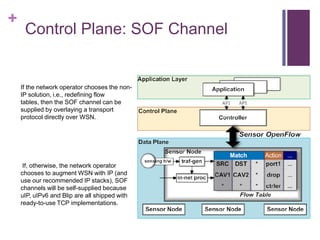
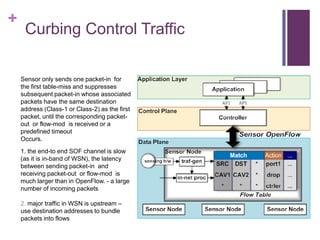
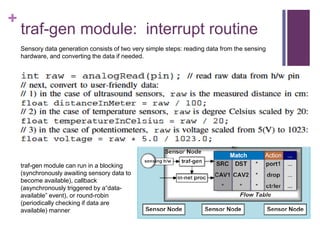
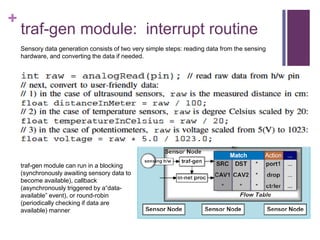
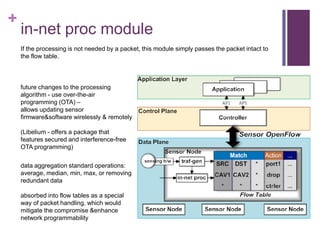
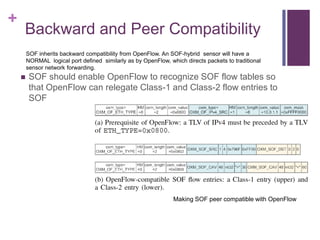
This document proposes enabling software-defined networking capabilities in wireless sensor networks. It discusses adapting the OpenFlow protocol by redefining flow tables to classify wireless sensor network addressing schemes and handle sensor data packet flows. It also addresses providing the software-defined network control channel, reducing control traffic, generating and processing sensor data, and ensuring backward and peer compatibility with OpenFlow. The goal is to provide programmable routing and flexible policy enforcement for wireless sensor networks.

![+
Data Plane: Creating Flows
Redefine flow tables to cater for the special addressing schemes in WSN
classify WSN addressing schemes into Class-1 , compact network-unique addresses such as the ZigBee 16-bit network
addresses (e.g., 0x796F as assigned by the CSkip algorithm [9]), and Class-2 , concatenated attribute-value pairs (CAV)
such as “30< temperature< 60” and “Zone-ID=7 AND x -coordinate> 150”](https://image.slidesharecdn.com/wirelesssensoropenflow-130227171838-phpapp01/85/Wireless-sensor-open-flow-2-320.jpg)