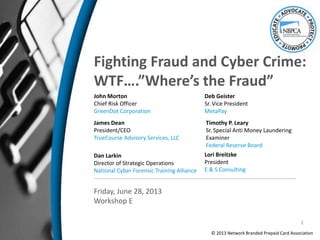
Workshop E: Fighting Fraud and Cyber Crime: WTF…"Where's the Fraud"
- 1. Fighting Fraud and Cyber Crime: WTF….”Where’s the Fraud” John Morton Chief Risk Officer GreenDot Corporation James Dean President/CEO TrueCourse Advisory Services, LLC Friday, June 28, 2013 Workshop E Dan Larkin Director of Strategic Operations National Cyber Forensic Training Alliance Deb Geister Sr. Vice President MetaPay Lori Breitzke President E & S Consulting © 2013 Network Branded Prepaid Card Association Timothy P. Leary Sr. Special Anti Money Laundering Examiner Federal Reserve Board 1
- 2. Thank You To Our Sponsors Presenting Sponsors Supporting Sponsor Welcoming Reception Sponsor Associate Sponsors Founding Sponsors
- 3. • The Power of Collaboration • Obstacles of Collaboration • Regulator’s View of Prepaid Cards • Industry’s View of Prepaid Fraud Mitigation • NBPCA’s Collaboration • Discussion with the Panel of Experts 3 Agenda
- 5. Law Enforcement Alliance for Prepaid (LEAP) • New program with selected Prepaid Anti Fraud Forum members to participate in this more direct connect with law enforcement thru NCFTA & others (IAFCI) • Information sharing for company and industry level benefits • Bi-weekly action calls with NCFTA • Monthly NCFTA/LEAP industry status reporting • Quarterly research papers • Coordination of reporting standards/CyFin • Establish Best Practices for LE communication • Aggregation of crimes for prosecution • Special projects 5
- 6. LEAP Evaluation Background • Approximately 6 week review • 7 member companies tasked with the review • Activities included; – Development of evaluation criteria – Onsite reviews & system demos – Weekly calls & reviews – Interviews with NCFTA Staff and industry imbeds – Interviews with members using services on trial basis – Development of findings, benefits, ROI potential and recommendations • Results – Recommendations, Presentation and Report • Positive presentation • Contract entered into • Kickoff meetings conducted and program underway 6
- 7. Primary LE Complaint “Difficult for LE to track down who to speak to in order to identify account information for investigations and fund recovery efforts.” LEAP Response • Created a resolution pursuit team • Focused on analyzing the root cause, and recommending resolution • Conducted problem walk-thru with NCFTA and interviews with other LE officers • Created initial inventory of financial contacts • Added findings to NBPCA best practices and with ongoing NCFTA collaboration to update and refine • Scenarios: what’s really being found in the field and how to address 7
- 8. Three Scenarios 1. “Suit case in the field” Cards are found in the field by LE officers. Due to suspicious circumstance, the field officers wish to find out quickly if cards are stolen, have suspicious balance, etc. 2. “Investigation of seized cards” During an arrest, a large number of cards are seized, or a large number of account numbers are uncovered and investigating officers need research by FI’s into the accounts. 3. “Electronic Loads into Prepaid accounts” Outbound funds appear to be wired or ACH to what appears to be PPD accounts. LE or FI’s. LE or FI’s wish to contact the PPD FI to freeze or recover funds 8
- 9. Objective •Law enforcement is trying to collect evidence of suspicious activity regarding potential prepaid cards identified during a stop – the goal is to make an arrest. •Chain of evidence is NOT needed Questions to ask •What is LE trying to determine? •Is the card(s) real, counterfeit or stolen? •Have there been suspicious transactions? •Is the Balance at a suspicious level? •Immediate response IS needed LE Actions •Call customer service number on back of card •Asked to be transferred to fraud management hotline for FI’s prepaid products •Tell them LE believes the card is involved in criminal activity and wish to determine 1-3 •Provide them with items 1 -7 “Suit Case in the Field” Data Points LE has: (may vary by product) The Card 1. Name of issuing bank 2. Network Brand 3. Marketing Brand 4. Card number 5. CVV number 6. Date of expiration 7. Name on card 8. Website 9
- 10. NBPCA Best Practices Findings Industry Best Practices • Thru NBPCA create and maintain Fraud management contact information • Publish information through NCFTA • Determine methodologies to identify PPD Accounts, and sub-accounts in Pooled accounts, from ACH & Wire transfers. Electronic Loads Industry Best Practices • Through NBPCA create and maintain Fraud management contact information • Publish information through NCFTA • Determine methodologies to identify PPD Accounts, and sub-accounts in Pooled accounts, from ACH & Wire transfers. Seized cards Industry Best Practices • Establish PPD LE 24/7 Hotline • Train Customer Service to direct LE calls to hotline • Develop inventory of products and contact numbers of Responsible party • Require responsible parties to create hotline Field Operations 10
