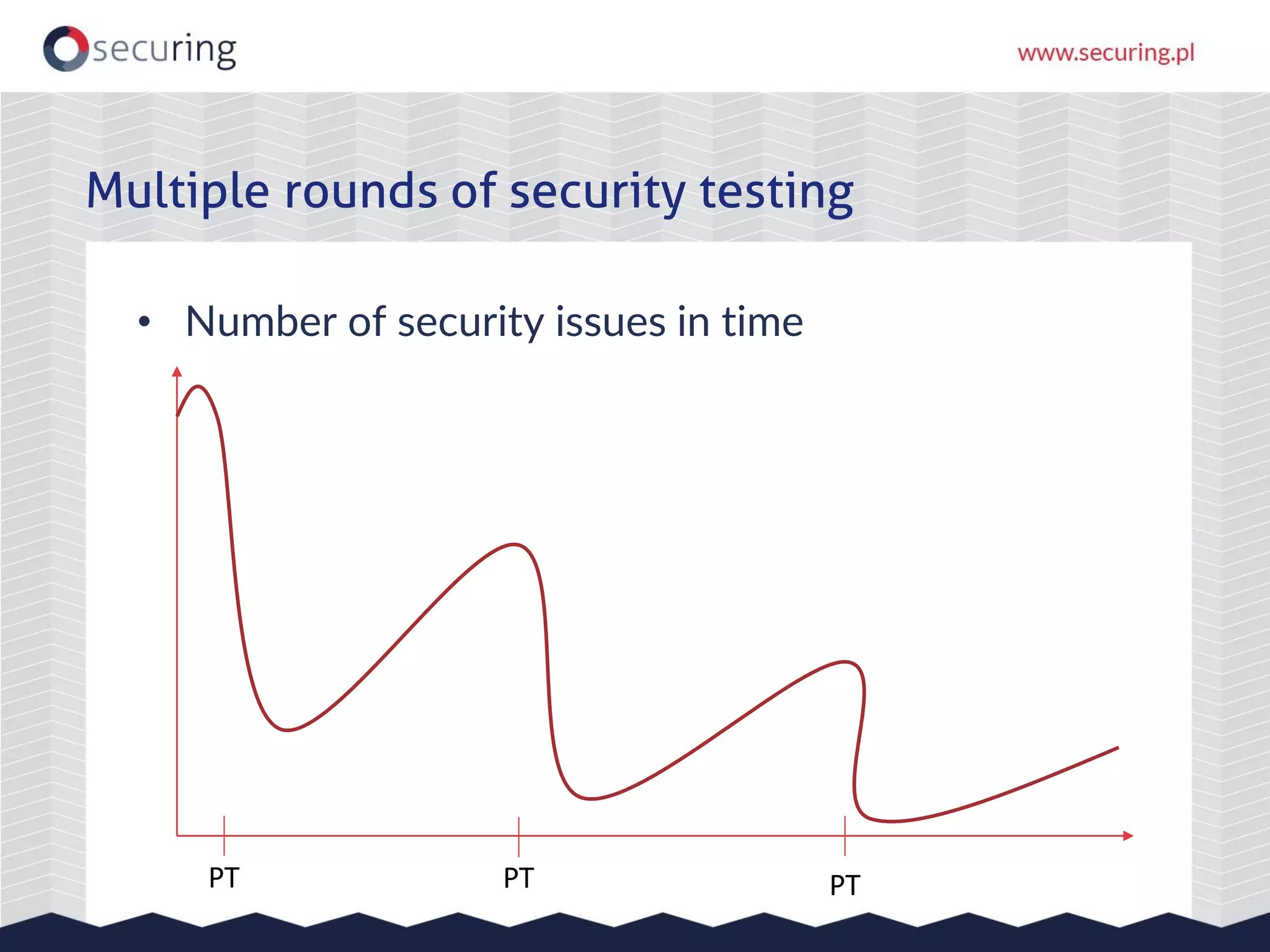
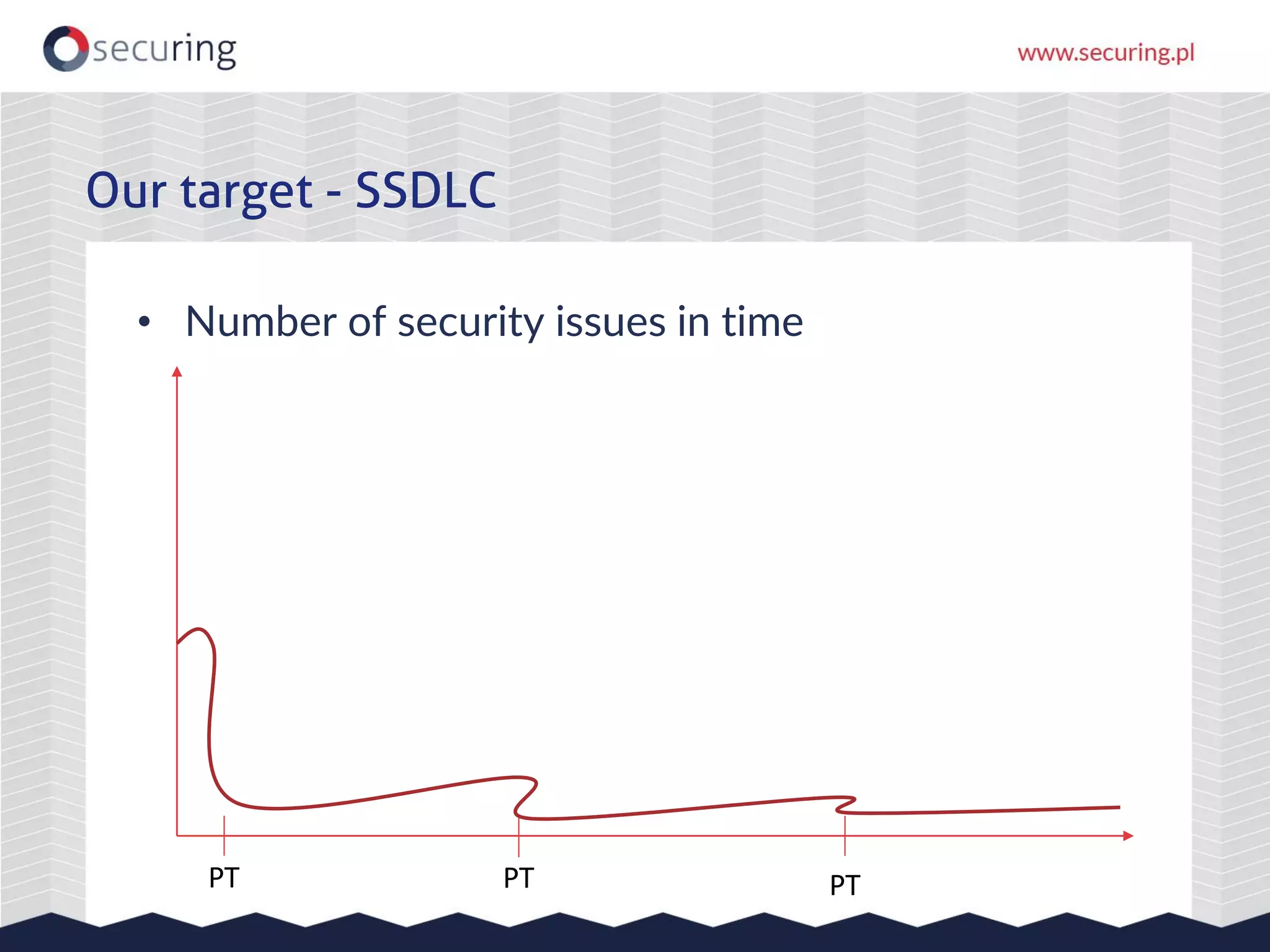
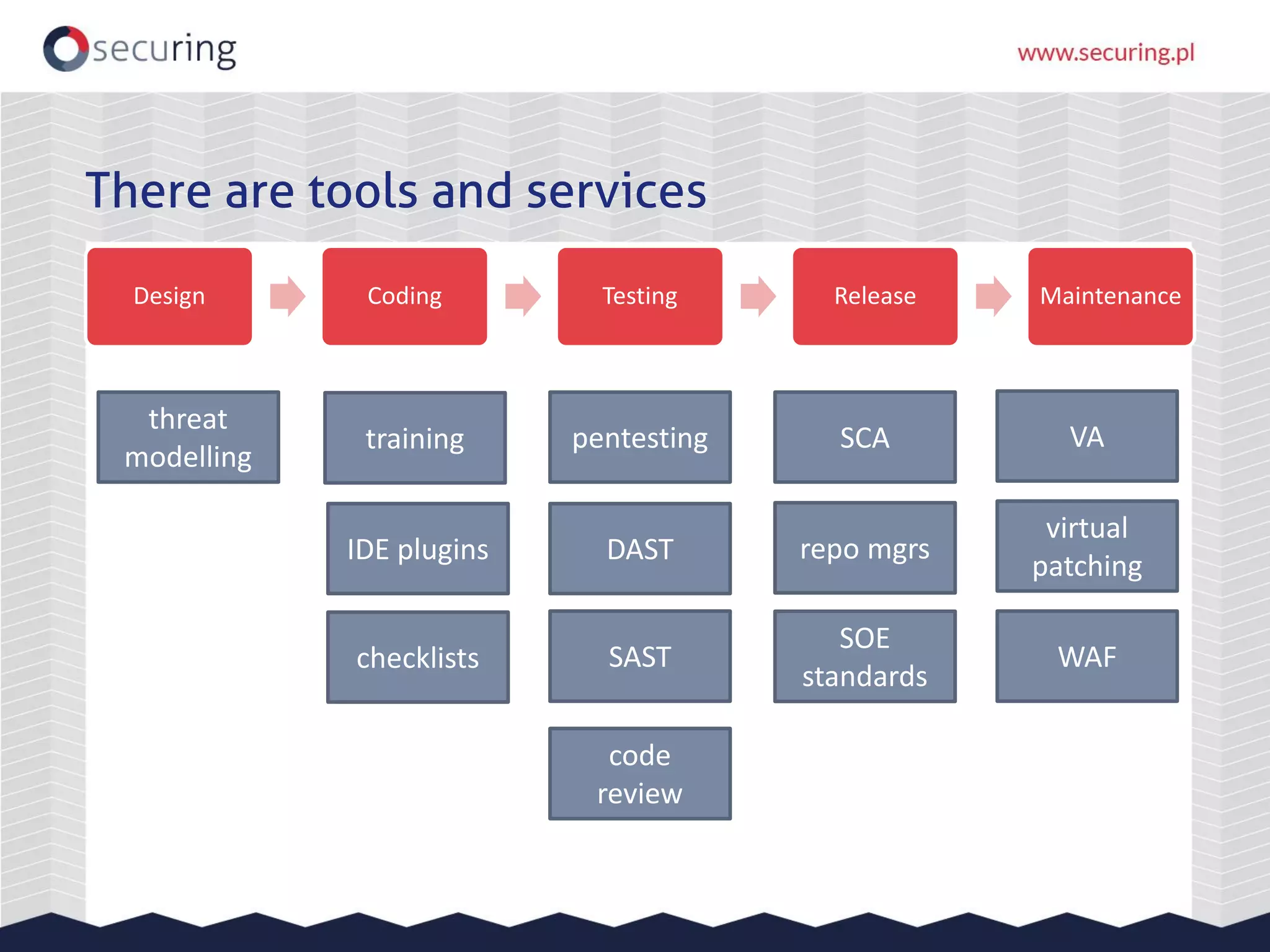
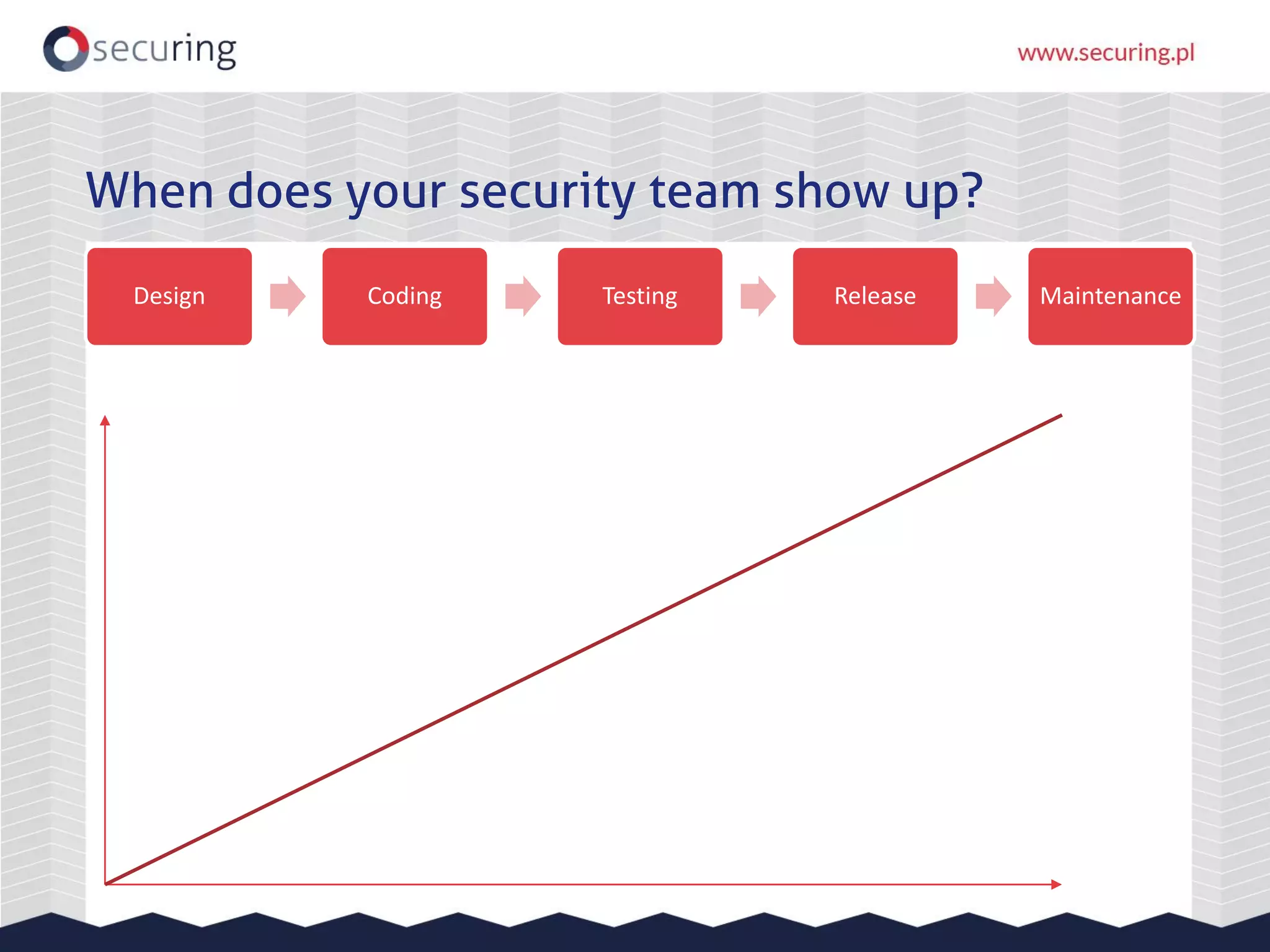
