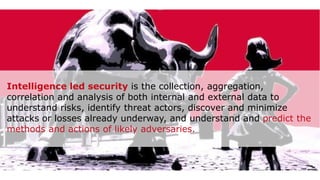
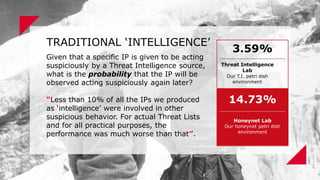
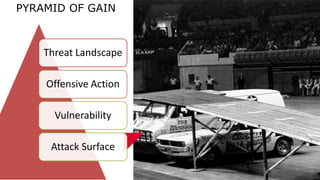
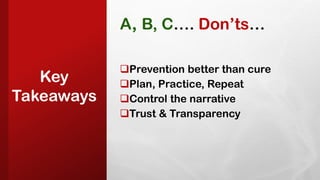
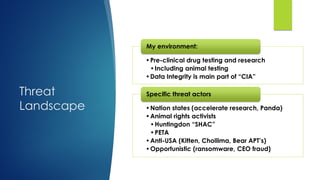
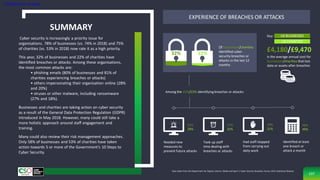
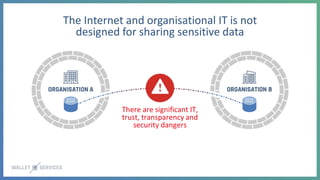
The document details the discussions held at Digit's 6th annual Scot-Secure event, emphasizing the importance of cybersecurity awareness, team collaboration, and the evolving threat landscape. Key topics include the need for effective security team integration, the challenges posed by social engineering and insider threats, and the essential nature of maintaining trust with customers. Additionally, strategies for fostering a culture of security within organizations and the significance of threat intelligence in shaping security practices are highlighted.
































































































































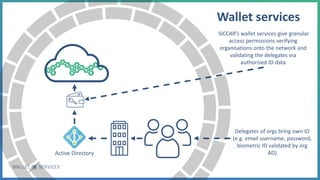


![CLAIM: I AM A
VERIFIED DELEGATE
[DEVICE ID + SECURITY
CERTIFICATE] + ORG
[AUTH ID]
Org 1
ATTESTATION:
IS VALID ORG
Org 2
ASSURING CLAIMS & ATTESTATIONS FOR GUARANTEEING
ANONYMITY
CLAIM: I AM A
VERIFIED DELEGATE
[DEVICE ID + SECURITY
CERTIFICATE] + ORG
[AUTH ID]
ATTESTATION:
IS VALID ORG
DELEGATED
DISCLOSURES](https://image.slidesharecdn.com/ss20speakerslidesslideshare-200221123237/85/ScotSecure-2020-274-320.jpg)