- 11. NCFTA Prepaid Report • Value of working across industry and agency – Predictive – Preventive – Fraudsters are product indifferent…just looking for weak points. Thus, apply learnings from mature products to emerging products • Value in being proactive vs. reactive in Industry/Agency collaboration • Prepaid as a model of young industry – Getting in front of fraud trends while the industry is young • NCFTA written report: Increased Interest in Anonymous Prepaid – Trends in US vs. International – Findings in types of accounts – Virtual currency related to Prepaid 11
- 12. Financial CyberCrime Chain Intrusions Data Breach Key Logging Network Applications ATOs Ishing(S) False identities Stolen cards Services Forums Markets Recruitment Scams Fraud Id theft ATOs Loading ACH Wire W/U Cash out ATM’s W/U Virtual Purchases Crime Manager(s) Crime Sponsor(s) Funding Strategy Recruiting Management Budgeting Hackers Hosters Phishers/Hackers Mules Money Laundering FraudIdentity Theft CounterfeitingCyberCrime Drugs Trafficking Porn Gambling Future crimes Committed Crimes (AML) 18m 3-6m 1-3 m 12-24hrs 12
- 13. Next Steps – Expand the Blocks • Specific threats • Actors • Prepaid value chain target • Risk Level • Metrics – Volume – Velocity • Case Studies ATOs Ishing(S) False identities Stolen cards • Best Practices • Defensive resources – Partners – Tools – Products & Vendors • Reaction Plans – Management/Media • LE involvement points Threat characteristics Mitigation protocols 13
- 14. Govt/L.E Hurdles • Defining problem/threat too narrowly = pipes • Rhetoric vs. Reality “collaborating- sharing” Really?? • Re-inventing wheels every 2-4 years… • Slight re-wording = same results. (see above) • Continuity of Teams (Including Executive Management) • Need to sync L.E with regulators (Fin, Telco, Cable) • Need to adopt universal “OC” (people focus) model 14
- 15. Joint Initiative Approach (Refined Partnerships) • SLAM-SPAM • Digital Phishnet (DPN) • Stock-Aid • Cy Fin • Pharm-Assist • Telco/Mobile – (Int Reshipping/Money Laundering) 15
- 16. NCFTA Successes NCFTA provided intelligence to law enforcement who then arrested Jason Jordan for the sale and distribution of counterfeit airbags. The indictment seeks prison time, the forfeiture of $57,063 in seized proceeds, and a money judgment of $669,732 in calculated proceeds. 16
- 18. Bringing together a growing pool of cross-sector Subject Matter Experts, real time to rapidly identify, mitigate and ultimately neutralize global cyber based threats. 18
- 19. • Networks • Employees • Customers • Suppliers – vendors –sub-contractors • Proprietary information 19
- 20. HOW IT WAS.or Citizen/Cyber Complaint FBI Local Office Cyber SSA Way too small: LOW priority. Trash or “O” File Local Big Business INFRAGUARD DIRECT FBI Local Office Cyber SSA “Russia – No Way!” Thumbs Down.- declined *Major assumption that industry would actually reach out at all to L.E. * U.S Attorney Complaints from victims… Complaints from companies… Historical Cyber Threat Intelligence – Path to L.E 20
- 21. HOW IT IS. ISP/Telcos AV Security Multiple Industry HQ Level L.E. Real Time Intel NCFTA Analysts FBI L.E. Analysts CONSENSUS STEP #1 Actionable Intel IIR’s Case Initiative Development Actionable Intel PSA’s, etc.Feedback Likely not to happen under old model * * * * * * *Did not exist in old model STEP #2 Adopting the NCFTA & CIRFU Models…. 21
- 22. Govt/Law EnforIndustry/NCFTA FBI –HQ = 13 Other Gov = 1-4 DHS = 2-4 DoD = 1-2 DEA = 1 International = 2-6 PG HTTF = 3 -5 Total @ 25 – 40+ Specific Industry = 10+ Funded industry = 10-12 Analyst/Teams = 20 + NCFTA Admin & IT = 12 Total @ 50 + Neutral “Meet in the Middle” (Non-Profit) Space Intel Reports Analysis Alerts -PSAs Case Development Case Referrals Proactive Support 22
- 23. Industry Inhibitors • View of the problem – Scope (in-house, within sector) • L.E. can’t help– or will hurt! Can’t find them “declined” • Think they can’t share intell, believe L.E won’t either.. • View of available resources (who is part of my team?) • Acquisitions/outsourcing – where is best early warning? • Who owns that intell? • Who needs (wants) help understanding context? • Who wants to remain blissfully ignorant? • Regulation or L.E encouragement? 23
- 24. Industry inhibitors & L.E Hurdles= drive the need for NCFTA & CIRFU models 1) Focus on Cross-Sector Intelligence sharing (2-way) 2) Build Model that emphasized resource sharing incl: 1) People 2) Tools 3) Live it, Prove it! Re-conditioning-thinking-doing= 24