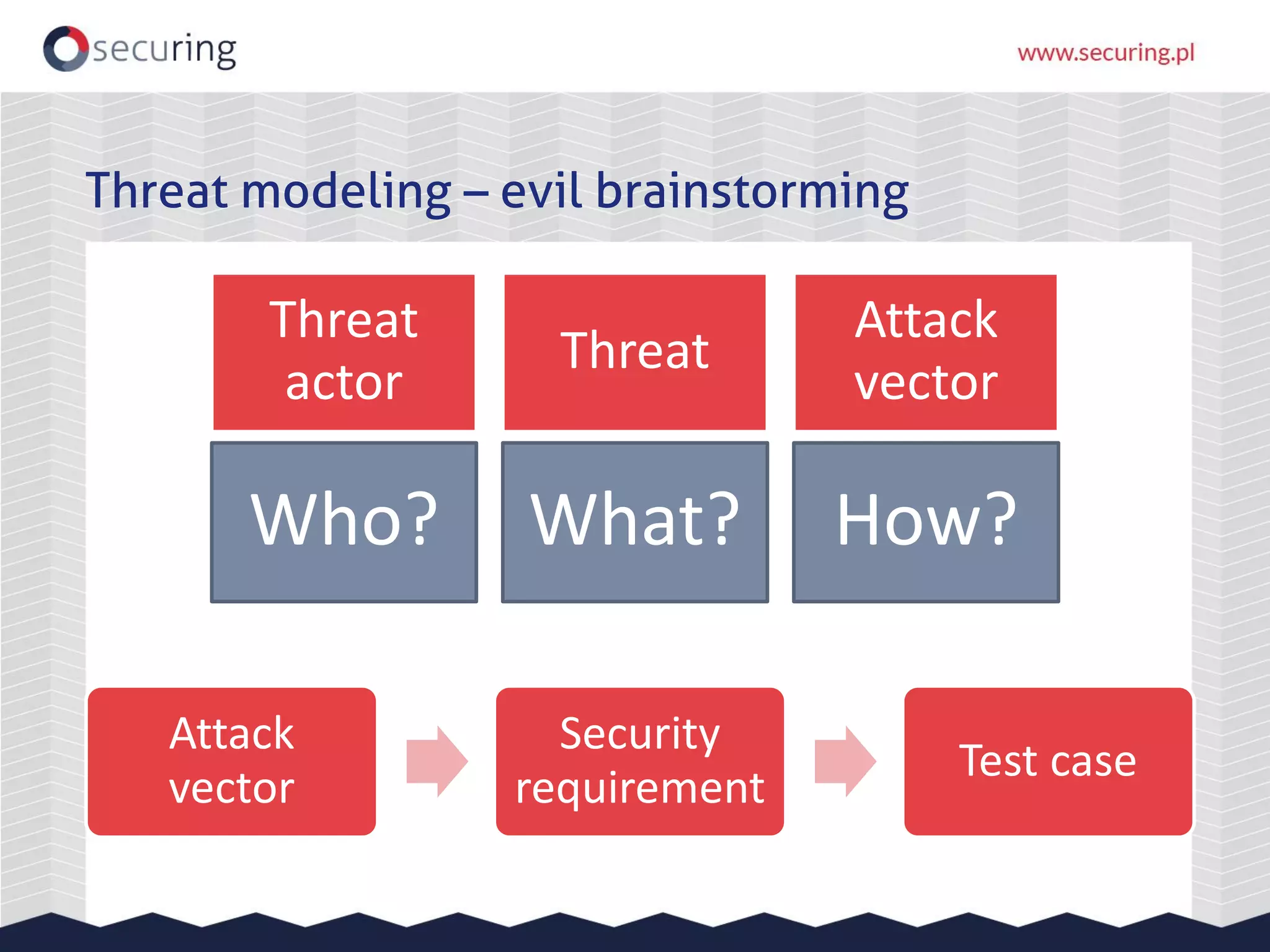
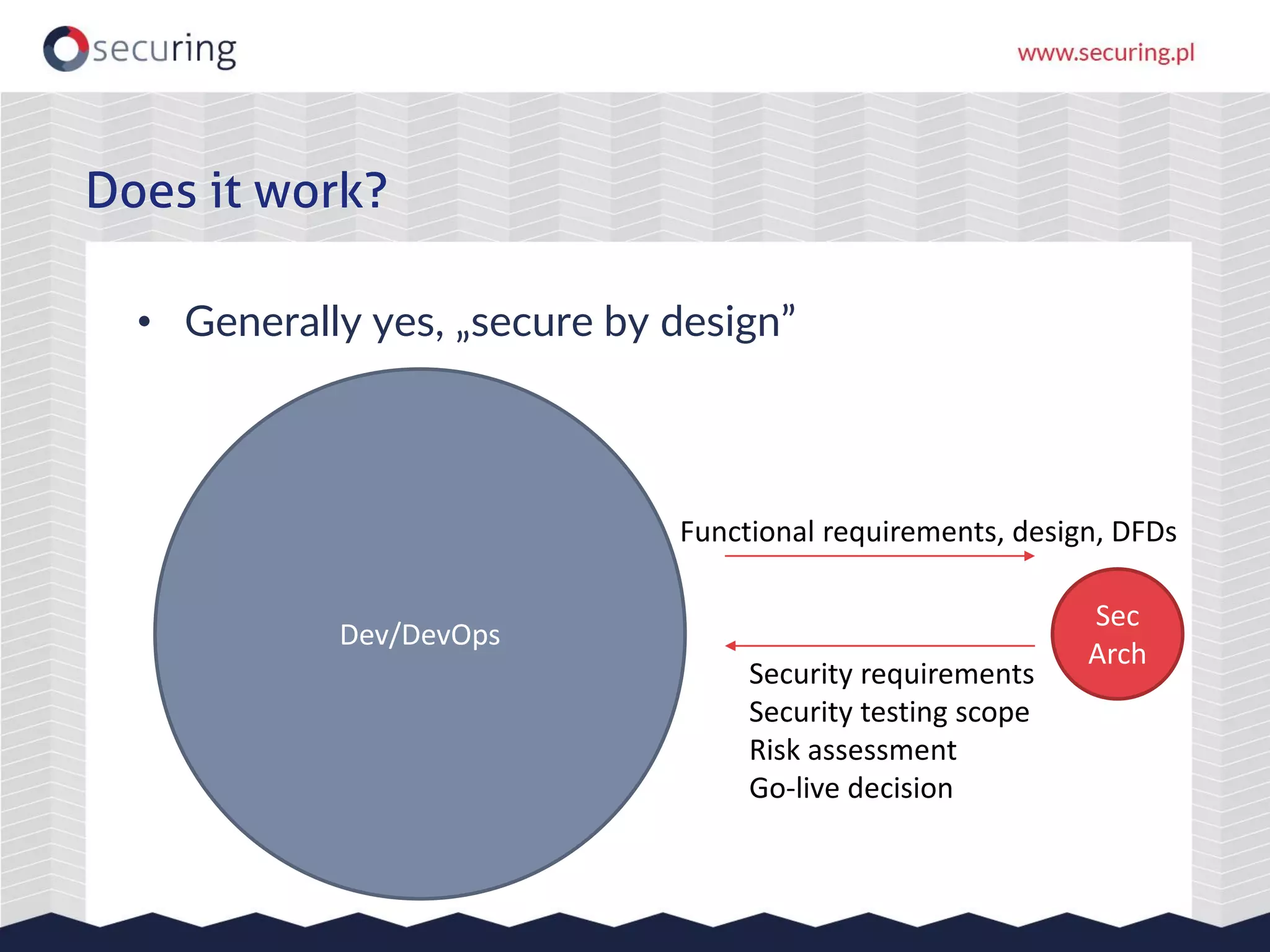
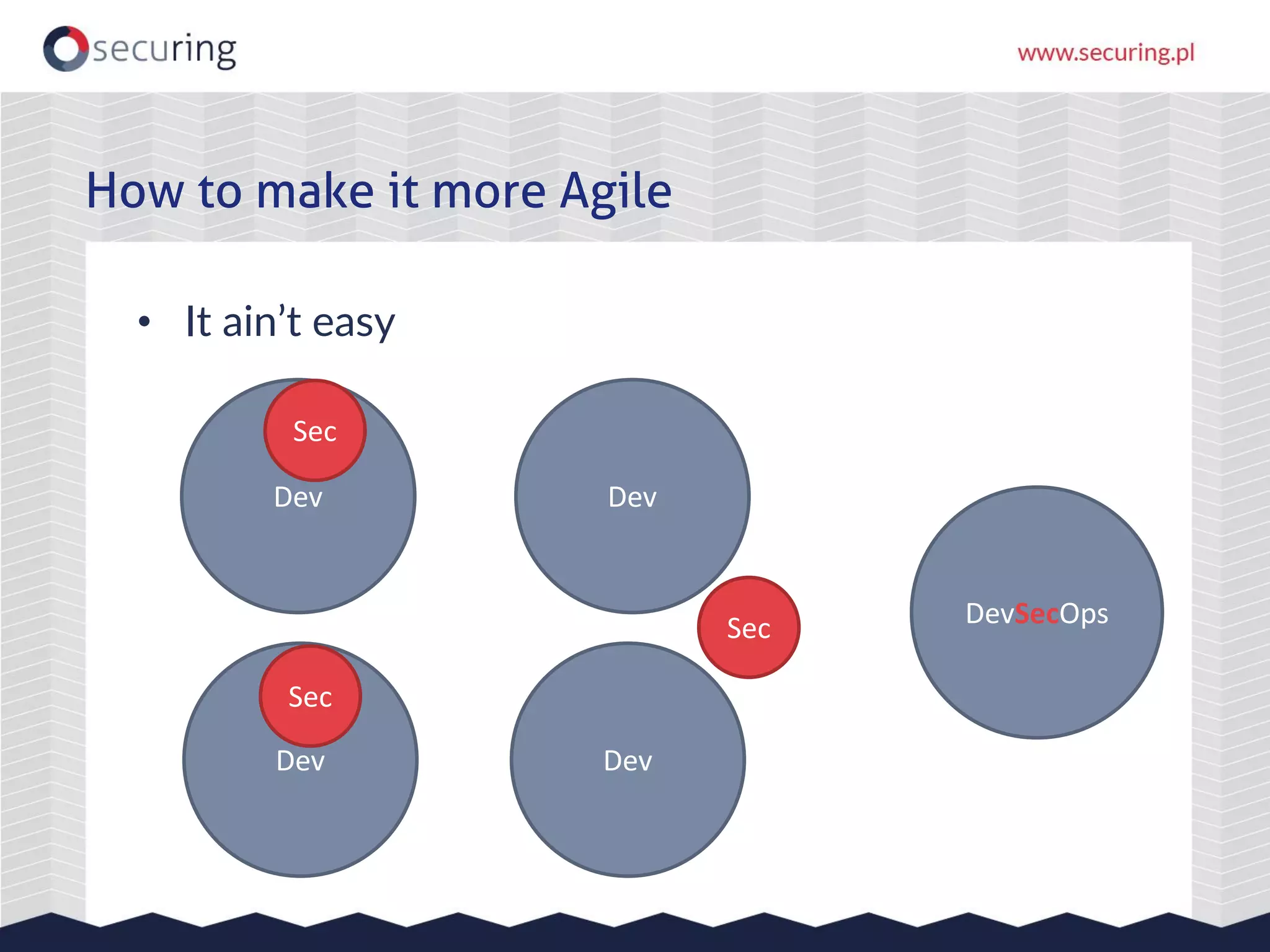
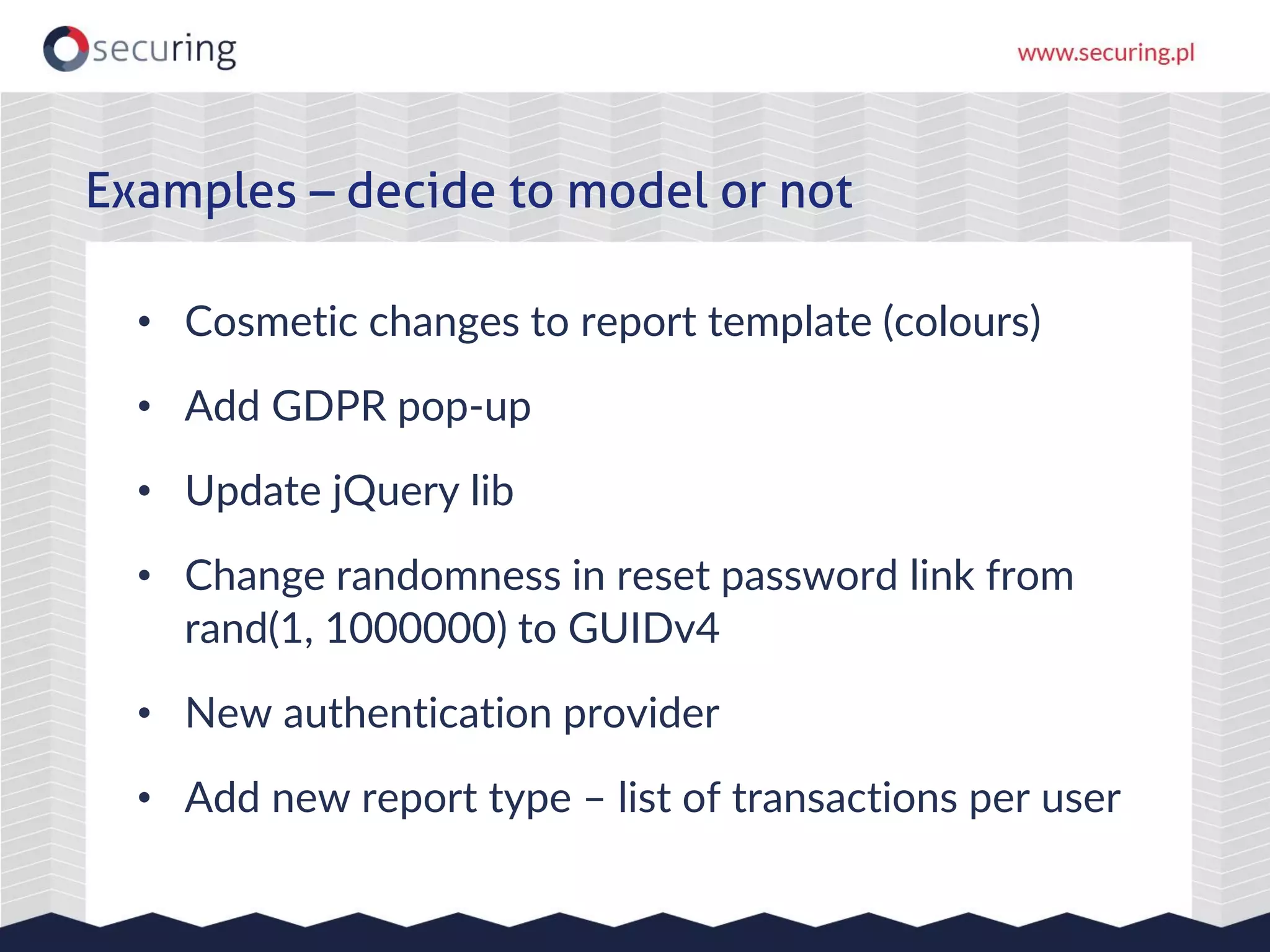
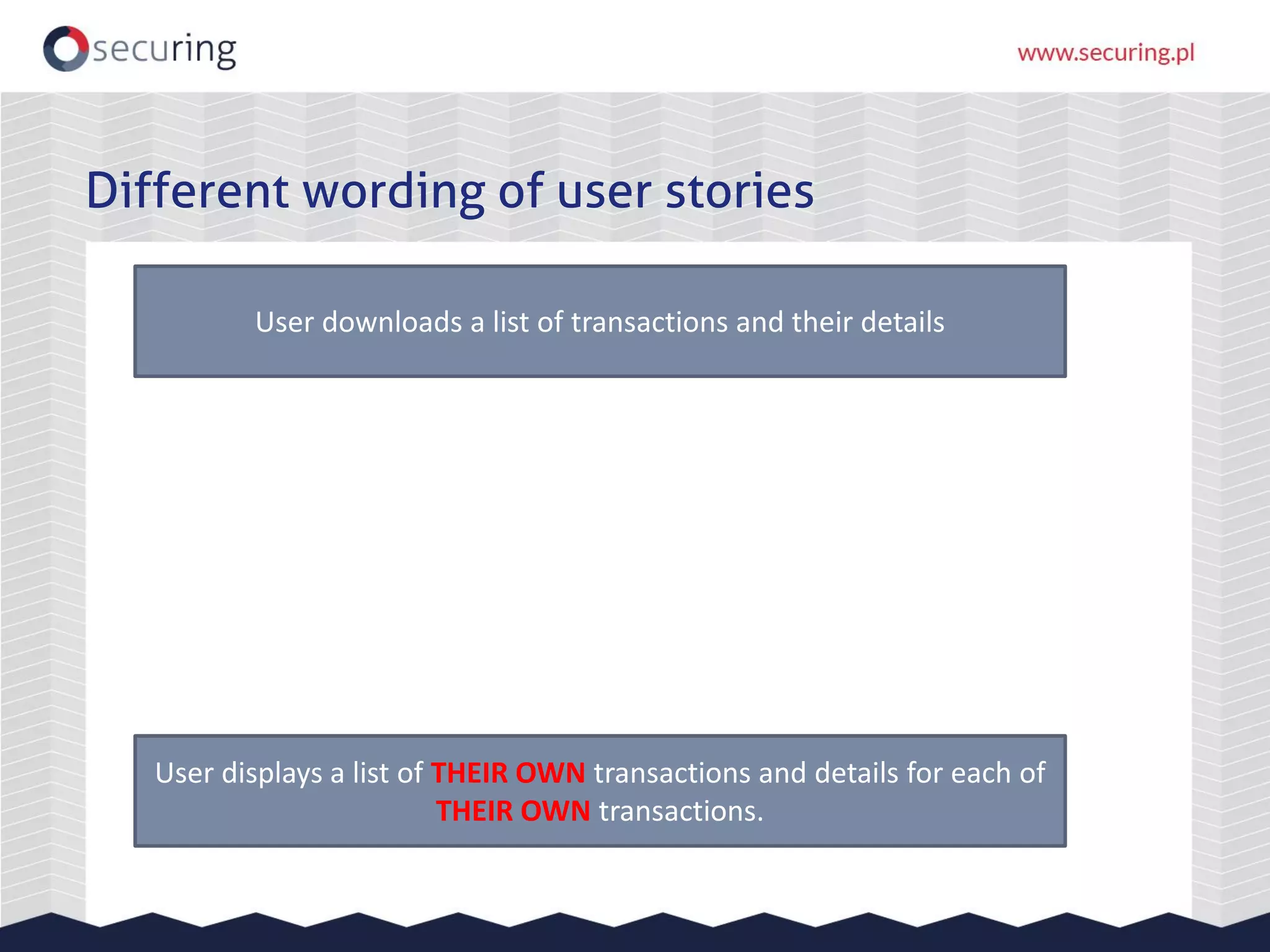
