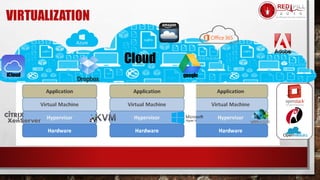
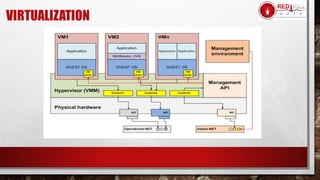
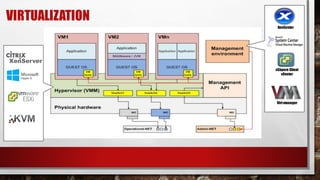
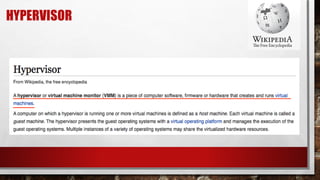
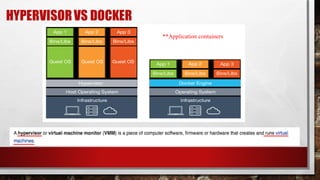
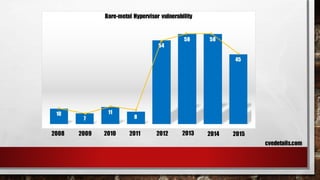
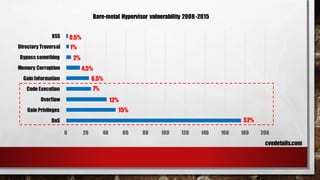
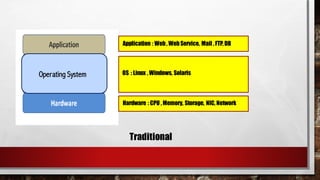
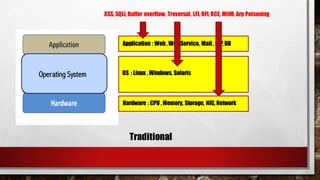
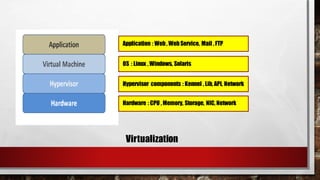
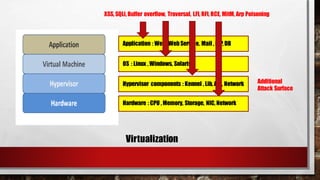
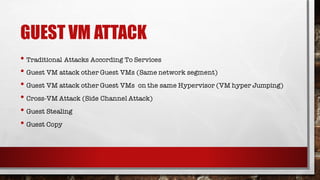
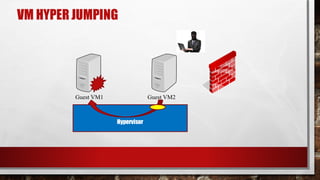
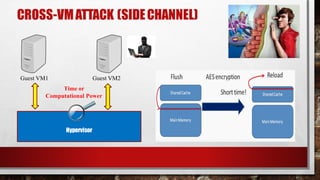
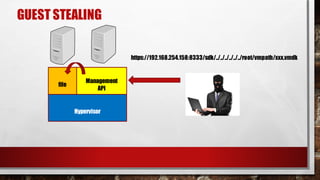
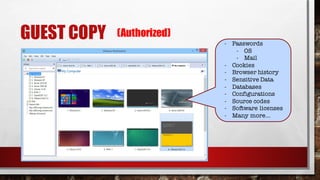
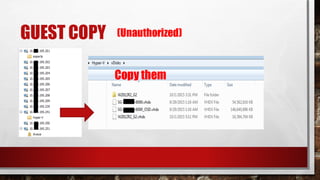
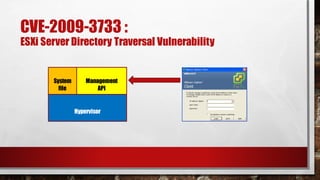
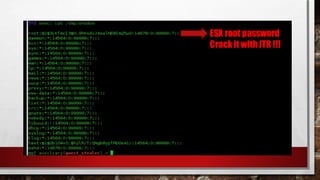
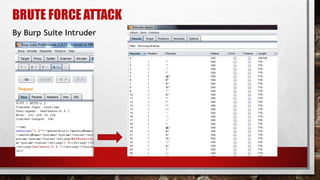
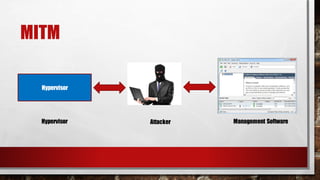
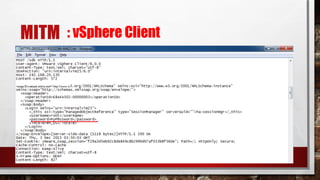
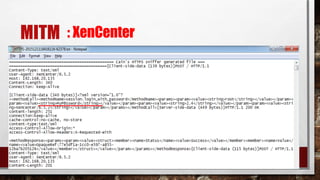
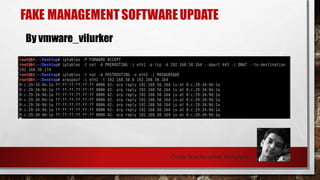
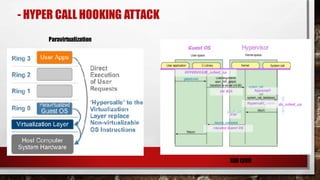
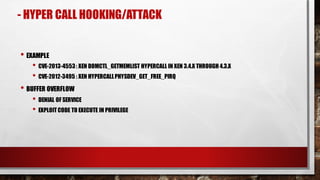