- 25. Pop3scan SMTP Relays Compromised POP Accounts Plx_ssh2.c ssh brute force Warez? Load Modified Apache Load IVM Answering Attendant Load Fast Email Extractor Fonosip Inphonex Callfire Call-em-all Leaddiamond Ifbyphone Automs Marketingburst Coatelecenter Junctionnetworks Voiceblast vontoo 3rd Party Calling Services WWW Compromised Asterisk Systems Area Code Email List Bank Credit Union Card Info Victims call in to get Voice Response Unit IVM Answering Attendant Mules cash out in: Romania Spain San Diego Chicago NYC LA Infrastructure Bank – CU Customers (et al) 25
- 26. • Cooperation and sharing of information between firms allowed for the establishment of trends and investigation of this case. It is now aiding the FBI in their criminal investigation. • Spoofing of User Agents is a new and real threat. This threat highlights the importance of capturing and sharing additional UA information including: js useragent, screen resolution, and time offset. WHAT IS THE SIGNIFICANCE? 26
- 27. Victims of success… • GAO – In a 2007 report on Cyber Crime, the U.S. Government Accountability Office (GAO) acknowledged the economic cyber crimes and the resultant threats to U.S. national security. Mitigation efforts noted by GAO included the creation of cybercrime “partnerships” between public and private sector entities designed to facilitate cooperation and information sharing. The GAO specifically acknowledged the NCFTA as a partnership example. • President Obama’s 60 day Cyber Security Study – The NCFTA is the first partnership of its kind in the nation and was recently noted in the President’s 60-day, comprehensive, “clean-slate” review to assess U.S. policies and structures for cyber-security cited the NCFTA as one of three international examples as an “effective model” which “has a clearly defined institutional mission, well-defined roles and responsibilities for participants, and a clear value proposition that creates incentives for members to participate” and “mitigates concerns that would otherwise discourage participation by establishing and maintaining an environment of trust among the members.” 27
- 28. NCFTA – Built to: • Fit and evolve primarily to industry needs • Serve as a cross-sector bridge to assets (Industry & Govt/L.E) that can help • Identify and engage key “responsible” stakeholders- towards building Best Practices 28
- 29. Joint Initiative Process • Industry describes threat/problem • Industry consensus achieved (broader buy in) • Law Enforcement (Criminal Context) buy in • Focus Group meeting convened – Scope of threat and intelligence collection defined – Process for sharing intelligence & other resources – Key SME resources (embedded & remote) defined – Near & longer term goals & objectives defined 29
- 30. Partnerships—Global & Growing • Support from International Law Enforcement and Industry in 34 nations… • TDY and in-country model – Australia – Canada – U.K. – Germany – Romania – Italy – India – Turkey 30
- 31. 31
- 32. BCP CyFIN FRAUDSTOP RETAIL IRC BROKERAGE ROMANIANAUTO AUCTION BPHOSTING SMS VOIP MOBILEMALWARE PTP - BRAND TRADEMARK MALWARE ANTI MONEY LAUNDERING TELCO PREPAID RELOADABLE MONEY TRANSMITTERS VIRTUAL CURRENCY IPR – ECONOMIC ESPIONAGE HEALTH AND SAFETY HEALTHCARE - CYBER FAKE ID SOCIAL MEDIA/GAMING PHARMA COUNTERFEITGOODS MALWARE/BOTNETS BANKING PAYMENTCARDS HACTIVISM FULL TIME FORUMS FORUM RESEARCH – RUSSIAN/ROMANIAN/GERMAN IFA 32
- 33. NCFTA – CIRFU/LE Space DPN DB SPAM DB Other DB IDS Co’s ie Symantec DB’s L.E DBs ISP’s DB’s Financial Srvs Partners DB’s Software Co DB’s via BSA Other Fusion Centers Intel Merchants via MRC DB’s FBI Secure Space US CERT DHS US Postal & Internat’l– L.E 33
- 34. 1 FRAUD CASE, 6 INDUSTRIES EMAIL PROVIDERS BROKERAGE FIRMS BANKS DATING WEBSITES INTERNATIONAL WIRES TELCO 34
- 35. NCFTA Successes NCFTA provided intelligence to law enforcement who coordinated the arrest of seven organized crime leaders in Romania, the Czech Republic, the UK, and Canada who operated an online auto auction scam network. 35
- 36. NCFTA provided intelligence to law enforcement who arrested more than 100 cyber criminals in Romania and the US, who stole approximately $10 million via an online auto auction scam. NCFTA Successes 36
- 37. Intelligence provided by NCFTA industry partners led to the arrest of the money mule Alexander Kireev NCFTA Successes 37
- 38. NCFTA was instrumental in providing information to law enforcement that lead to the arrests of 32 “Anonymous” Members. NCFTA Successes 38
- 40. Discussion Points • Emerging technology • Prepaid Access – What is it and how does it work? • Open vs. closed loop products • Characteristics and features • Prepaid access payment chain • Assessing and managing anti-money laundering risks 40