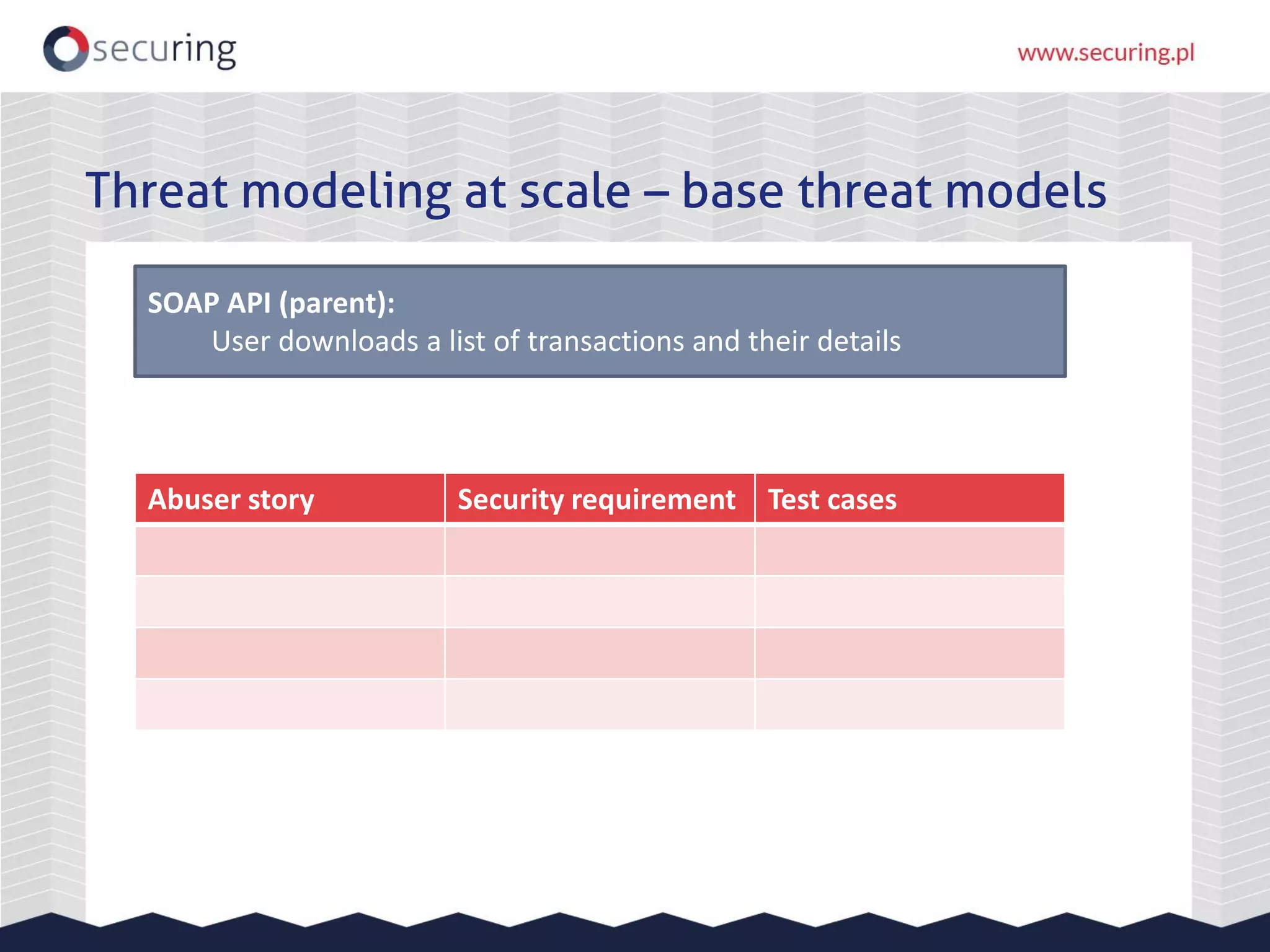
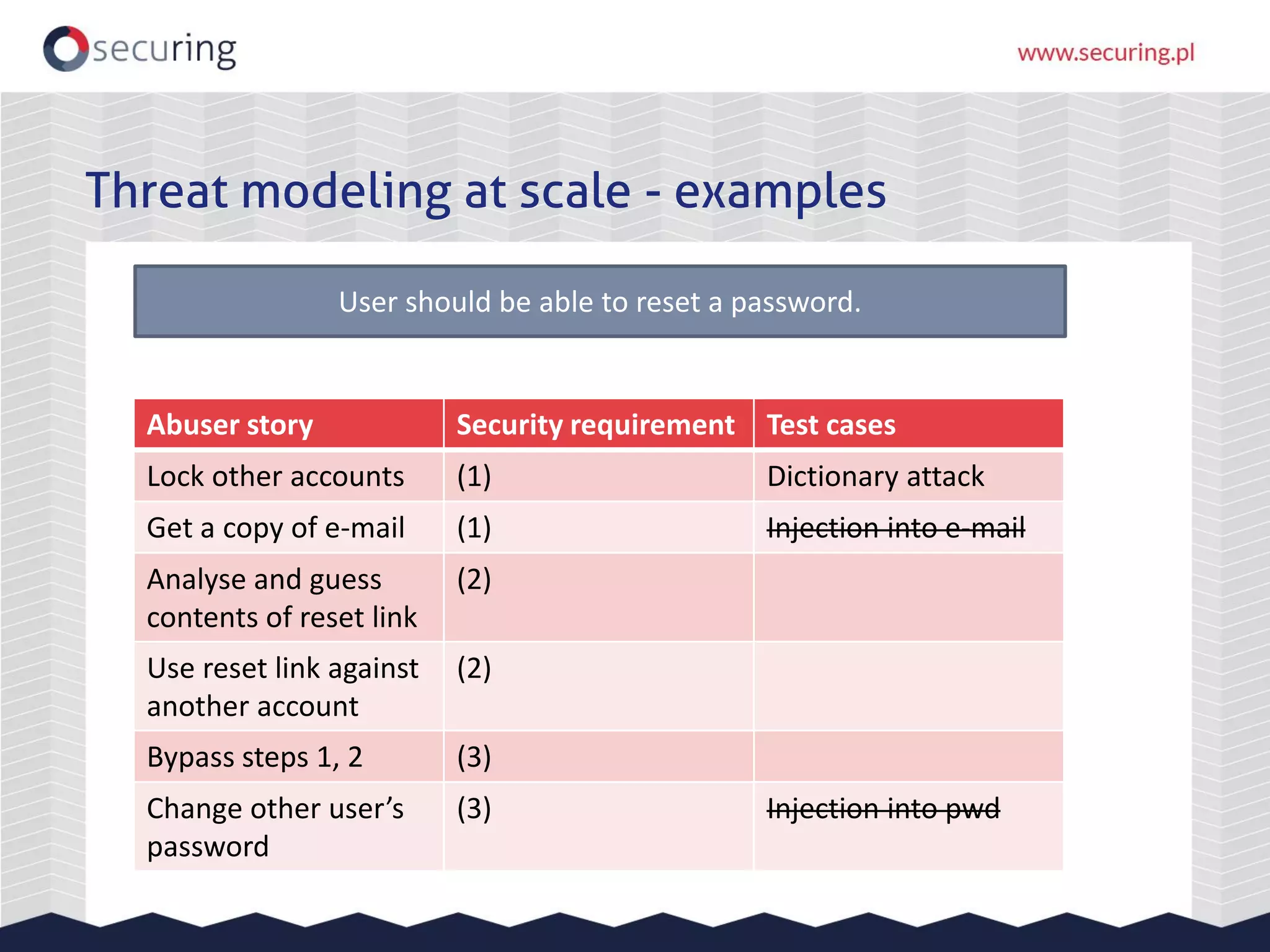
This document discusses using threat modeling at scale in agile development to improve security. It proposes identifying security requirements and test cases for each user story by considering potential "abuser stories". This would involve breaking down high-level user stories, assigning security champions to identify abuser stories, and having the security team maintain base threat models and own testing. Examples of threat modeling user stories around password resets and money withdrawals are provided. The goal is to shift security left in the SDLC by introducing it earlier through systematic threat modeling of user stories.





