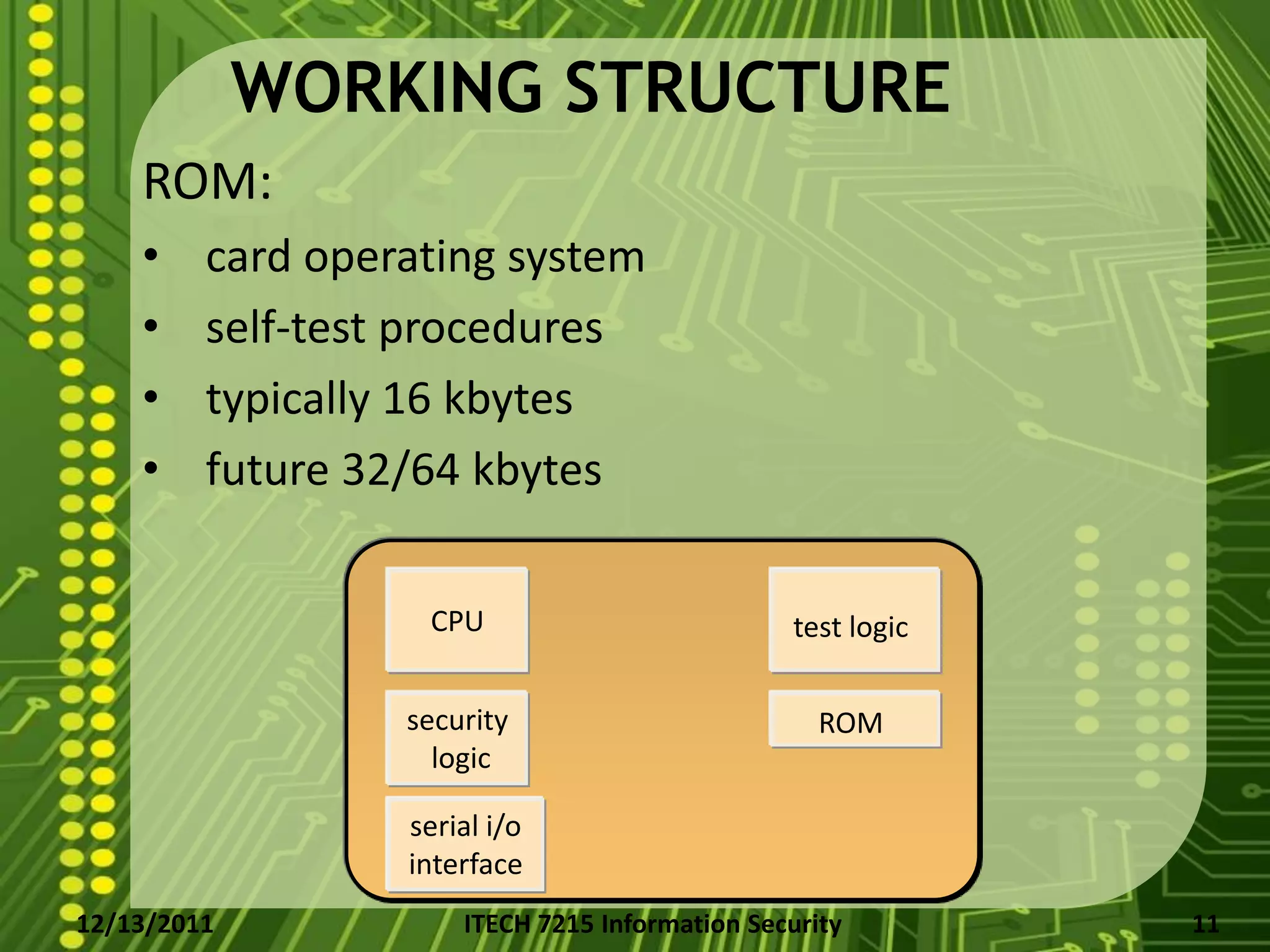
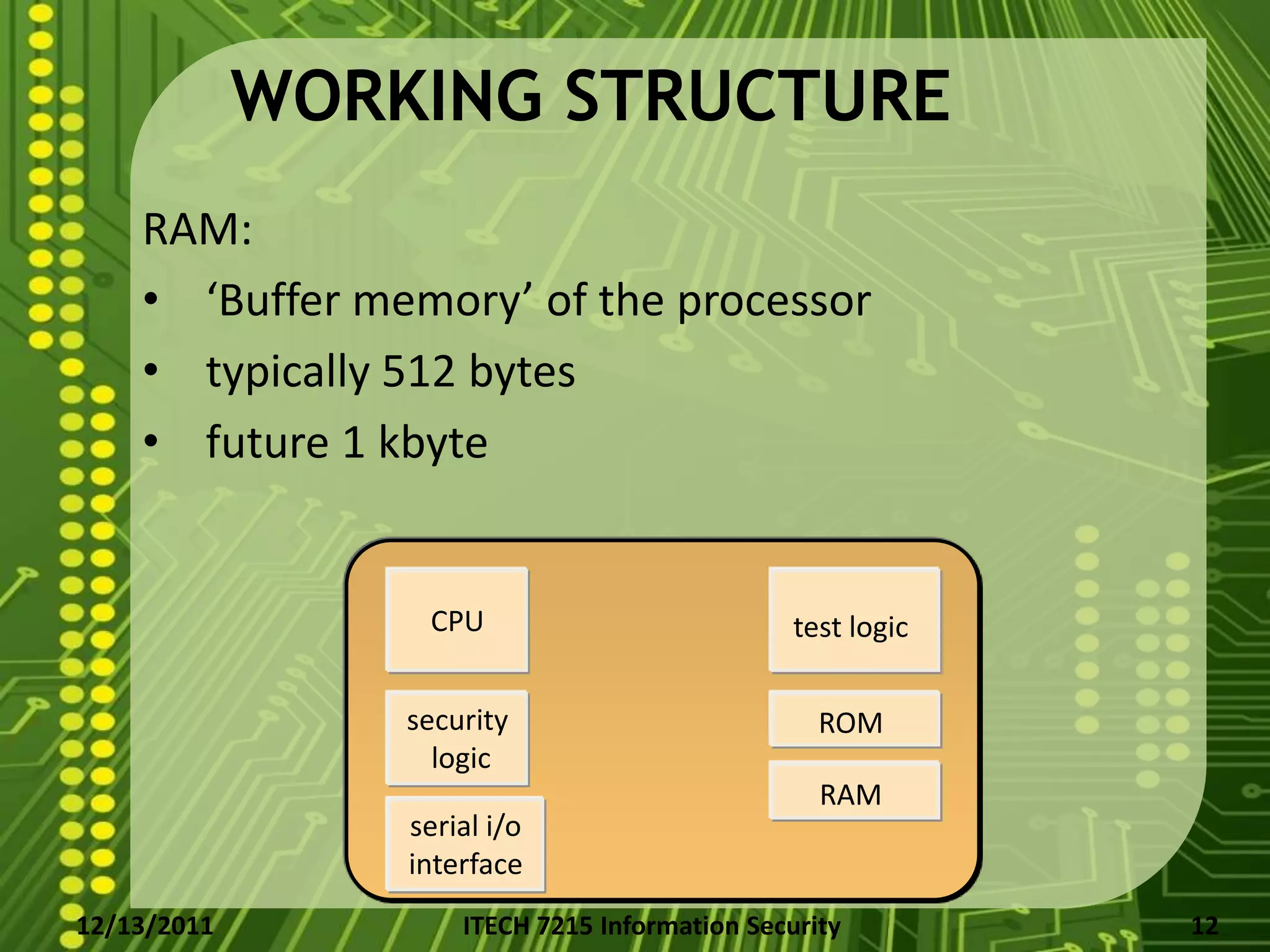