- 41. Emerging Technology Generally New products and services: • Have changed how we do business – less face-to-face transactions • Internet/ P-2-P transactions/ digital check imaging/ mobile payments/ virtual worlds involving financial transactions • Have impacted financial and social behaviors • Who is offering the new product or service? A bank? A money services business? An unregulated entity? • Have varying money laundering risks depending on their features and characteristics and how they are managed 41
- 42. Prepaid Access: What is it? • Pay-in-advance • May be used like money • Likely transferable • Closed loop system: Starbucks card, mass transit cards • Open loop system: general purpose reloadable cards 42
- 43. Prepaid Access • Prepaid products require the consumer to pay in advance for future purchases of goods and services. Each payment is subtracted from the balance of the card or product until the total amount is spent • Bank Secrecy Act (BSA) regulatory definition: Access to funds or the value of funds that have been paid in advance and can be retrieved or transferred at some point in the future through an electronic device or vehicle, such as a card, code, electronic serial number, mobile identification number, or personal identification number. (31 C.F.R. 1010.100(ww)) • Some products permit consumers to pay bills, make purchases, and withdraw cash from ATM networks 43
- 44. Types Of Prepaid Access Scope Open Loop May be used by an unlimited number of merchants Closed Loop Use is limited to a specific location, vendor, or system Storage Capacity Fixed Amount Purchased for a certain denomination Does not allow upgrades or reloads Reloadable Purchased for a certain amount Allows reloading after use, up to a certain denomination Upgradeable Allows for additional amounts to be added after purchase 44
- 45. Types - Continued Access to prepaid funds Cash Accessible May obtain funds through ATM network or point of sale (POS) Non-cash Accessible May not obtain funds through ATM network or POS Storage Capacity Network Based Access information contained in magnetic stripe (like a credit card) Value stored on a remote database Chip Based Access information code on computer chip embedded in the card 45
- 46. Technology Chip and Pin Vs. Magnetic Stripe • Many countries outside the U.S. use the “chip and pin” (EMV standard) technology, where a computer chip is embedded in the prepaid card and the consumer must also enter a personal identification number at the point of sale (POS). • Different POS readers and infrastructure are needed for this product than for the magnetic stripe prepaid products. • The magnetic stripe prepaid card, common in the United States, contains account data recorded on the stripe that is reviewed by a magnetic reader at POS, like a credit card. • These products clear and settle through or “ride the rails” of the network branded credit card system. 46
- 47. Open vs. Closed Loop • Open Loop Prepaid Product: Generally understood to mean a network branded general spend prepaid product that is accepted everywhere that Visa, MasterCard, American Express or Discover is accepted. – Some open loop products are reloadable and function similar to traditional bank deposit accounts, often requiring the collection of customer information before activation. – Many open loop products are anonymous but others can also be issued in the name of an individual. 47
- 48. Open vs. Closed Loop (continued) • Closed Loop: This generally means a prepaid product used for a specific purpose or specific service. – BSA Regulatory Definition - Closed loop prepaid access: Prepaid access to funds or the value of funds that can be used only for goods or services in transactions involving a defined merchant or location (or set of locations), such as a specific retailer or retail chain, a college campus, or a subway system. (31 C.F.R. 1010.100 (kkk)) 48
- 49. Prepaid Transaction Chain • There is no one business model. • Some participants may serve in multiple roles. • A prepaid transaction chain may have limited participants or many along the chain. • The terms for prepaid and for the participants are many and there is no agreed upon vernacular. • Many participants along the transaction chain may hinder financial transparency. 49
- 50. Participants in the Transaction Chain • Program Manager: Runs the program’s day-to-day operations. This entity may or may not also be the entity that creates the program and designs the features and characteristics of the prepaid product. • Network: Any of the payment networks, including MasterCard, VISA, Discover and American Express, that clears, settles, and processes transactions. • Distributor: Ships prepaid products to endpoints. • Payment Processor: The entity that tracks and manages transactions and may be responsible for card account set-up and activation; adding value to products; and fraud control and reporting. • Issuing Bank: A bank that offers network branded prepaid cards to consumers and may serve as the holder of funds that have been prepaid and are awaiting instructions to be disbursed. • Seller or Retailer: A convenience store, drugstore, supermarket, or location where a consumer can buy a prepaid product. 50