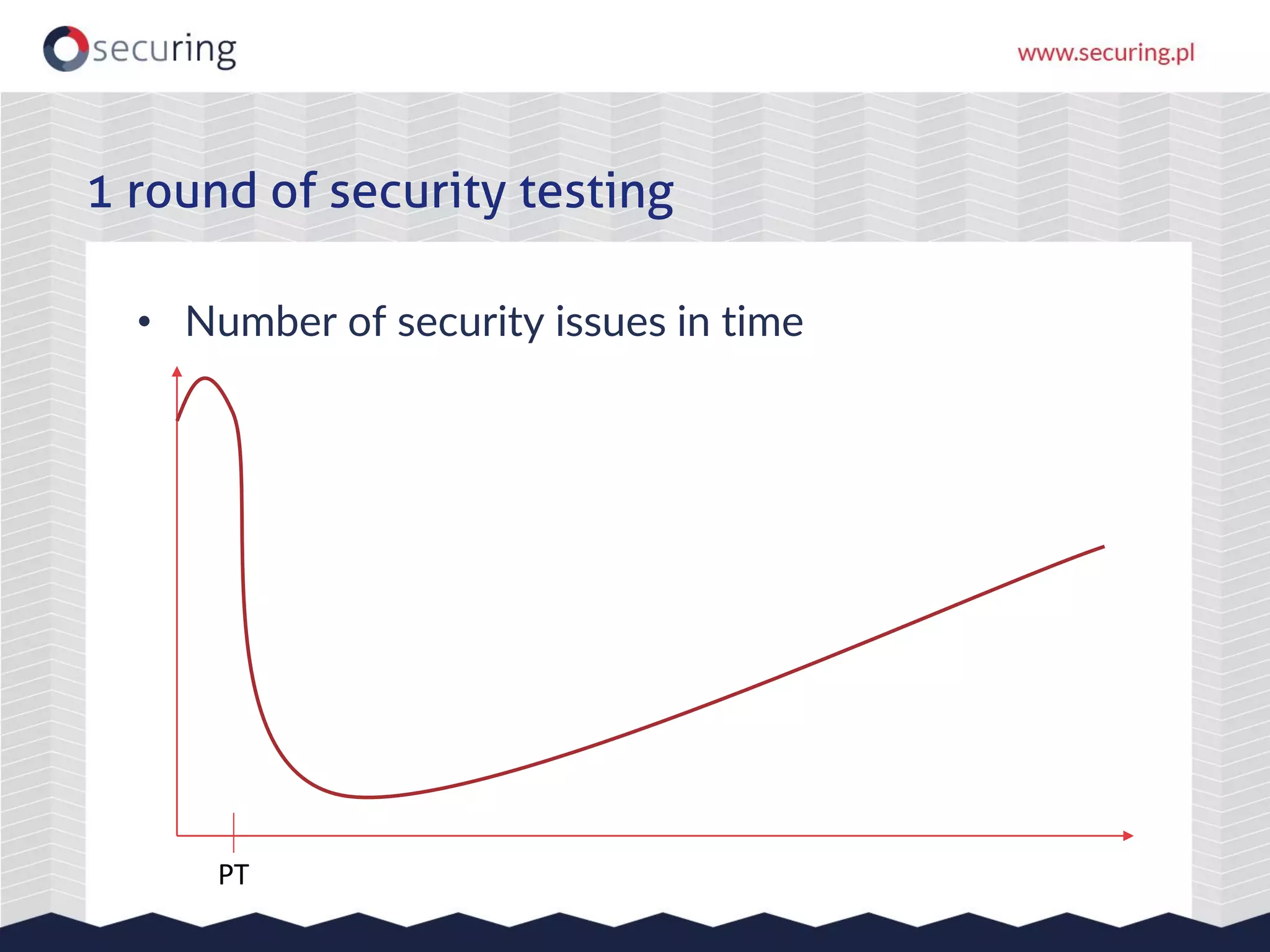











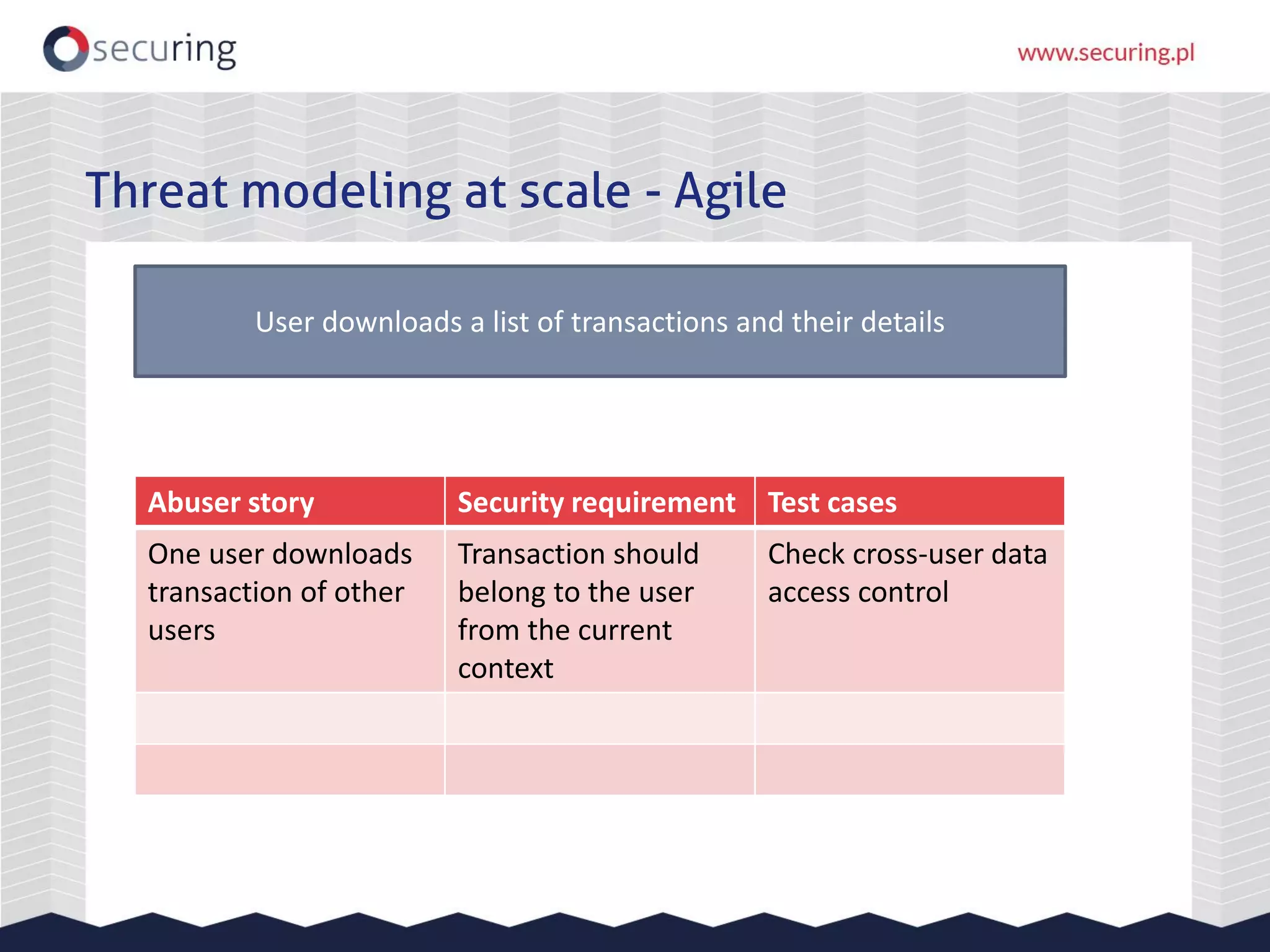






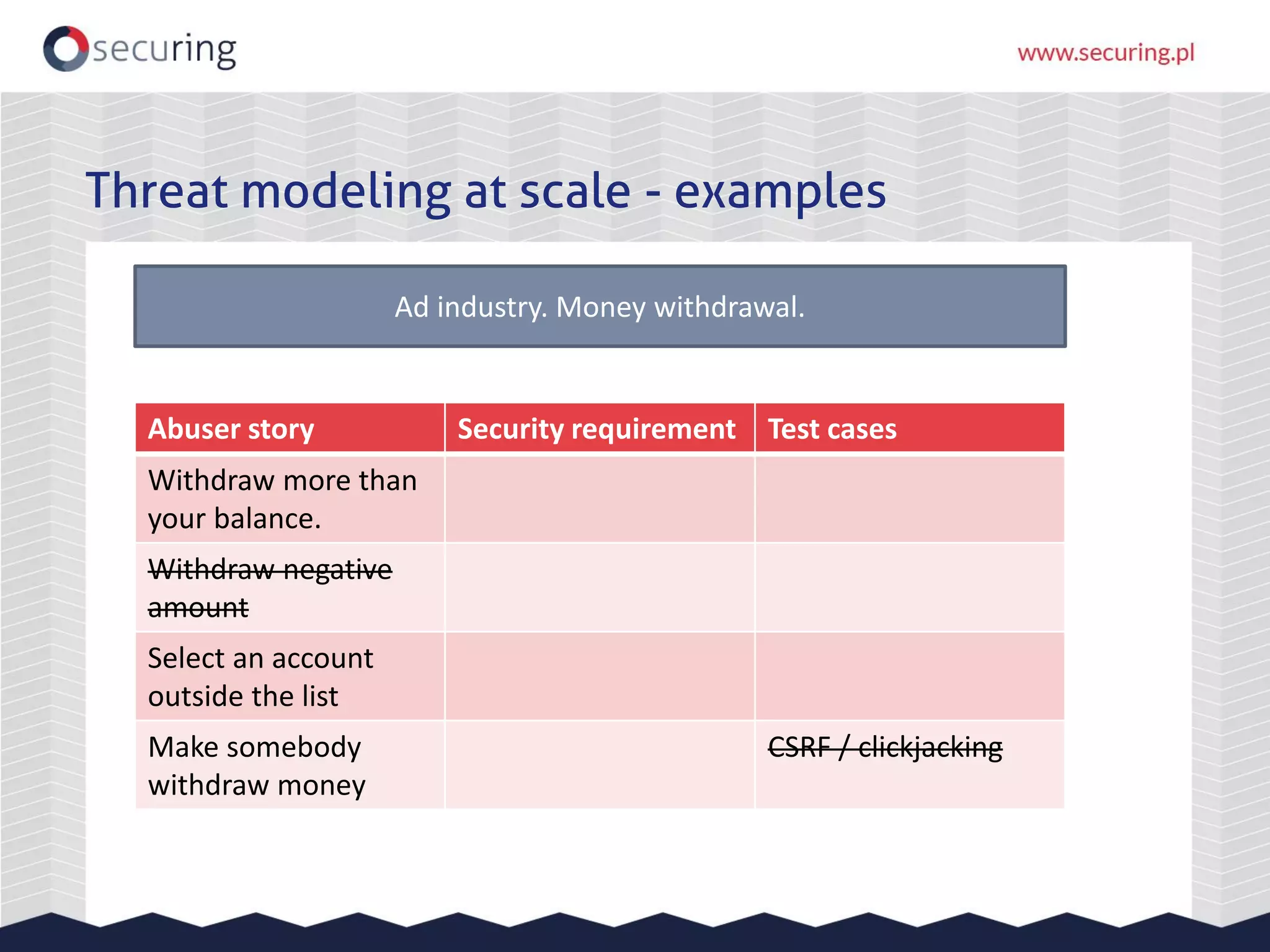
![Threat modeling at scale - examples
User should be able to reset a password.
Abuser story Security requirement Test cases
1. Your e-mail: […]
2. https://example/reset?e-mail=x@y&rnd=12345
3. New pwd: [..], confirm new […]](https://image.slidesharecdn.com/letsgetevil-threatmodellingatscale-191022195630/75/OPD-2019-Threat-modeling-at-scale-47-2048.jpg)
