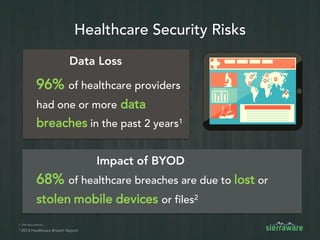
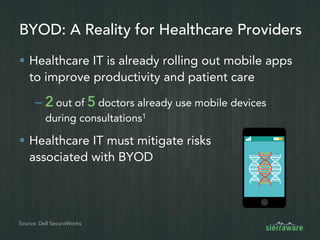
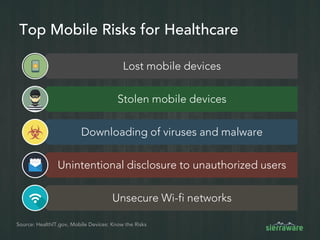
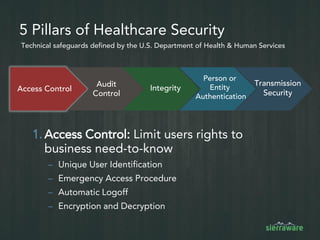
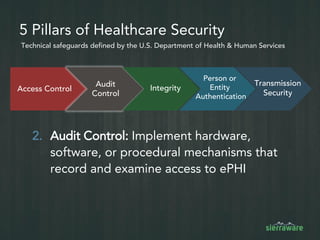
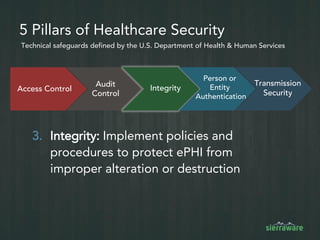
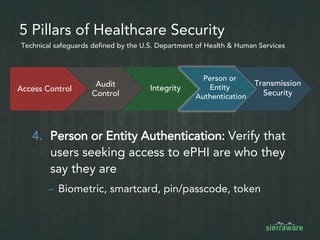
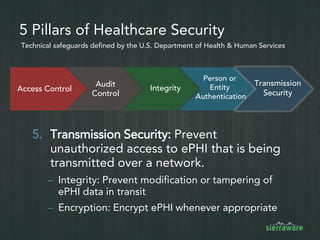
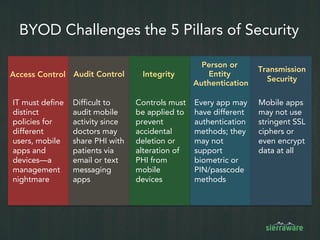
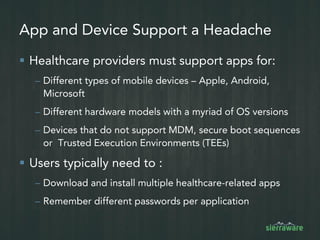
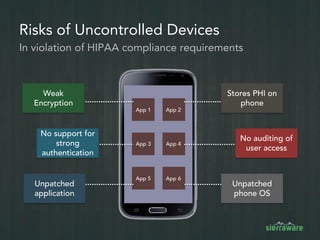
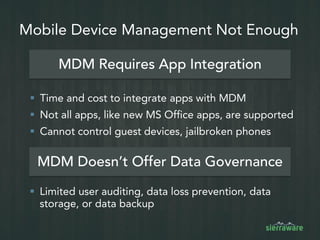
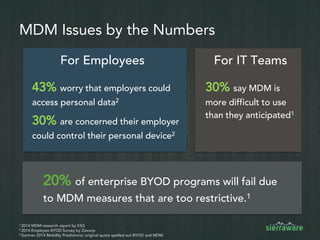
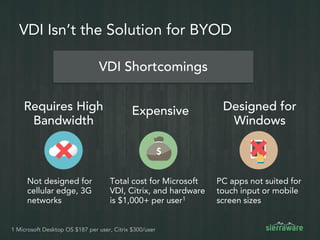
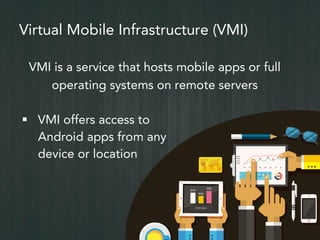
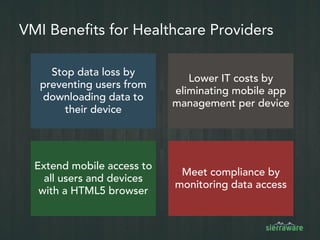
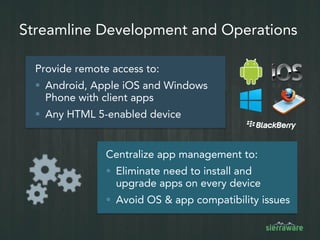
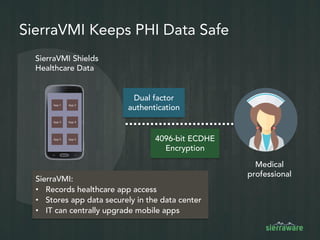
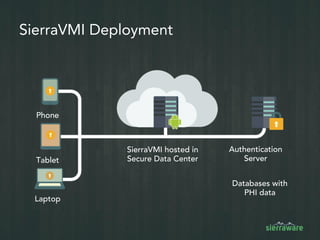
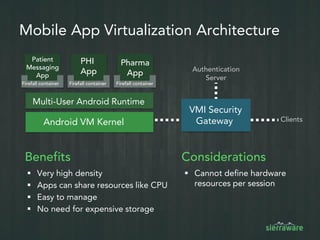
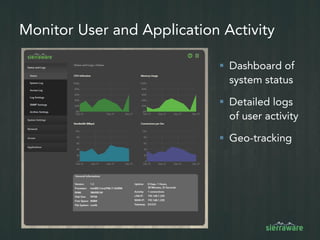
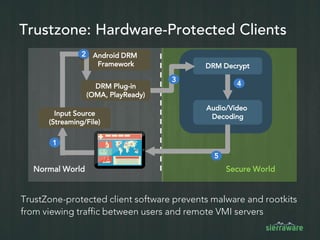
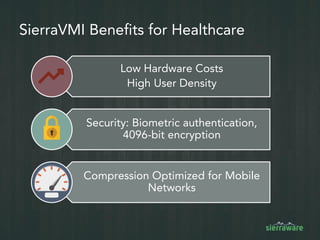
The document outlines a roadmap for healthcare security focusing on BYOD (Bring Your Own Device) challenges and solutions. It highlights the significant risks of data breaches in healthcare, particularly through mobile devices, and emphasizes the importance of technical safeguards like access control, audit control, and encryption. The use of Virtual Mobile Infrastructure (VMI) is proposed as a solution to centralize app management and enhance security while meeting compliance requirements.