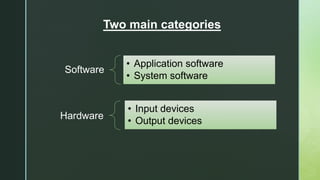
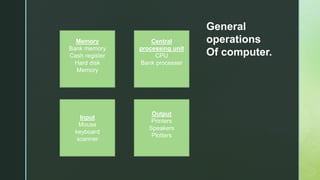
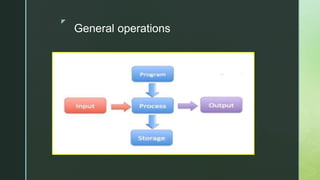
A computer is an electronic device that processes and manipulates data, consisting of hardware, software, and peripheral devices. It operates through two main types of software: application software, which performs specific tasks, and system software, which manages hardware functions. Input and output devices facilitate data entry and retrieval, while connectivity enables interaction with other systems over the internet.