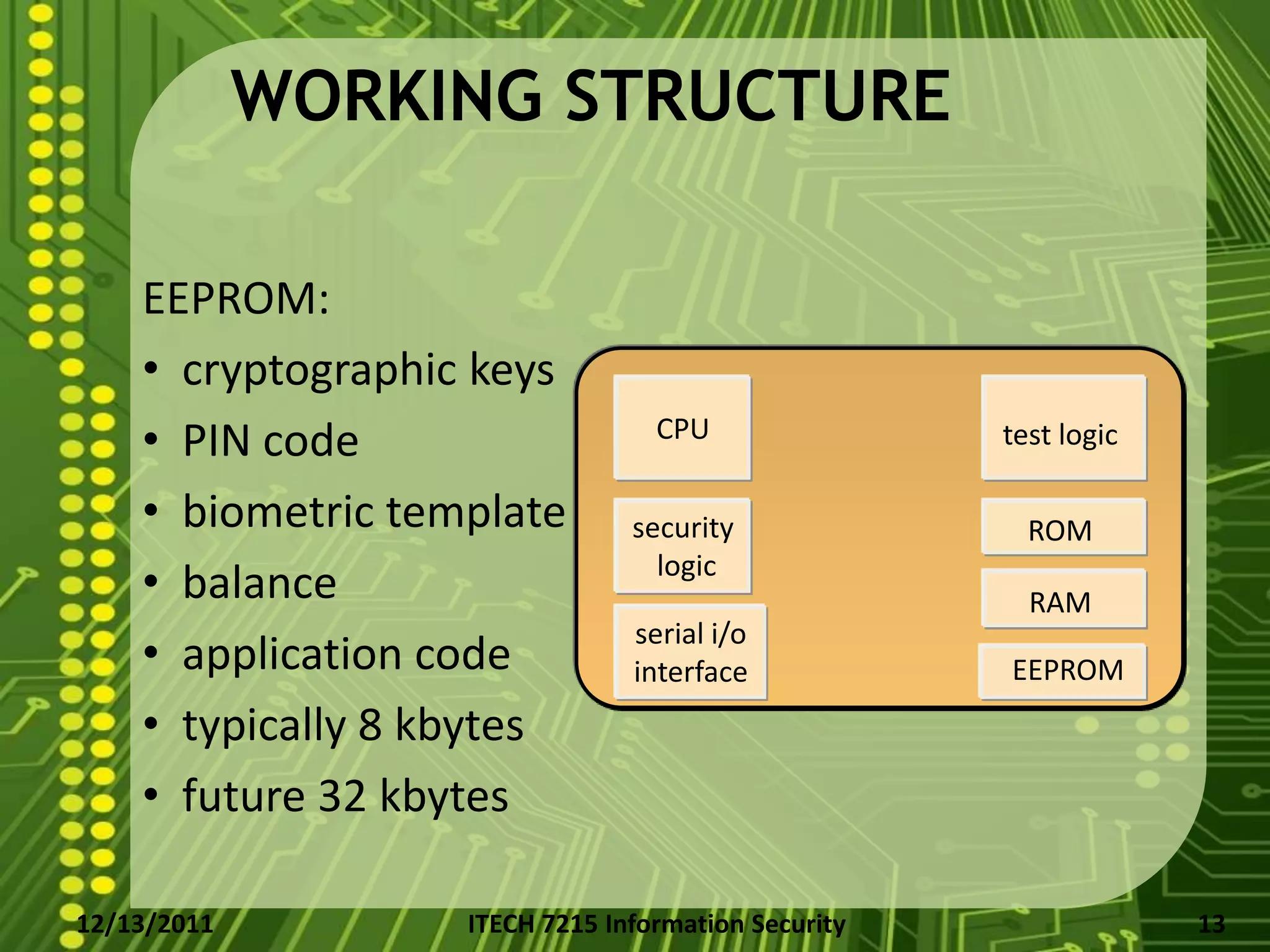
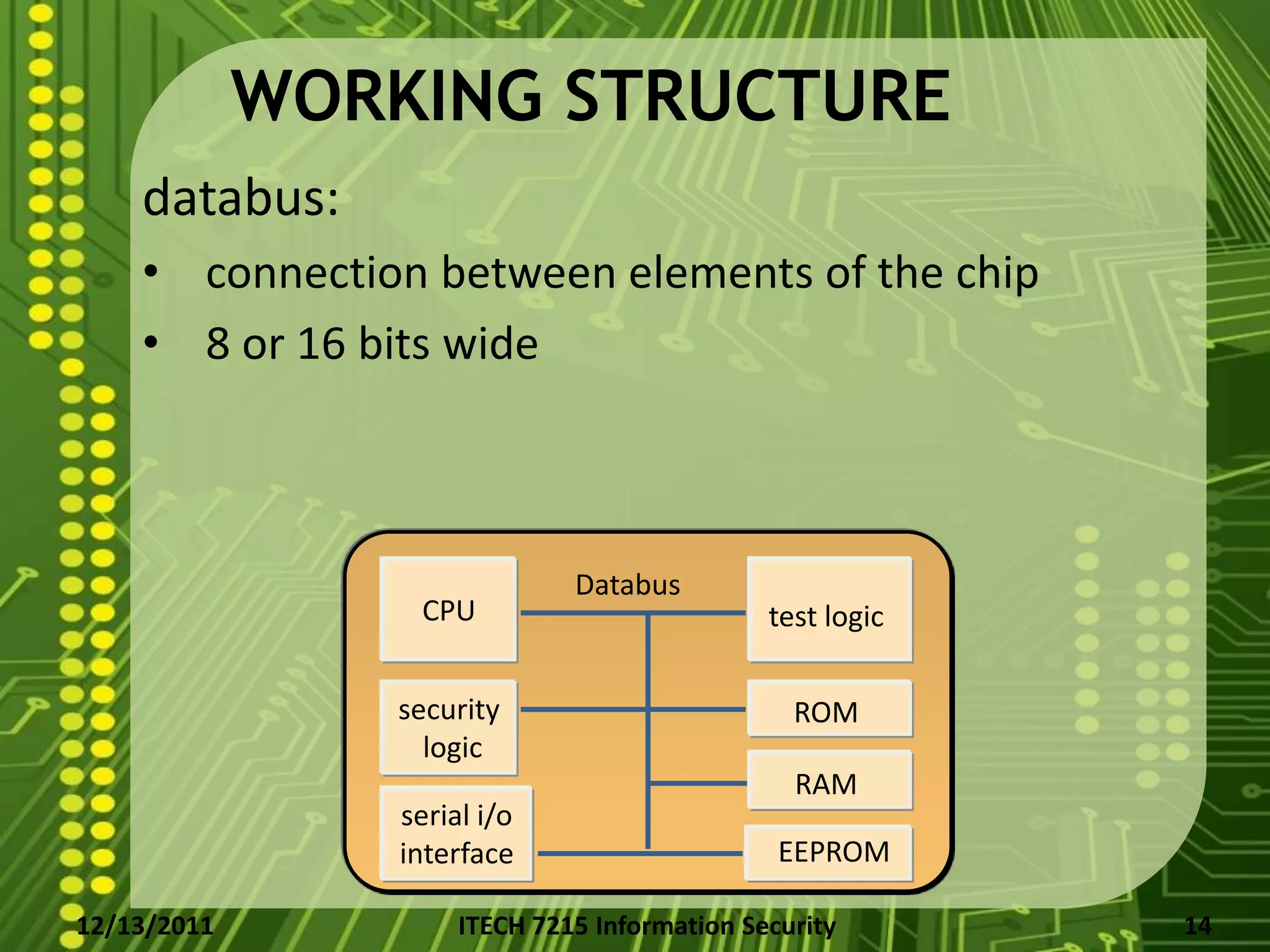