- 51. Key Concepts • BSA/AML compliance responsibilities attach to institutions (e.g., banks), not products. – Accurately assessing risk (e.g., due diligence, 3rd- party relationships) – Suspicious activity monitoring (“by, at, or through the bank”) – OFAC 51
- 52. Risk Factors • Frequency – daily or monthly limits? • Dollar thresholds – maximum loads? • Anonymity • Ability to reload • International use • Ability to transfer funds • Ability to co-mingle funds • Primary purpose and use of the card 52
- 53. Assessing Risk • As when introducing any new product, banks should ensure their risk assessment is updated to accurately reflect BSA/AML risks associated with a new payment system. – Existing or new customers? – Online capabilities and non-face to face transactions? – Existing or new geographies? – 3rd parties? 53
- 54. Assessing Risk • Understand the specific product/program. – How will the bank and the partners manage the program? – Responsibilities, checks, and controls. – Usually contractual (pros and cons). – How will the bank’s name be used? – Who has what information? – Who sets limits and who enforces them? – Involvement of other third parties. 54
- 55. 3rd Party Due Diligence • Program Managers, Independent Sales Organizations, Agents, Marketers, Processors – Company reputation? References? – Financial information, banking relationship – Ownership, principals, structure, beneficial owners – Location of operations? Web-based? Site visit? – Related parties? Other companies? – Internet, open source information – Who performs the due diligence? – Limited or negative information 55
- 56. Suspicious Activity Monitoring • Fraud, discontinuing access to bank’s systems • Across multiple processors or programs? • Volume, compatibility of data • Average loads, balances • Common elements (address, TIN, e-mail) • Transaction locations, types, velocity • Series of transactions over time • MSB registration (provider or seller of prepaid access?) 56
- 57. 2010 Exam Manual Updates Related to Payments Issues • Prepaid cards (Electronic Cash) • Remote Deposit Capture (Electronic Banking) • Cover payments (Funds Transfers) • International Automated Clearing House Transactions (ACHs) • Feedback or ideas for next update? 57
- 58. Conclusions • As electronic payments volume, new products, and entry points continue to increase, financial institutions must have effective and comprehensive policies, procedures, and processes to identify, measure, and limit the risks associated with these activities. • Open, consistent, and effective interaction between operations, business lines, and compliance is critical to identifying and managing the risks associated with processing payments. • Financial institutions that process payments for third parties, including payment processors and high-risk merchants, must implement enhanced risk management practices to protect against BSA/AML compliance and fraud risks. 58
- 59. Closing Thoughts • The highest BSA/AML/OFAC risk is not necessarily in the program with the greatest number of cards or outstanding balances • “The issuing bank maintains ultimate responsibility for BSA/AML compliance whether or not a contractual agreement has been established.” FFIEC BSA/AML Examination Manual (2010) at 236. 59
- 60. Contact Information Timothy P. Leary Board of Governors of the Federal Reserve System (202) 452-2428 Timothy.P.Leary@frb.gov www.frb.gov Infobase: www.ffiec.gov/bsa_aml_infobase/default.htm 60
- 62. Common Types of GPR Fraud • Load Fraud • Tax fraud • Federal benefits fraud • Other ACH fraud (following account takeover) • Human Trafficking • Fraudulent cash loads • Credit/Debit card fraud loads • Mobile check deposit fraud • Spend Fraud • Unauthorized use (lost/stolen, card not present, compromised card, account takeover, etc.) • Frivolous Reg. E disputes • Authorization hold fraud 62
- 63. 63 Identity Thief Taxpayer Identity thief steals taxpayer’s personal information both to open the prepaid card and file the fraudulent return IRS Fraudulent return claiming refund is filed IRS issues refund via ACH to prepaid card $ Legitimate return may also be filed If legitimate return filed after fraud one, IRS sends notice of duplicate filing X Tax Related ID Theft Incidents Identified by IRS 2008 47,730 2009 165,524 2010 147,680 2011 242,142 2012 641,690 Source: GAO
- 64. Stolen Identity Refund Fraud (SIRF) Overview • Victim profile: – Typically real identities with long established address histories – In 63% of the cases, there was a mismatch between the address used for CIP and the address on file in public records databases • Ie. Person had always lived in Vermont and the card was signed up for an address in Texas • Two distinct victim profiles: – Elderly—typically born prior to 1934 – Very young— “Emerging credit” ages 18-22 64