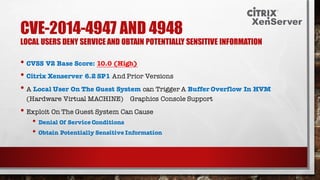
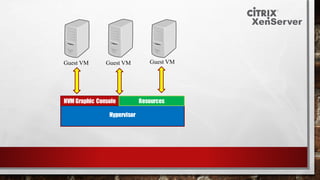
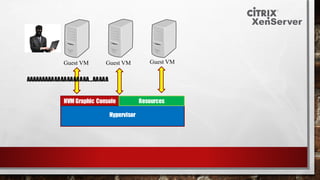
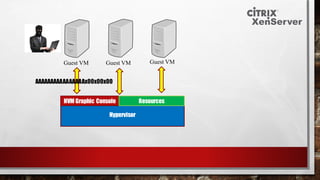
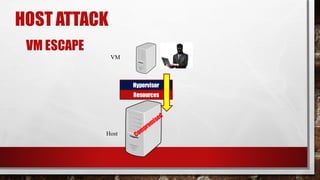
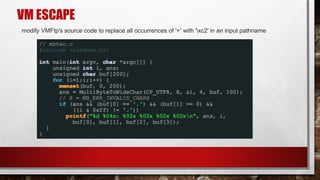
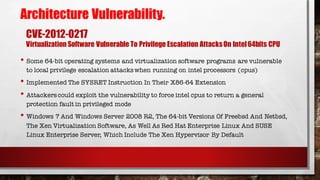
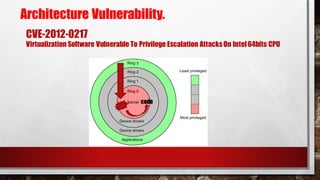
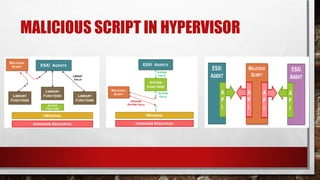
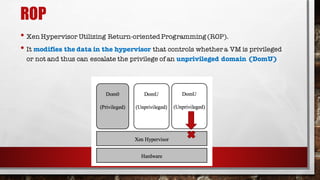
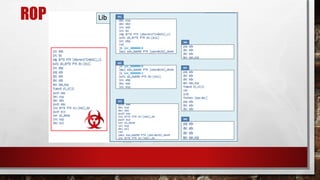
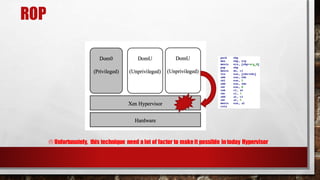
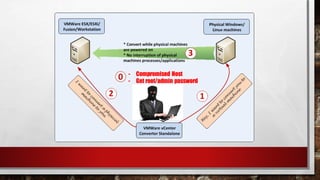
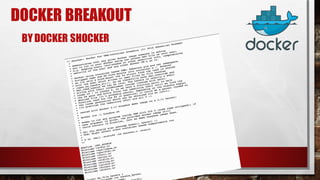
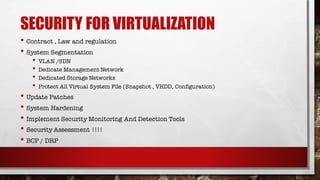
This document provides an overview of virtualization security topics. It discusses various virtualization threats including guest VM attacks, hypervisor attacks, and management API attacks. Specific vulnerabilities are also mentioned, such as directory traversal issues and buffer overflows in hypervisor components like the virtual floppy disk controller. Attack methods like privilege escalation, denial of service, and taking control of the hypervisor are covered at a high level.