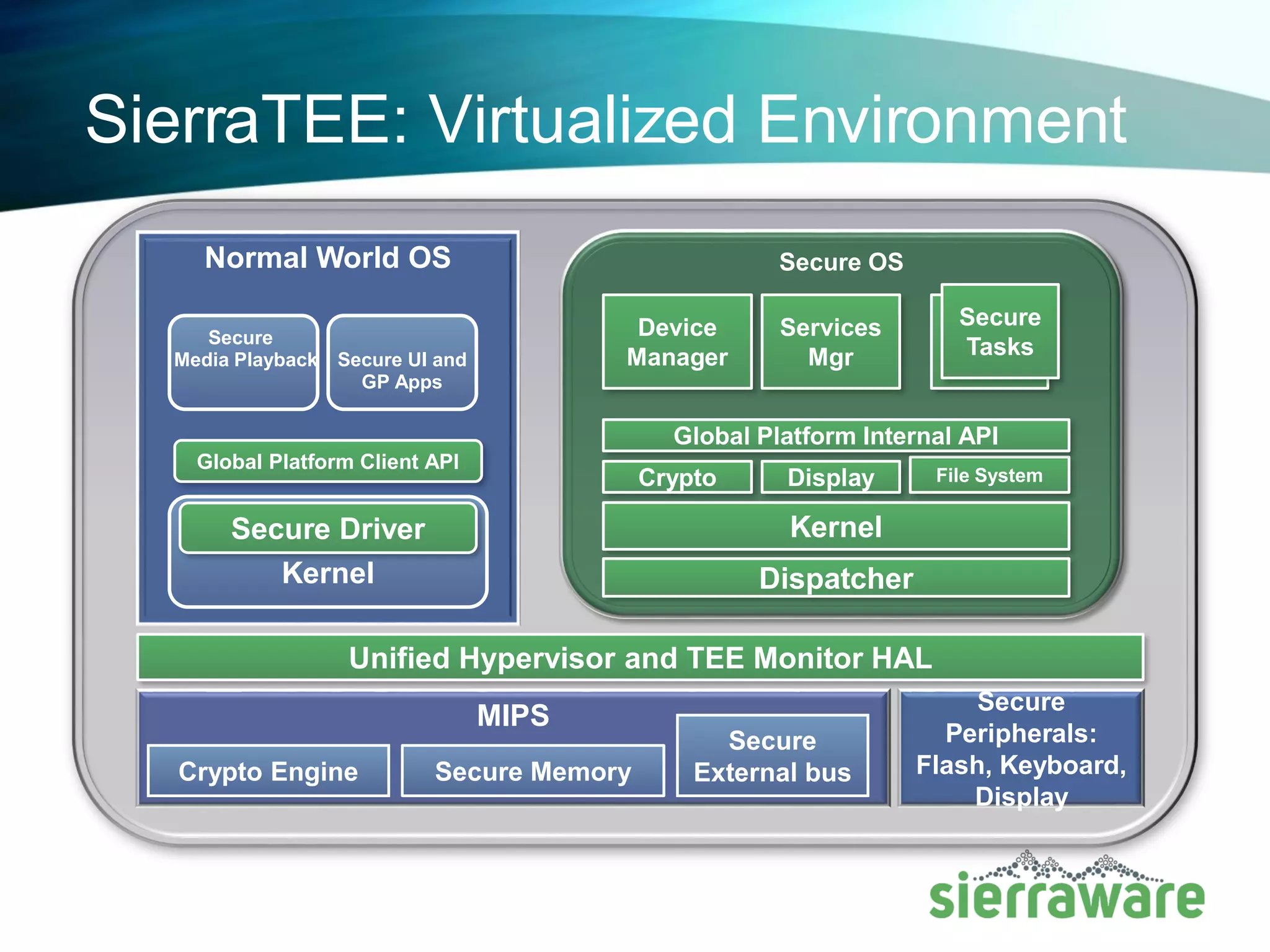
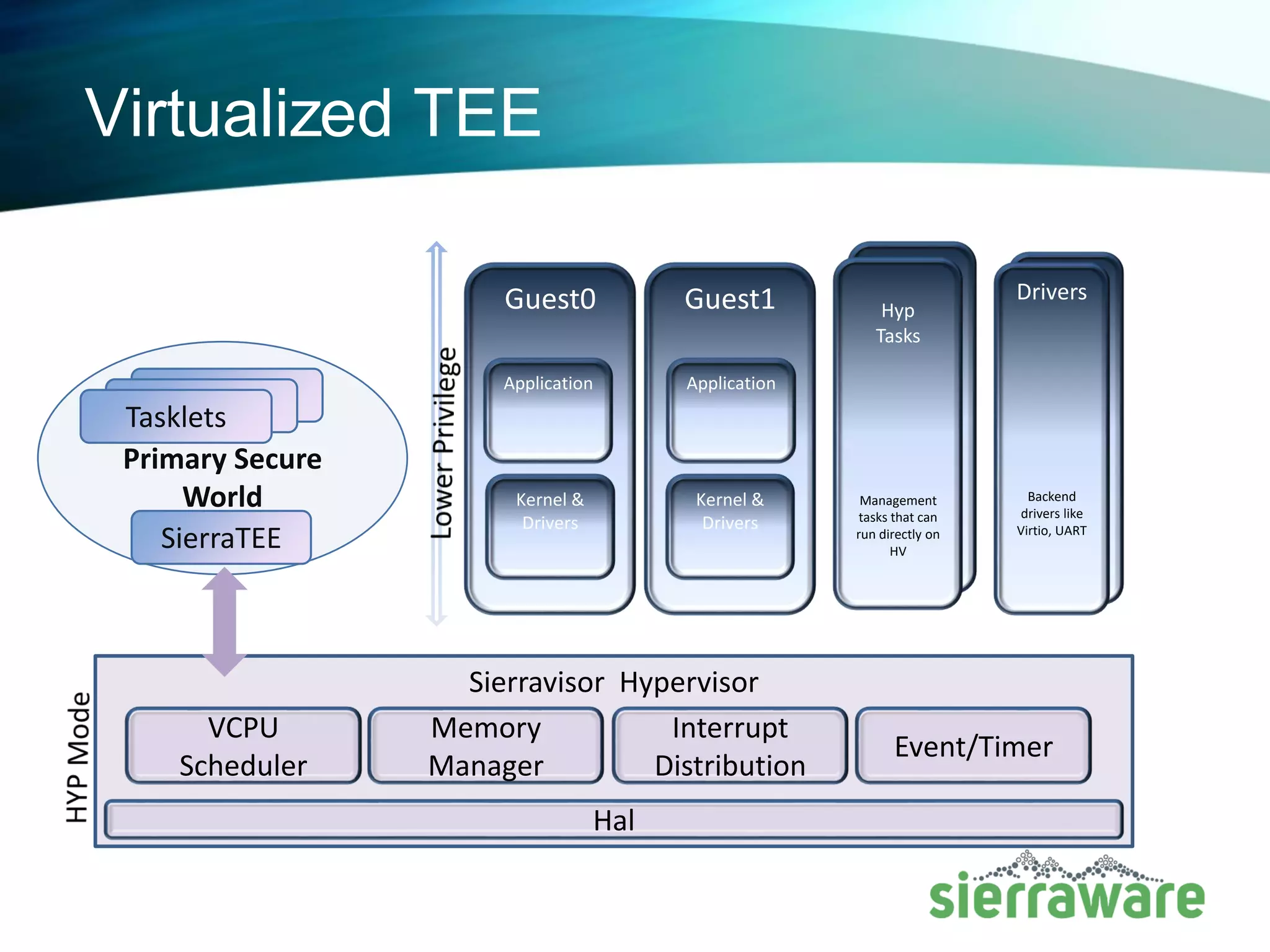
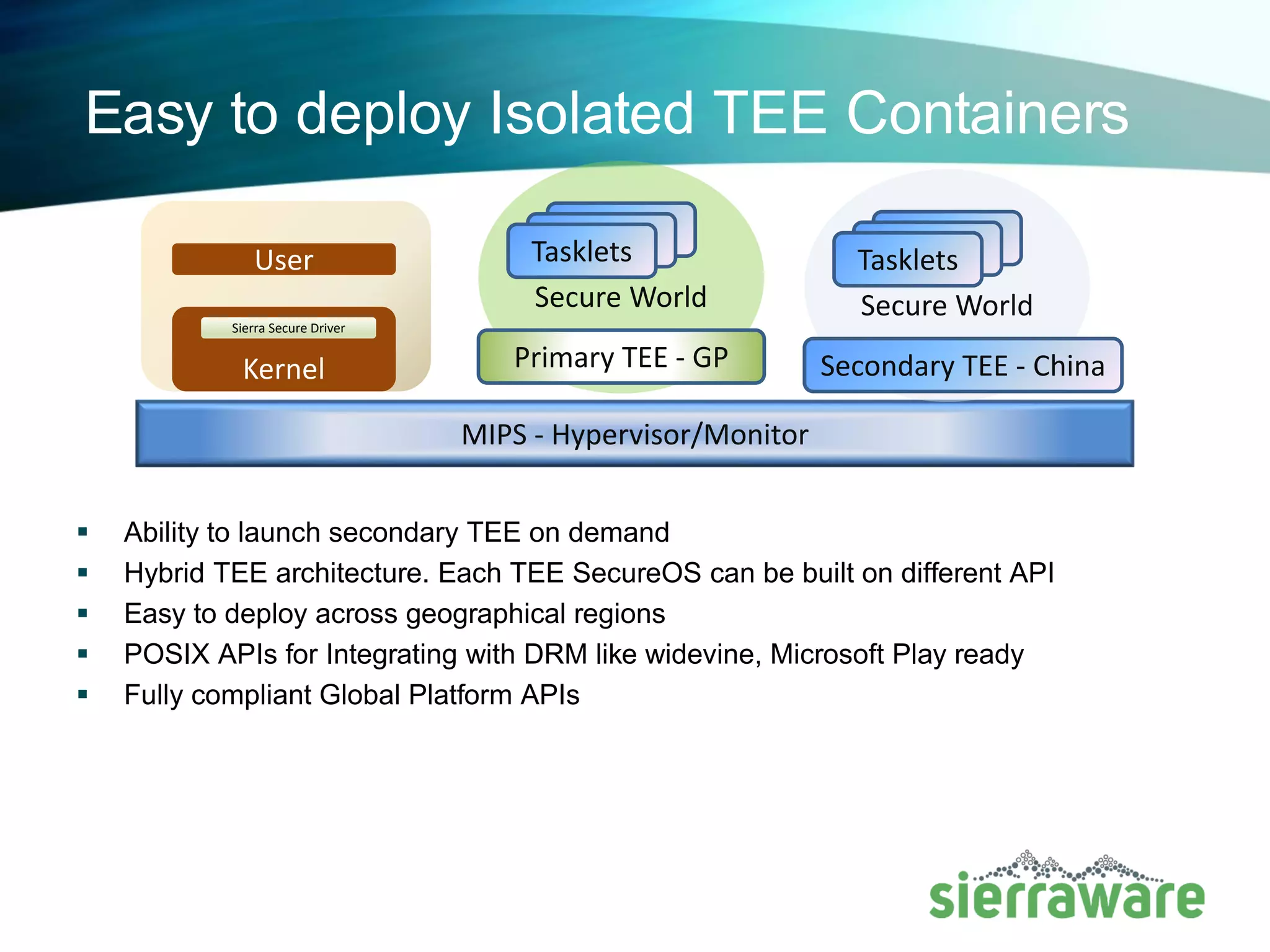
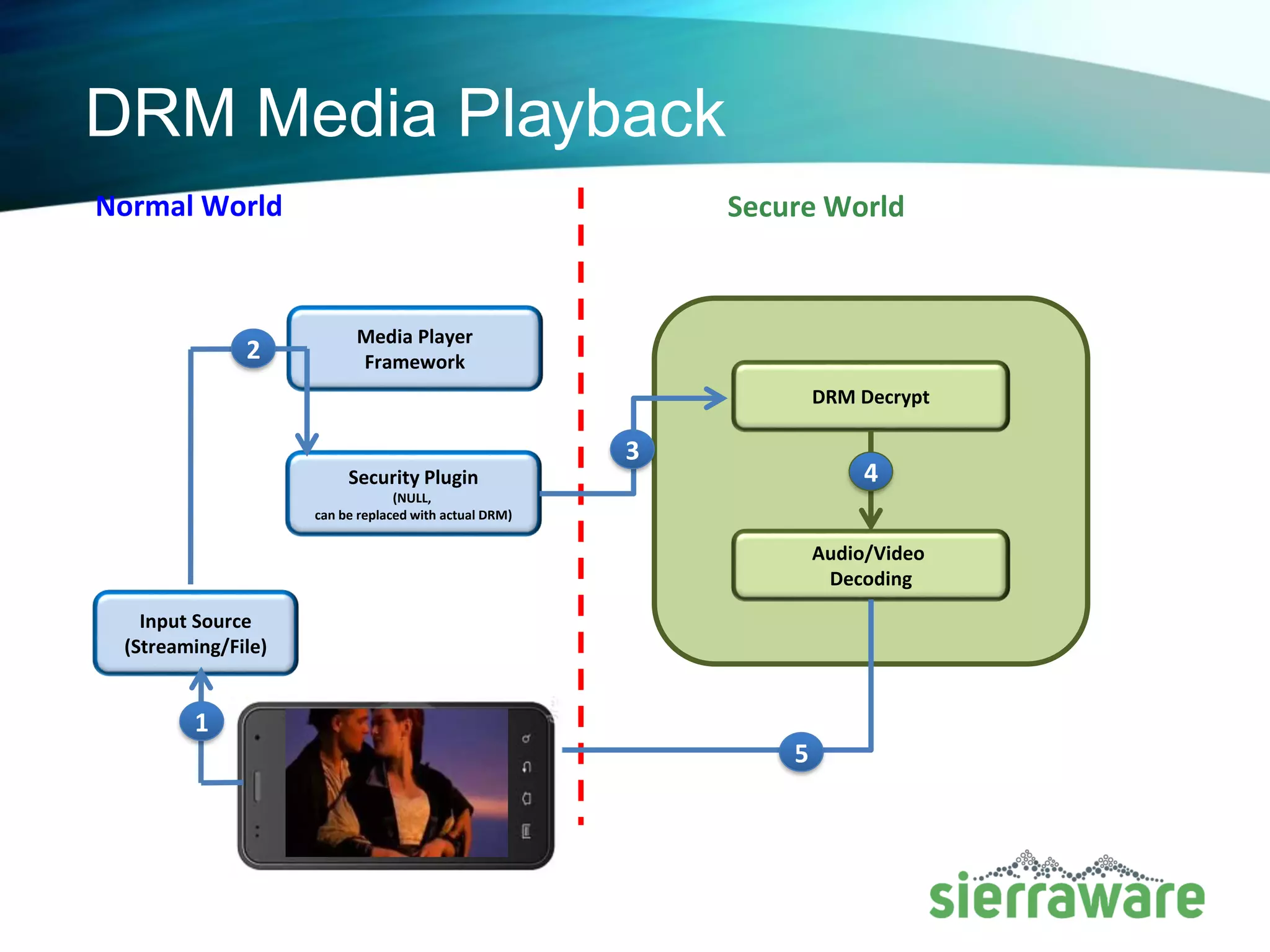