- Their architecture which includes a CPU, memory (RAM, ROM, EEPROM), security logic, and interface.
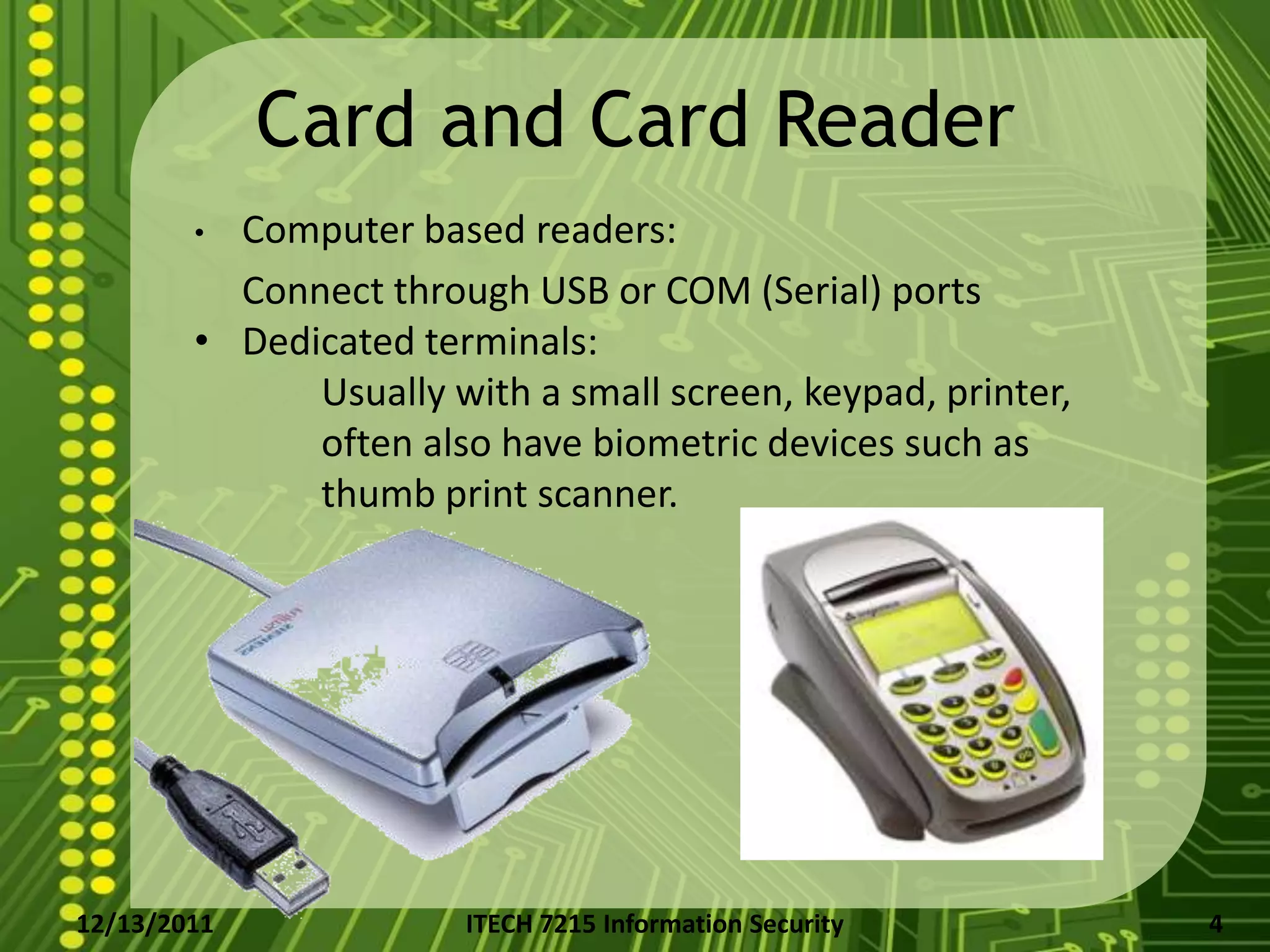