- 65. Stolen Identity Refund Fraud (SIRF) Overview • Little to no activity was seen on the card until a tax refund • Refund was typically in the “cardholder” name • Many times the amount was inconsistent with the applicant data – Ie $10,000 tax refund for an 86 year old woman • Some cards attempted to put numerous tax refund in different names on the card 65
- 66. Tax Fraud – A Case Study • Review of accounts receiving mismatched tax refunds (SSN on refund did not equal SSN on account) led to a suspicious account that had an unusual email format – SSN#@domain.com (e.g. 123456789@yahoo.com) • Analysis of existing records identified thousands of unique email addresses using same format; these email addresses were then linked to specific accounts and physical addresses • Review of addresses led to the identification of a handful of high risk addresses that had received the bulk of the plastics • Same address line 1/zip code combination but different unit numbers (e.g. 12488 Oxnard St., North Hollywood, CA) 66
- 67. Tax Fraud – A Case Study 86% of tax funds deposited to accounts linked to this address had already been secured through blocks placed by other rule sets 67 A successful fraud deterrence strategy relies on numerous fraud controls (defense in depth)
- 68. Federal Benefits Fraud – Typical Pattern • Stolen identity used to open a GPR card – almost always in victim’s name but typically with a different address than victim • Direct deposit re-routed to GPR card or paper check changed to DD • May involve phishing of victim to get information needed to re-route benefits payment • DD can be rerouted through a variety of channels including via phone (with benefits provider) or via prepaid program’s direct deposit enrollment (ENR) process • Funds are quickly withdrawn via same methods as tax fraud • Due to the often critical nature of these payments, victim may detect fraud quickly – usually within days of missed payment 68Source: Treasury FMS
- 69. Cash Load (Victim Assisted Fraud) Typical Pattern • Use of stolen identities and/or mules to open GPR cards • Perpetrators will have access to numerous cards spread across many different issuers/program managers; will use same identity across different programs • Confidence scam initiated where victim is required to pay fraudster money using cash reload product; common scams include: • Lottery • Malware • Debt collection • Loan fees • Past due utility bill • Satellite TV upgrades • Product for sale • Victim buys reload product and provides reload “PIN” to fraudster, who then applies funds to a card in their control • Funds are withdrawn by fraudster via the usual methods or sold to cash out ring for X cents on the dollar (going rate appears to be 60 cents) • Only later does the victim realize they were duped at which point they may file a dispute/complaint with reload network and regulatory agency (FTC) 69
- 70. Cash Load (Victim Assisted Fraud) Case Study • Dispute filed with reload network by purchaser of cash reload product • Purchaser (victim) was contacted by “debt collection agency” related to a current or previous payday loan • Victim threatened with foreclosure, jail time, job loss if payment not made immediately via cash reload product • Victim buys cash reload and provides reload PIN to “debt collector” to satisfy debt • Reload PIN immediately loaded to a GPR card that is part of the reload network • Victim later realizes this was not a legitimate debt collection and files dispute • Funds spent off of fraudsters’ GPR cards via a series of CNP transactions conducted by what appear to be India-based debt collection merchants 70
- 71. ACH Fraud Typical Pattern • Fraudster, typically with a stolen identity, opens a GPR card as the receiving account for incoming ACH transfers from accounts at other financial institutions (FIs) • Account takeover occurs at another FI with fraudster initiating ACH transfers to GPR card • Funds are then withdrawn from GPR via ATM withdrawal, cash back at POS, spend on card • Funds can be stolen from any ACH enabled account including credit card rewards redemptions • GPR issuer is typically RDFI in this scenario so doesn’t own any of the financial risk associated with the fraudulent transfer – however reputational and regulatory risk remain • Due to high loss rates, some FI’s have blocked outbound ACH transfers to prepaid programs • Program managers/issuers should carefully consider risk associated with becoming an ODFI that allows “pull” ACH transfers from another FI 71
- 72. 72 One identity used to open up 38 different prepaid cards across 34 programs issued by 14 banks.