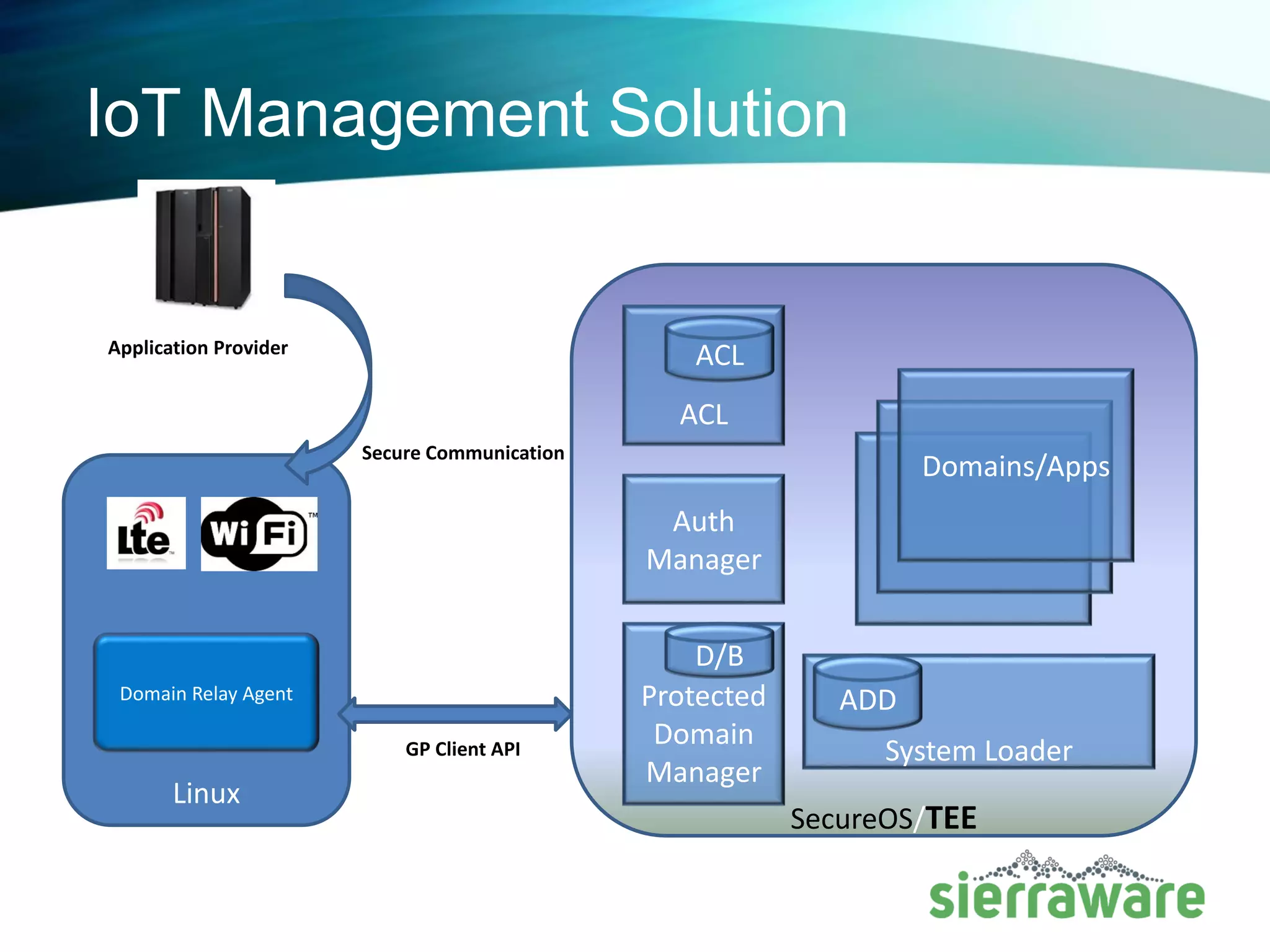
SierraWare offers a secure OS and hypervisor solution tailored for MIPS IoT security and virtualization, providing a unified TEE and hypervisor implementation that adheres to global standards. Their products cater to various platforms, including residential gateways and automotive systems, and include features like virtualized multi-TEE architecture and easy deployment across regions. The solution supports compliance with industry standards and offers extensive professional services for integration and support.