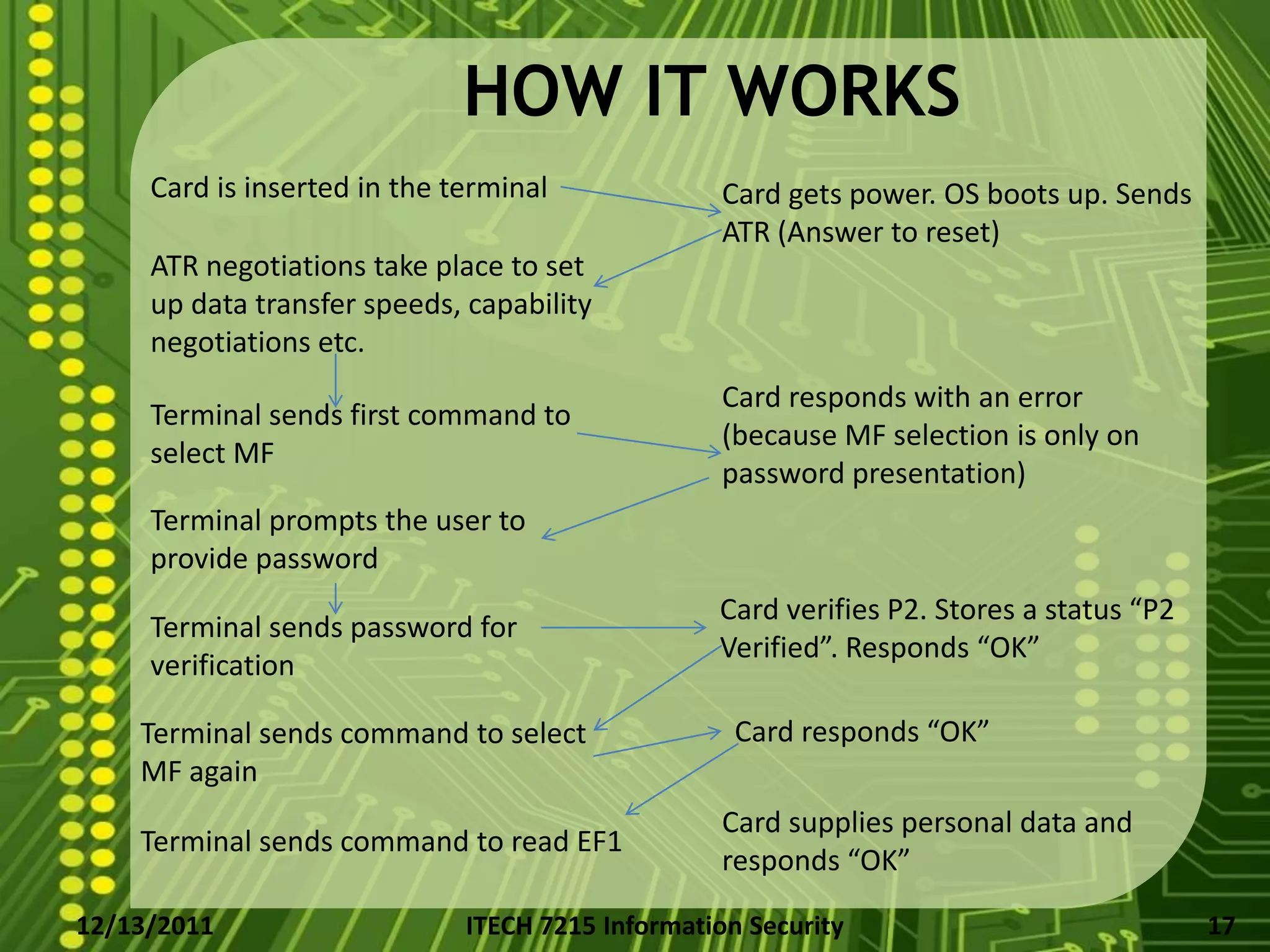
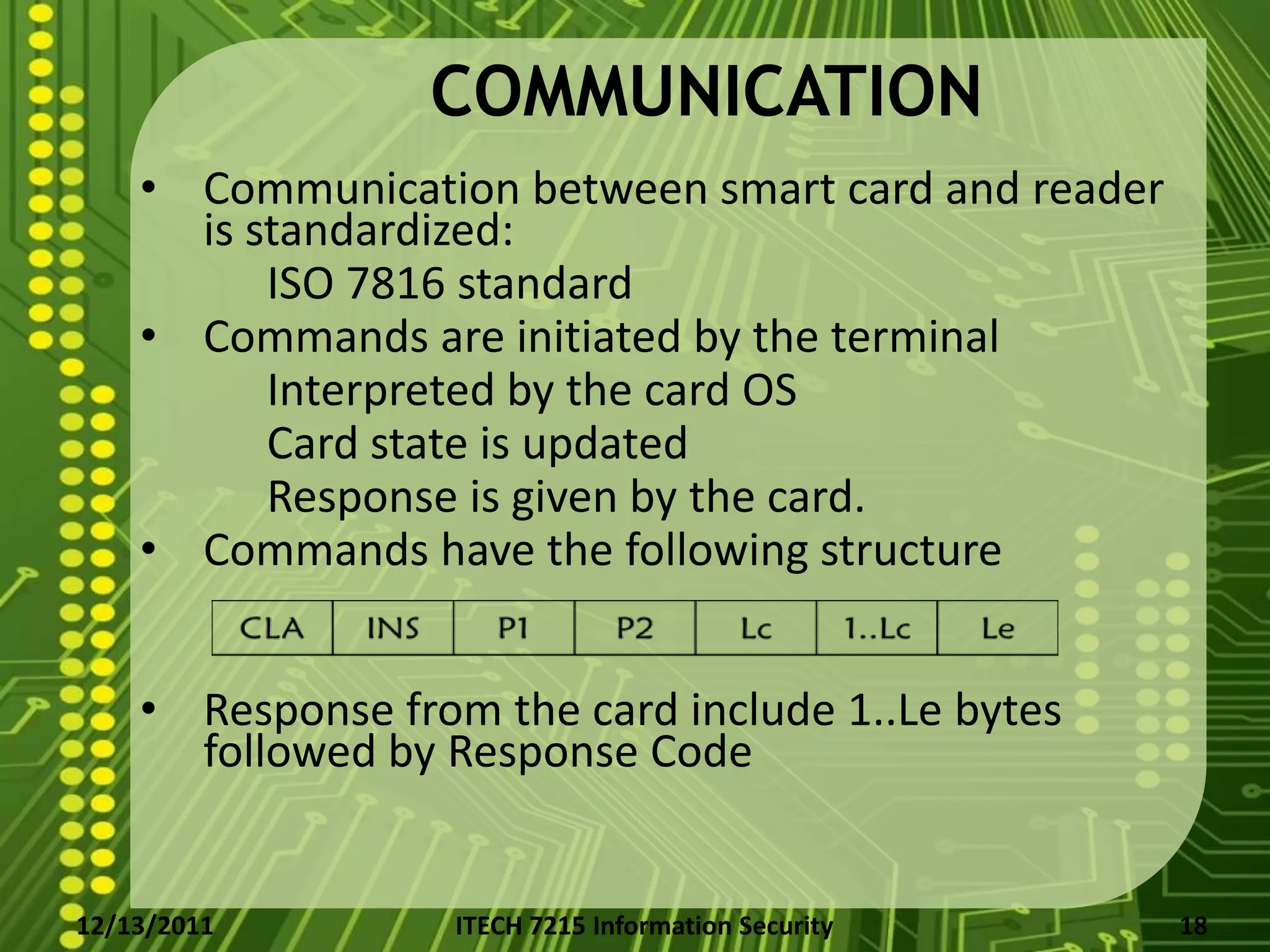
- How they work by communicating with card readers using standardized commands and responses.