- 73. Human Trafficking Overview • There are both domestic and International laws against human trafficking • Human trafficking is a form of modern-day slavery. • Human trafficking is prevalent in many countries around the world. Different countries may be primarily sites of origin, transit, destination, and/or internal trafficking. • Cases of human trafficking have been reported in all fifty states of the United States (Free the Slaves). • Human trafficking is a market-based economy that exists on principles of supply and demand. It thrives due to conditions which allow for high profits to be generated at low risk. • Common theme--“Compelled Service.” Can include: – Human trafficking – Forced Labor – Prostitution – Sex trades 73
- 74. Human Trafficking • Myths and Misperceptions – Trafficking is not smuggling or forced movement. – Trafficking does not require transportation or border crossing, and does not only happen to immigrants or foreign nationals. – Trafficking does not require physical force, physical abuse, or physical restraint. – The consent of the victim is considered irrelevant, as is payment. 74
- 75. Backpage.com • What is backpage.com? – Similar to Craig’s list – Allows the advertisement of “Adult Services” – Allows advertising of adult services in multiple cities at once – Most local posts are FREE – Adult services and postings in multiple cities charge a fee 75
- 76. Who Are Traffickers • Based on an analysis of human trafficking cases that have been identified, examples of potential traffickers include: – Pimps – Intimate partners/family members – Gangs and criminal networks – Brothel and fake massage business owners and managers – Growers and crewleaders in agriculture – Labor brokers – Employers of domestic servants – Small business owners and managers – Large factory owners and corporations 76
- 77. Victimology • Unfortunately, due to the nature of trafficking there is not a clear victim profile that has emerged. • Based on U.S. federal law, trafficked persons in the U.S. can be; – men or women, – adults or children, – foreign nationals or U.S. citizens. – Some are well-educated, while others have no formal education. – Some immigrant victims are currently in the U.S. legally, and others are undocumented. • Some form of vulnerability tends to be the common thread amongst all different trafficking victims. 77
- 78. Typologies & Detection • Identifying issues – Spend on backpage.com purchases, typically multiple (5 per week for a total of more than $20 activity) – Travel activity seen on the card • Airfare • Hotels • Cash on • Cash off • Liquor stores • Bus tickets – Other Considerations • Money transfers • Business as a front • Geographic clustering 78
- 79. Solutions • Identify the behavior patterns • Backpage.com and such sites are a good indicator • Triangulate with other behaviors • Understand the victim is typically the identity you will see • Takes a much deeper dive to get to the suspect data 79
- 80. FRAUD CONTROLS TO CONSIDER 80
- 81. Prepaid Card Fraud & AML Control Framework 81 Administration Return Mail Processing, Reg. E Disputes, Law Enforcement Support, SAR Filing, Federal Benefits Support, Cash Reload Dispute Processing Money Out (Spend/Withdrawal) Restricted Access on Temporary Card or Until Personalized Card Activation, Transaction Limits, Transaction Monitoring & Blocks, Refund Monitoring Money In (Funds Loaded) Restricted Access on Temporary Card or Until Personalized Card Activation, Transaction Limits, Velocity Checks, High Risk Reviews & Blocks, Name/SSN Match Logic, Out of Wallet Questions Card Out Device ID, Velocity Checks, Invalid Application Data Check Customer In (Acquisition) USPS Address Standardization, Negative File, OFAC Check, Velocity Checks, Risk Based CIP, High Risk Indicators, Out of Wallet Questions, eMail & Cell Phone Verification
- 82. Customer In Control • Customer Identification Program (CIP) • Much of the GPR fraud begins with a stolen identity being used to open a prepaid card; therefore a robust CIP program should be your first line of defense to mitigate fraud • Most GPR programs rely on non-documentary verification, which is generally less robust than a documentary verification process • Consider enhanced verification processes (e.g. out of wallet questions) for higher risk activations or transactions • Monitor fraud or suspicious activity rates by CIP response code to determine which codes drive the highest rates; target additional processes or review towards those codes • Many third party verification services provide high risk response codes • SSN invalid, never issued, deceased, issued prior to DOB, associated with multiple people; phone is pager or invalid; address is mail forwarding, mail drop, commercial address or prison address 82
