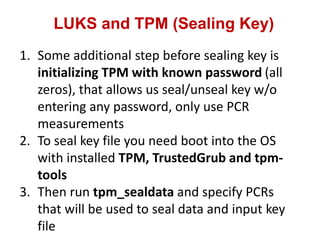
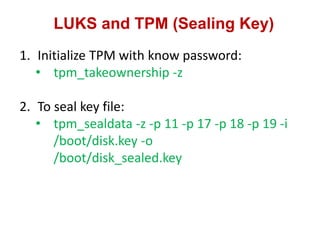
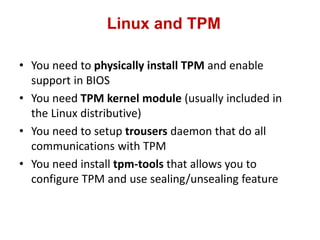
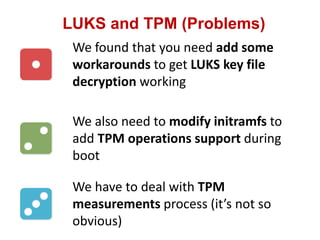
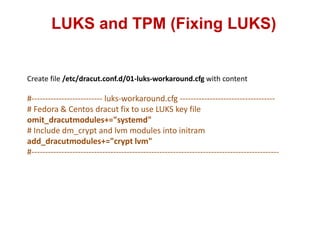
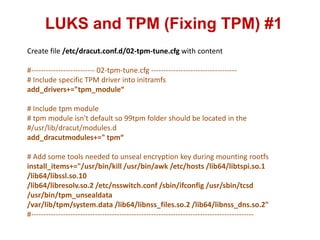
The document discusses using a Trusted Platform Module (TPM) to securely store encryption keys for disk encryption on Linux. It describes configuring TPM to measure and seal an encryption key file using PCR registers. Modifications are made to initramfs and cryptroot scripts to support unsealing the key during boot without user input by using the TPM. While TPM provides secure storage, integrating it with Linux disk encryption requires additional configuration to get the key unsealed and passed to cryptsetup during early boot stages.






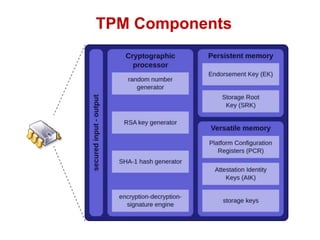
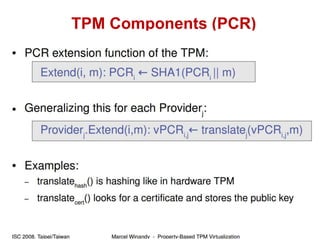
![TPM Components (PCR)
• Reset all registers, transfer execution to Core
Root of Trust Measurement
• Measure next stage of firmware into PCR[0]
and data into PCR[1]
– Hardware test and configuration
• Code always measured first, then executed
• New PCR value is SHA-1 hashed then
concatenated with previous hash;
permanently written to PCR
• Option ROMs and data into PCR[2] and [3]
• MBR into PCR[4], partition table in PCR[5]
PCR[0]
PCR[1]
PCR[2]
PCR[3]
PCR[4]
PCR[5]
PCR[6]
PCR[7]
PCR[8]
PCR[9]
PCR[10]
PCR[11]
PCR[12]
PCR[13]
PCR[14]
PCR[15]
PlatformConfigurationRegisters
Stephen.lamb@microsoft.com
http://blogs.technet.com/steve_lamb](https://image.slidesharecdn.com/tpmpresentation-160711095258/85/Wroclaw-3-Trusted-Computing-14-320.jpg)
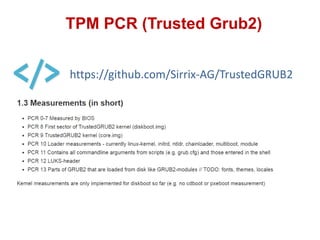


![LUKS and TPM (Fixing TPM) #3
Edit file /usr/lib/dracut/modules.d/90crypt/cryptroot-ask.sh
#You need to find "if [ $ask_passphrase -ne 0 ]; then" section and delete/comment it #out and add new logic:
if [ $ask_passphrase -ne 0 ]; then
/sbin/modprobe tpm_module
if [ -f /dev/urandom ]; then
/bin/mknod -m 644 /dev/urandom c 1 9
fi
/sbin/ifconfig lo 127.0.0.1
PID=`ps -eaf | grep tcsd | grep -v grep | awk '{print $2}'`
if [[ "" == "$PID" ]]; then
/usr/sbin/tcsd -f &
sleep 3
fi
mkdir -p /mnt
mount -o ro /dev/sda1 /mnt
## copy unsealed key to tmpfs partition ##
mkdir -p /key_tmpfs
mount tmpfs /key_tmpfs -t tmpfs -o size=32m
/usr/bin/tpm_unsealdata -z -i /mnt/disk_sealed.key -o /key_tmpfs/disk_unsealed.key
cryptsetup luksOpen --key-file=/key_tmpfs/disk_unsealed.key "$device" "$luksname" && ask_passphrase=0
umount /key_tmpfs
##
if [[ "" != "$PID" ]]; then
kill -9 $PID
fi
umount /mnt
unset PID
fi](https://image.slidesharecdn.com/tpmpresentation-160711095258/85/Wroclaw-3-Trusted-Computing-37-320.jpg)