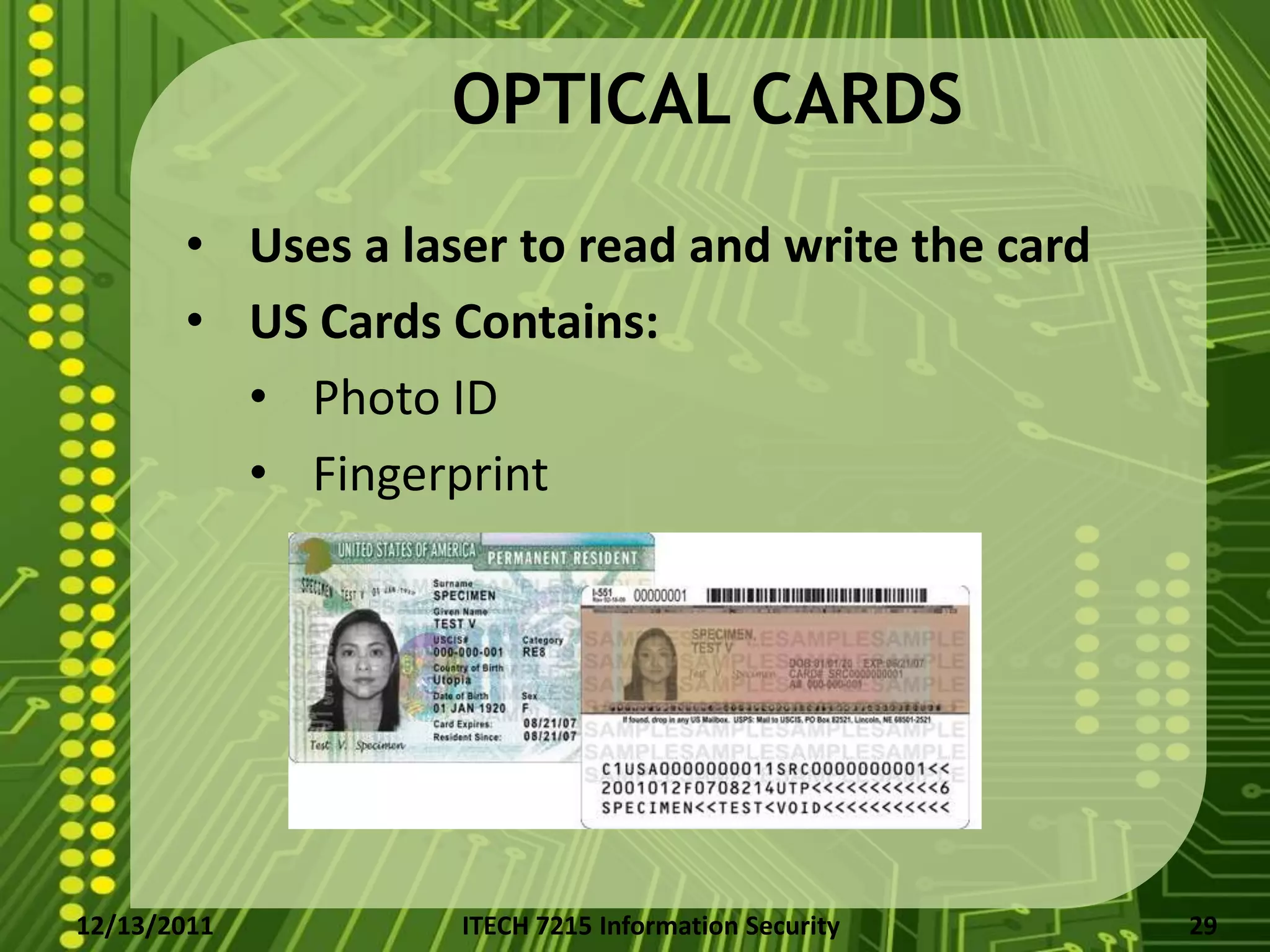
- Security mechanisms like passwords, cryptographic challenges, and biometric storage to authenticate users and the card/terminal.