- 83. Customer In Controls • Address standardization – ensures address provided is deliverable per USPS database and put into standard USPS format • Residential vs. commercial address confirmation • eMail verification • Passive confirms email domain is deliverable • Active requires customer to receive email and act on instructions • Cell phone verification, geo-location, one time passwords • IP location services; for example, does your program allow activations from foreign countries? • Negative or black list – list of application data elements (SSNs, addresses, phones, emails) previously used to commit fraud • Velocity Controls • # of cards per customer/SSN • # of online generated cards per customer/SSN • # of activations per ANI, IP or device ID • # of cards per phone, physical address or email address 83
- 84. SIRF Solutions - Meta • All cards that will accept tax loads are required to match 4 of 4 CIP elements before load occurs • Preventing the identity fraud helps to reduce the number of fraudulent tax returns • Fraudulent loads decreased by 83% over last year • Current efforts by both the IRS as well as continued Meta strategy refinement have contributed to the reduction 84
- 85. Card Out Controls • # of cards or identities associated with a specific address, email or phone • # of cards/identities associated with a specific building (e.g. address line 1/zip code combination) • Cards activated by a specific device (web/mobile activations) • Cards activated with anonymized email domains (e.g. yopmail/hushmail) • Cards activated with same SSN but different last names • Reviewing recently opened accounts with returned mail • Address change limitations on recently opened accounts • Limit or eliminate expedited delivery (FedEx) 85
- 86. Money In Controls • Max balance limits • Velocity (#) and/or volume ($) limits on different load types (e.g. cash, ACH loads); can be aggregated at card, SSN, address, phone, email level • Monitoring of ACH deposits from international locations • Geographic disparity between cash loads and card location • Account verification processes including micro debit/credit process– typically used to verify ownership of external funding source • Rules or regression based models to identify and interdict suspicious loads • Restrictions on ENR enrollments (e.g. OOW) • Specific tax fraud controls • Mismatch deposits – refund in different name/SSN than cardholder • Velocity of refunds received by same person • Refunds received in name of recently added secondary cardholder • Refunds received after tax season 86
- 87. Money Out Controls • Velocity (#) and/or volume ($) limits on cash withdrawals and spend transactions (includes daily ATM and spend limits); can be aggregated at card, SSN, address, phone, email level • Velocity/volume limits on bill pay transactions • Specific limits or blocks on foreign activity (e.g. Jamaica or Dominican Republic) • Monitoring of spend/withdrawal activity trends by country • Monitoring and aggregation of refund activity by account parameters (e.g. SSN, address, phone, email, etc.) • Rules or regression based models to identify and interdict suspicious monetary and non-monetary transactions (e.g. address change, card requests, PIN changes) 87
- 89. Conference Name Date City, State ACI Prepaid Compliance 1.29-30, 2013 Washtinton, DC ABA Prepaid Roundtable 2.17.13 Orlando, FL RSA Conference 2.25-3.1, 2013 San Francisco, CA Prepaid Expo USA 2013 3.4-6, 2013 Orlando, FL CFSA 2013 3. 5-8, 2013 Dana Point, CA BAI--Payments Connect 3.11-13, 2013 Phoenix, AZ PMTS: INNOVATION Project 2013 3.20-21, 2013 Cambridge, MA Card Forum 4.7-10, 2013 Boca Raton, FL USPS/Financial Industry Mail Security Initiative 4.10.2013 Phoenix, AZ CYFIN--Cyber Financial Crime 4.16-17, 2013 Pittsburgh, PA NACHA 4.21-24, 2013 San Diego, CA IAFCI 5.15, 2013 Downey, CA CNP Expo 5.20-23, 2013 Orlando, FL CFSI 6.5-7, 2013 Miami, FL Power of Prepaid 6.26-28, 2013 Washington, DC IAFCI 8.26-30, 2013 Denver, CO Congressional Black Caucus--Legslative Conference 9.18-21, 2013 Washington, DC MTRA Conference 9.25-26. 2013 New Orleans, LA Money 2020 10.6-9, 2013 Las Vegas, NV IAFCI Regional meeting 10.10-11, 2013 Williamsburg, VA ATM, Debit and Prepaid Forum 10.20-23, 2013 Las Vegas, NV BAI--Retail Delivery 11. 5-7, 2013 Denver, CO 2013 NBPCA Conferences Listed are the conferences which NBPCA, along with interested members, participates in, supports, or hosts. 89
- 90. QUESTIONS?? 90