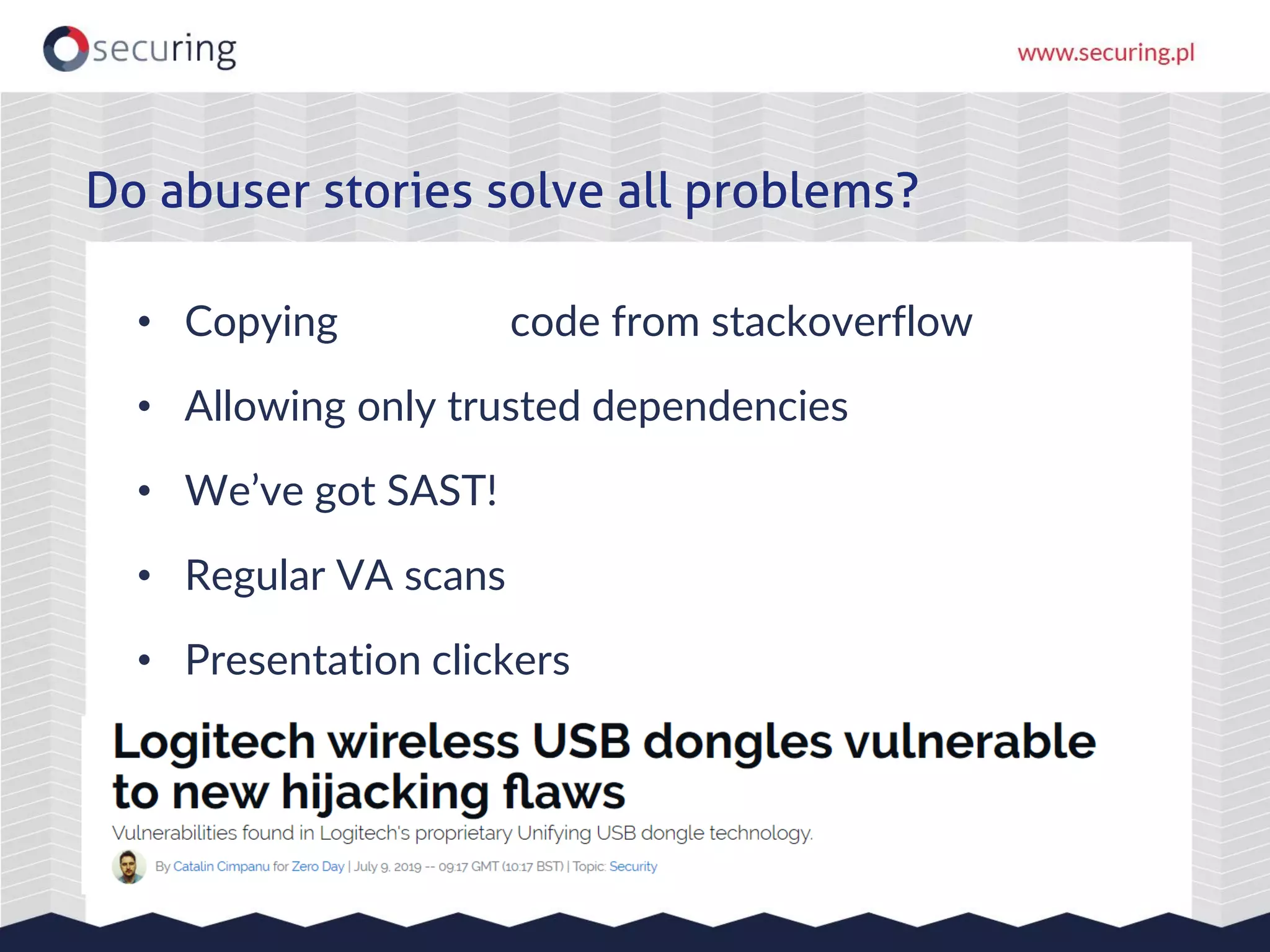
![Threat modeling at scale - examples
Ad industry. Money withdrawal.
Abuser story Security requirement Test cases
How much do you want to withdraw: […]?
To which of your accounts […] (drop-down list)?](https://image.slidesharecdn.com/letsgetevil-threatmodellingatscale-191022195630/75/OPD-2019-Threat-modeling-at-scale-49-2048.jpg)