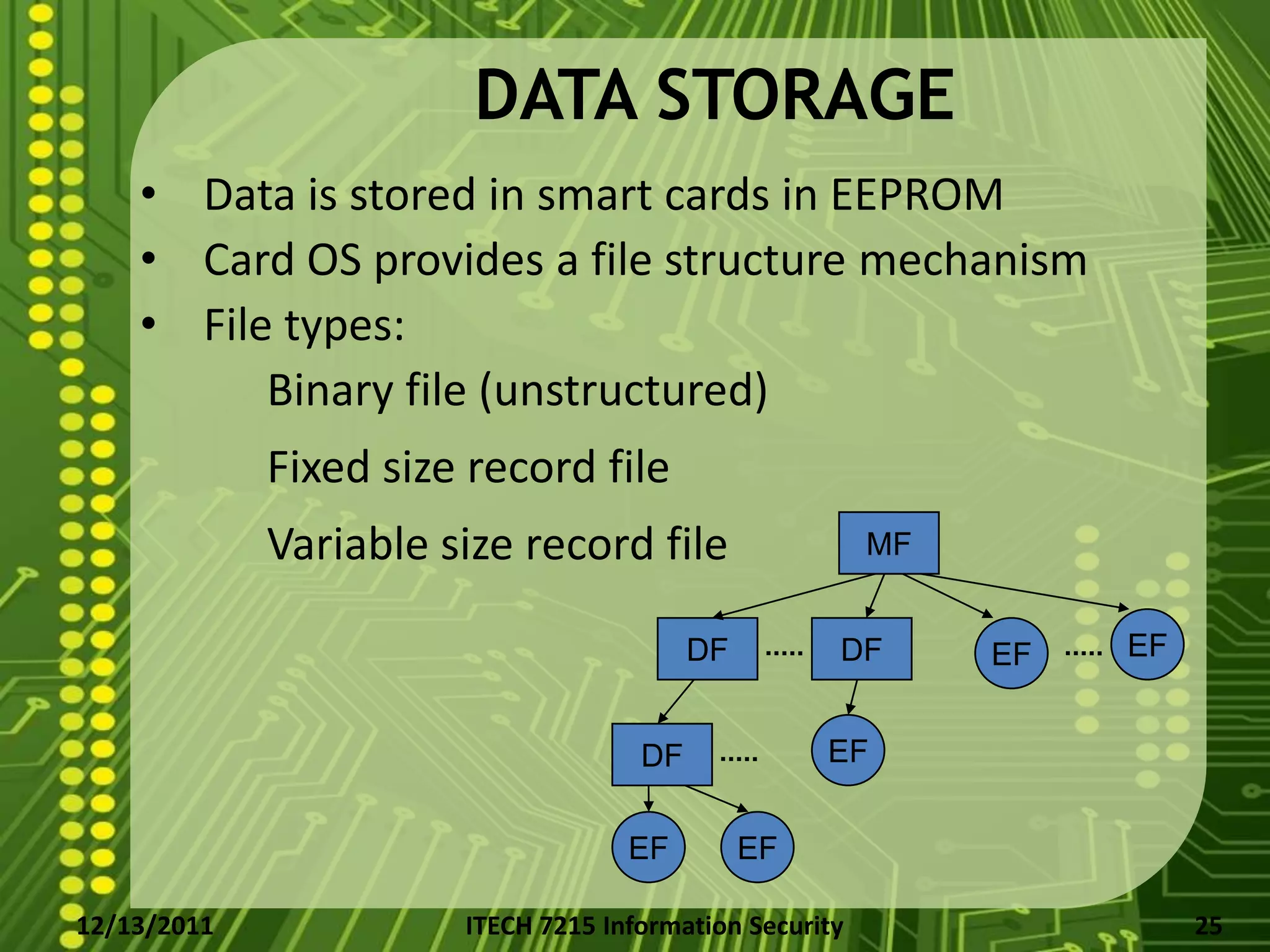
- How data is stored in their EEPROM memory organized in a file structure.